Featured News
-

 273Geek
273GeekApple Tips & Tricks: How To Unlock iPhone To Use it on Another Carrier
Are you wondering how to unlock your iPhone so you can use it with another carrier? Then wonder no more! Although initially...
-
 209Geek
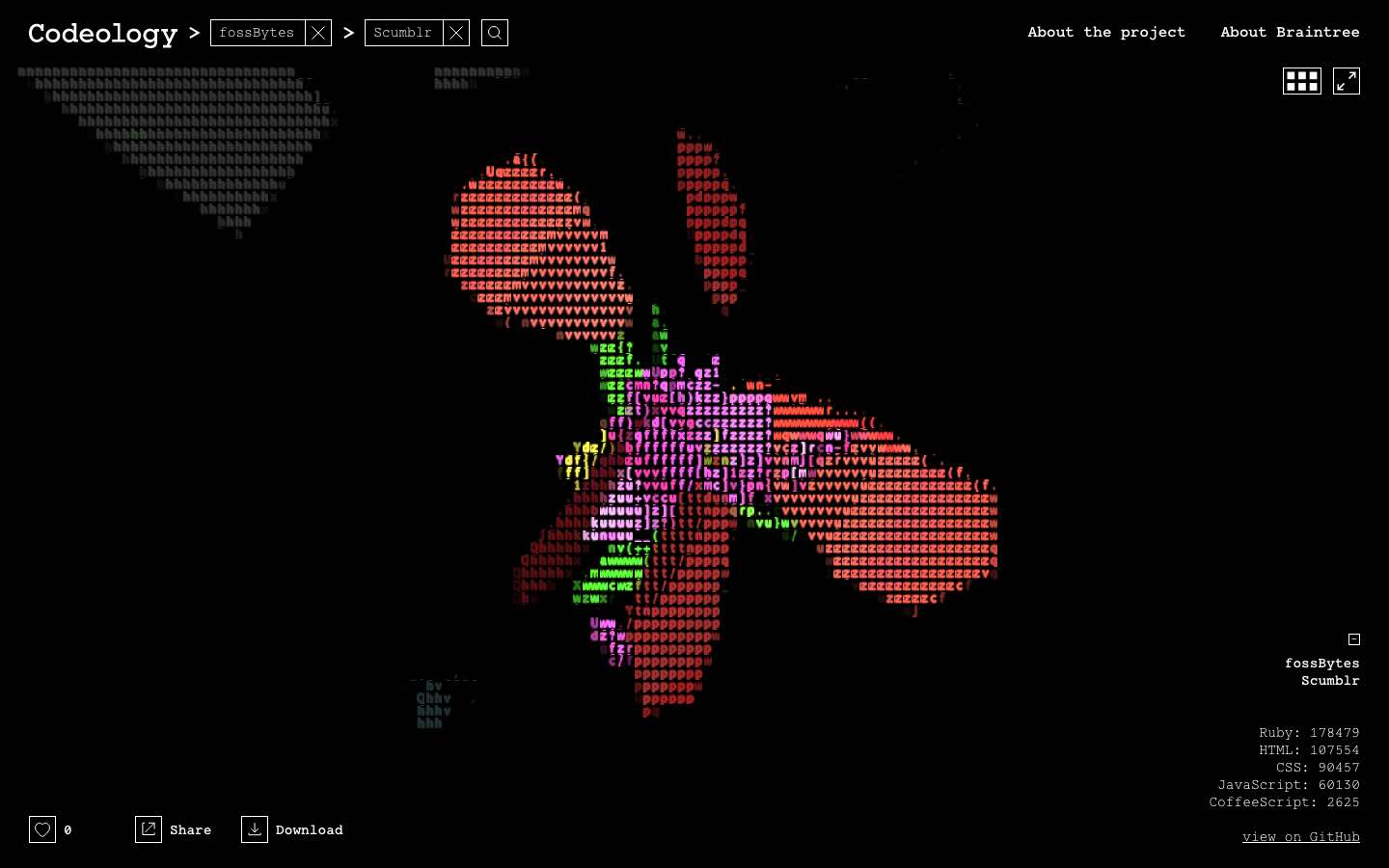
