Featured News
-

 217Vulnerabilities
217VulnerabilitiesHackers Prefer File Upload, XSS, and SQLi Bugs When Attacking WordPress Sites
WordPress is a free, open source content management system (CMS) for creating websites, and is considered to be the most popular blogging system...
-

 101Incidents
101IncidentsMajor DNS provider hit by mysterious, focused DDoS attack
Attack on NS1 sends 50 million to 60 million lookup packets per second. Unknown attackers have been directing an ever-changing army of bots...
-
 305Hacked
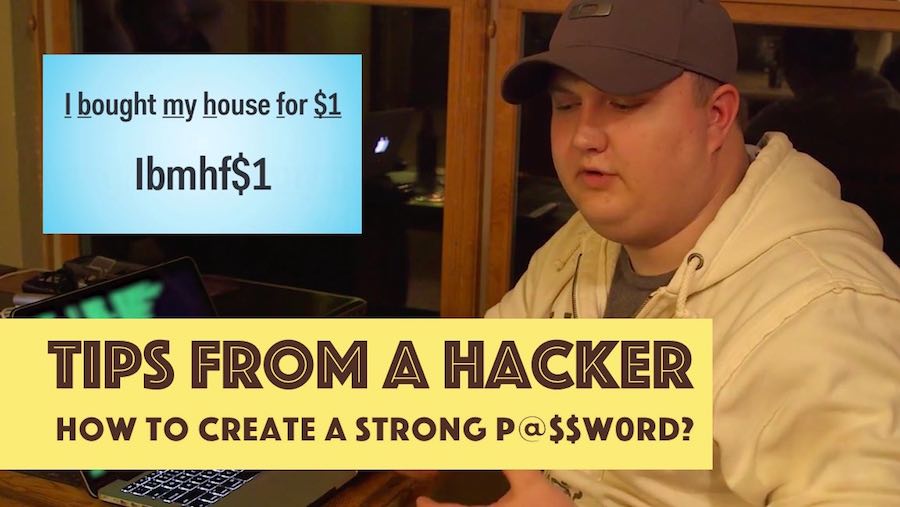
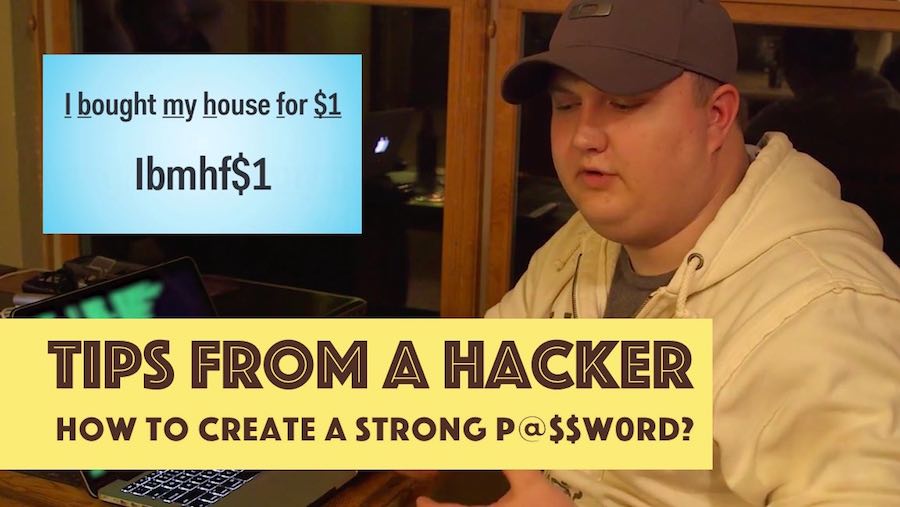
305HackedTips From A Hacker: Trick To Come Up With A Strong Password
Short Bytes: A security consultant from the RedTeam talks about the easiest way to come up with a strong password. You just...
-
 361Geek
361GeekAndroid + Raspberry Pi: Google Is Soon Bringing Official Support For RPi 3
Short Bytes: The Raspberry Pi 3 is a cheap and small computer that has gained wide support from programming and maker community....
-

 289News
289NewsTwitter accounts are getting hacked and spreading adult content
More than 2,500 Twitter Accounts Hijacked and Taken Over by Pornbots in last two weeks! The hijacking of over 2,500 Twitter accounts...
-
 295Geek
295GeekTor Developers collaborate to accelerate development of Next Gen Onion Service
Tor Developers go for hack fest to brainstorm about Next Generation of Onion Services ideas A group of Tor developers recently got...
-

 119Geek
119GeekGood Bye Passwords as Google Plans a Different Verification Option
Android users will be able to log in to services using a combination of their face, typing patterns and how they move!...
-

 121Cyber Crime
121Cyber CrimeCyber Criminals Targeting Users with WhatsApp Gold Version Malware Scam
No there is no Gold Version for WhatsApp — If you have received an invitation from a friend it’s because their account has...
-

 230Privacy
230PrivacyGDPR Day: countdown to a global privacy and security regimen?
This thing called GDPR will impact data security and privacy policy at many US firms when it takes effect two years from...
-

 118Data Security
118Data SecurityNext-gen Tor to use distributed RNG, 55-character addresses
Numbers so random no one can predict how random they’ll be. The Tor project has cooked up a new way to generate random...
-
 222Geek
222GeekBlisk — A Free Web Browser That Every Programmer And Developer Must Use
Short Bytes: Blisk is a new web browser designed specifically for web developers who need multiple tools to test their websites on different...
-

 269How To
269How ToHow To Create A Hidden User Administrator Account On Windows 10
Short Bytes: Using a hidden user administrator account on Windows 10, you can ensure the privacy of your personal data very easily....
-
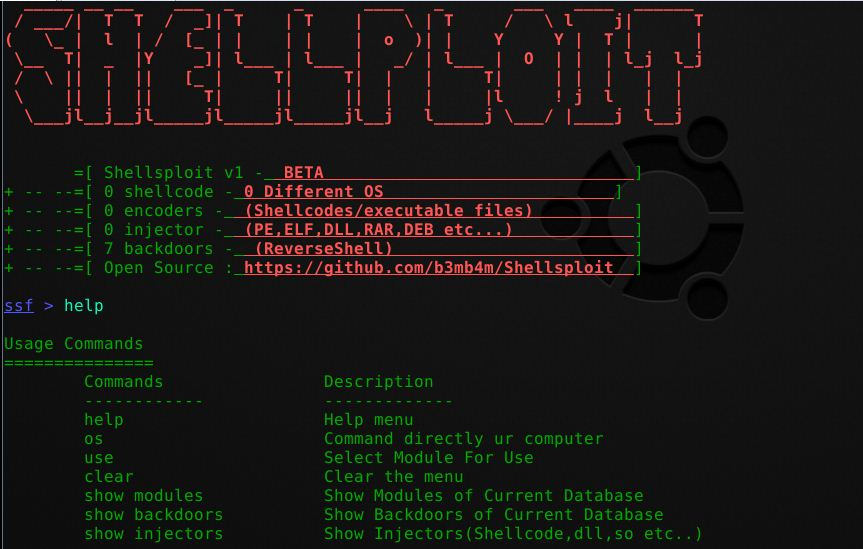
 216Hack Tools
216Hack ToolsShellsploit – New Generation Exploit Development Kit
Shellsploit let’s you generate customized shellcodes, backdoors, injectors for various operating system and let’s you obfuscate every byte via encoders. Install/Uninstall If...
-

 209Data Security
209Data SecurityPastejacking Attack Overrides Your Clipboard to Trick You into Running Evil Code
Copy-pasting commands into your terminal allows attackers to append, automatically execute and then hide malicious code. This type of attack is known...
-

