Featured News
-

 239News
239NewsAnonymous Wants Saudi Arabia Out from Olympics for Battering Human Rights
The Online Hacktivist Anonymous Demands Exclusion of Saudi Arabia from Olympics for Battering Human Rights Saudi Arabia has always been criticized by...
-

 173Vulnerabilities
173VulnerabilitiesRemote Code Execution: All Versions Of Windows Hit By ‘Severe’ Security Vulnerabilities
Short Bytes: As a part the latest Patch Tuesday, Microsoft released 13 security patches for all version of Windows and other software like...
-

 187Data Security
187Data SecurityHearthstone add-ons, cheating tools come with data-stealing malware
Attackers have disguised information-stealing and Bitcoin malware as third-party add-ons and cheats for Blizzard’s online card game. Hearthstone, a free-to-play card game...
-

 3.6KData Security
3.6KData SecurityHow to Hack the Power Grid Through Home Air Conditioners
TENERIFE, SPAIN—THERE ARE many ways we know of to cause a blackout. You could hack industrial equipment to spin a generator out...
-

 311Data Security
311Data SecurityVigilante Hackers Fight Lizard Squad For Control Of 150,000 Home Routers
Home routers with little to no security are far too common. They’re dangerous from a number of perspectives: as peeping holes for spying on people’s...
-
 112Malware
112MalwareRent the infamous AlienSpy backdoor is now quite easy
Security experts at Kaspersky have spotted in the wild a new variant of AlienSpy RAT Family openly offered with a model of...
-
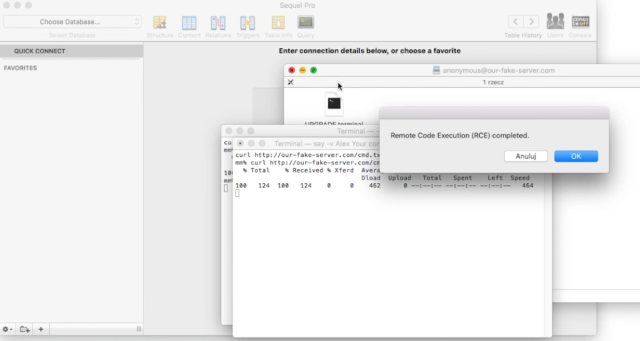
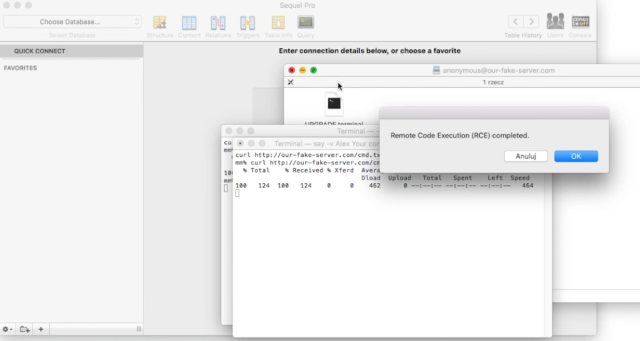 174Vulnerabilities
174Vulnerabilities“Huge” number of Mac apps vulnerable to hijacking, and a fix is elusive
Apps that use 3rd-party updater over insecure HTTP channels subject to MiTM attacks. Camtasia, uTorrent, and a large number of other Mac...
-

 162Data Security
162Data SecurityFacebook Hacking Tool Is Here To Hack Your Accounts, But Here’s A Catch
Short Bytes: Your desire to master the art of Facebook hacking can harm you in a big way. Recently, a variant of Remtasu...
-

 214Geek
214GeekFacebook’s Sneaky User Data Sharing Hammered by French Privacy Regulators
French privacy advocates tell Facebook to stop spying on its citizen within 3 month It’s a fact that European countries are not...
-
 246How To
246How ToHow To Get Pluralsight Courses For Free | 6 Months Subscription
Short Bytes: Pluralsight has one of the biggest collections of programming video courses. Here’s a simple way that tells you how to...
-