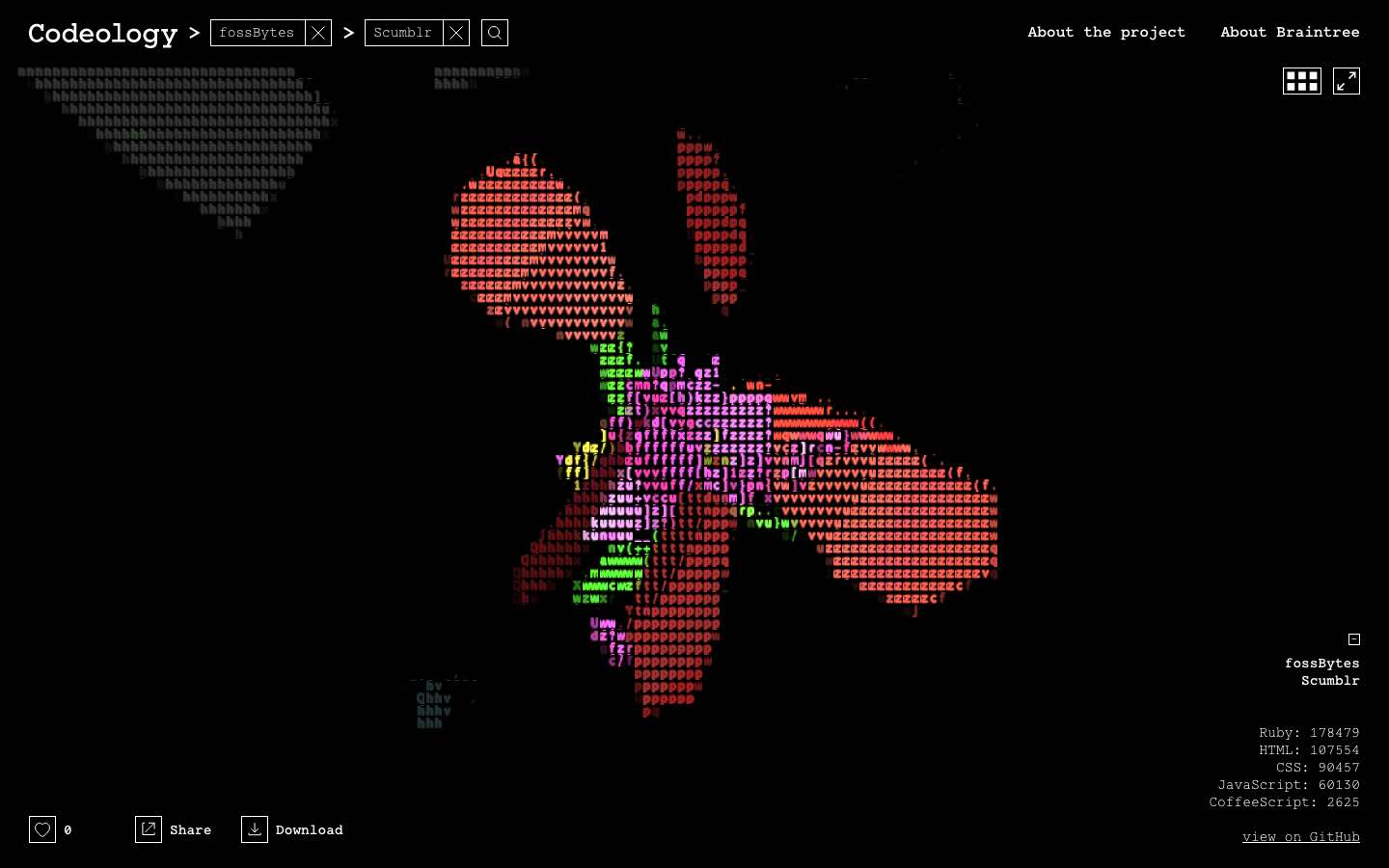
209GeekA Programmer’s Dream: This Is What Your Code Actually Looks Like On GitHub
Short Bytes: Codeology is an online visualization program that allows you to see your GitHub project in front of your eyes. Give...
-

