Vulnerabilities
-

 298
298Vulnerability in Oracle Access Manager exploited to bypass authentication and control the account of any user
Wolfgang Ettlinger of SEC Consult Vulnerability Lab, information security expert, found vulnerability in Oracle Access Manager that can be exploited remotely to bypass authentication...
-
 141
141RCE Vulnerability Over 1 Million Fiber Router Allows Attacker to Bypass all Authentication in Entire Network
Update: Now VPN Mentor has been released a user-friendly patch for affected users who can provide their WebUI URL of the router and...
-
 178
178GitHub says bug exposed some plaintext passwords
A small but unspecified number of GitHub staff could have seen plaintext passwords. GitHub has said a bug exposed some user passwords...
-
 227
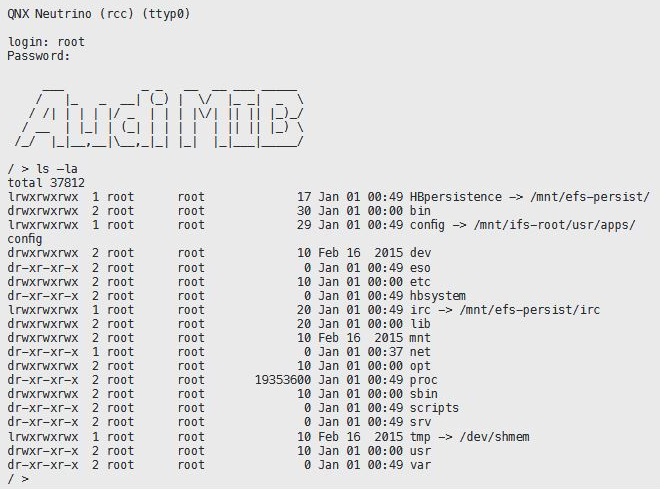
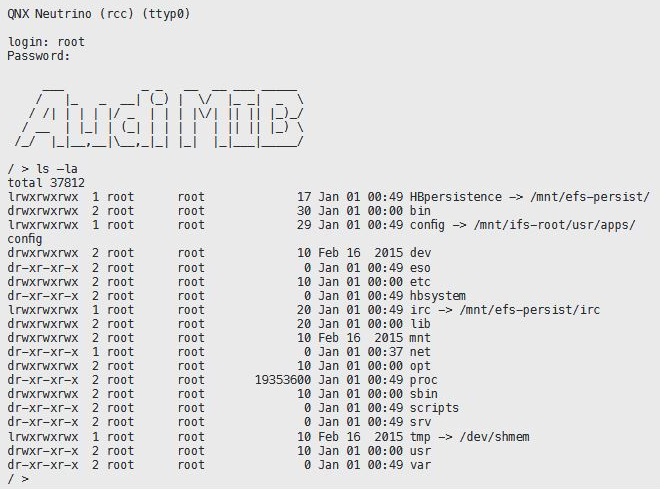
227With This Vulnerability You Can Remotly Hack Volkswagen and Audi Cars
Recently a Dutch information security company has discovered that vehicle infotainment systems (IVI) implemented in some Volkswagen Group car models are vulnerable...
-
 270
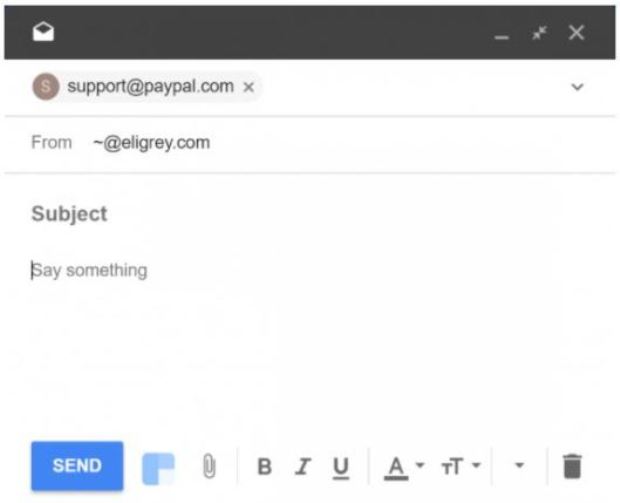
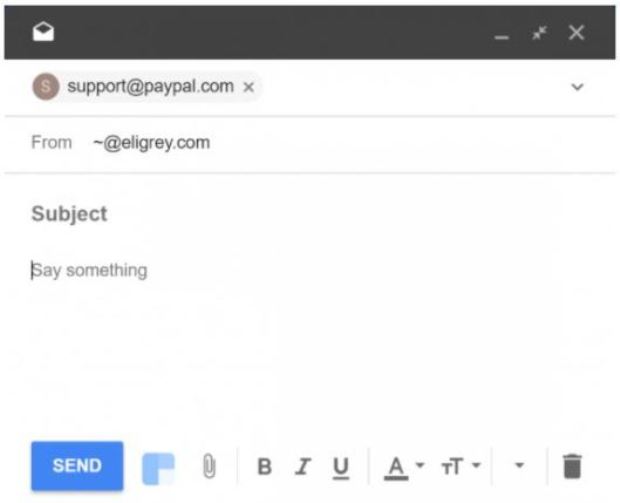
270Hack Google Inbox with a new Spoofing vulnerability
Almost a year ago, on May 4, 2017, information security researcher privately discovered and reported a spoofing vulnerability of the recipient in...
-

 249
24990% of SAP Implementations are Vulnerable to New SAP Vulnerability
For the most part, SAP implementations continue to be affected by vulnerability in the security configuration initially documented in 2005, information security...
-

 300
300150000 Drupal websites got hacked by this new vulnerability
The Drupal security team has fixed another Drupal remote code execution vulnerability, which suggests users to implement the updates offered immediately as...
-

 327
327How to find Vulnerabilities in Active Directory Settings?
An information security expert explains that Grouper is an unstable PowerShell module designed for use by pentesters and redteamers that filters the XML output...
-
 180
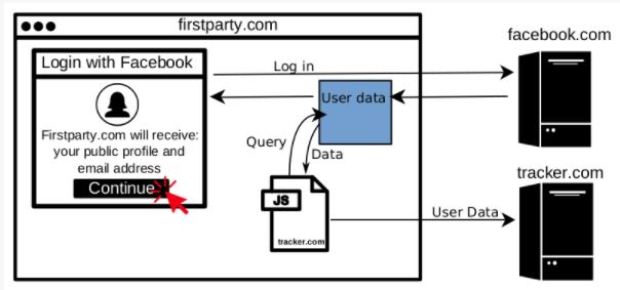
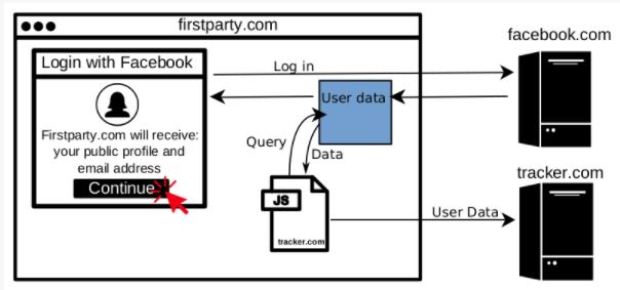
180Vulnerabilities exploited by third-party trackers to abuse Facebook Login
So far, researchers have uncovered how web trackers exfiltrate identifying information from web pages, browser password managers, and form inputs. Now, the...
-

 302
302Bug in LinkedIn allowed data to be stolen
Private profile data, like phone numbers and email addresses, could have been easily collected. According to information security experts, the flaw was found in...
-

 254
254Hackers Could hack Cisco WebEx with a malicious Flash file
Cisco has issued a critical patch to fix a serious vulnerability (CVE-2018-0112) in its WebEx software that could be exploited by remote...
-

 234
234Vulnerability in Drupal CMS used for cryptomining
Drupal beside some things is also an open-source content management system (CMS) just like WordPress and is used by over a million...
-
 185
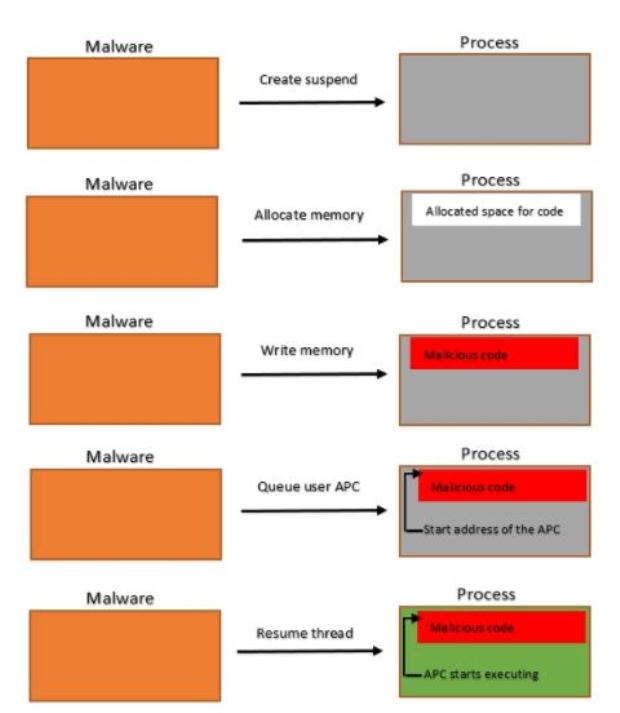
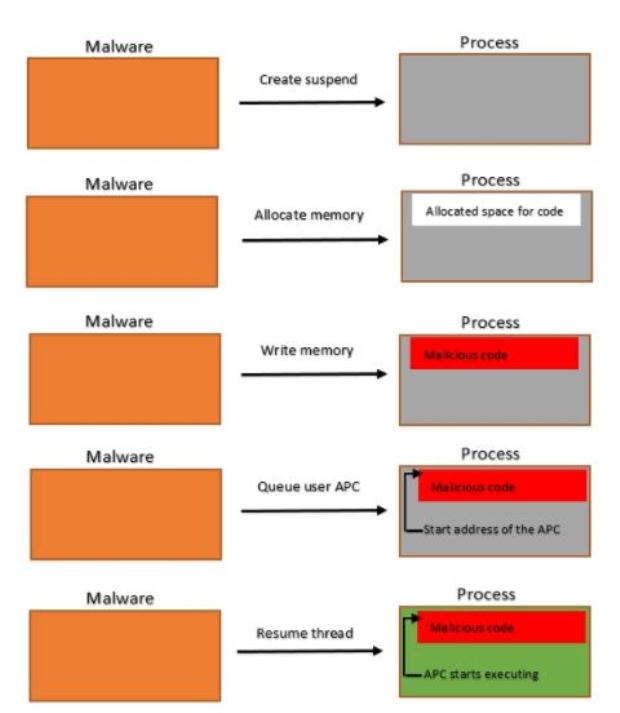
185New ‘Early Bird’ Code Injection Technique
This injection technique allows the injected code to run before the entry point of the main thread of the process, thereby allowing...
-
 209
209Vulnerability in Intel SPI allows attackers to erase or modify the BIOS or UEFI
Intel has addressed vulnerability in the configuration of several CPU series that allow an attacker to alter the behavior of the chip’s...
-

 220
220Is your Android phone a ‘toxic hellstew’ of vulnerabilities? There’s an app to help you find out
Just because Android tells you it’s patched and everything is safe doesn’t mean it is. But there’s an app to help you...
-

 260
260JShielder Automated Hardening Script for Linux Servers
JSHielder is an Open Source tool developed to help SysAdmin and developers secure their Linux Servers in which they will be deploying...
-
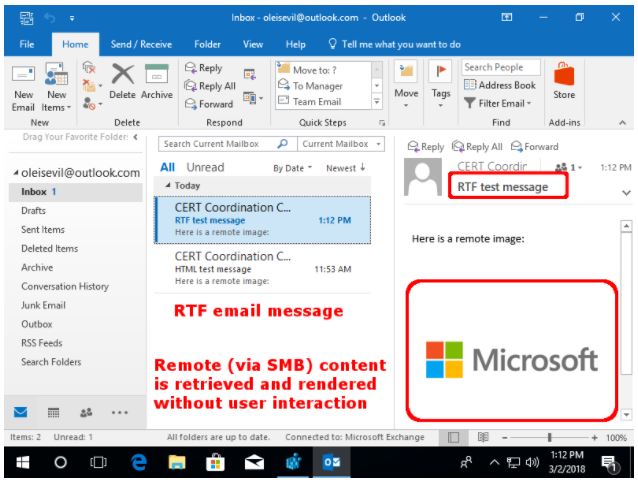
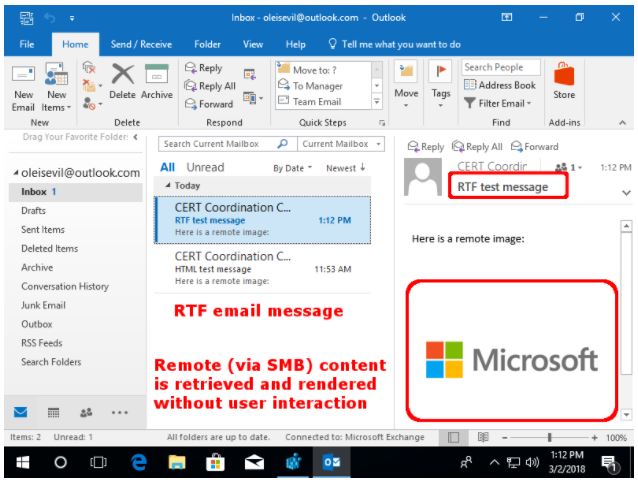 224
224Vulnerability in Outlook let hackers to steal password hashes
Most people rely on Outlook email address for work-related as well as personal tasks. Unfortunately, Outlook may not be as secure as...
-

 212
21217 Years Old Hacker Finds Critical Flaw in Signal App that Allows Anyone to Bypass Password & Screen lock in iOS
A 17 Years old Hacker who inspired by Edward Snowden discovered a critical vulnerability in Signal app that allows anyone to Bypass...
-
 273
273What happened to the Internet: attack on Cisco switches
Let’s say that your internet connection suddenly went down or, perhaps, you cannot reach your favorite website. There’s a reason for that;...
-
 163
163Massive Cyber Attack Across the World Against ISP’s & Data Centres : More than 200,000 Cisco Switches Hacked
Biggest Hackers Group Performing Massive Cyber attack against internet service providers, data centers around the world by compromising Cisco switches. Hackers compromising more than 200,000...
-

 211
211A load of Intel CPUs have Spectre v2 flaw that can’t be fixed
Intel won’t fix Meltdown nor Spectre for 10 product families covering 230-plus CPUs. Intel has issued new “microcode revision guidance” that reveals...






