Featured News
-
 85Malware
85MalwareSystem Updates: Governments Can Hack Most Software Using This “Golden Key” Backdoor
Short Bytes: When you read the headlines like “FBI is forcing Apple to create a backdoor in their products”, what you are really...
-

 65Malware
65MalwareRazzies for malware: These were the worst performances of the year
Just as audiences have suffered from bad movie craftsmanship, IT users have had to endure the consequences of the malicious work done...
-
 98Data Security
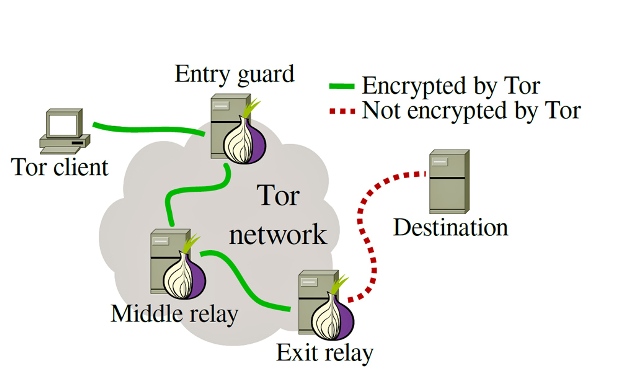
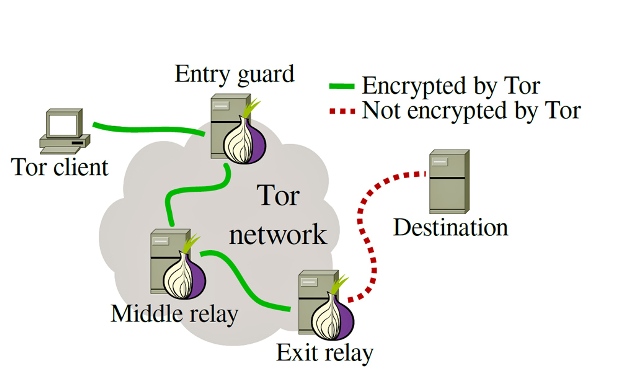
98Data SecurityTor takes aim against malicious nodes on the network
‘Sybil’ nodes could be used to de-anonymise traffic. The Tor Project is working with Princeton University boffins to try and identify possibly malicious...
-

 86Data Security
86Data SecurityFBI could use 3 other hacks on killer’s iPhone besides an Apple backdoor
Other than an Apple backdoor hack, FBI could use 3 other hacks on killer’s iPhone. According to hardware-security experts, there are at least...
-

 313News
313NewsReporter Gets His Email Hacked on The Plane
The reporter from USA Today claims his fellow passenger hacked his email during the flight while he was working on an article about...
-

 375Geek
375GeekSnowden’s Favorite Signal App Developer Hired by Apple
Apple has hired one of the developers behind Signal app — The app which has been used and endorsed by Edward Snowden So...
-

 274News
274NewsWatch How An iPhone was Hacked with a Simple Toy
While the FBI is almost begging Apple to let them have a backdoor access to its iPhone, a Chinese company demonstrated how...
-

