Latest News
-
 98Vulnerabilities
98VulnerabilitiesAcademics Find Critical Flaws in Self-Encrypting Hardware Drives
Some consumer-grade, self-encrypting external hard drives are littered with security vulnerabilities that render their encryption an afterthought. An academic paper published in...
-

 233Cyber Events
233Cyber EventsBack to the Future II: 13 Technologies That Became Reality in 2015
How many of you have watched the sci-fi film’s sequel “Back to the Future II”? Do you know the time machine on...
-

 188Geek
188GeekMicrosoft Debuts Its First Release of Homemade SSH for Windows
Short Bytes: Working to fulfill its promise, Microsoft has released the first build of the Windows Powershell version of SSH tool. The...
-
 226News
226NewsHackers Transform Malware into Chrome Lookalike Browser
Researchers have discovered a malware that takes over Chrome as a browser and looks quick similar to chrome in every aspect. The...
-

 175Malware
175MalwareMalware Is Using the Dark Web to Stay Hidden
The dark web is well known as a space where anything can be bought or sold: guns, drugs, stolen data, and extreme...
-
 119Privacy
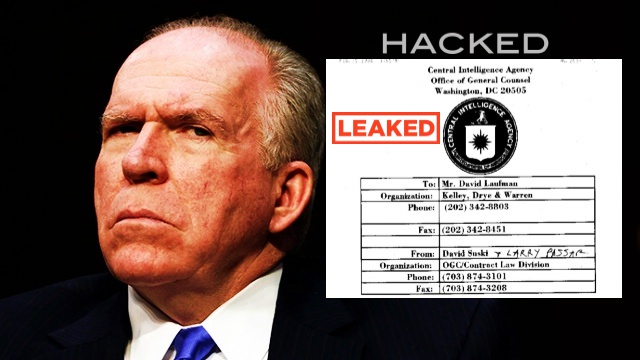
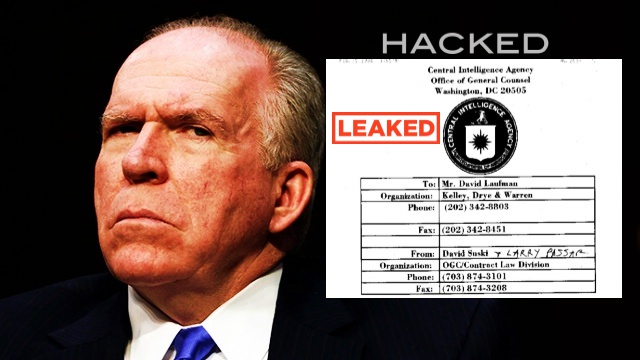
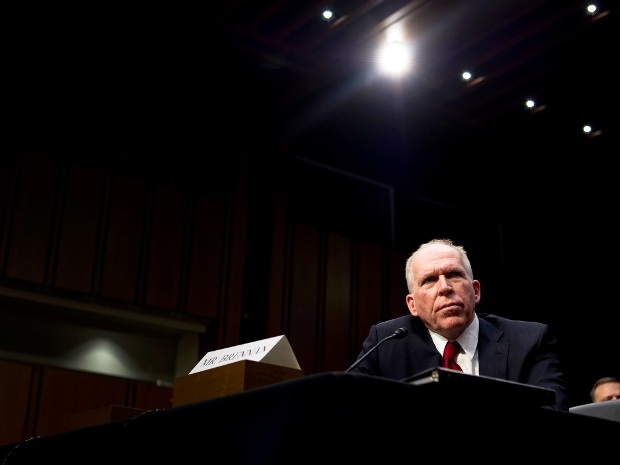
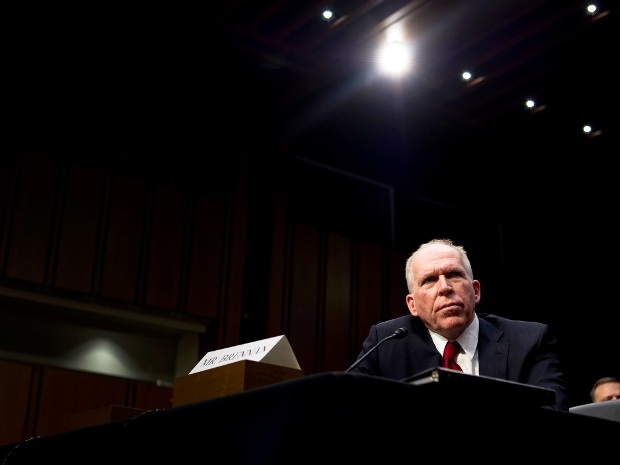
119PrivacyCIA director’s personal email account ‘breached by teen’
It has been claimed that the director of the CIA has had his personal email account breached by a teenager, with social...
-
 271Hacked
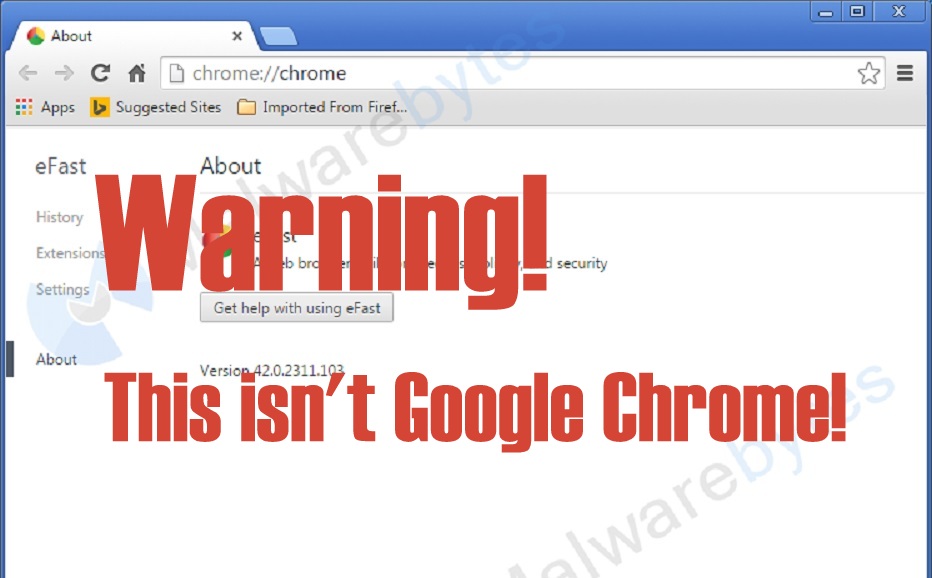
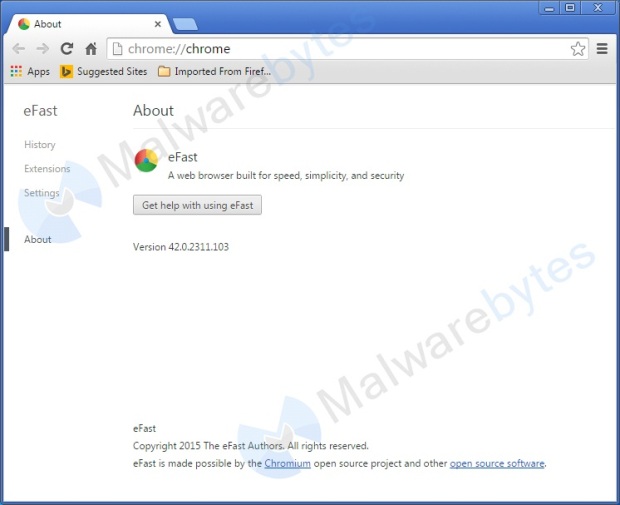
