Pentest
-
 202
202Kali Linux 2019.1 Released — Operating System For Hackers
Wohooo! Great news for hackers and penetration testers. Offensive Security has just released Kali Linux 2019.1, the first 2019 version of its...
-
 169
169Popular Torrent Uploader ‘CracksNow’ Caught Spreading Ransomware
It’s not at all surprising that downloading movies and software from the torrent network could infect your computer with malware, but it’s...
-

 324
324DCOMrade – Powershell Script For Enumerating Vulnerable DCOM Applications
DCOMrade is a Powershell script that is able to enumerate the possible vulnerable DCOM applications that might allow for lateral movement,...
-
 178
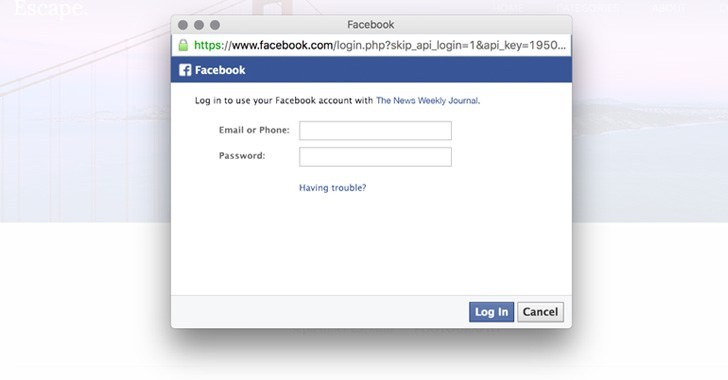
178WARNING – New Phishing Attack That Even Most Vigilant Users Could Fall For
How do you check if a website asking for your credentials is fake or legit to log in? By checking if the...
-

 174
174Hacker Breaches Dozens of Sites, Puts 127 Million New Records Up for Sale
A hacker who was selling details of nearly 620 million online accounts stolen from 16 popular websites has now put up a...
-
 178
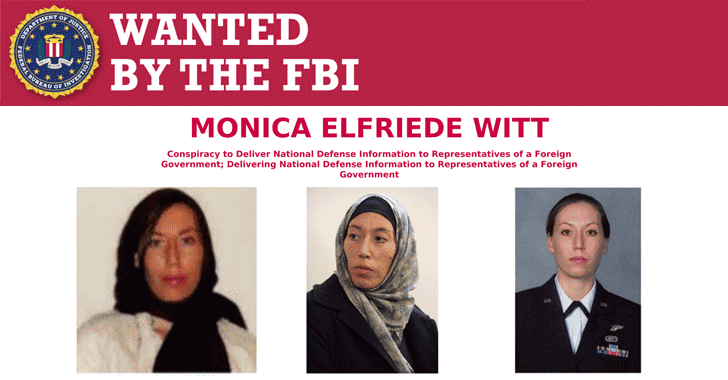
178Ex-US Intelligence Agent Charged With Spying and Helping Iranian Hackers
The United States Department of Justice has announced espionage charges against a former US Air Force intelligence officer with the highest level...
-

 250
250RunC Flaw Lets Attackers Escape Linux Containers to Gain Root on Hosts
A serious security vulnerability has been discovered in the core runC container code that affects several open-source container management systems, potentially allowing...
-
 327
327Justniffer – Network TCP Packet Sniffer
Justniffer is a network protocol analyzer that captures network traffic and produces logs in a customized way, can emulate Apache web server...
-
 162
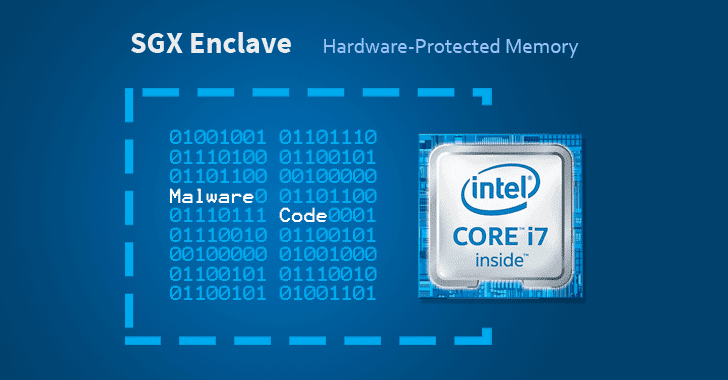
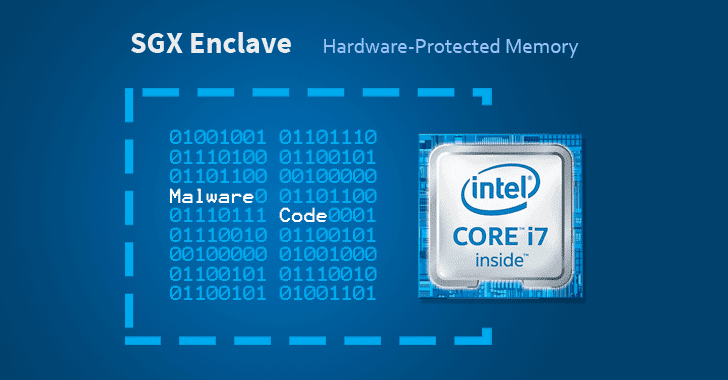
162Researchers Implant “Protected” Malware On Intel SGX Enclaves
Cybersecurity researchers have discovered a way to hide malicious code in Intel SGX enclaves, a hardware-based memory encryption feature in modern processors...
-

 167
167Snapd Flaw Lets Attackers Gain Root Access On Linux Systems
Ubuntu and some other Linux distributions suffer from a severe privilege escalation vulnerability that could allow a local attacker or a malicious...
-
 204
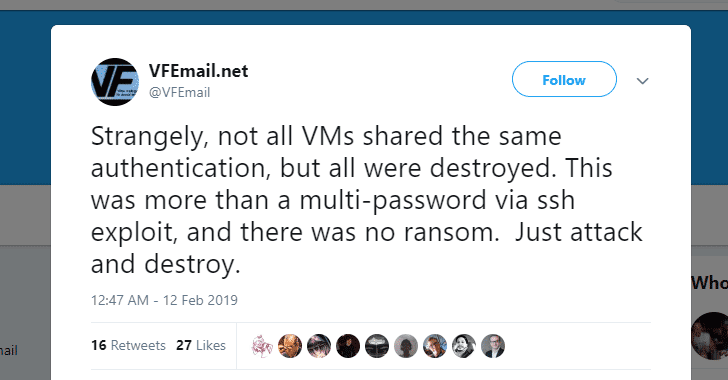
204Hackers Destroyed VFEmail Service – Deleted Its Entire Data and Backups
What could be more frightening than a service informing you that all your data is gone—every file and every backup servers are...
-
 249
249Adobe Releases February 2019 Patch Updates For 75 Vulnerabilities
Welcome back! Adobe has today released its monthly security updates to address a total of 75 security vulnerabilities across its various products,...
-

 192
192New Unpatched macOS Flaw Lets Apps Spy On Your Safari Browsing History
A new security vulnerability has been discovered in the latest version of Apple’s macOS Mojave that could allow a malicious application to...
-

 241
241Microsoft Patch Tuesday — February 2019 Update Fixes 77 Flaws
Microsoft has issued its second Patch Tuesday for this year to address a total of 77 CVE-listed security vulnerabilities in its Windows...
-

 198
198Xiaomi Electric Scooters Vulnerable to Life-Threatening Remote Hacks
Smart devices definitely make our lives easier, faster, and more efficient, but unfortunately, an insecure smart device can also ruin your day,...
-

 184
184Beware!! New Windows .exe Malware Found Targeting macOS Computers
A malicious Windows EXE file can even infect your Mac computer as well. Yes, you heard me right — a .exe malware...
-

 215
215First Android Clipboard Hijacking Crypto Malware Found On Google Play Store
A security researcher has discovered yet another cryptocurrency-stealing malware on the official Google Play Store that was designed to secretly steal bitcoin...
-

 285
285HTTrack Website Copier – Web Crawler And Offline Browser
HTTrack allows you to download a World Wide Web site from the Internet to a local directory, building recursively all directories, getting...
-
 300
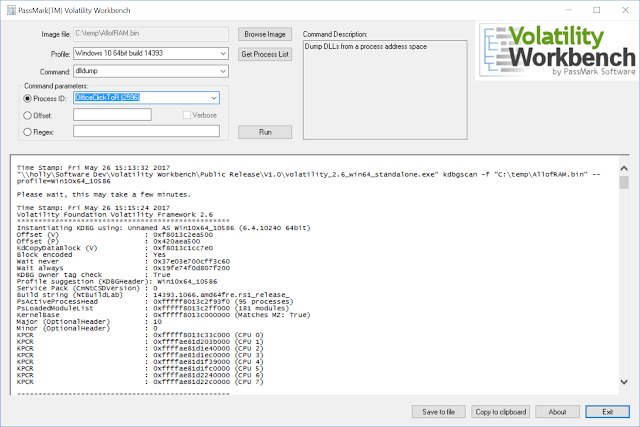
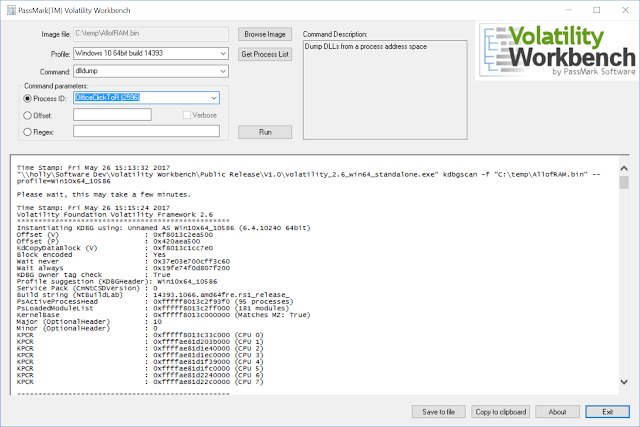
300Volatility Workbench – A GUI For Volatility Memory Forensics
Volatility Workbench is a graphical user interface (GUI) for the Volatility tool. Volatility is a command line memory analysis and forensics tool...
-

 176
176Latest iOS 12.1.4 Update Patches 2 Zero-Day and FaceTime Bugs
Apple has finally released iOS 12.1.4 software update to patch the terrible Group FaceTime privacy bug that could have allowed an Apple...
-
 192
192Google Created Faster Storage Encryption for All Low-End Devices
Google has launched a new encryption algorithm that has been built specifically to run on mobile phones and smart IoT devices that...