 237Geek
237GeekUS Army Revolutionize Bullet Design — A Self-Destructing Bullet
The US army is working on a self-destructing bullet in order to reduce the risk of collateral damage Researchers from the US...
-
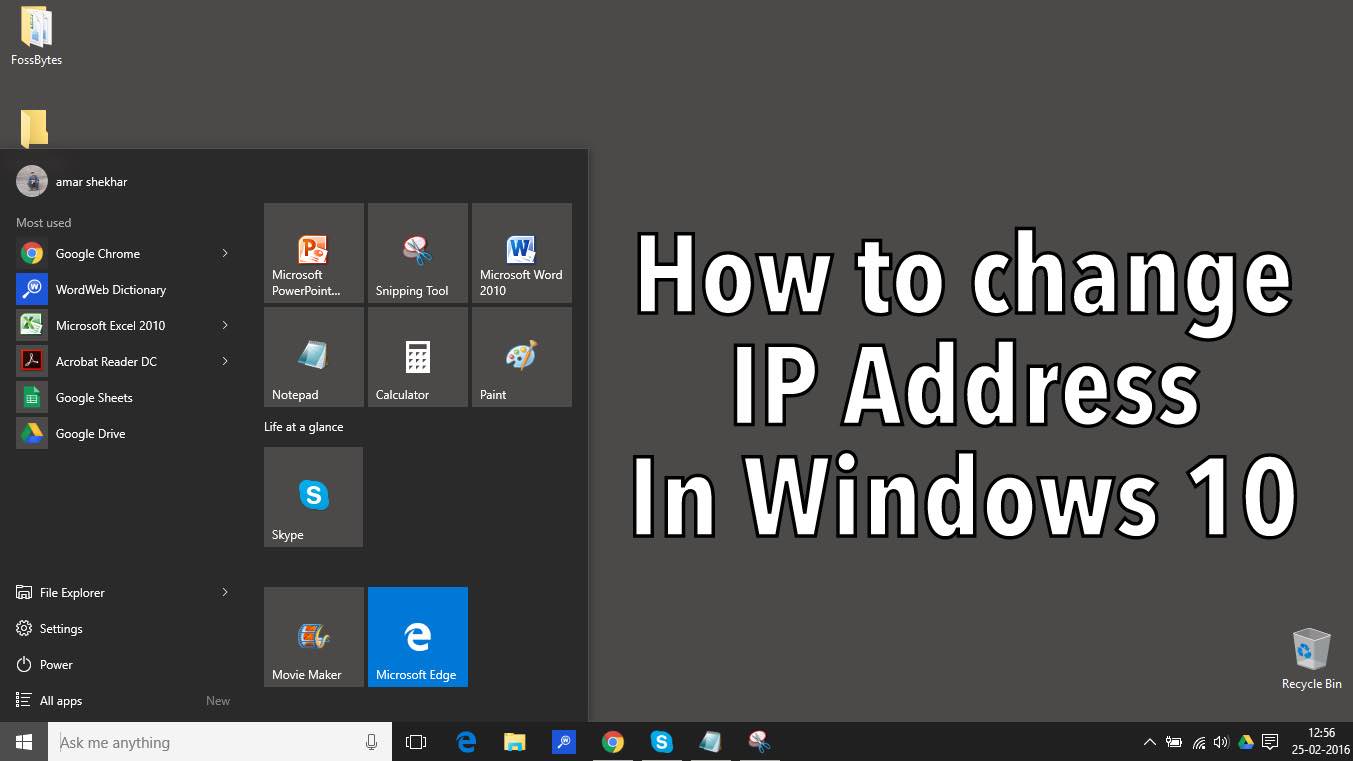
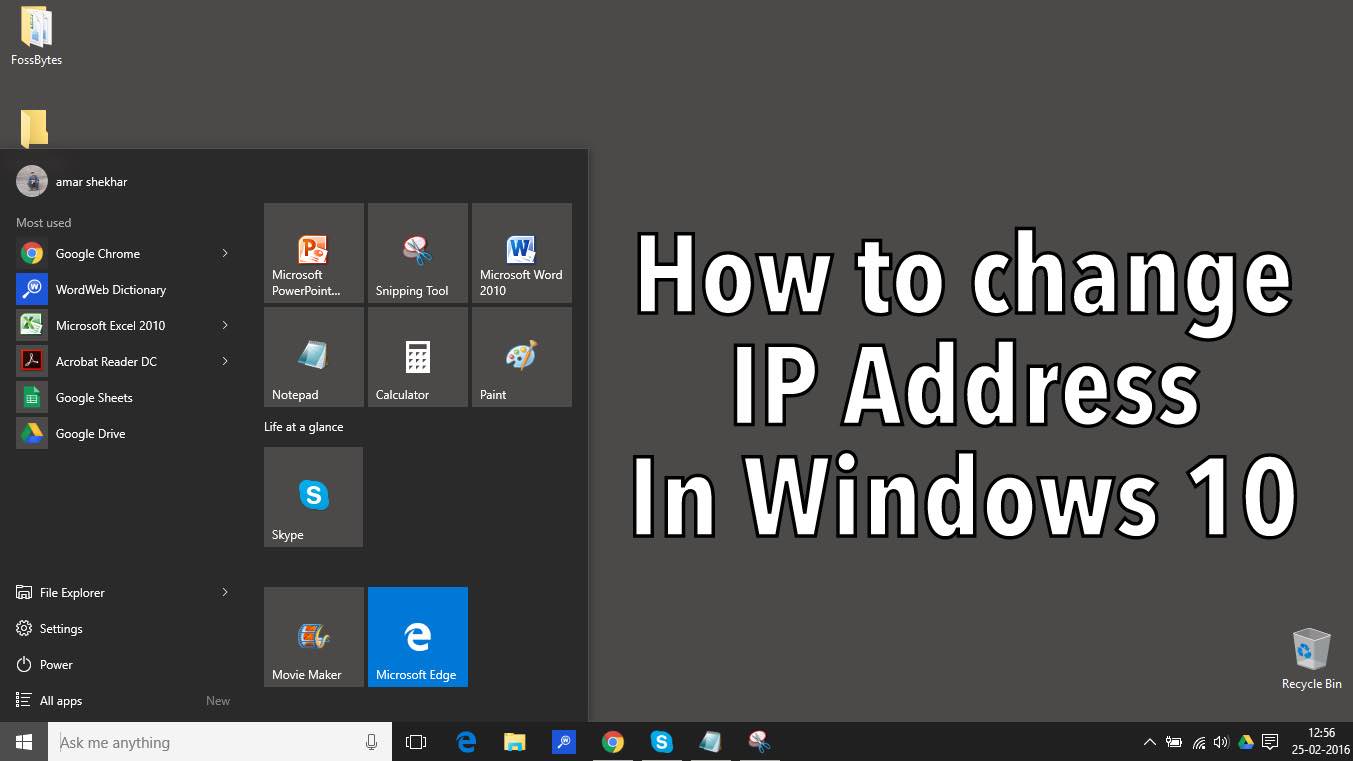 275How To
275How ToHow To Change IP Address in Windows 10: A Visual Guide
When working in a larger environment, we are often asked to change our IP address. To change IP address in Windows 10,...
-

 301Geek
301GeekStory of Chris Putnam: The First Facebook Hacker
I know you might have stumbled upon the Facebook icon of a certain guy with his face upwards to his right at...
-

 133News
133NewsPro-ISIS hackers post video message against CEOs of Twitter and Facebook
The terrorist group ISIS is not happy with Facebook and Twitter deleting their accounts, profiles, pages and groups — So it is...
-
 82Malware
82MalwareChinese ISPs Caught Injecting Ads and Malware in Their Network Traffic
Most ISPs that engage in this practice are owned by two of Asia’s biggest network operators, both located in China. Three researchers...
-

 112Vulnerabilities
112VulnerabilitiesMedical superbugs: Two German hospitals hit with ransomware
Infection forces patients onto phones and medicos onto faxes. At least two hospitals in Germany have come under attack from ransomware, according...
-

 132Data Security
132Data SecuritySecurity cameras and bank accounts can be hacked with an email as demonstrated by a hacker
All it takes to hack security cameras and bank accounts is an email, demonstrates a hacker. What happens when you challenge a series...
-

 156Incidents
156IncidentsDiscover how many ways there were to hack your Apple TV
Apple has patched more than 60 vulnerabilities affecting the Apple TV, including flaws that can lead to arbitrary code execution and information...
-

 258Lists
258Lists21 Top Programming Languages On GitHub And Stack Overflow – January 2016
Short Bytes: RedMonk has just published its list of the top 21 programming languages of 2016 Q1. This list is based on...
-

 239Cyber Crime
239Cyber CrimeAnonymous Hit Italian Government Sites Against Trans Adriatic Pipeline Project
Anonymous Italy Launches #OperationGreenRights- Targets Italian Government Portals with DDoS Local government portals of Apulia and Basilicata regions in southern Italy have...
-
 182Geek
182GeekFacebook Reactions — What’s it all About?
The legendary Like button will no longer be gracing our Facebook pages as frequently as it regularly does since Facebook Reactions are...
-

 293How To
293How ToHow To Enable Windows 10 Fast Startup: The Ultimate Windows 10 Guide
Short Bytes: Windows 10 Fast Startup feature is an inbuilt feature of Windows 10 which saves some Windows 10 files upon shutdown...
-
 225News
225NewsAnonymous France’ Trio Due to be Sentenced in March for Targeting Police sites
Anonymous activists’ Trio Due to be Sentenced in March for Targeting French Police and Government French judicial system is known for its...
The Latest
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Cyber Attack
Cyber AttackMicrosoft Patches 61 Flaws, Including Two Actively Exploited Zero-Days
-
 Cyber Attack
Cyber AttackThe 2024 Browser Security Report Uncovers How Every Web Session Could be a Security Minefield
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Data Breach
Data BreachBlack Basta Ransomware Strikes 500+ Entities Across North America, Europe, and Australia
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Data Breach
Data BreachA SaaS Security Challenge: Getting Permissions All in One Place
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment




