Featured News
-

 230Hacked
230HackedAnother Facebook Hacking Tool Is Here To Hack Your Accounts, But Here’s A Catch
Short Bytes: Your desire to master the art of Facebook hacking can harm you in a big way. Recently, a variant of Remtasu...
-

 236Scams
236ScamsSouthwest Airlines flight giveaway scams spread on Facebook
There is no such thing as a free lunch, and even if there was... who likes airline food that much anyway?
-

 121Privacy
121PrivacyStay safe with our Facebook cheat sheet
Learn how to boost your Facebook privacy on Safer Internet Day with our excellent cheat sheet. It'll work to your advantage now...
-
 192Data Security
192Data SecurityOxford School District Victim of hacker’s “Crypto-Ransomware”
Oxford, Miss. (TLV)—Sunday, Feb 7, The Oxford School District was attacked by an “unknown hacker” using “crypto-ransomware.” OSD has shut down all...
-
 134Incidents
134IncidentsHacker Leaks The Personal Information Of 20,000 FBI Agents
Short Bytes: An attack by a hacker has just revealed the sensitive information of about 20,000 FBI employees. Besides this personal contact...
-
 198Data Security
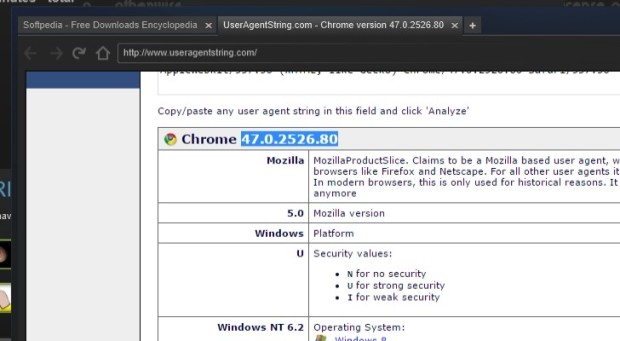
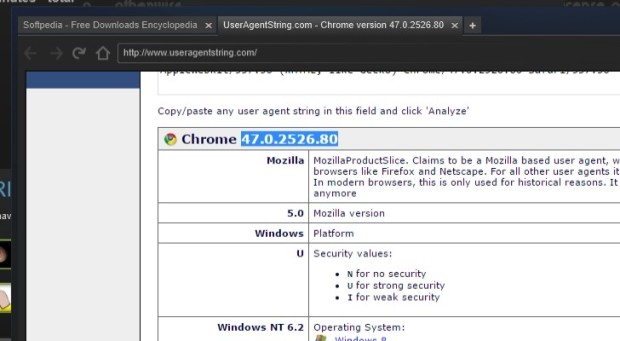
198Data SecuritySteam Uses Out-of-Date Chromium Browser with Security Feature Disabled
Steam’s built-in browser runs in a no-sandbox mode. The latest version of the Steam gaming client is employing an outdated Web browser that...
-

 116Incidents
116IncidentsClever bank hack allowed crooks to make unlimited ATM withdrawals
Banking malware is using techniques once reserved for state-sponsored hacking gangs. To appreciate how malware targeting banks and other financial institutions is...
-
 133Vulnerabilities
133VulnerabilitiesTor Project patches critical XSS bug in its blog after researcher publicly discloses it
Tor Project patches critical bug but refuses to acknowledge the bug discovery by a security researcher. Tor Project’s website had a critical cross-site...
-

 105Cyber Crime
105Cyber CrimeBeware, Latest WhatsApp Scam Drops Malware on Your Device
Watch out for latest WhatsApp scam tricking users into opening malware link sent by ”friends” The favorite app of all youngsters and...
-
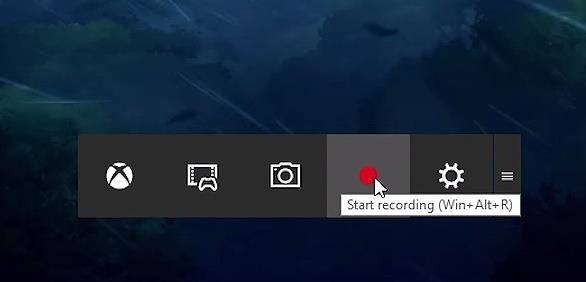
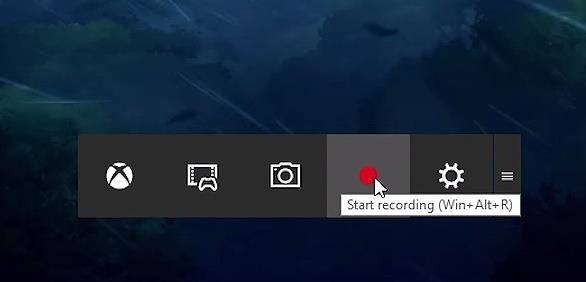 220How To
220How ToHow To Record Windows 10 Screen Using Xbox App
Short Bytes: Windows 10 has an inbuilt feature which lets a user record the Windows screen up to 2 hours. This screen...
-

 90Malware
90MalwareRemtasu is disguising itself as a tool to appropriate Facebook accounts
Almost a year ago we warned about the spreading of Remtasu, and far from lessening, we have been able to identify numerous...
-

 290Data Security
290Data SecurityHackers leaked DHS staff records, 200GB of files are in their hands
A hacker accessed an employee’s email account at the Department of Justice and stole 200GB of files including records of 9,000 DHS...
-

 205Vulnerabilities
205VulnerabilitiesDLL Hijacking Issue Plagues Products like Firefox, Chrome, iTunes, OpenOffice
Oracle patches Java installer against DLL hijacking issue. Oracle has released new Java installers to fix a well-known security issue (CVE-2016-0603) that also...
-
 263Hacked
263HackedHere’s How Windows 10 ‘Spying’ Forced A User To Switch To Linux Mint On His Computer
Short Bytes: Irritated by the telemetry and spying features in Windows 10, a Voat user decided to make the switch. After installing...
-

 89Data Security
89Data SecurityHacking Microsoft SQL Server Without a Password
During a recent penetration test, I was performing some packet captures and noticed some unencrypted Microsoft SQL Server (MSSQL) traffic. The syntax was...
-

 93Malware
93MalwareT9000 Backdoor Malware Targets Skype Users, Records Conversations
T9000 can also steal files from your hard drives. A new backdoor trojan is making the rounds, coming equipped with features that allow...
-
 185Data Security
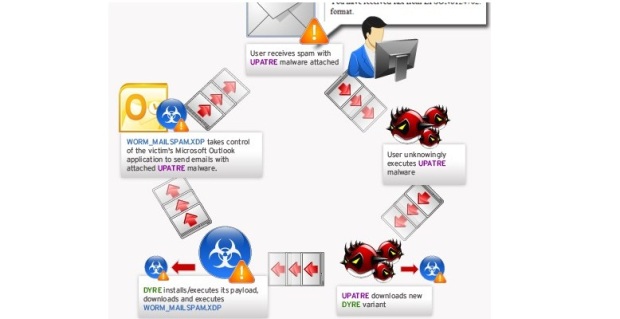
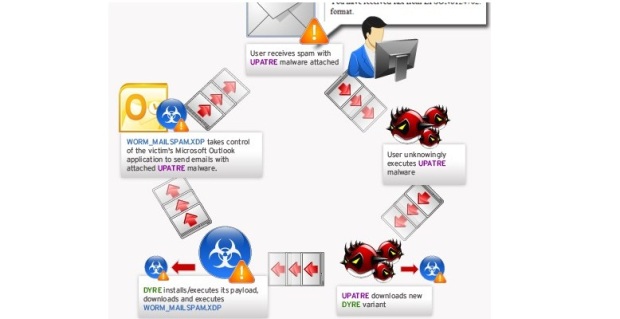
185Data SecurityDyre crackdown, the biggest effort to date by Russian authorities against cybercrime
Russian authorities raided offices of a Russian film distribution and production company as part of an operation against the Dyre gang. Russian...
-

 179Geek
179GeekA Simple Hangman Game Implemented In 3 Lines Of Python
Short Bytes: Today I’m sharing a clever implementation of Hangman in python by programmer Danver Braganza. Take a look at this 3-lines-long program and...
-

 337Data Security
337Data SecurityNew Malware Targets Skype Users, Saves Screenshots, Records Conversations
The internet is abuzz with news about a new backdoor Trojan that is equipped with such advanced features that it can steal...
-

 279News
279NewsAnonymous Targets African Governments Against Corruption
Anonymous and supporters of LulzSec hackers target African governments against massive corruption. The online hacktivist Anonymous is targeting African countries to protest...
The Latest
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Malware
MalwareEternal Malware: CVE-2024-3400 Rootkits Persist Through Palo Alto Firewalls Updates and Resets
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Data Breach
Data BreachNavigating the Threat Landscape: Understanding Exposure Management, Pentesting, Red Teaming and RBVM
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage




