Featured News
-

 163Geek
163Geek“New Facebook Message” Email Not Only Drops Malware But Phish You
If you receive an email claiming to have a ”new message” from Facebook just delete it because the attachment contains Nivdort malware...
-

 186News
186NewsAnonymous Declares Michigan Governor Guilty Over Flint Water Crisis
The infamous hacktivists collective Anonymous has declared Michigan governor Rick Snyder guilty for the ongoing Flint water contamination crisis. On Wednesday, a...
-

 225Cyber Events
225Cyber Events8 Most Popular and Best Hacking Tools
The internet has as many downsides as well as upsides but it’s the lack of knowledge about dangers on users’ behalf makes...
-
 182Malware
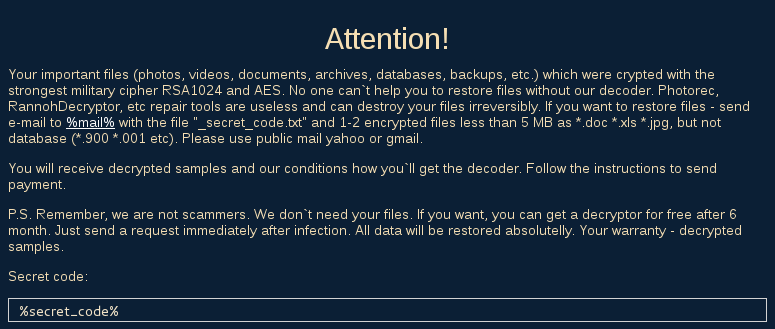
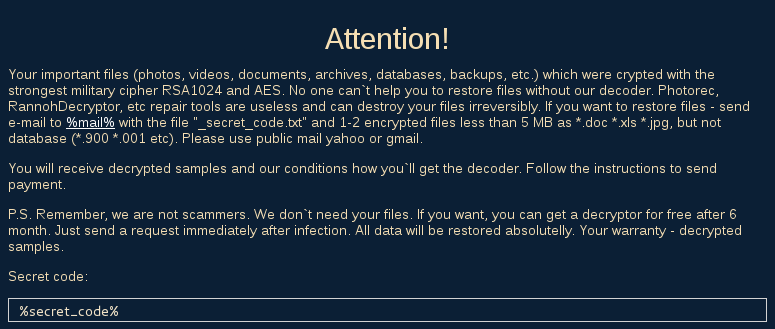
182MalwareLeChiffre, Ransomware Ran Manually
LeChiffre is yet another ransomware that recently has been observed to cause some major damage (in Mumbai – read more here). Not...
-
 98Incidents
98IncidentsWeb Reconnaissance Attack Infects 3,500 Websites, Possibly WordPress
Attackers are adding unauthorized code at the top of infected websites, over 3,500 8sites already infected. Alarms are ringing in Symantec’s offices,...
-

 217Malware
217MalwareTrojan.DNSChanger circumvents Powershell restrictions
In recent variants of the infamous DNS-changer adware we have found that the coders use a particularly interesting method to bypass the...
-

 80Data Security
80Data SecurityTorMail hack, FBI surgical operation, or dragnet surveillance?
In 2013 the FBI agents seized TorMail, now new information are emerging on the operations. Someone believes it was a surgical ops...
-

 268Geek
268GeekThis mystery house is blamed for lost phones in Atlanta City
The people come to the house and demand their lost phone back from this couple probably because of some error in phone-finding apps Christina...
-
 332News
332NewsOfficial Web Portal of Supreme Leader of Iran Ruhollah Khomeini Hacked
The official web portal of founder and first supreme leader of Iran Ruhollah Khomeini has been hacked by Saudi hackers While tensions...
-

 229Lists
229ListsBest Windows 10 Cortana Features and Commands
ShortBytes: FossBytes brings you the list of the best Cortana features and commands available for the Windows users. You can search for...
-

 199Incidents
199IncidentsChinese Group Trying to Exploit Old Fortinet SSH Backdoor
Scans for Fortinet devices have intensified. An unknown group has been scanning the Internet for old Fortinet equipment that includes a secret SSH...
-

 61Cyber Crime
61Cyber CrimeIrish lottery and ticket terminals knocked offline by DDoS attack
It should have been a great week for the Irish Lottery, with the largest jackpot (12 million euros) for 18 months up...
-
 99Malware
99MalwareDon’t open that Facebook email attachment — it could be malware
Two weeks ago, the Comodo Threat Research Lab discovered a malware campaign aimed at businesses and consumers using the WhatsApp mobile messaging...
-

 243Geek
243GeekTrumpScript – Two Coders Have Turned Donald Trump Into A Programming Language
Short Bytes: Participating in a hackathon and after a 20-hours long coding session, two programmers have written a python-based programming language called...
-

