Featured News
-

 167News
167NewsIranian Hackers Breached Computer of Ex-Israeli Army Chief-of-Staff
Computers of 1800 Key Personalities including Ex-Israeli Army Chief-of-Staff Penetrated by Iran-Sponsored Hacker Last year, some private pictures of IDF’s women soldiers were...
-

 170Geek
170GeekEasiest Way to Improve Your Phone’s Battery Life – Deleting Facebook App
Facebook app uses your smartphone battery more than any other app — It’s time to get rid of the app and use...
-

 552Courses & Ebooks
552Courses & EbooksCEH v9 – Certified Ethical Hacker v9 Course PDF + Tools DOWNLOAD
This is the worlds most advanced ethical hacking course with 18 of the most current security domains any ethical hacker will ever...
-
 181Data Security
181Data SecurityKaspersky Researcher Shows How He Hacked His Hospital While Sitting In His Car
Short Bytes: When we visit a hospital, we put our complete trust in our doctor and the medical equipment that he/she uses....
-
 195News
195NewsFBI Demands Removal of its Employees’ Leaked Data from the Internet
The United States Department of Homeland Security had its data leaked online — FBI is forcing websites to remove the data ASAP....
-
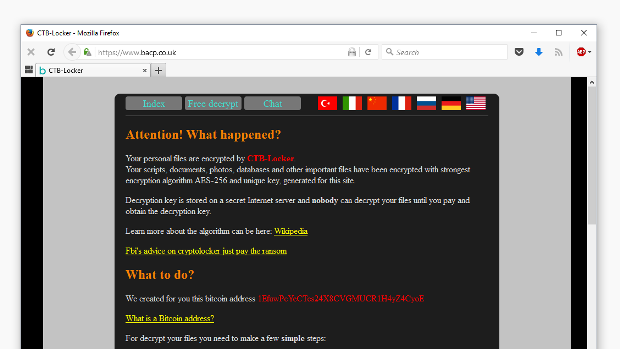
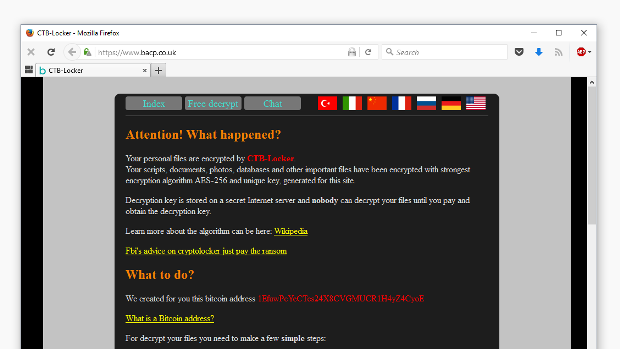 159Malware
159MalwareFirst Time Ever: Ransomware Hits Website and Defaces Homepage
CTB-Locker ransomware spotted on a Linux machine. The website of the British Association for Counseling & Psychotherapy (bacp.co.uk) has been hit by...
-
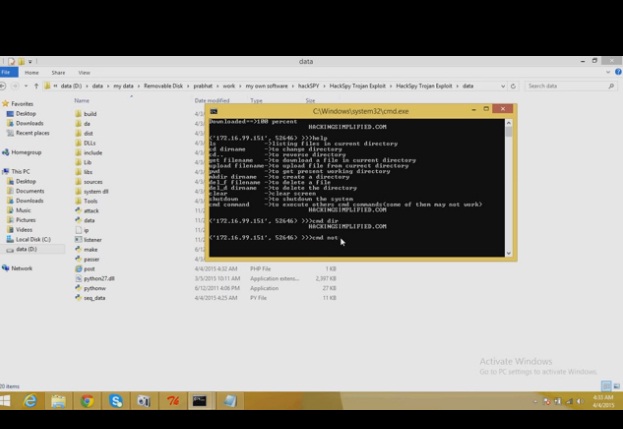
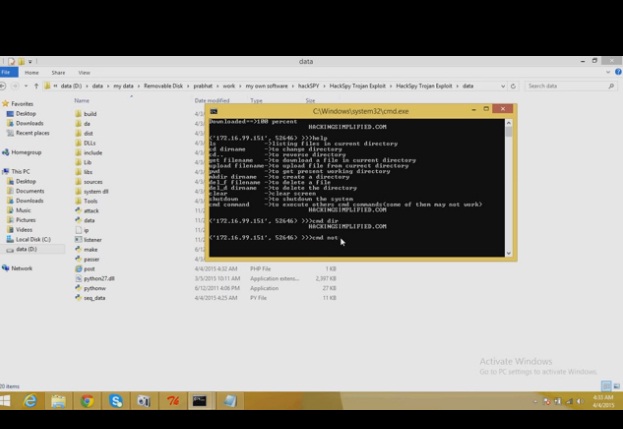 121Data Security
121Data SecurityHackSpy Trojan Exploit
HackSpy Trojan Exploit this tool make undetectable trojan virus….which can help you to spy on other computers…….. this version consists of a trojan...
-
 302Data Security
302Data SecurityUK police arrested teenage hacker who allegedly hacked CIA and FBI officials
UK Police and FBI have arrested a teenager suspected to be Cracka, the hacker who hacked the CIA Director John Brennan. The...
-

