Featured News
-

 109Cyber Crime
109Cyber CrimeBeware, Latest WhatsApp Scam Drops Malware on Your Device
Watch out for latest WhatsApp scam tricking users into opening malware link sent by ”friends” The favorite app of all youngsters and...
-
 223How To
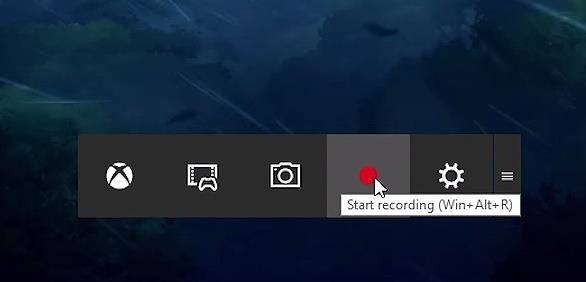
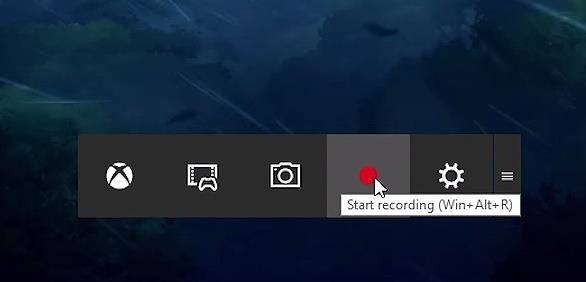
223How ToHow To Record Windows 10 Screen Using Xbox App
Short Bytes: Windows 10 has an inbuilt feature which lets a user record the Windows screen up to 2 hours. This screen...
-

 93Malware
93MalwareRemtasu is disguising itself as a tool to appropriate Facebook accounts
Almost a year ago we warned about the spreading of Remtasu, and far from lessening, we have been able to identify numerous...
-

 291Data Security
291Data SecurityHackers leaked DHS staff records, 200GB of files are in their hands
A hacker accessed an employee’s email account at the Department of Justice and stole 200GB of files including records of 9,000 DHS...
-

 208Vulnerabilities
208VulnerabilitiesDLL Hijacking Issue Plagues Products like Firefox, Chrome, iTunes, OpenOffice
Oracle patches Java installer against DLL hijacking issue. Oracle has released new Java installers to fix a well-known security issue (CVE-2016-0603) that also...
-
 266Hacked
266HackedHere’s How Windows 10 ‘Spying’ Forced A User To Switch To Linux Mint On His Computer
Short Bytes: Irritated by the telemetry and spying features in Windows 10, a Voat user decided to make the switch. After installing...
-

 90Data Security
90Data SecurityHacking Microsoft SQL Server Without a Password
During a recent penetration test, I was performing some packet captures and noticed some unencrypted Microsoft SQL Server (MSSQL) traffic. The syntax was...
-

 95Malware
95MalwareT9000 Backdoor Malware Targets Skype Users, Records Conversations
T9000 can also steal files from your hard drives. A new backdoor trojan is making the rounds, coming equipped with features that allow...
-
 188Data Security
188Data SecurityDyre crackdown, the biggest effort to date by Russian authorities against cybercrime
Russian authorities raided offices of a Russian film distribution and production company as part of an operation against the Dyre gang. Russian...
-

 182Geek
182GeekA Simple Hangman Game Implemented In 3 Lines Of Python
Short Bytes: Today I’m sharing a clever implementation of Hangman in python by programmer Danver Braganza. Take a look at this 3-lines-long program and...
-

 341Data Security
341Data SecurityNew Malware Targets Skype Users, Saves Screenshots, Records Conversations
The internet is abuzz with news about a new backdoor Trojan that is equipped with such advanced features that it can steal...
-

 280News
280NewsAnonymous Targets African Governments Against Corruption
Anonymous and supporters of LulzSec hackers target African governments against massive corruption. The online hacktivist Anonymous is targeting African countries to protest...
-

 188Geek
188GeekEyebrows Raised as The Pirate Bay Becomes Largest Video Streaming Portal
The brand new Torrents-Time browser plugin has helped The Pirate Bay take the industry of online video portal by storm as it...
-
 283News
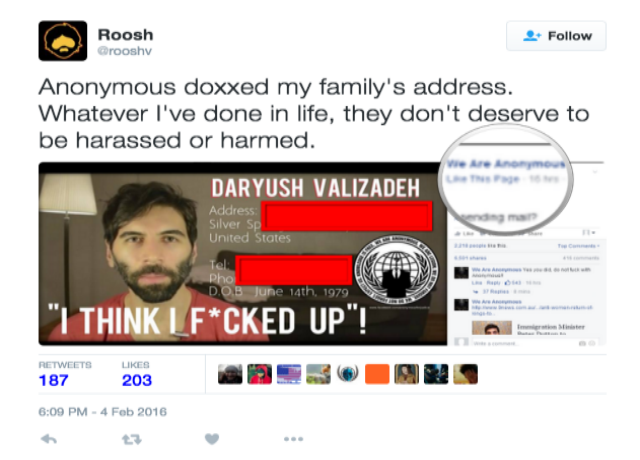
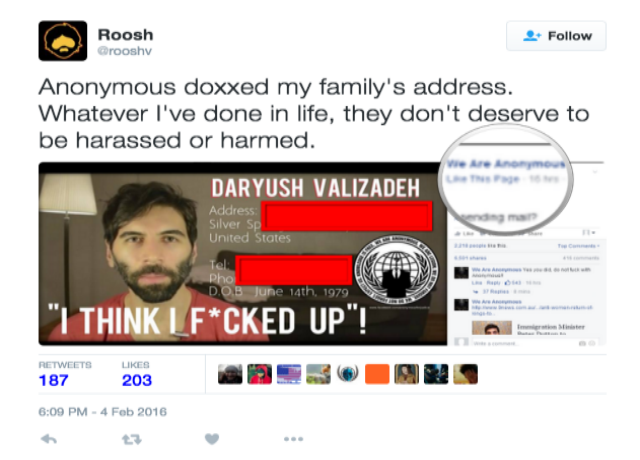
283NewsAnonymous Doxes and Forces Pro-Rape Pick-up Artist To Cancel His Meetings
Pro-rape and controversy child Roosh blames Hacktivists for hacking his family’s address and spreading hoax news The controversial ‘neo-masculinist” Roosh has claimed...
-
 195Hacked
195HackedWelcome To The Malware Museum: An Epic Online Collection Of Old-school Viruses
Short Bytes: Do you remember computer viruses from 1990’s that left you with no option but to reinstall your operating system? Well,...
-

 186Data Security
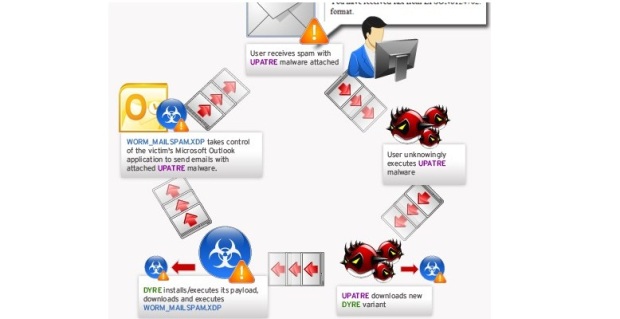
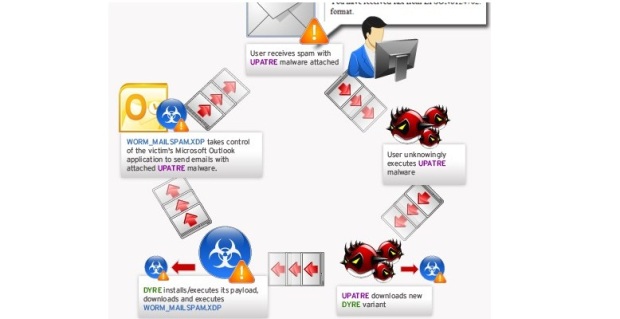
186Data SecurityBrazilian companies receive more than 40,000 spam emails in infostealer campaign
Spam campaign targets Portuguese-speaking firms in Brazil and other regions to deliver malware and steal sensitive data. Symantec has observed an ongoing...
-

 214Data Security
214Data SecurityJulian Assange’s 3.5-Year Detainment in Embassy Ruled Unlawful
THREE AND A half years after he sought temporary asylum in the Ecuadorean embassy in London only to find himself a captive...
-

 301Cyber Crime
301Cyber Crime7 Online Activities That Can Get You Arrested
Here are 7 activities that users should avoid doing on the Internet The Internet is a wonderland. It is a place where...
-
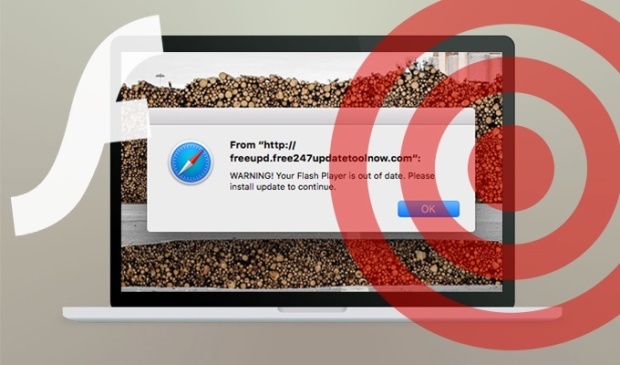
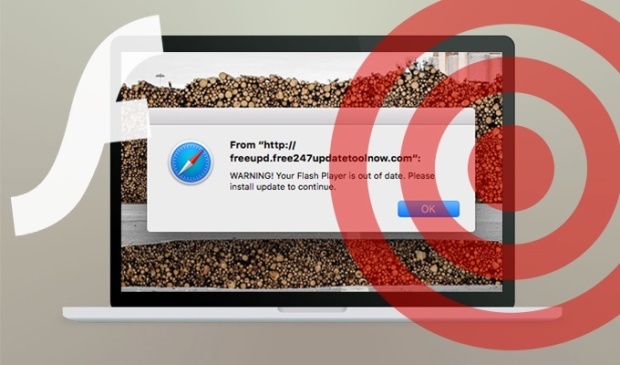 101Vulnerabilities
101VulnerabilitiesResearchers spotted a new OS X scareware campaign
Experts at the SANS Technology Institute spotted an OS X scareware campaign that leverages fake Adobe Flash Player installers. Johannes Ullrich, security...
-
 174Malware
174MalwareRoll up, roll up to the Malware Museum! Run classic DOS viruses in your web browser
Relive simpler times for some Friday fun. The Internet Archive has opened a new collection dubbed the Malware Museum that lets you run...
The Latest
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Cyber Attack
Cyber AttackMicrosoft Patches 61 Flaws, Including Two Actively Exploited Zero-Days
-
 Cyber Attack
Cyber AttackThe 2024 Browser Security Report Uncovers How Every Web Session Could be a Security Minefield
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Data Breach
Data BreachBlack Basta Ransomware Strikes 500+ Entities Across North America, Europe, and Australia
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Data Breach
Data BreachA SaaS Security Challenge: Getting Permissions All in One Place
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment




