Vulnerabilities
-

 305
305LTE and 5G networks could be affected by new vulnerabilities
A group of pentest researchers has demonstrated ability to passively identify session details and perform hijacking, allowing phishing attacks. According to the International Institute...
-

 229
229Zerodium pays up to $500 000 for zero-day exploits
The sale of zero-day exploits is a very profitable business that most people completely ignore. The International Institute of Cyber Security talks...
-
 206
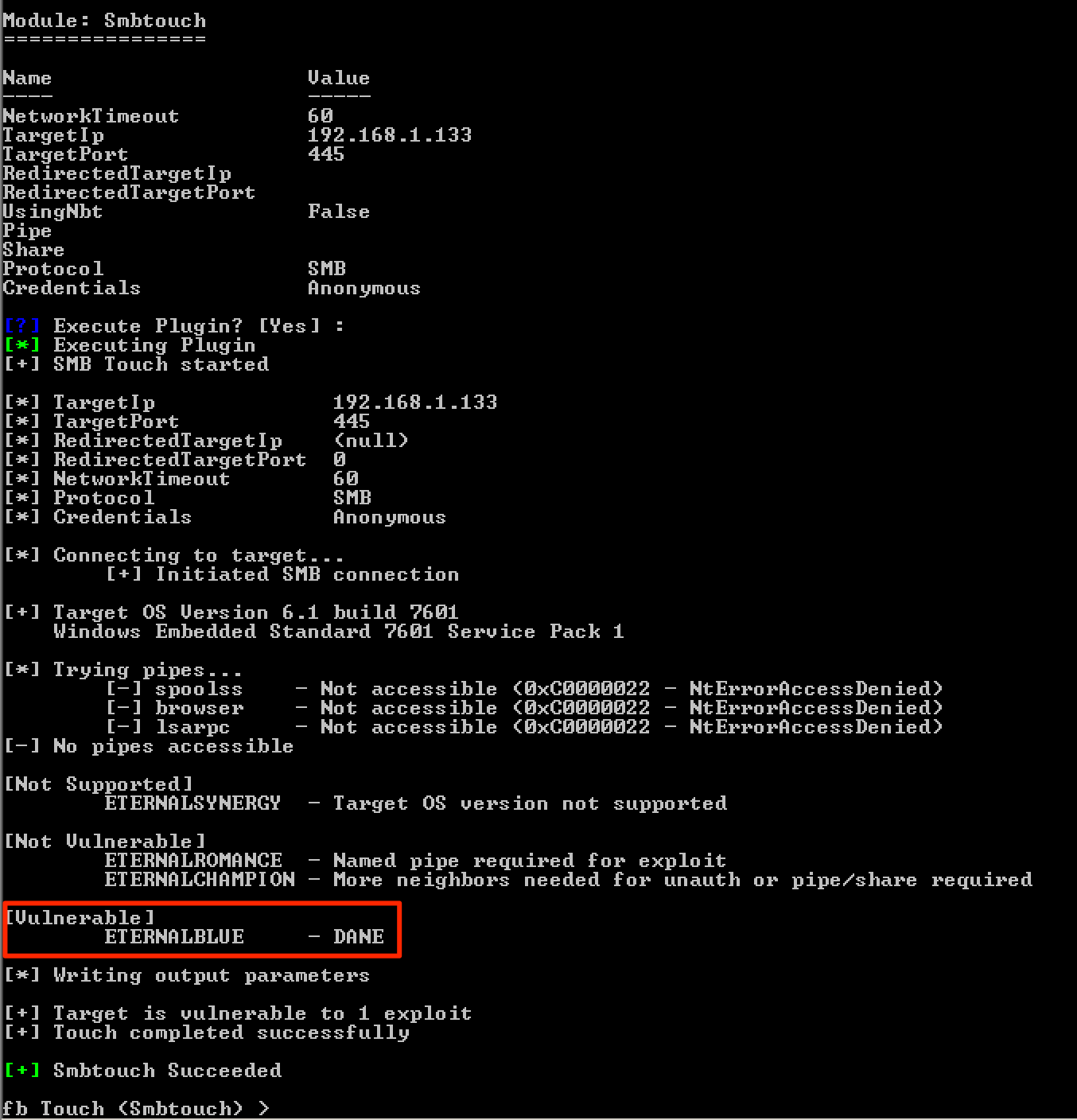
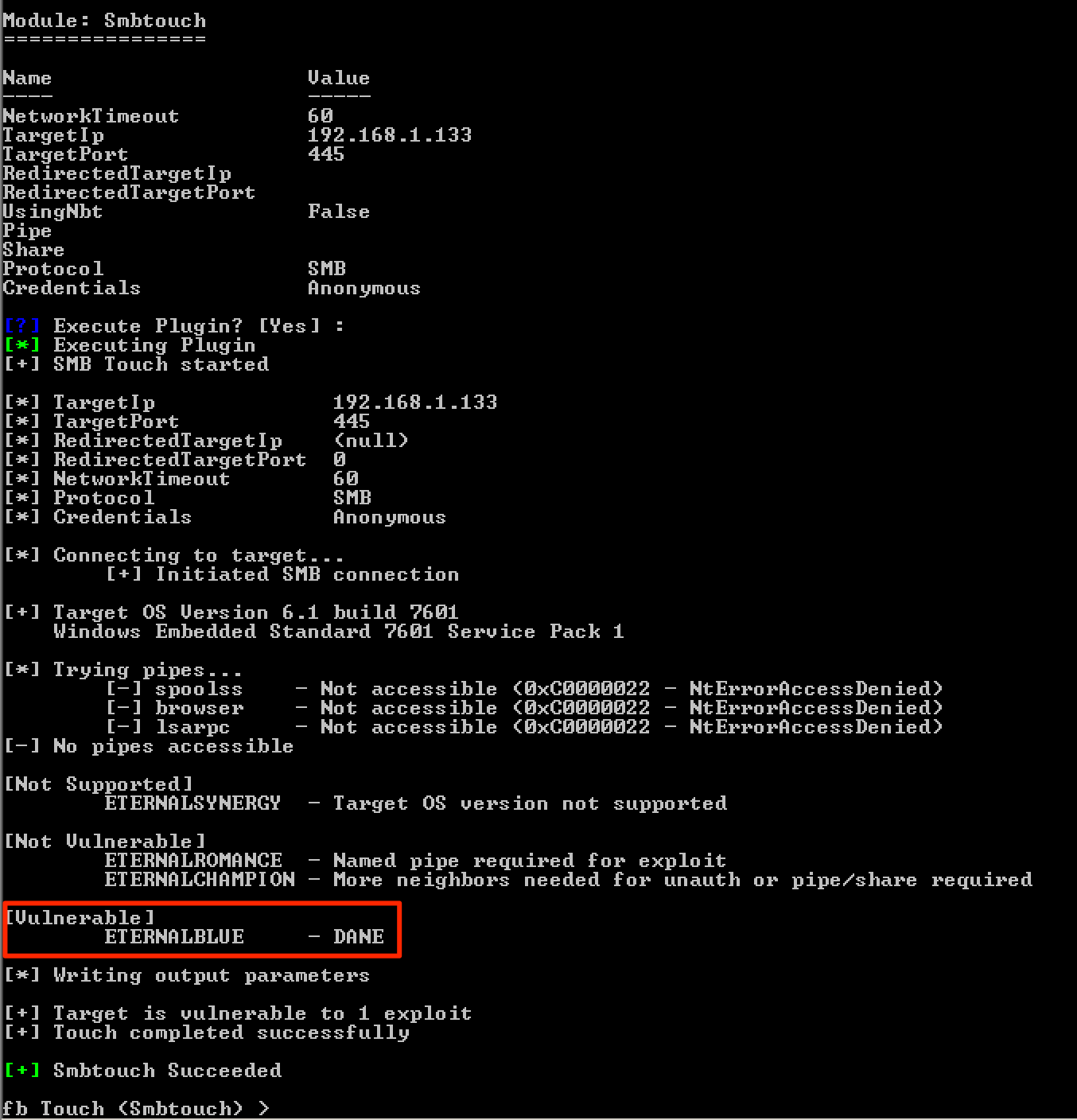
206Patching DoublePulsar to Exploit Windows Embedded Machines
During one of my engagements, I discovered some Windows devices that were affected by the MS17-010vulnerability. One of these devices caught my attention...
-

 213
213Exploited vulnerability in Cisco ASA and Firepower devices
A severe vulnerability affecting CISCO ASA and Firepower devices is being exploited after an exploit was released online, as revealed by late...
-

 284
284Microsoft Edge bug could be exploited to send your emails to malicious websites
After issuing a patch, users are encouraged to make sure they are using the latest version of the browser. According to...
-
 221
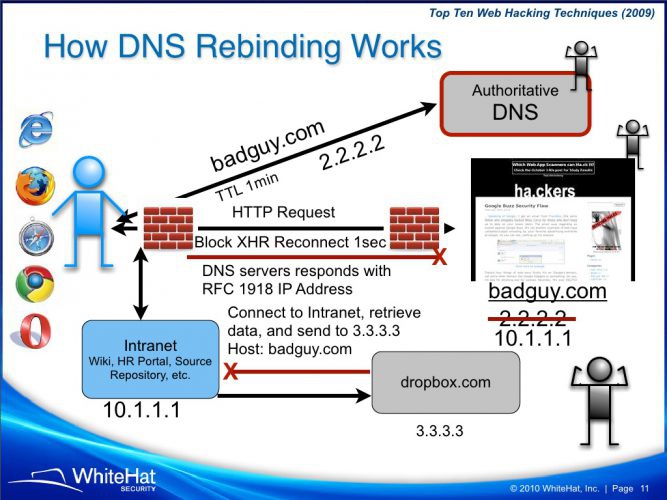
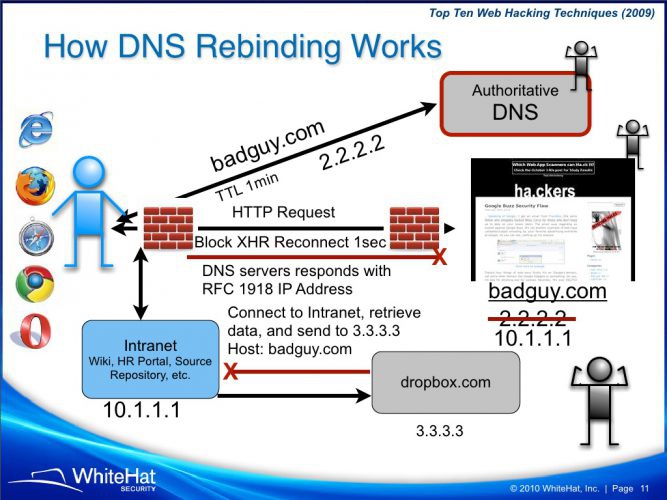
221Attacking Private Networks from the Internet with DNS Rebinding
TL;DR Following the wrong link could allow remote attackers to control your WiFi router, Google Home, Roku, Sonos speakers, home thermostats and more....
-

 292
292Cisco launches 34 update patches for different vulnerabilities, 5 of them critical
Cisco, a company dedicated to manufacturing telecommunications devices, launched patches for 34 failures in its software, including solutions for five critical vulnerabilities...
-

 411
411Cisco Released Patches for More than 30 Vulnerabilities Including the 5 Critical One’s in FXOS and NX-OS
Cisco released patches for 34 vulnerabilities affecting multiple products that include 5 critical vulnerabilities, 20 High severity vulnerabilities and 9 medium level...
-

 178
178Bug in Google Chromecast and Home devices would reveal location of users
Information technology and information security training experts have found a strange and maybe dangerous flaw in the privacy of these devices that...
-

 134
134Zip Slip vulnerability affects thousands of projects
An arbitrary file-overwrite vulnerability affects a large number of projects, researchers reveal. The flaw, known as Zip Slip by information security training...
-
 229
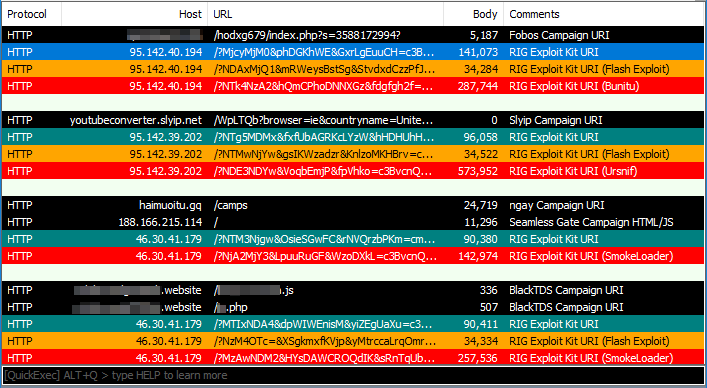
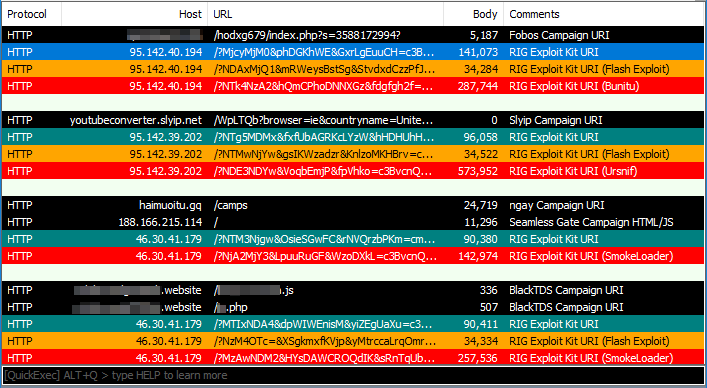
229Exploit kits: Spring 2018 review
Since our last report on exploit kits, there have been some new developments with the wider adoption of the February Flash zero-day, as well as...
-

 211
211Vulnerability in GnuPG has allowed counterfeiting of digital signatures for decades
A failure affecting GnuPG has made some of the most commonly used e-mail encryption programs vulnerable to digital signature falsification. The list...
-

 203
203Smart padlocks can be hacked in seconds
A cutting edge technology padlock, operating with fingerprint, can be opened by anyone who has a smartphone, as discovered by information security...
-

 399
399Hackers can use Cortana to break into computers with Windows 10
Cortana has security vulnerabilities when it operates on the lock screen Microsoft has launched a security update to prevent hackers from entering...
-

 247
247VMware Released Security Updates for Critical Remote Code Execution Vulnerability
VMware security updates published for its AirWatch Agent that affected by critical remote code execution vulnerability. VMware is a virtualization software which...
-

 245
245Adobe Issues Patch for Critical Flash Player Zero-day Vulnerability : Its Time to Update
Adobe has released patches for critical zero-day vulnerabilities in Adobe Flash Player 29.0.0.171 and earlier versions. The updates released for Windows, macOS,...
-
 222
222SS7 routing-protocol breach of US cellular carrier exposed customer data
40-year-old SS7 is being actively used to track user locations and communications. The US Department of Homeland Security recently warned that malicious...
-
 150
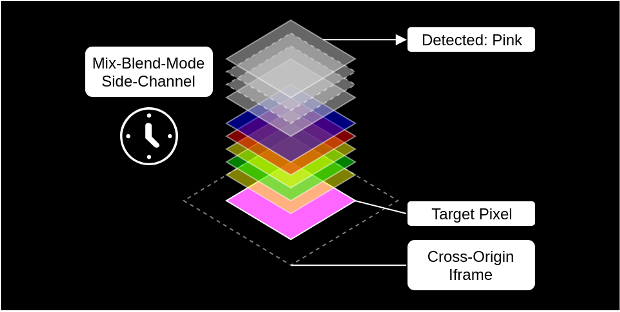
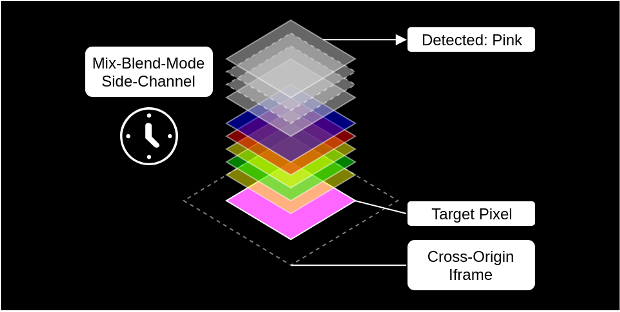
150Side-channel attacking browsers through CSS3 features
With the staggering amount of features that were introduced through HTML5 and CSS3 the attack surface of browsers grew accordingly. Consequently, it...
-
 167
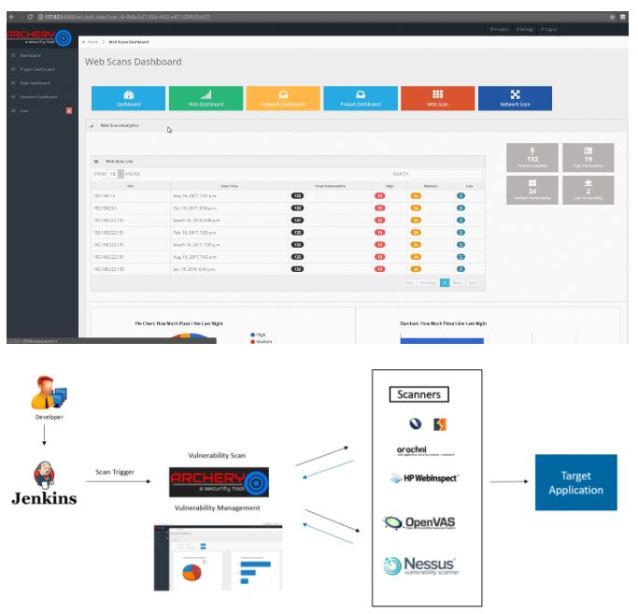
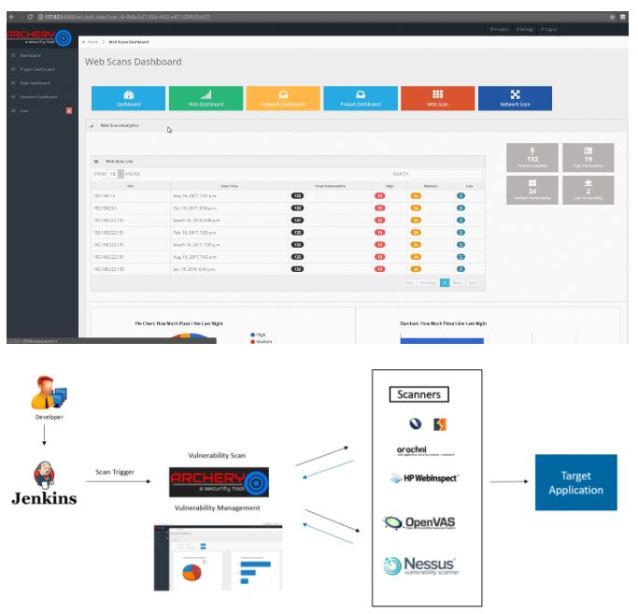
167Archery, perform scans and manage vulnerabilities with this tool
An information security expert explains that, Archery is an open source vulnerability management and evaluation tool that helps developers and evaluators perform scans and...
-

 329
329Multiple Vulnerabilities in IBM QRadar SIEM Allows Attackers to Escalate Privileges and to Execute Arbitrary Commands
Multiple Vulnerabilities found in IBM QRadar chained together allows a remote attacker to bypass authentication and to execute arbitrary commands with root...
-

 254
254D-Link DIR-620 Routers with Critical Vulnerabilities
After an investigation, security professionals have found a backdoor account in the firmware of the D-Link DIR-620 routers; this allows malicious actors...






