Latest News
-
 274Hacked
274HackedInternet Inventor Vint Cerf and Experts Suggest 5-Points to Improve WiFi Router Security
Short Bytes: The FCC is on the receiving end over its proposed rules to alter WiFi routers to make them secure as...
-

 193Geek
193GeekHere are few things you should know about Facebook privacy before it’s too late
Facebook is a great platform for those who are looking for new friends, finding old ones or to promote their business. In...
-

 191Incidents
191IncidentsUltraDNS Server Problem Pulls Down Websites, Including Netflix, for 90 Minutes
UltraDNS, a web content delivery service, went down Thursday afternoon, taking with it a number of popular websites, including Netflix and Expedia....
-
 272Hacked
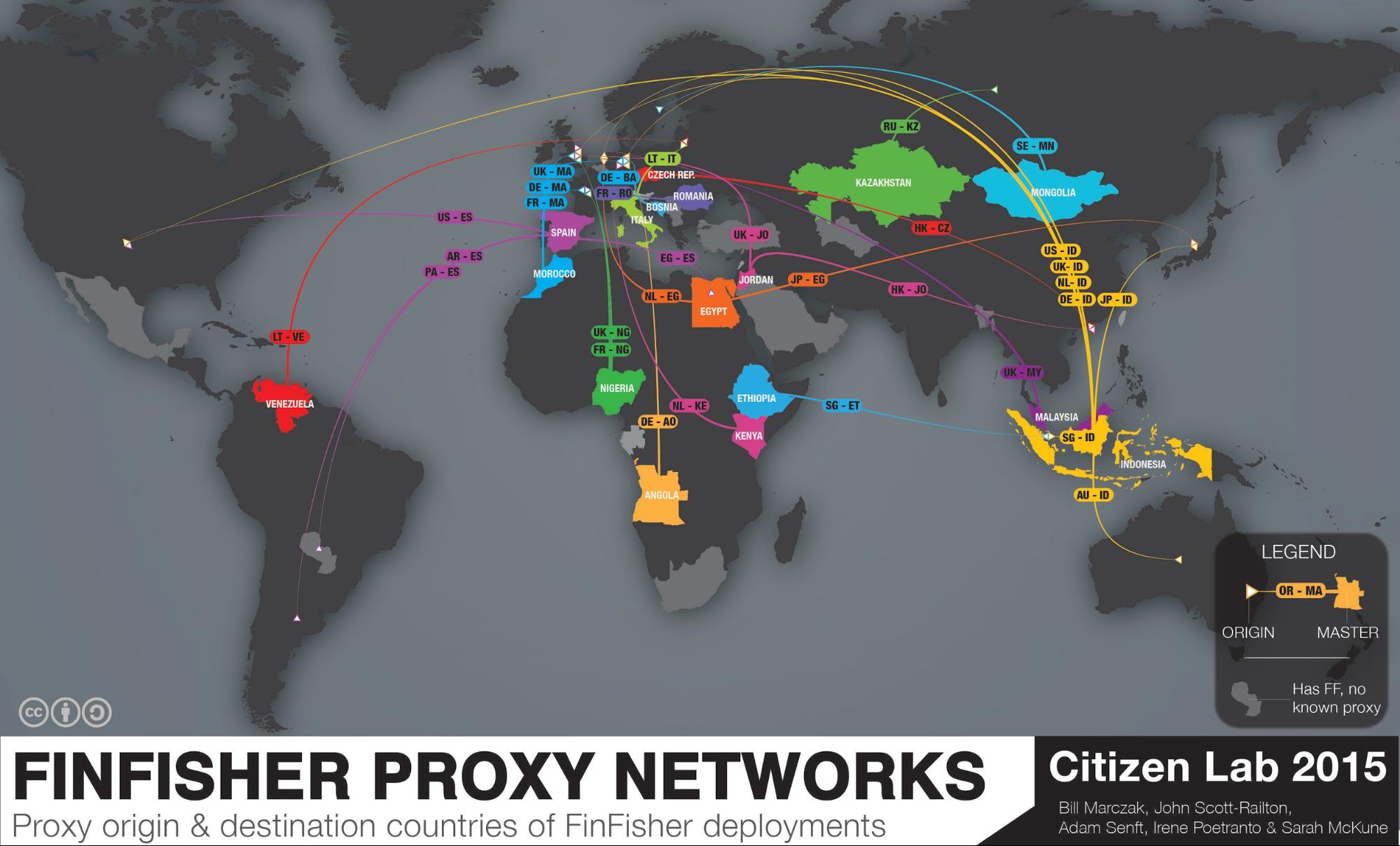
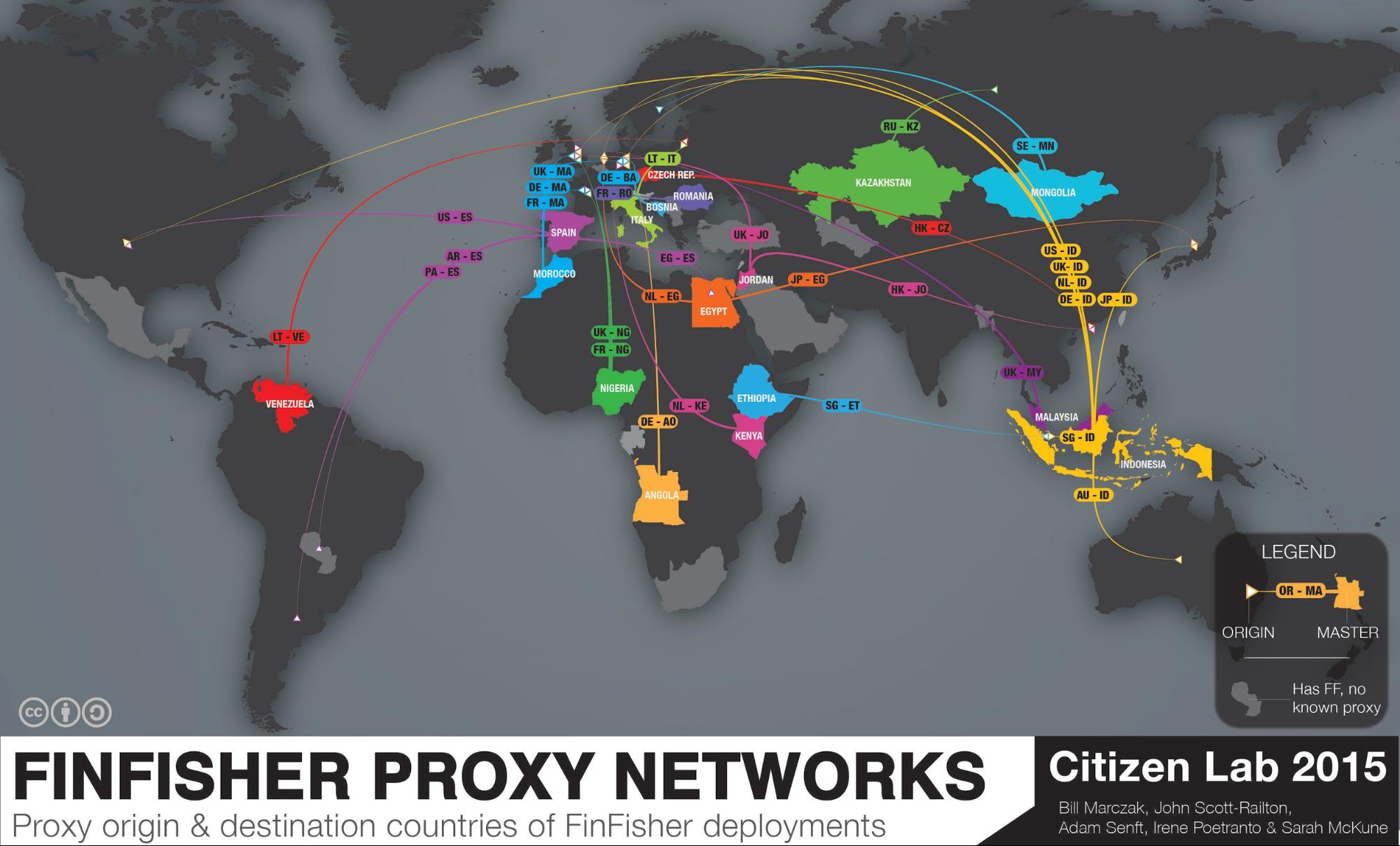
272HackedThis Nearly “Impossible to Trace” Spyware is Used by 32 Governments to Spy on You
Short Bytes: In 2015, the infamous spyware FinFisher is spread in 32 countries to perform advanced citizen surveillance. Citizen Lab, a security watchdog,...
-
 175Data Security
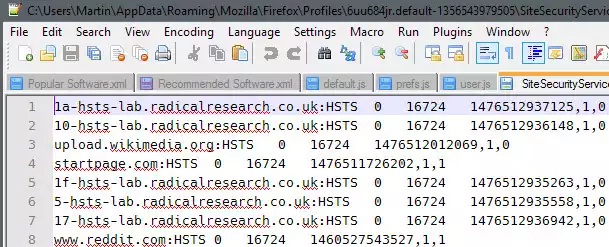
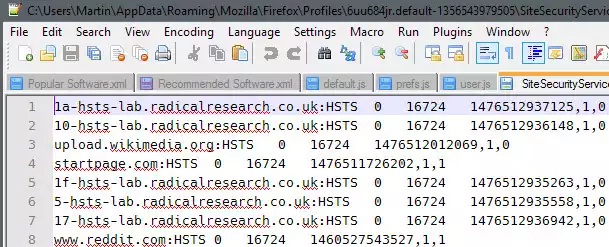
175Data SecurityHow to prevent HSTS tracking in Firefox
HTTP Strict Transport Security (HSTS) was designed to help secure websites (those using HTTPS) by declaring to web browsers that they should...
-

 170Hacked
170HackedFacebook Scans Your Phonebook To Guess Who You Are Dating Online
Short Byte: In a bizarre incident, Facebook users are reportedly seeing increasing friend suggestions of the people they have dated before through...
-

 195Lists
195ListsBest Flying Cars of The Future, Pick Your Ride
Short Bytes: Flying cars dream would soon change into a reality. So, get ready and pick your ride in advance. Good luck...
-

 194Vulnerabilities
194VulnerabilitiesWordPress Fixes Critical Stored XSS Error in Akismet
Developers at Automattic, the parent company behind the blogging platform WordPress, fixed a nasty stored cross-site scripting error this week in Akismet,...
-

 75Data Security
75Data SecurityBrolux trojan targeting Japanese online bankers
A banking trojan, detected by ESET as Win32/Brolux.A, is targeting Japanese internet banking users and spreading through at least two vulnerabilities: a...
-

 132Data Security
132Data SecurityHow the NSA can break trillions of encrypted Web and VPN connections
Researchers show how mass decryption is well within the NSA’s $11 billion budget. For years, privacy advocates have pushed developers of websites,...
-

 166Geek
166GeekHackers show Google Now and SIRI can be hacked via Radio waves
Hacking SIRI and Google Now silently from 16feet away now possible via Headphones, claim ANSSI Researchers. French researchers at the government’s information...
-
 269Surveillance
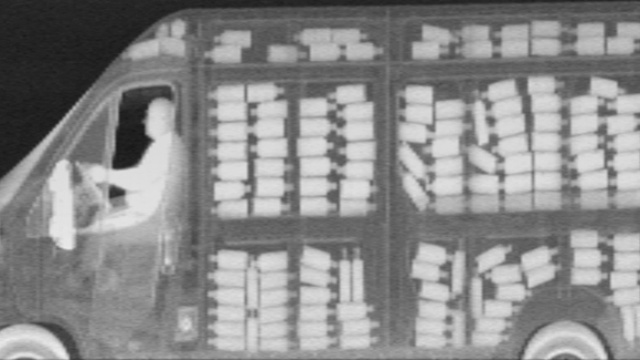
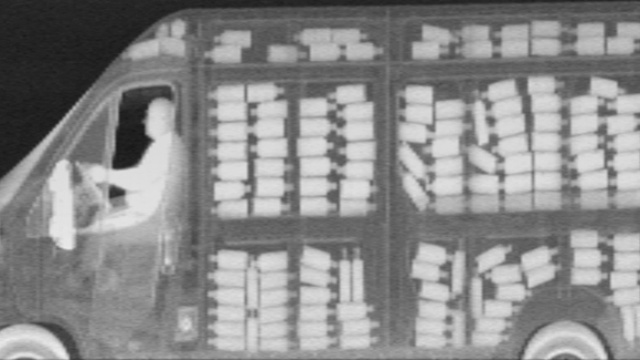
269SurveillanceEverything in New York to be X-rayed as NYPD brings in X-ray vans
Extremely secretive spy vehicles equipped with X-ray facility, Z Backscatter, will now be seen patrolling the city streets — NYPD hasn’t disclosed...
-

 117Geek
117GeekPost popularity exposed on Facebook, thanks to a new bug
For a Facebook marketer, the most important statistic is how many people have viewed their post and although Facebook provides details regarding...
-
 260Hacked
260Hacked“You Can Hack a Computer Just by Looking at It” – HP Explains Visual Hacking
Short Bytes: Visual Hacking is a security threat that is often overlooked by us. This is the act of stealing information by...
-

 304Hacked
304HackedExplained: How Criminals Hack Your Chip And Pin Card
Short Bytes: EMV credit cards have till now been assumed to be unhackable. The security professor from the University of California explains how...
-

 86Data Security
86Data SecurityVideo Explainer: How Criminals Can Easily Hack Your Chip & PIN Card
You may be under the impression that the new EMV chip system for credit card payments is nice and secure. But the...
-

 165Data Security
165Data SecurityPrices of stolen data on the Dark Web
Over the years, the McAfee Labs team has worked with IT security vendors, law enforcement and others to identify and evaluate numerous...
-

 58Cyber Crime
58Cyber CrimeAdobe Flash is putting your computer at risk – and there’s no patch yet
Sooner or later you are going to have to address the Flash problem on your computers. And there doesn't seem a better...
-
 263Hacked
263HackedHere’s How Hackers Can Control Your Entire Digital Life in Minutes
Short Bytes: Continuing our “steps to effective security” series, we are here with a true story that tells about the basic security...
-
 159Data Security
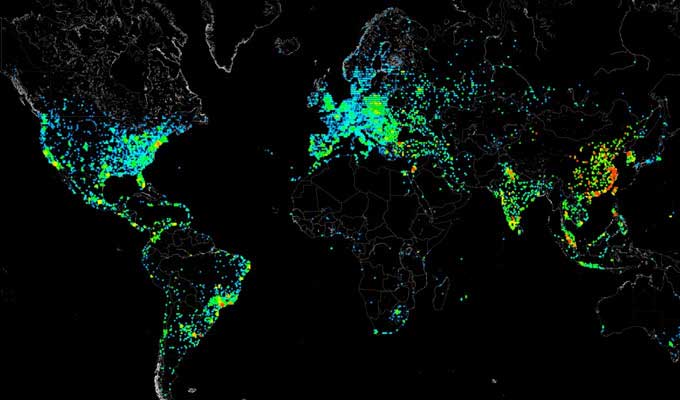
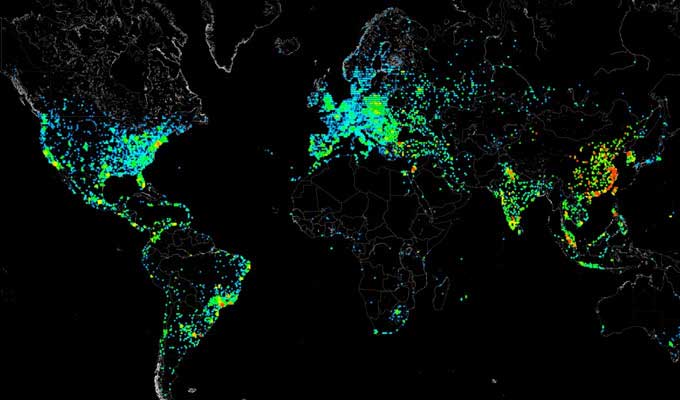
159Data SecurityHow to scan whole Internet 3.7 billion IP addresses in few minutes?
Cyber security audit and ethical hacking training professionals normally use scanner to scans the networks. Scanning every IP address on the internet...