 127Malware
127MalwareAndroid Malware About to Get Worse: GM Bot Source Code Leaked
IBM X-Force threat intelligence has found that the source code for Android malware GM Bot was leaked on an underground board in...
-

 265News
265NewsHacker Shows How To Hack Wireless Burglar Alarm System Like A Pro
SimpliSafe Alarm Systems’ Inherent Vulnerability Exposes Hazards of Wireless Security Devices Digital age has brought along countless blessings and conveniences for the...
-

 386Vulnerabilities
386VulnerabilitiesHow to Use NMAP 7 to Discover Vulnerabilities, Launch DoS Attacks and More!
NMAP is an essential tool in any hacker’s arsenal. Originally written by Gordon Lyon aka Fydor, it’s used to locate hosts and...
-
 142Vulnerabilities
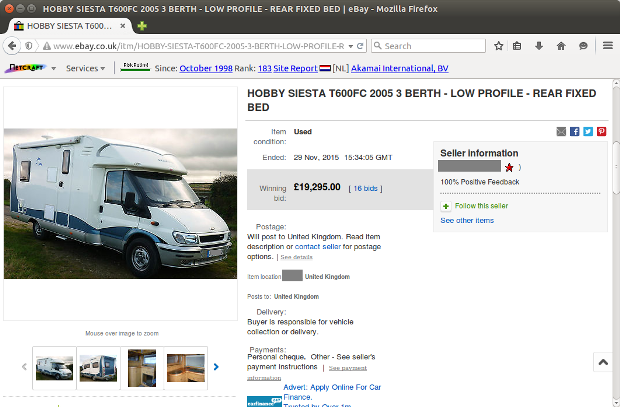
142VulnerabilitiesJSF*** eBay XSS Bug Exploited in the Wild, Despite the Company’s Fix
Attackers exploit eBay’s lackluster security policy. The JSF*** XSS bug that cyber-security firm Check Point discovered two weeks ago is being used in...
-
 91Incidents
91IncidentsMan admits he stole nude celebrity pics from Apple and Gmail accounts
Phishing scheme gained illegal access to accounts storing 161 nude images. An Oregon man has admitted he tricked hundreds of people into divulging...
-

 339Geek
339GeekWhich Phone is More Vulnerable to Hacking – iPhone or Android?
iOS users take on Android while Android users criticize Apple — But which OS is actually secure? It is a fact that...
-

 199News
199NewsAnonymous To Hit Israeli Military Against Detention of Palestinian Journalist
Al-Qeeq’s Detention Enrages Anonymous- Widespread DDoS Campaigns Planned Against Israel Army The online hacktivist Anonymous is known for targeting Israeli cyberspace including government,...
-

 190Geek
190GeekSelfie Crazy Tourists Responsible for Tragic Death of Rare Baby Dolphin
It takes nothing to go so low and kill a beautiful creature of nature for the sake of fun Suppose you are...
-

 151Data Security
151Data SecurityProtect your iPhone from the clutches of the FBI by switching to longer passcodes
Protect your iPhone from the clutches of the FBI by switching to longer passcodes The on-going tussle between the FBI and Apple...
-

 304Opinion
304OpinionThe Four “A”s of Account Management
It's said that the biggest vulnerabilities in a network environment are its users. If only there was a way to control those...
-

 105Data Security
105Data SecurityHackers paid $17,000 in bitcoin ransom by L.A. hospital to get back medical records
Los Angeles hospital paid hackers $17,000 ransom in Bitcoins to decrypt medical records. We had earlier reported that hackers had infected the Hollywood Presbyterian...
-

 277Opinion
277OpinionApple and ‘exceptional access’ to crypto protection
Apple is the latest in a host of technology players to be requested to allow exceptional access, that is, access in exceptional...
-
 151Malware
151MalwareGozi Banking Trojan is now fully compatible with the Edge browser in Windows 10
Banking trojans, like ransomware, have become big business today. And the people behind all of these malicious products are always moving forward,...
-
 119Incidents
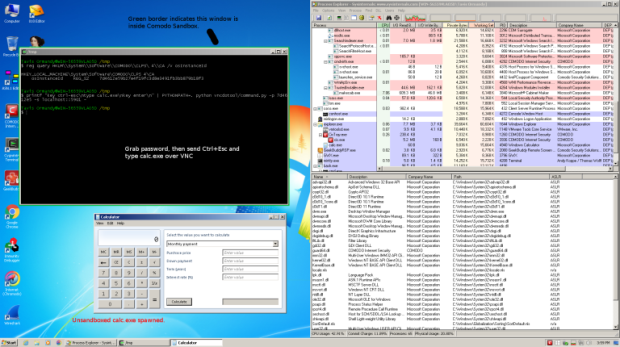
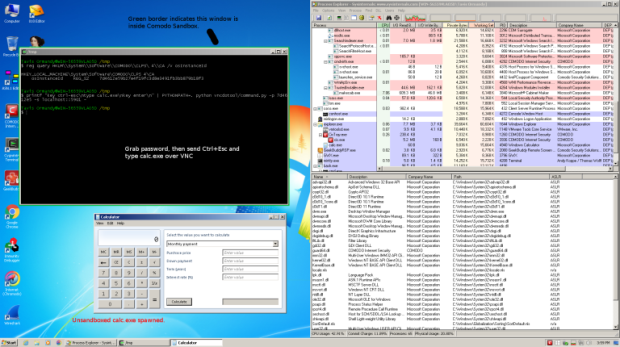
119IncidentsComodo Internet Security opened your PC to attackers
Comodo Internet Security, in the default configuration, installs an application called GeekBuddy that also installs a VNC server enabled by default. The hackers...
-

