Latest News
-
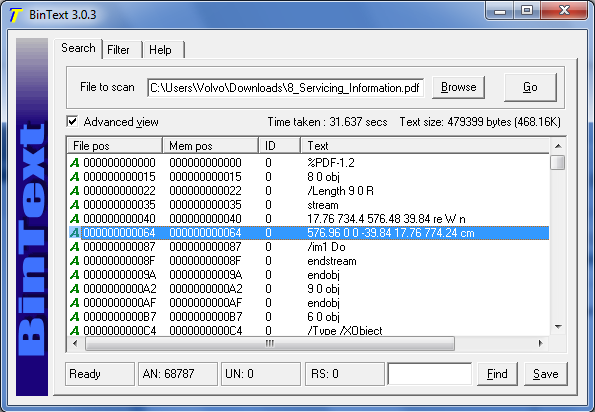
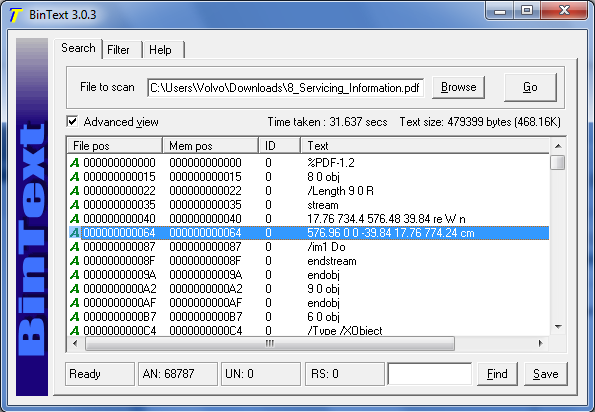 339Binary Analysis
339Binary AnalysisReverse Engineering Tool – BinText
A small, very fast and powerful text extractor.It can extract text from any kind of file and includes the ability to find...
-

 120Vulnerabilities
120VulnerabilitiesPatch now! Flash-exploitin’ PC-hijackin’ attack spotted in the wild by Huawei bods
Adobe squeezes out one last batch of security fixes for 2015. Adobe has issued new versions of Flash to patch a load...
-
 437News
437NewsTop 15 Cyber Attacks and Security Breaches in 2015
With 2016, just a few days away, let’s have a flashback of the top 15 security incidents that took place this year....
-

 219Lists
219ListsThese Are The Most Popular Websites In 11 Biggest Countries
Short Bytes: BI has spotted a very attractive graph in Goldman Sachs’ yearly compilation. This graph tells us the most popular websites...
-

 272Geek
272GeekHolidays Offer Scam on Facebook Drops Malware on User PCs
Crooks are targeting English and Portuguese speaking Facebook users with “Holidays special offers malware scam.” It’s that time of the year when...
-

 290Data Security
290Data SecurityNorth Korea’s Linux (Red Star OS) is a nut hard to crack
North Korea is known as an authoritarian state but researchers have found their technological systems to be following the same path. Researchers...
-

 223Geek
223GeekRuby 2.3.0 Released With New Features And Performance Improvements
Image: fossBytes Short Bytes: Ruby development team has released Ruby 2.3.0 – the first stable release of Ruby 2.3 series. It comes...
-

 346News
346NewsResearcher Finds 191 Million US Voter Registration Records Online
Chris Vickery, a security researcher who is known for finding leaked databases online claims he has found US voter registration records of 191...
-

 350Cyber Crime
350Cyber CrimePolice Dogs Trained To Sniff Out Hard Drives Coming For Pedophiles
After using malware on pedophiles, law enforcement authorities in the United States have decided to add Hard-Drive Sniffing Dogs in their units...
-

 313Banking
313BankingRansomware rearing its ugly head, goes after business
Ransomware is the latest tool in the cybercriminal’s arsenal, but it has to date largely been used to target consumers. Could it...
-

 258Data Security
258Data SecurityHow the Internet of Things Got Hacked
THERE WAS ONCE a time when people distinguished between cyberspace, the digital world of computers and hackers, and the flesh-and-blood reality known...
-

 108Data Security
108Data SecurityChina passes controversial anti-terrorism law to access encrypted user accounts
China’s legislature unanimously passed a controversial anti-terrorsim law on Sunday despite months of objections from major tech firms and Washington alike. Among...
-

 250Lists
250ListsTop 10 Most Pirated Movies And TV Shows of 2015
Short Bytes: In the list of top 10 most pirated movies and TV shows of 2015, Interstellar tops the chart with over...
-
 369Geek
369GeekBest Features Of Solus OS — The Fastest Booting Linux Distro
Images | Project Solus Short Bytes: Solus OS, pegged as the fastest booting Linux OS, was released in December. Shipping with Linux...
-

 186Incidents
186IncidentsHackers DDoS Coinbase, website down
Coinbase website DDoSed by hacker group. A hacker group consisting of two hackers, @L7Crew and @An0CBR claimed to have brought down the Bitcoin exchange website Coinbase. The...
-

 242Hacked
242HackedBanks Mum Over Credit Card Flaw: Because Fraud Is a Profitable Business?
Short Bytes: A new flaw in the card transaction has been revealed by the German security experts. This flaw, capable of cloning...
-

 231Data Security
231Data SecurityHack Like a Pro: Using Sparta for Reconnaissance
As all of you know, reconnaissance is critical to being successful in a pentest or hack. Recon is where we gather all...
-
 113Data Security
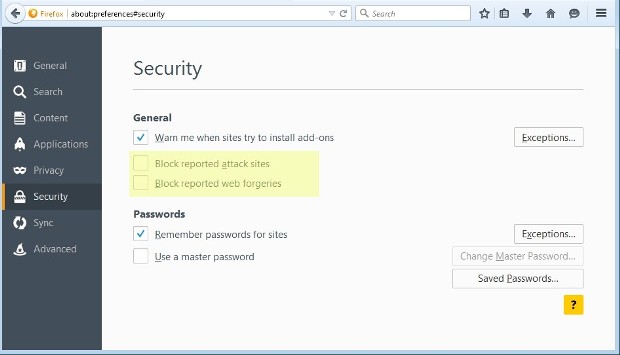
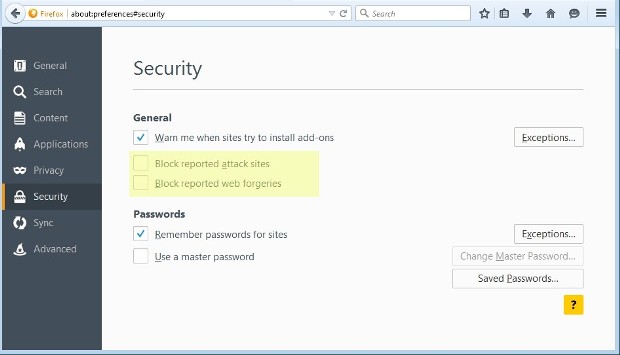
113Data SecurityAdware Sneakily Turns Off Firefox Safe Browsing
Mintcast adware uses user.js settings files for persistence.Two PUPs (Potentially Unwanted Programs) are secretly turning off Safe Browsing support in Firefox to...
-
 197News
197NewsAnonymous Claims To Avert Possible Terrorist Attack On Italy
The online hacktivist Anonymous claimed to have averted a terrorist attack in Italy planned by the so-called Islamic State (ISIS) or Daesh...
-
 277Cyber Events
277Cyber EventsAustralian Government Portal Asks Users To Get Rid of Two-Factor Authentication
MyGov, a portal used for managing various Australian government services is asking users to turn off their two-factor verification while traveling abroad. Portal’s administrator...



