Latest News
-
 236Data Security
236Data SecurityTor Project To Launch Bug Bounty Program
Tor would soon be launching a bounty program which would reward any person who finds a vulnerability in one of the most...
-
 234Geek
234GeekMicrosoft is Collecting Your Encryption Keys, Here’s How to Delete it
It is possible to prevent encryption keys from reaching Microsoft’s Servers – Learn how: It is a known fact that for all...
-

 364Cyber Crime
364Cyber Crime5 things you need to know about social engineering
Social engineering plays an important part in a significant number of cyberattacks, however big, small or sophisticated the crime is. However, little...
-

 85Malware
85Malware‘BackStab’ can hack and steal private data on your mobile phone without you knowing it
Palo Alto Networks unravels ‘BackStab’ technique which allows criminals to get access and steal your private data, via unprotected phone backups. The security...
-
 163Data Security
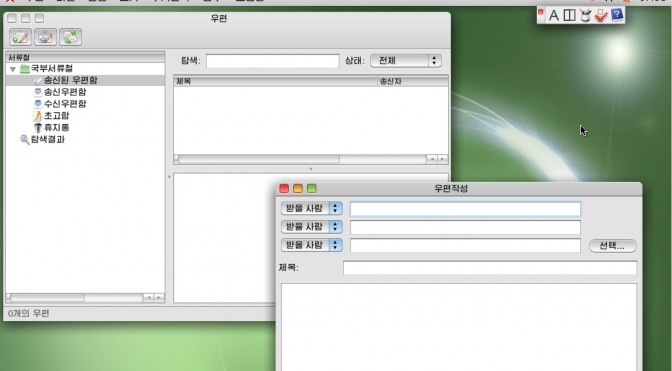
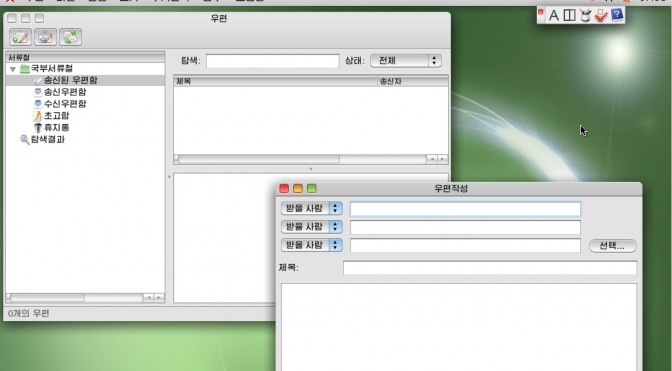
163Data SecurityNorth Korea’s Linux-based Red Star OS is as oppressive as you’d expect
North Korea’s homegrown computer operating system mirrors its political one – marked by a high degree of paranoia and invasive snooping on...
-
 224Geek
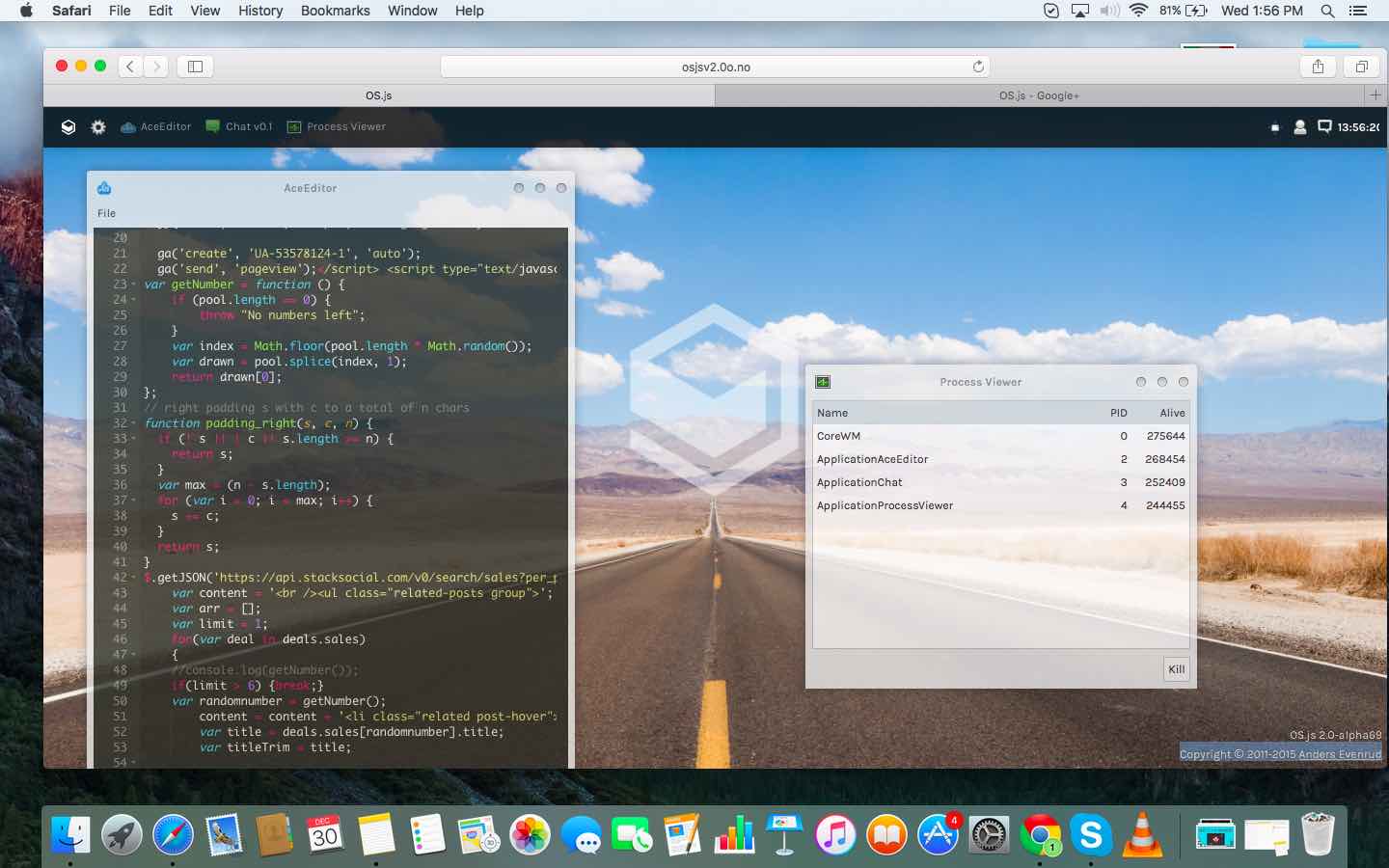
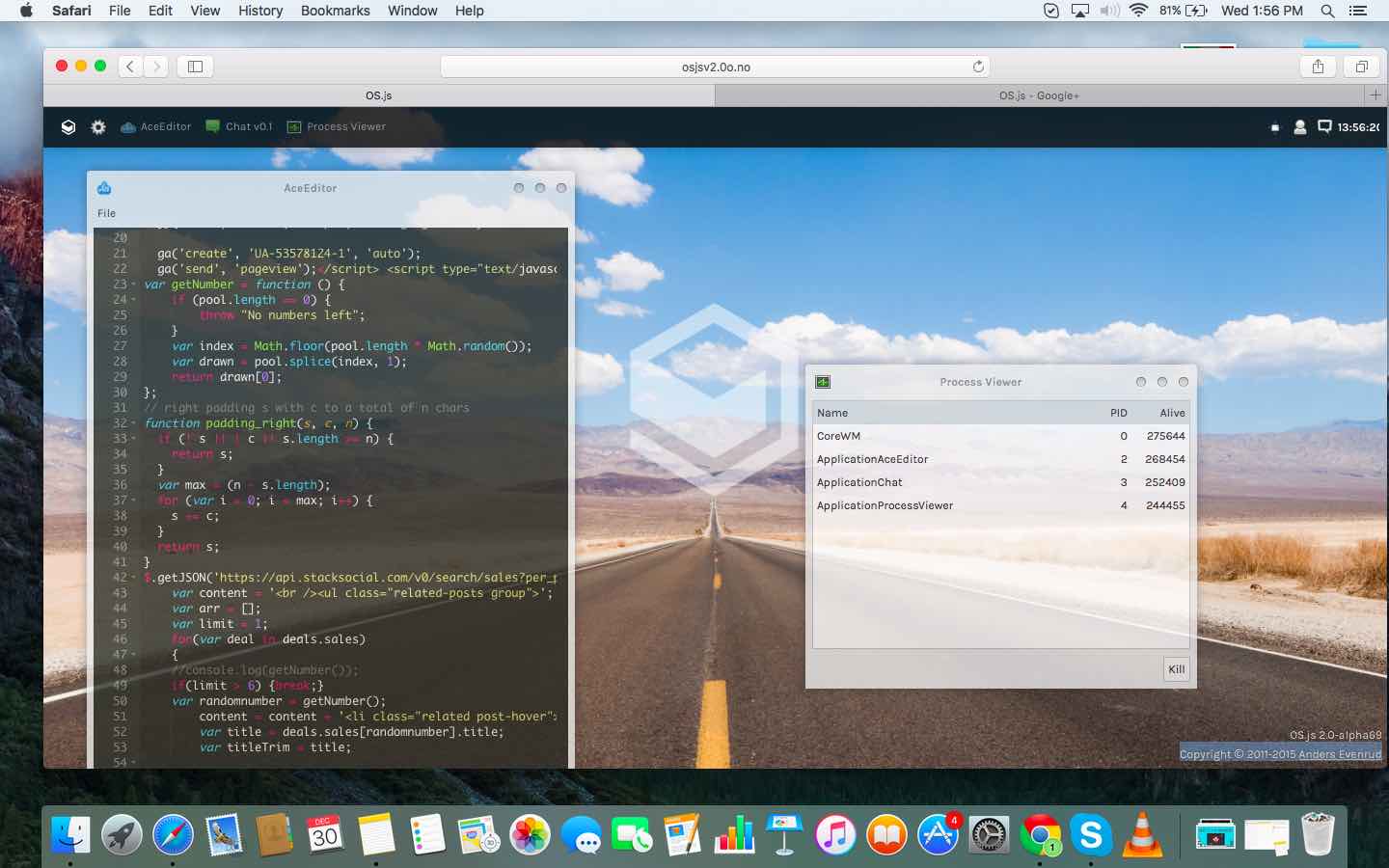
224GeekOS.js Is A New Javascript Based Open Source Operating System Running In Your Browser
Image | fossBytes Short Bytes: OS.js is a free and open source operating system that runs in your web browser. Based on...
-

 181Data Security
181Data SecurityGadget Hacks’ Favorite Must-Have Android Apps of 2015
Here at Gadget Hacks, we spend countless hours scouring the web to find the most interesting apps as they make their debuts,...
-

 89Data Security
89Data SecurityMicrosoft may have your encryption key; here’s how to take it back
It doesn’t require you to buy a new copy of Windows. As happens from time to time, somebody has spotted a feature...
-
 118Malware
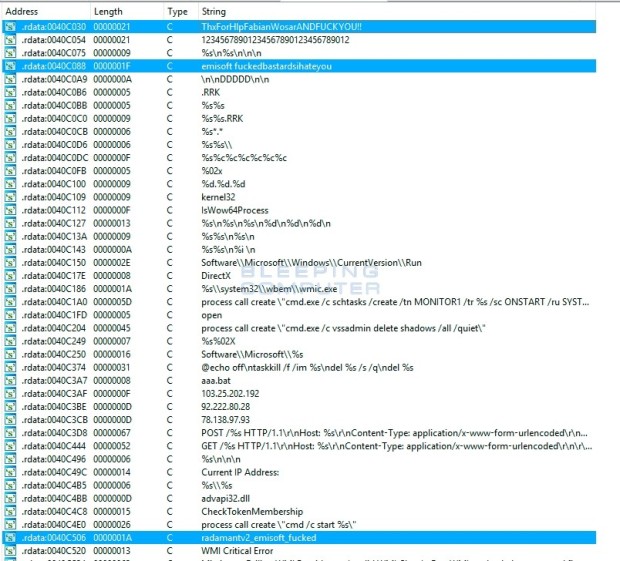
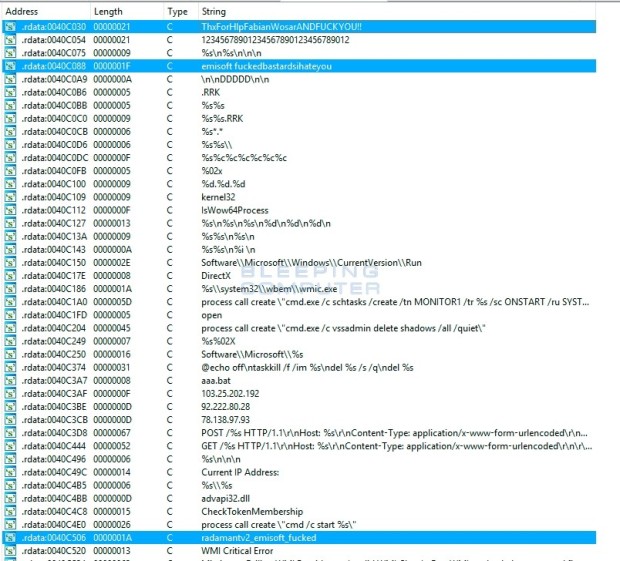
118MalwareRadamant Ransomware Author Has a Fit When Researcher Cracks His Encryption
Radamant ransomware v1 and v2 are now decryptable. Fabian Wosar, security researcher at Emsisoft, has managed to crack the encryption algorithm for the...
-

 144Data Security
144Data SecurityProxyBack Malware Converts Your PC Into Proxy
Palo Alto Networks researchers have identified a unique malware that infects home PCs and transforms them into internet proxies using HTTP tunnel....
-

 203News
203NewsHacked Website of Connecticut University Caught Spreading Malware
Simple DNS hijacking enables attackers to distribute Fake Infected Flash Player at UConn website. On Sunday, the official web portal of the...
-
 336Geek
336GeekAndroid Malware Poses As Google App To Ditch Security Apps
Android Malware poses as Google app to infect Android Devices and to Block Security Apps. Recently, security researchers at Symantec Corp identified...
-

 332News
332NewsSomeone Hacked A Freeway Sign To Display Pro-Donald Trump Message
On Christmas Day Caltrans Freeway sign in Corona Displayed Especial Message for Donald Trump. On Christmas Day, Caltrans Freeway sign in Corona...
-

 150Incidents
150IncidentsMisconfigured Database Exposes Details of 191 Million US Voters
Researchers could not track down the database’s owner.Security researcher Chris Vickery has identified a misconfigured database that contains the personal details of...
-
 178Data Security
178Data SecurityYandex worker stole search engine source code, tried selling for just $28K
An employee of Russia’s Internet giant Yandex, Dmitry Korobov, stole the source code of its search engine and tried to sell it...
-

 107Vulnerabilities
107VulnerabilitiesCVE-2015-8562 – 16,000 Daily Attacks on vulnerable Joomla servers
Experts at Symantec discovered that hackers quickly take advantage of CVE-2015-8562 remote code execution to compromise Joomla servers. Joomla recently patched the CVE-2015-8562...
-

 261Hacked
261HackedISIS Terrorist Attack On Italy Blocked By Anonymous Hackers, Group Claims
Short Bytes: Anonymous hacktivist group has claimed to block a possible ISIS terror attack on Italy. While Anonymous hasn’t released any evidence to...
-

 237Hacked
237HackedHacker Discovers 191 Million American Voters’ Database Leak
Short Bytes: Recently an open US voter database leak was discovered by Chris Vickery, a white hat hacker. This database contains information...
-

 323Hacked
323HackedBest Free Android Antivirus For Your Smartphone, According To AVTest
Short Bytes: Here is a list of 25 best android Antivirus that were put on test by AVTest, a company specialized in...
-

 231Data Security
231Data SecurityCommon payment processing protocols found to be full of flaws
Stealing PINs and pillaging bank accounts are both trivial. Credit card users could have their PINs stolen, and merchants could have their bank...