 89Malware
89MalwareHow malware moved the exchange rate in Russia
After an investigation period, details were published about a unique cyberattack on a Russian bank where a malware placed trade orders for...
-

 152Scams
152ScamsPrince Charming: The Valentine’s Day scammer
In this feature, we highlight some of the key tactics used by cybercriminals via online dating websites, helping you stay safe on...
-

 175Data Security
175Data SecurityNYPD Admits To Using Cell Phone Spy Tool More Than 1000 Times Since 2008
The New York Police Department has admitted to using controversial cell phone spying systems known as Stingrays—which can be used to track...
-

 136Malware
136MalwareNetflix malware and phishing campaigns help build emerging black market
Attackers steal users’ Netflix credentials and add them to black markets focused on providing access to the streaming service for cheaper prices....
-

 103Data Security
103Data SecurityIBM Researchers Hack Into A Smart Building To Highlight The Backdoors Created For Hackers
This smart building was hacked by IBM researchers to show hacking risks associated with Internet of Things. IBM security researchers are warning...
-
 185News
185NewsHackers Pull Another Attack at IRS, Stopped Before Anything Was Taken
Last year, IRS was hacked twice where personal information of thousands of taxpayers was stolen. Now, according to a statement issued Tuesday...
-

 317Cyber Crime
317Cyber CrimeThe Dangers of Online Dating: Watch Out for ‘Sweetheart Scammers’
Once an almost unheard-of phenomenon, online dating is today a go-to resource for many busy, career-oriented individuals for finding their true love...
-
 251Cyber Events
251Cyber Events6 Boldest Cybersecurity Predictions For 2016
Attacks in the cyberspace have been a cause of concern for the entire world. The world, where everything is being carried over...
-

 90Malware
90MalwareHow to isolate VBS or JScript malware with Visual Studio
ESET has seen a rise in malware developed using scripting languages. We can understand the threats better by isolating them in a...
-

 159Vulnerabilities
159VulnerabilitiesSevere Vulnerability Affects Cisco ASA VPN Server Equipment
Attackers can take over Cisco firewalls and VPN servers. Cisco has released urgent security patches aimed at fixing a security vulnerability in some...
-

 196Data Security
196Data SecurityGmail to warn you if your friends aren’t using secure e-mail
Messages coming to or from non-encrypted sources will be flagged by Google. Google has confirmed a number of changes to Gmail with...
-
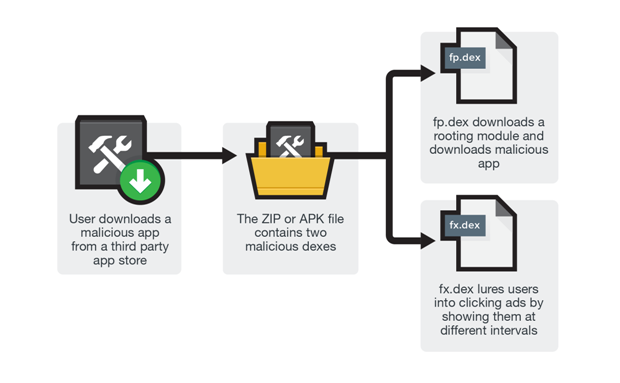
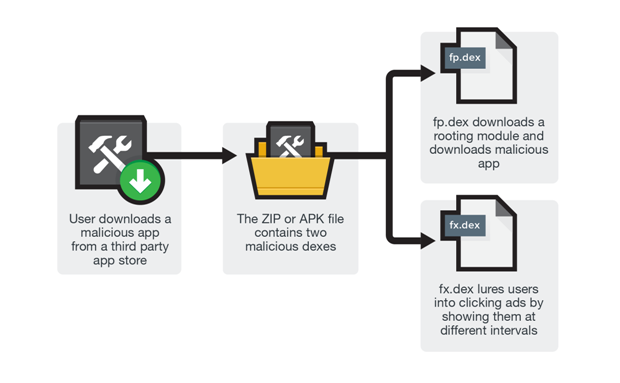 176Malware
176MalwareUser Beware: Rooting Malware Found in 3rd Party App Stores
Think of third-party app stores as independent shops in the city where people go to as an alternative to the city mall....
The Latest
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Malware
MalwareEternal Malware: CVE-2024-3400 Rootkits Persist Through Palo Alto Firewalls Updates and Resets
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Data Breach
Data BreachNavigating the Threat Landscape: Understanding Exposure Management, Pentesting, Red Teaming and RBVM
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage