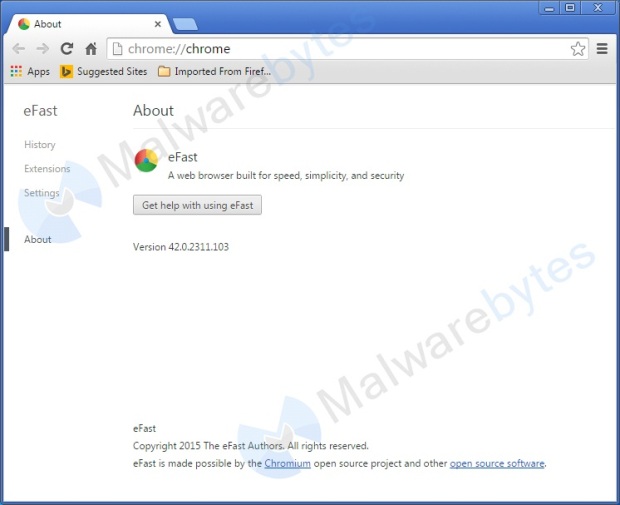
271HackedThis Malware Deletes Your Chrome Browser and Replaces It With a Fake One
Short Bytes: A new malware named eFast Browser looks just like Google Chrome. This malware deletes Google Chrome and replaces by installing...
-
 321News
321NewsPro-Palestinian High School Students Hacked CIA Boss John Brennan’s Email
Some high school students are claiming to have hacked the email account of CIA’s director John Brennan. After hacking into the account,...
-
 192Hacked
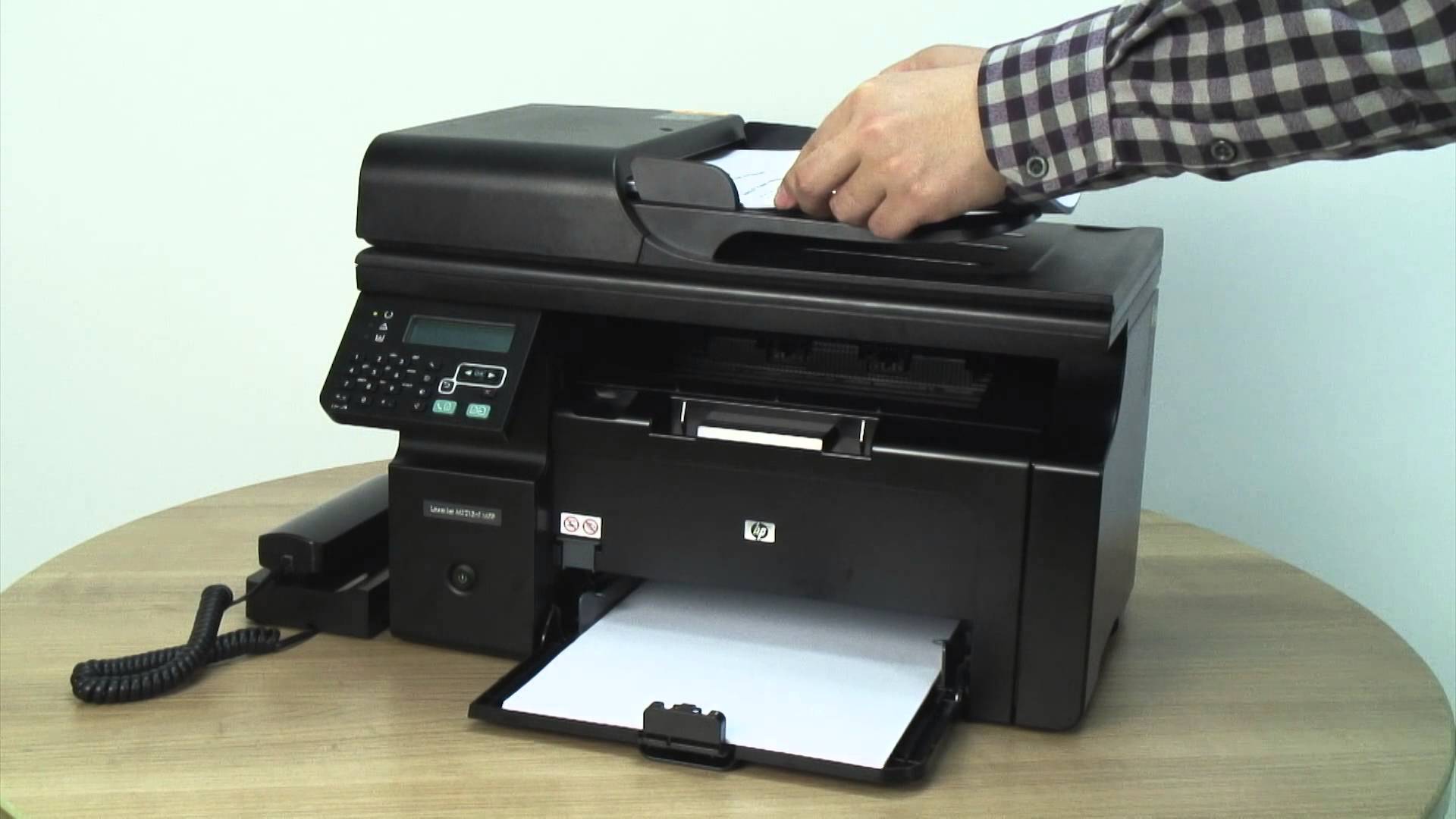
192HackedThis Secret Code in Your Printer is Helping Governments to Spy On You
Short Bytes: According to a latest EFF research, it’s possible that you own printer is leaking the important information about you to...
-

 166Vulnerabilities
166VulnerabilitiesInsecure Internet-Connected Kettles Help Researchers Crack WiFi Networks Across London
Unbelievable Breaking News: IoT kettles are insecure. Security researchers at Pen Test Partners have found a security vulnerability in the iKettle Wi-Fi Electric...
-

 355How To
355How ToNow Boost Your WiFi Signal With A Beer Can
Short Bytes: Out of the box thinking proves more valuable than exhaustive drudgery. Depicted in this amazing lifehack, is one example that...
-

 164Hacked
164HackedHow An Attacker Can Kill Your Phone and PC by Making It Older and Some “MAGIC”
Short Bytes: The researchers at NYU have revealed a way of attacking electronic devices by accelerating the aging of electronic chips. The...
-
 138Malware
138MalwareTricky new malware replaces your entire browser with a dangerous Chrome lookalike
This malicious browser looks and acts just like Chrome–except for all the pop-up ads, system file hijacking, and activity monitoring. Security researchers...
-

 152Data Security
152Data SecurityX-Ray Scans Expose an Ingenious Chip-and-Pin Card Hack
THE CHIP-ENABLED CREDIT card system long used in Europe, a watered down version of which is rolling out for the first time...
-
 113Incidents
113IncidentsTeen Who Hacked CIA Director’s Email Tells How He Did It
A HACKER WHO claims to have broken into the AOL account of CIA Director John Brennan says he obtained access by posing...
-
 168Geek
168GeekSecurity Agencies Eager to Get Hold of User Data: Microsoft’s Transparency Report
Microsoft announced the launch of a new transparency website in order to provide free access to the transparency reports published by the...
-
 195Lists
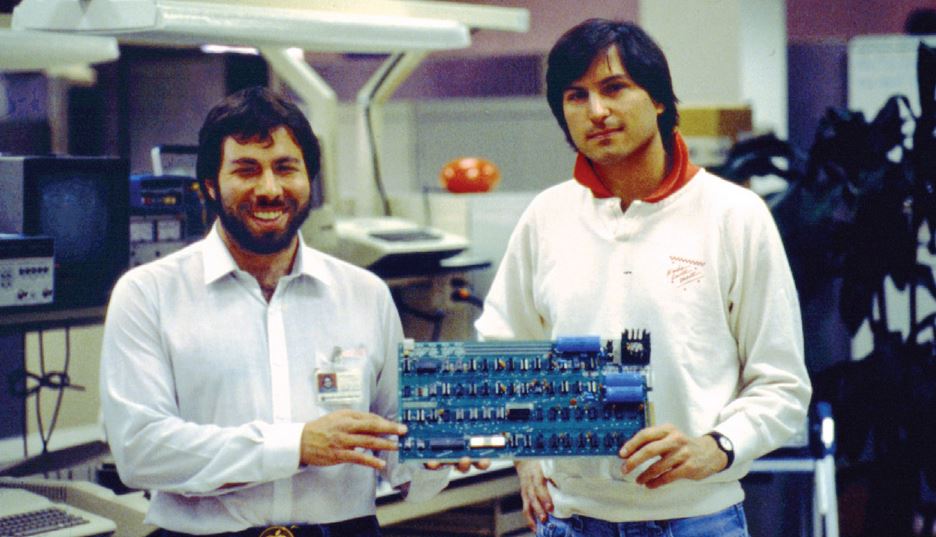
195ListsWho Were the First 10 Employees Of Apple and What Happened to Them?
Short Bytes: Each of the first 10 employees of Apple had made outstanding contributions to Apple in the field of design, funding,...
-
 177News
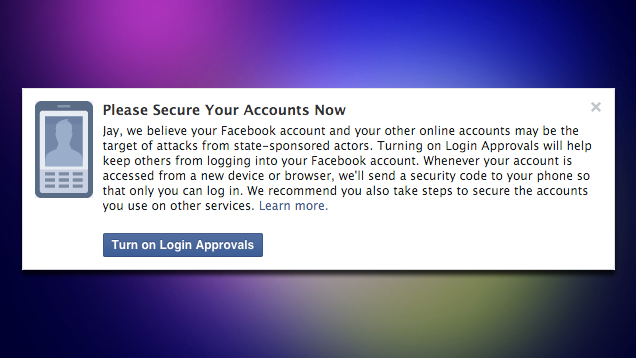
177NewsFacebook Will Warn You If It Thinks a Government Is Attacking Your Account
If you haven’t enabled two-factor authentication on Facebook, you should. If Facebook thinks someone has attempted to access your account, it will...
-
 127Geek
127GeekFacebook will notify you if the government is trying to get into your account
Facebook accounts are notorious for being hacked, either through poor passwords or phishing scams. So to help keep its users safe, the...
-

 211Vulnerabilities
211VulnerabilitiesMagento Websites Exploited in Massive Malware Distribution Campaign
A recently discovered zero-day bug may be at fault.Security researchers from both Sucuri and Malwarebytes have observed a recent massive malware distribution...