 273Data Security
273Data SecurityFBI May Have Hacked Innocent TorMail Users
Back in 2013, the FBI seized TorMail, one of the most popular dark web email services, and shortly after started to rifle...
-
 163Incidents
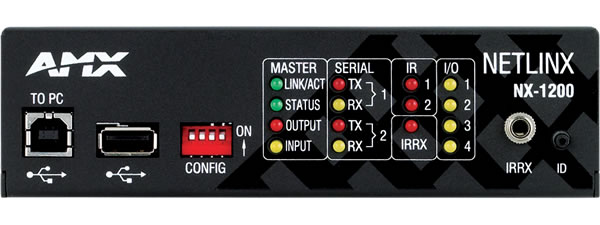
163IncidentsMedia devices sold to feds have hidden backdoor with sniffing functions
Highly privileged account could be used to hack customers’ networks, researchers warn. A company that supplies audio-visual and building control equipment to...
-

 194Data Security
194Data SecurityBritish Government Has Already Created a Data Encryption Protocol Complete With a Backdoor
GCHQ insists on shooting itself in the foot with backdoored VoIP encryption protocol, developed in-house by CESG. Britain’s intelligence agency, GCHQ (Government...
-

 307News
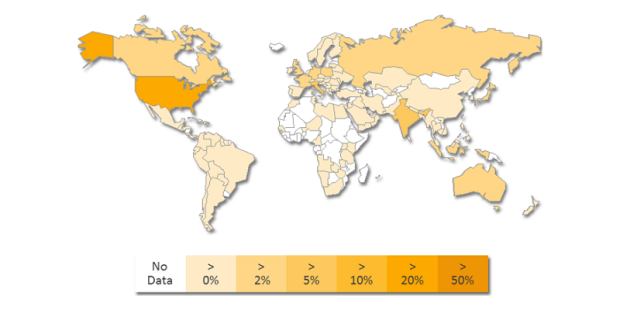
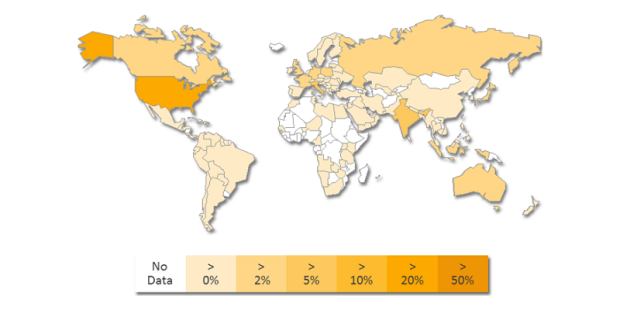
307NewsMore US Voters Data Circulating On The Dark Net
A country who has been spying on every computer in the world can’t protect voter data of its own citizens. Recent chronicles...
-

 288Data Security
288Data SecurityAlert Users: MSN Main Page Dropping Malware on User PCs
If you visit MSN.com there is a chance your PC has been affected with a malware — Outlook users should also check...
-
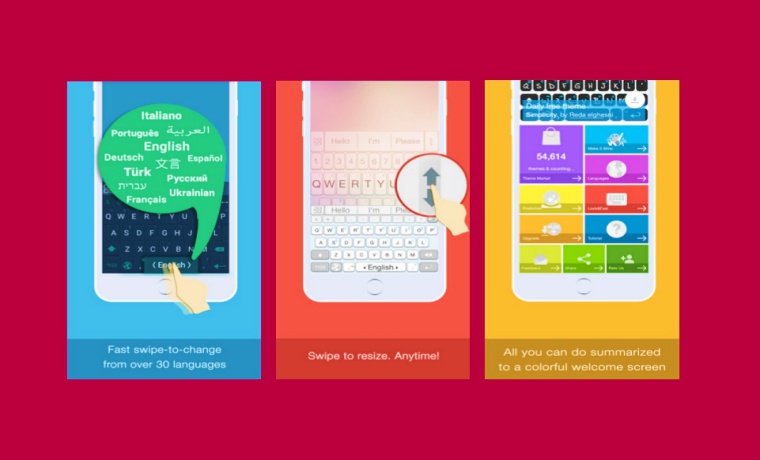
 288Geek
288GeekAI.Type Keyboard Bug on iOS Opens All Premium Features For FREE
Exclusive: An Apple fan has found a bug in AI.Type Keyboard on iOS allowing anyone to open All Premium Features For FREE Apple’s App...
The Latest
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Malware
MalwareChina-Linked Hackers Suspected in ArcaneDoor Cyberattacks Targeting Network Devices
-
 Malware
MalwareNew ‘Cuckoo’ Persistent macOS Spyware Targeting Intel and Arm Macs
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Malware
MalwareHackers Increasingly Abusing Microsoft Graph API for Stealthy Malware Communications
-
 Malware
MalwareNSA, FBI Alert on N. Korean Hackers Spoofing Emails from Trusted Sources
-
 Vulnerabilities
VulnerabilitiesFour Critical Vulnerabilities Expose HPE Aruba Devices to RCE Attacks
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Vulnerabilities
VulnerabilitiesWhen is One Vulnerability Scanner Not Enough?
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Vulnerabilities
VulnerabilitiesNew “Goldoon” Botnet Targets D-Link Routers With Decade-Old Flaw
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Malware
MalwareZLoader Malware Evolves with Anti-Analysis Trick from Zeus Banking Trojan
-
 Malware
MalwareEternal Malware: CVE-2024-3400 Rootkits Persist Through Palo Alto Firewalls Updates and Resets
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024