 183Hacked
183HackedGoogle Trust API Will Replace Your Passwords With A ‘Trust Score’
Short Bytes: In the wake of increasing security threats and password leaks, Google is working on Project Abacus that will introduce Trust...
-
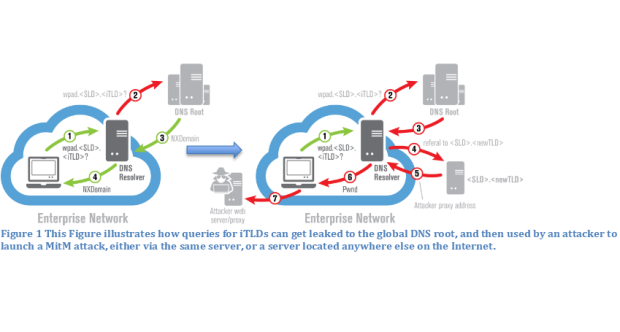
 272Data Security
272Data SecurityWPAD Protocol Bug Puts Windows Users at Risk
WPAD name collision issue can lead to MitM attacks. US-CERT has issued a public alert after researchers from the University of Michigan and...
-
 165Hacked
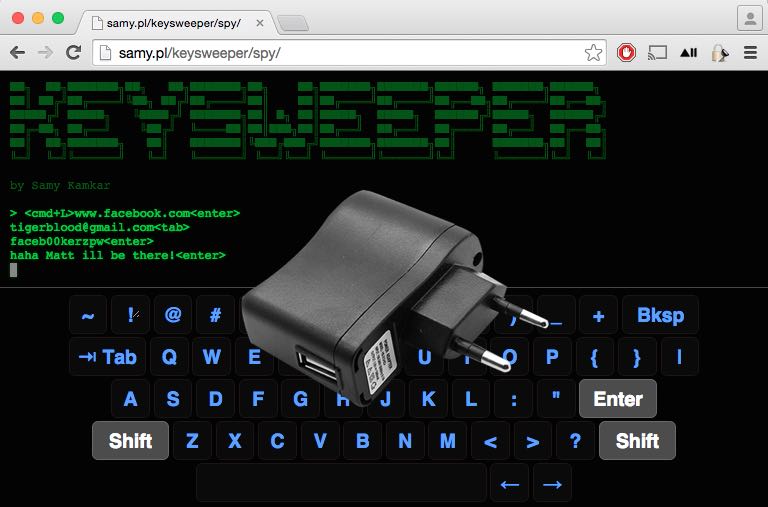
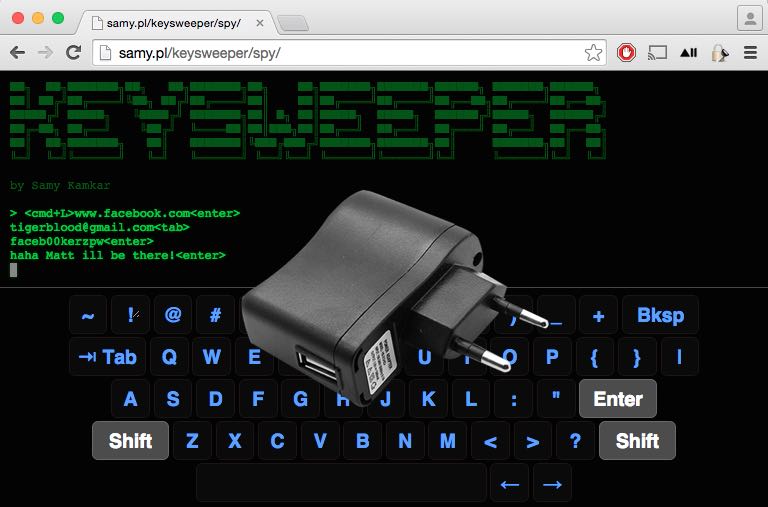
165HackedKeySweeper — You Could Be Using A Fake USB Charger That Records Everything You Type
Short Bytes: The FBI has issued a warning for the private industry to keep an eye on a stealthy Arduino-based keylogger hidden...
-

 90Data Security
90Data SecurityOperation Ke3chang Resurfaces With New TidePool Malware
Little has been published on the threat actors responsible for Operation Ke3chang since the report was released more than two years ago....
-

 336Geek
336GeekFacebook Facing Lawsuit for Scanning Users’ Private Messages for Likes
Ever think a social networking site that is currently counted among the world’s top three social media platforms would steep so low...
-

 334Data Security
334Data SecurityWatch out for this USB Device Charger, it could be Keystroke Logger: FBI
Private industry players have been warned by the FBI through its Private Industry Notification to keep an eye on those keystroke loggers...
The Latest
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Cyber Attack
Cyber AttackMicrosoft Patches 61 Flaws, Including Two Actively Exploited Zero-Days
-
 Cyber Attack
Cyber AttackThe 2024 Browser Security Report Uncovers How Every Web Session Could be a Security Minefield
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Data Breach
Data BreachBlack Basta Ransomware Strikes 500+ Entities Across North America, Europe, and Australia
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Data Breach
Data BreachA SaaS Security Challenge: Getting Permissions All in One Place
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment




