Pentest
-
 383
383SysAnalyzer – Automated Malcode Analysis System
SysAnalyzer is an open-source application that was designed to give malcode analysts an automated tool to quickly collect, compare, and report...
-
 342
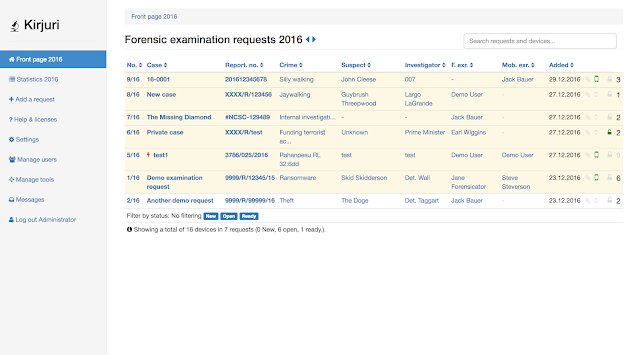
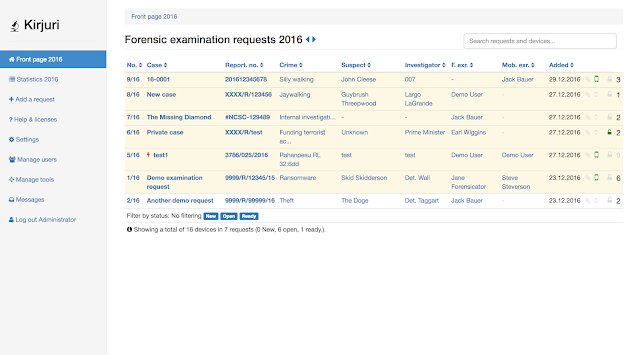
342Kirjuri – Web Application For Managing Cases
Kirjuri is a simple php/mysql web application for managing physical forensic evidence items. It is intended to be used as a...
-
 290
290LetsMapYourNetwork – Visualise Your Physical Network In Form Of Graph
It is utmost important for any security engineer to understand their network first before securing it and it becomes a daunting...
-

 411
411Botb – A Container Analysis And Exploitation Tool
BOtB is a container analysis and exploitation tool designed to be used by pentesters and engineers while also being CI/CD friendly...
-
 406
406Pixload – Image Payload Creating/Injecting Tools
Set of tools for creating/injecting payload into images. Useful references for better understanding of pixload and its use-cases: Bypassing CSP using polyglot JPEGs...
-

 340
340FudgeC2 – C2 Framework For Purple-Teaming
FudgeC2 is a campaign orientated Powershell C2 framework built on Python3/Flask – Designed for team collaboration, client interaction, campaign timelining, and...
-
 397
397Dr. ROBOT – Domain Reconnaissance and Enumeration
Introduction Dr. ROBOT is a tool for Domain Reconnaissance and Enumeration. By utilizing containers to reduce the overhead of dealing with dependencies,...
-

 437
437Mondoo – Cloud-Native Security And Vulnerability Analysis
Mondoo is infrastructure and security analytics your cloud-native applications. By removing the code literacy, we strive to make infrastructure operations and...
-
 479
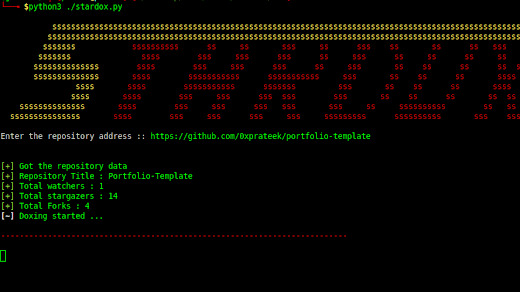
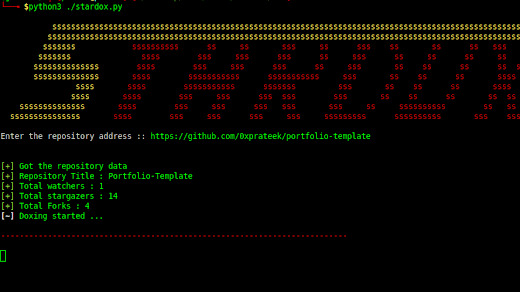
479Stardox – Github Stargazers Information Gathering Tool
Stardox is an advanced github stargazers information gathering tool. It scraps Github for information and display them in list tree view....
-
 503
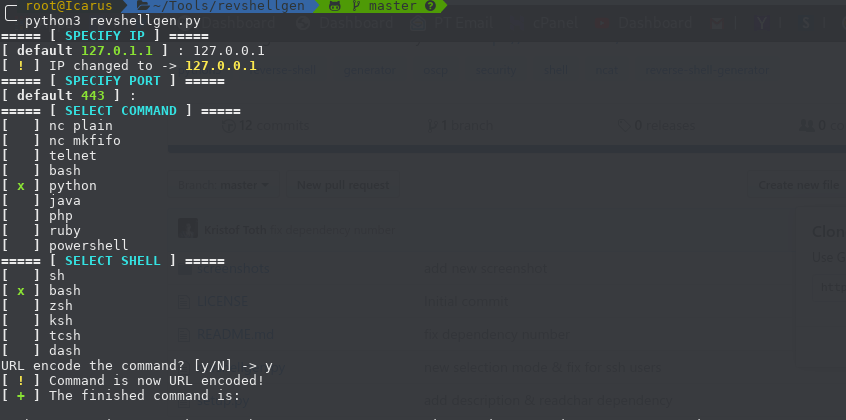
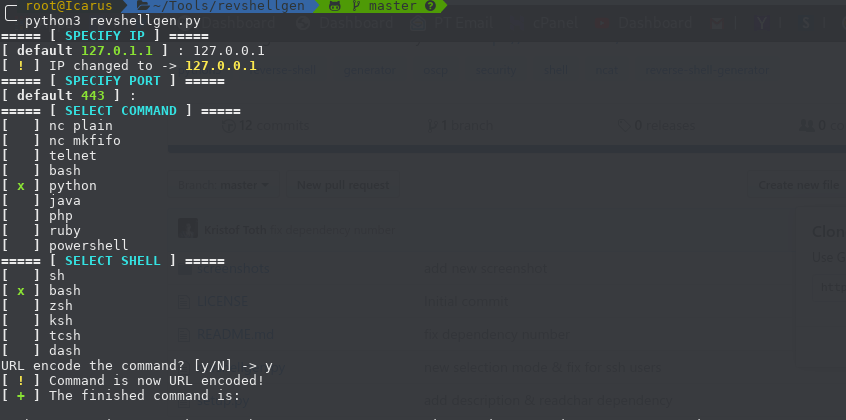
503Revshellgen – Reverse Shell Generator Written In Python
Standalone python script for generating reverse shells easily and automating the boring stuff like URL encoding the command and setting up...
-

 389
389gitGraber – Monitor GitHub To Find Sensitive Data
gitGraber is a tool developed in Python3 to monitor GitHub to search and find sensitive data for different online services such...
-
 334
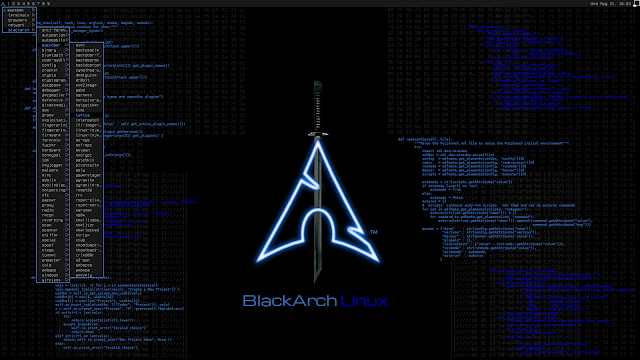
334BlackArch v2019.09.01 – Penetration Testing Distribution
BlackArch Linux is an Arch Linux-based distribution for penetration testers and security researchers. The repository contains 2336 tools. You can install...
-
 350
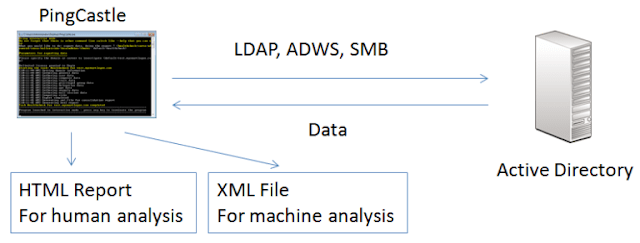
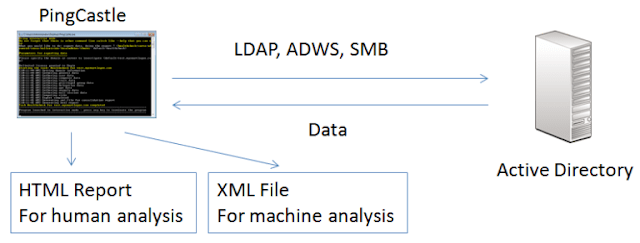
350PingCastle – Get Active Directory Security
The risk level regarding Active Directory security has changed. Several vulnerabilities have been made popular with tools like mimikatz or sites...
-