 208News
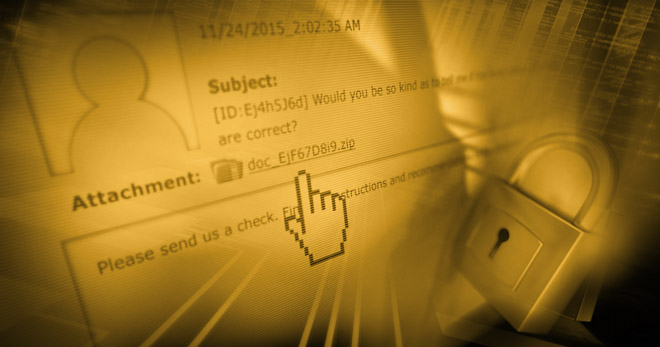
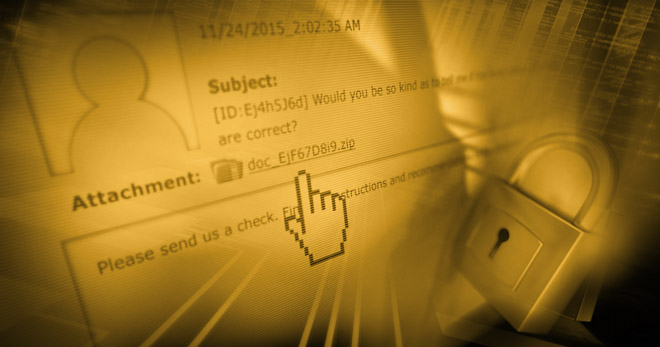
208NewsLocky Ransomware – Latest global Cyber Security incident
If you receive a mail masquerading as a company’s invoice and containing a Microsoft Word file, think twice before clicking on it....
-
 303Geek
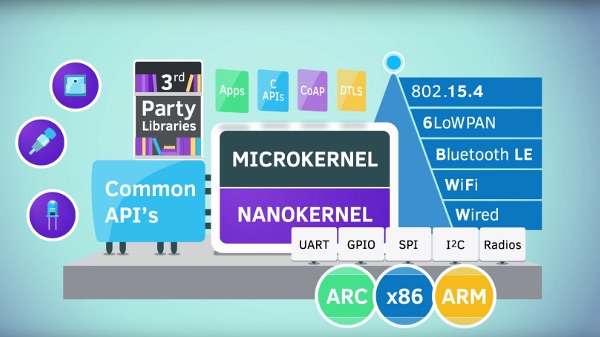
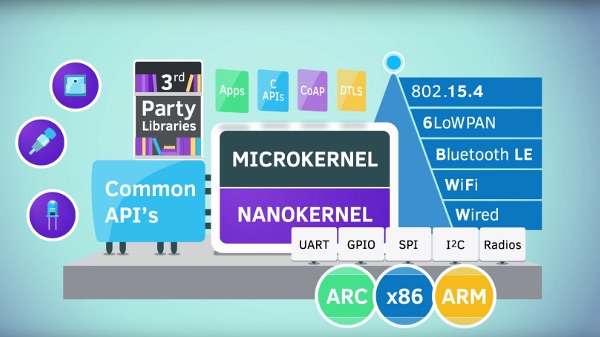
303GeekZephyr Project — Linux Foundation Announces Open Source Operating System For IoT
Short Bytes: IoT (Internet of Things) is going to get a major boost in the coming years. 48 hours ago, the Linux...
-
 160Malware
160MalwareLocky ransomware on aggressive hunt for victims
Millions of spam emails spread new ransomware variant on the day it first appeared. A new variant of ransomware known as Locky...
-
 244Hacked
244HackedHere’s Why John McAfee Is Ready To Decrypt The iPhone For FBI Free Of Charge
Short Bytes: “Cybersecurity legend” John McAfee has bashed the policies of American government’s stance on encryption. Taking Apple’s side, McAfee has offered FBI...
The Latest
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Cyber Attack
Cyber AttackMicrosoft Patches 61 Flaws, Including Two Actively Exploited Zero-Days
-
 Cyber Attack
Cyber AttackThe 2024 Browser Security Report Uncovers How Every Web Session Could be a Security Minefield
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Data Breach
Data BreachBlack Basta Ransomware Strikes 500+ Entities Across North America, Europe, and Australia
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Data Breach
Data BreachA SaaS Security Challenge: Getting Permissions All in One Place
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment




