Latest News
-

 310Hacked
310HackedAndroid Malware Hides as MS Word File, Sends Data To Hacker
Short Bytes: Attackers are now using an android malware app which camouflages itself as a Microsoft Word document. The malware once triggered, scans...
-

 186Hacked
186HackedNow Chat Anonymously with Tor Instant Messenger
Short Bytes: The Tor Project has announced the release of the beta version of its Tor Messenger that allows you to chat...
-

 315Vulnerabilities
315VulnerabilitiesHow to Build a Portable Hacking Station with a Raspberry Pi and Kali Linux
Cracking Wi-Fi passwords, spoofing accounts, and testing networks for exploits is all fun enough, but if you want to take the...
-
 222Malware
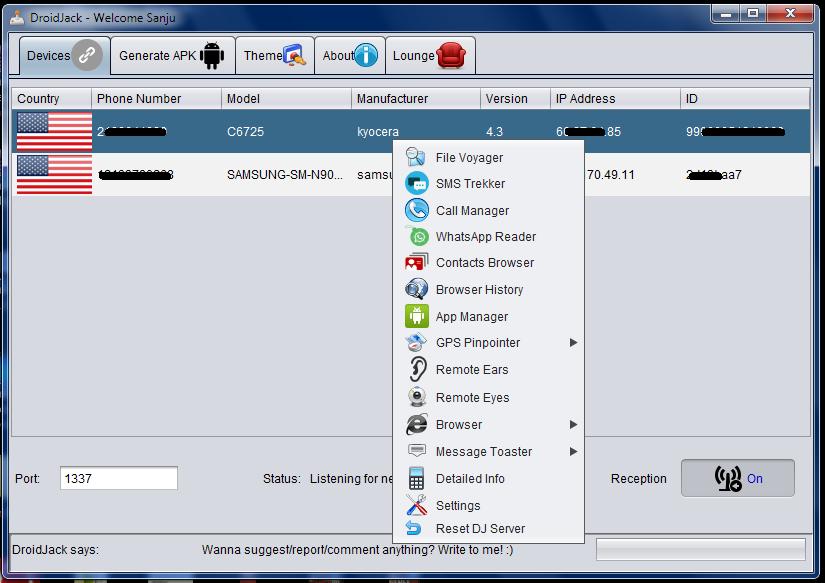
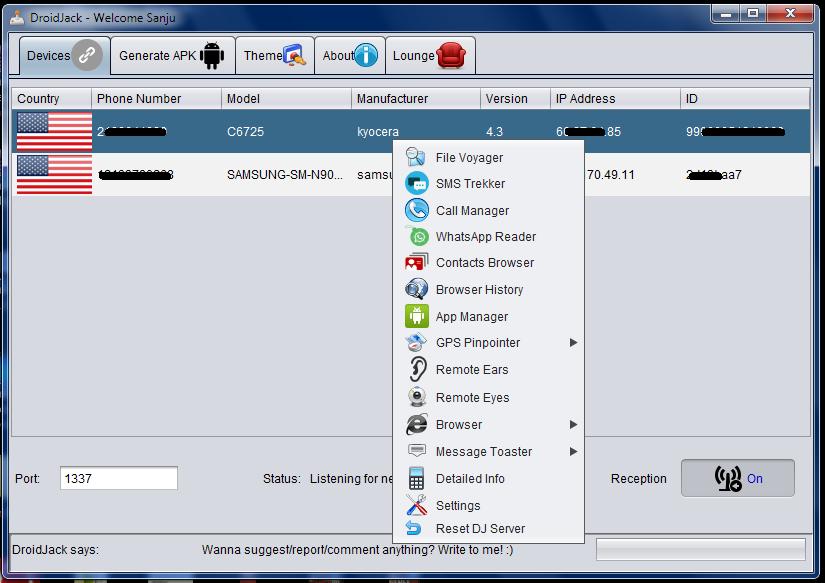
222MalwareEuropean Police Agencies declare war on DroidJack RAT
Authorities in several European countries announced they have coordinated an operation to arrest criminals using the popular DroidJack RAT. Android RATs are becoming...
-

 181Incidents
181IncidentsThousands stolen identities of Britons available on the Darkweb
600k customer identities have been stolen in 2014 and according to government officials thousands of Britons data available for sale in the...
-

 103Vulnerabilities
103VulnerabilitiesChikdos cross-platform DDoS botnet hit SQL servers worldwide
Experts at Symantec have discovered a new variant of the Chikdos DDoS-Trojan that is targeting MySQL servers worldwide. There is a malware...
-

 195Malware
195MalwarePolice raid homes across Europe over DroidJack malware
Thirteen homes in Germany were raided as part of the operation – Image by Thinkstock Police have raided homes in five European countries...
-
 135Incidents
135IncidentsWebhosting company loses 13 million plaintext passwords, says “thanks for your understanding”
There’s another data breach to report – and it’s a big one, affecting approximately 13 million customers of the “free” web hosting...
-

 88Cyber Crime
88Cyber CrimeUsing DroidJack to spy on an Android? Expect a visit from the police
Law enforcement agencies across Europe have searched homes this week, as part of an international crackdown against users of a notorious piece...
-

 323News
323NewsHacker Leaks 13 million emails and passwords in 000Webhost Breach
A security researcher (Troy Hunt), who owns the website (haveibeenpwned) have discovered a possible breach of webhosting service 000Webhost servers. Basically, hunt’s...
-

 257Lists
257Lists30 Toughest Questions Asked In Apple Interviews
Short Bytes: Apple boasts one of the best workforces in the tech world with employees ranging from a software engineer to a...
-

 189Geek
189GeekFacebook, WhatsApp Users can be tracked down by hackers
A group of researchers have demonstrated how locations of Facebook and WhatsApp users can be exposed by a security flaw in 4G networks....
-

 431Password
431Password11‑year‑old sets up cryptographically secure password business
An 11-year-old girl from New York has set up her own business selling cryptographically secure passwords, using a technique known as diceware.
-

 129Cyber Crime
129Cyber CrimeThe great car hacking debate
Can cars be hacked remotely or is the idea of remotely hackable cars still only a hypothetical threat? Evidence is presented to...
-
 202Hacked
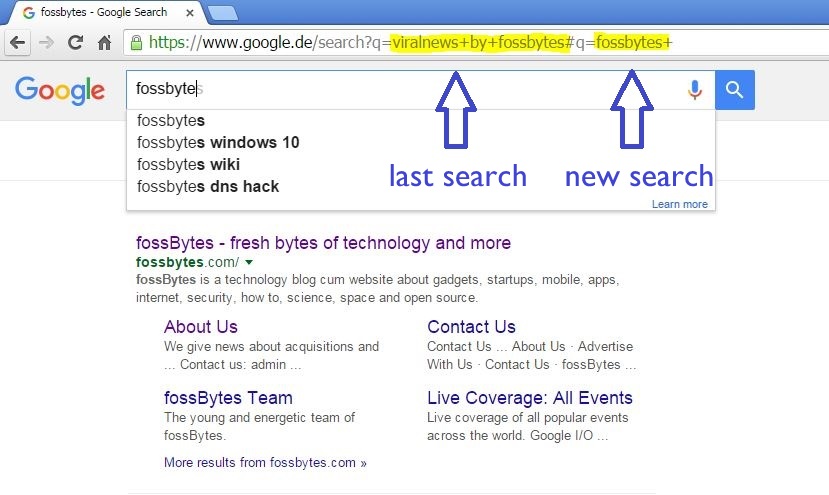
202HackedHow Innocent Copy-Paste Leaks Your Previous Embarrassing Google Searches
Short Bytes: Our innocent habit of copy-paste is reflected when we send the URLs of search pages as some reference to our...
-
 195Malware
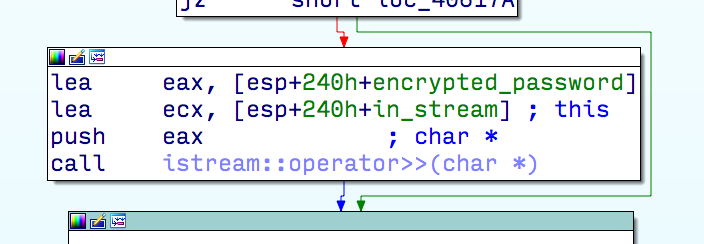
195MalwareMulti-stage exploit installing trojan
ESET researchers receive and analyze thousands of new malware samples every day. Earlier this year, one of them caught our attention because...
-
 94Data Security
94Data SecurityGoogle HTTP Search, yes, it is still possible
Google began to implement SSL on its search engine back in 2010. First on its own domain name, then as a...
-

 163Vulnerabilities
163VulnerabilitiesFewer IPsec VPN Connections at Risk from Weak Diffie-Hellman
A challenge has been made against one of the conclusions in a potentially blockbuster academic paper on cryptographic weaknesses that may be...
-

 178Vulnerabilities
178VulnerabilitiesJaguar car hack in New Zealand
A Jaguar XFR may have been stolen using hacking techniques increasingly seen on keyless cars. This unidentified thief did not have the...
-

 289Cyber Events
289Cyber EventsAnonymous Vows To Leak Personal Information of 1,000 KKK Members
The online hacktivist Anonymous is planning to leak personal information of around 1000 members of the white supremacist Christian organization the Ku Klux Klan...