 295
295Phishing-Simulation – Aims To Increase Phishing Awareness
Phishing Simulation mainly aims to increase phishing awareness by providing an intuitive tutorial and customized assessment (without any actual setup –...
-

 385
385Stegify – Capable Of Hiding Any File Within An Image
stegify is a simple command line tool capable of fully transparent hiding any file within an image. This technique is known...
-
 366
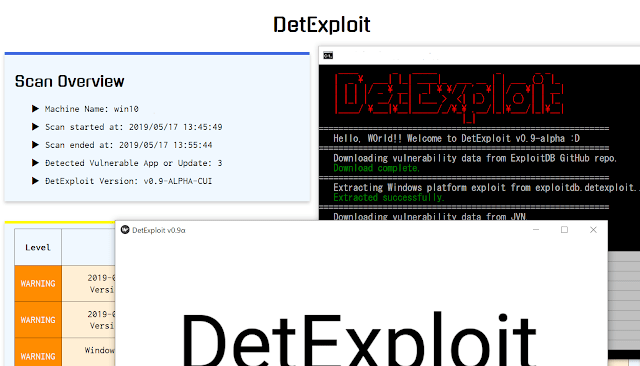
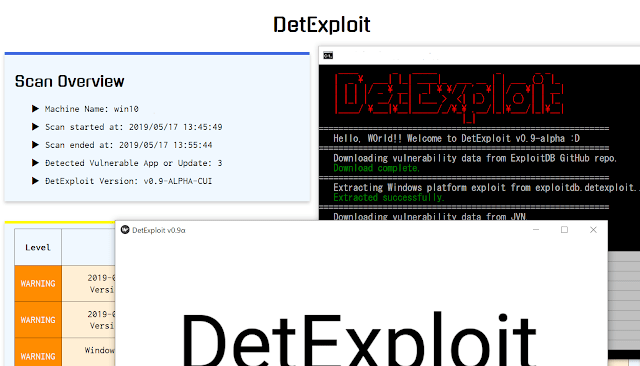
366DetExploit – Software That Detect Vulnerable Applications
DetExploit is software that detect vulnerable applications and not-installed important OS updates on the system, and notify them to user. As...
-
 349
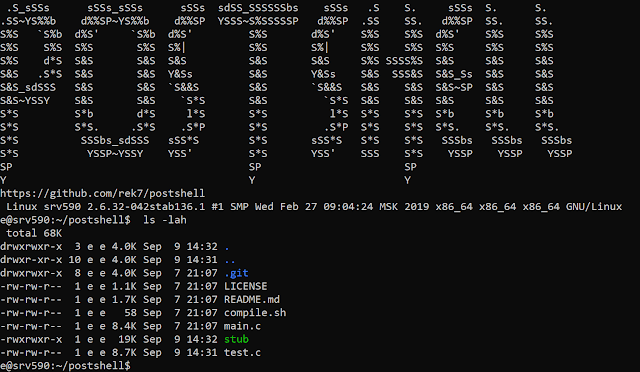
349PostShell – Post Exploitation Bind/Backconnect Shell
PostShell is a post-exploitation shell that includes both a bind and a back connect shell. It creates a fully interactive TTY...
-
 313
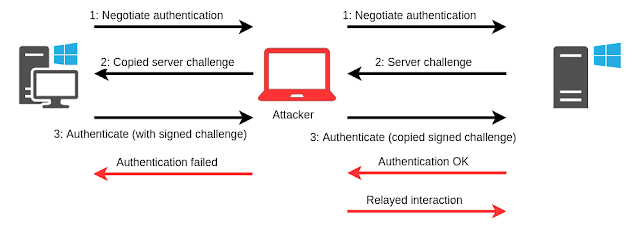
313PrivExchange – Exchange Your Privileges For Domain Admin Privs By Abusing Exchange
POC tools accompanying the blog Abusing Exchange: One API call away from Domain Admin. Requirements These tools require impacket. You can install...
-

 626
626Web Application Penetration Testing Checklist – A Detailed Cheat Sheet
Web Application Pentesting is a method of identifying, analyzing and Report the vulnerabilities which are existing in the Web application including buffer...
-

 313
313Converting Your Android Smartphone into Penetration Testing Device
Big corporations trying to improve the user experience by making everything around simplify, increasing performance and connections with “IoT’s”. Today with the...
-
 843
843Most Important Web Application Penetration Testing Tools & Resources for Hackers and Security Professionals
Web Application Pentesting Tools are more often used by security industries to test the vulnerabilities of web-based applications. Here you can find...