 198Hacked
198HackedCyber-Crime Barely Pays $30,000 A Year To A Black Hat Hacker
Short Bytes: In the war between good versus evil, ”Good’ makes more money than ‘Bad’ even if ‘Bad’ is good at finding the...
-

 167Cyber Events
167Cyber EventsNorth Korea Bears the Brunt of Satellite Launch- Becomes Target of Anonymous
A group of hackers famously known as New World Hackers (NWH) is claiming to attack a number of state websites in North...
-

 230Hacked
230HackedAnother Facebook Hacking Tool Is Here To Hack Your Accounts, But Here’s A Catch
Short Bytes: Your desire to master the art of Facebook hacking can harm you in a big way. Recently, a variant of Remtasu...
-

 235Scams
235ScamsSouthwest Airlines flight giveaway scams spread on Facebook
There is no such thing as a free lunch, and even if there was... who likes airline food that much anyway?
-

 120Privacy
120PrivacyStay safe with our Facebook cheat sheet
Learn how to boost your Facebook privacy on Safer Internet Day with our excellent cheat sheet. It'll work to your advantage now...
-
 192Data Security
192Data SecurityOxford School District Victim of hacker’s “Crypto-Ransomware”
Oxford, Miss. (TLV)—Sunday, Feb 7, The Oxford School District was attacked by an “unknown hacker” using “crypto-ransomware.” OSD has shut down all...
-
 133Incidents
133IncidentsHacker Leaks The Personal Information Of 20,000 FBI Agents
Short Bytes: An attack by a hacker has just revealed the sensitive information of about 20,000 FBI employees. Besides this personal contact...
-
 198Data Security
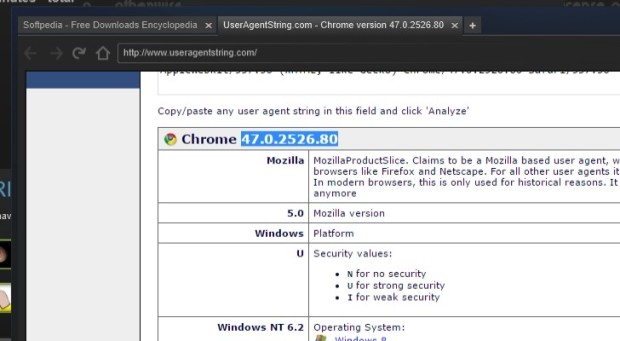
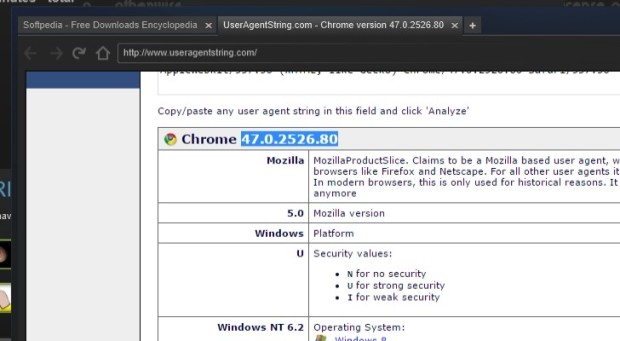
198Data SecuritySteam Uses Out-of-Date Chromium Browser with Security Feature Disabled
Steam’s built-in browser runs in a no-sandbox mode. The latest version of the Steam gaming client is employing an outdated Web browser that...
-

 115Incidents
115IncidentsClever bank hack allowed crooks to make unlimited ATM withdrawals
Banking malware is using techniques once reserved for state-sponsored hacking gangs. To appreciate how malware targeting banks and other financial institutions is...
-
 132Vulnerabilities
132VulnerabilitiesTor Project patches critical XSS bug in its blog after researcher publicly discloses it
Tor Project patches critical bug but refuses to acknowledge the bug discovery by a security researcher. Tor Project’s website had a critical cross-site...
The Latest
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft




