Featured News
-
 290Geek
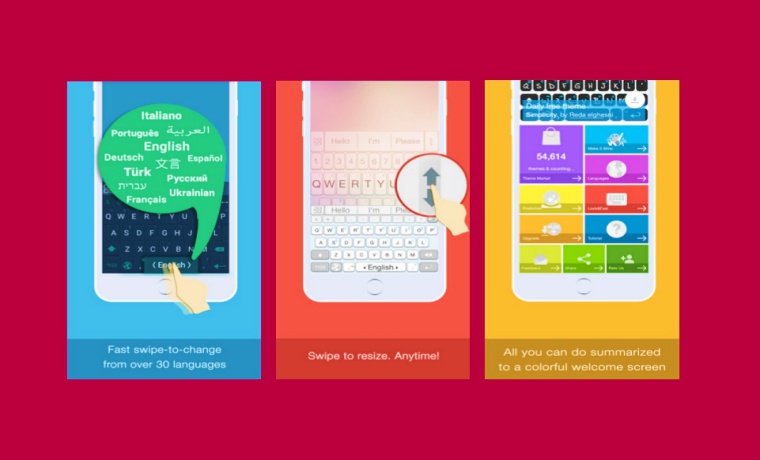
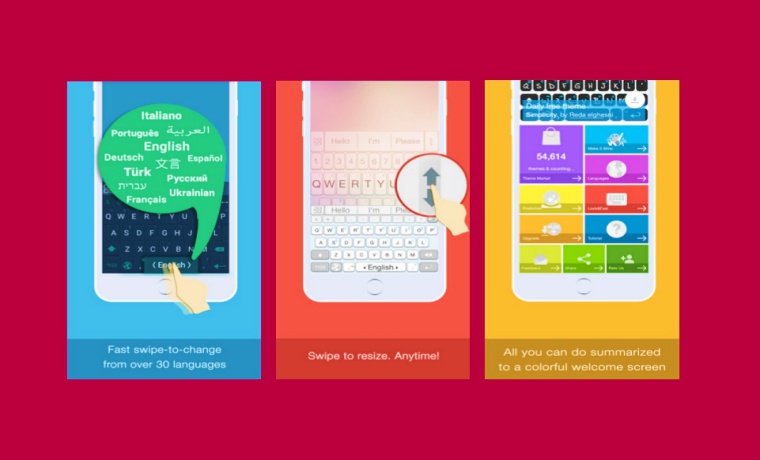
290GeekAI.Type Keyboard Bug on iOS Opens All Premium Features For FREE
Exclusive: An Apple fan has found a bug in AI.Type Keyboard on iOS allowing anyone to open All Premium Features For FREE Apple’s App...
-
 372How To
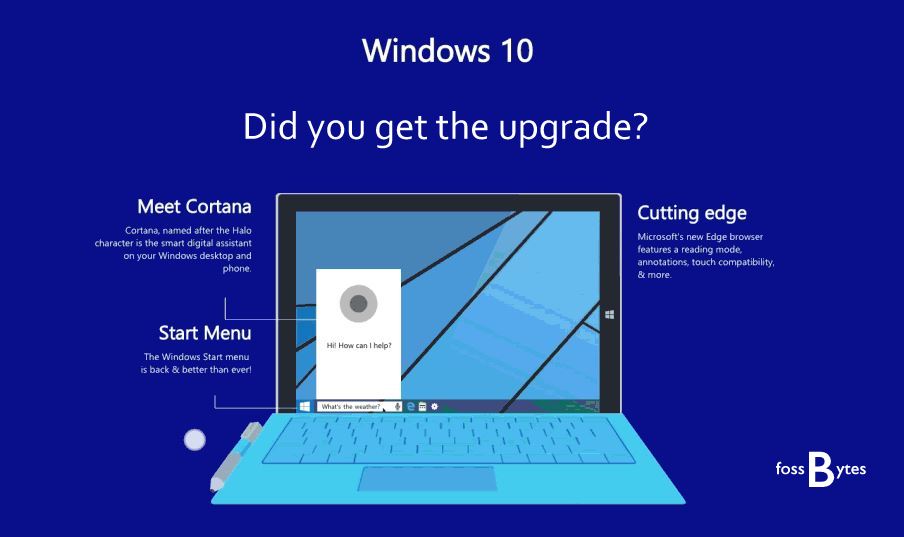
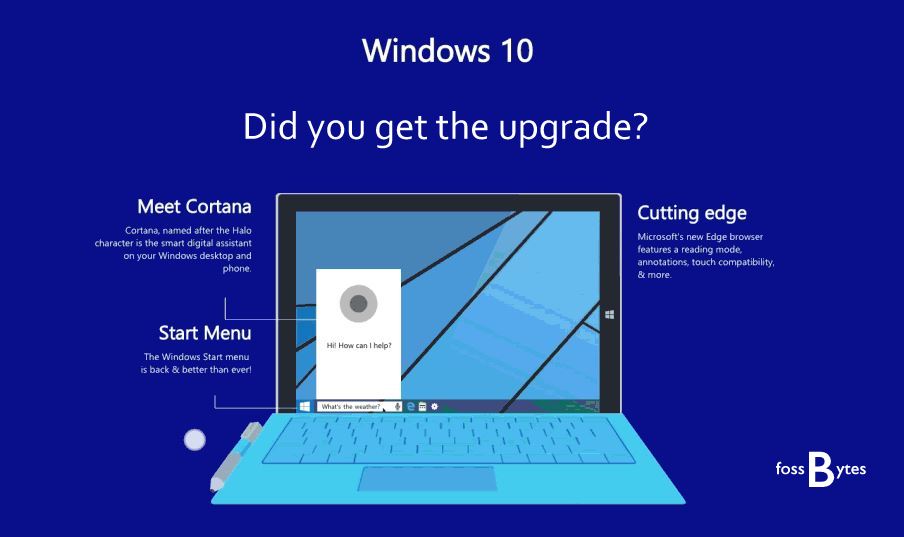
372How ToHow To Remove Pre-installed And Suggested Apps In Windows 10
Short Bytes: Though Windows 10 comes with free updates but along with that, comes a lot of unwanted pre-installed and suggested apps in Windows...
-

 188News
188NewsPsycho Voyeur Hacked Baby Monitor to Scare Toddler with Spooky Sounds
A cybercriminal was heard scaring baby by hacking into the nanny cam — “Wake up little boy, daddy’s looking for you.” “Look someone’s...
-
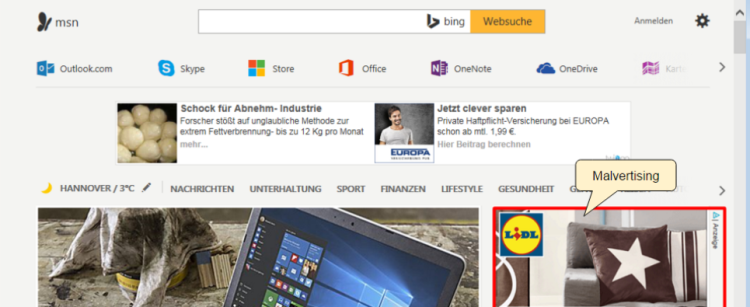
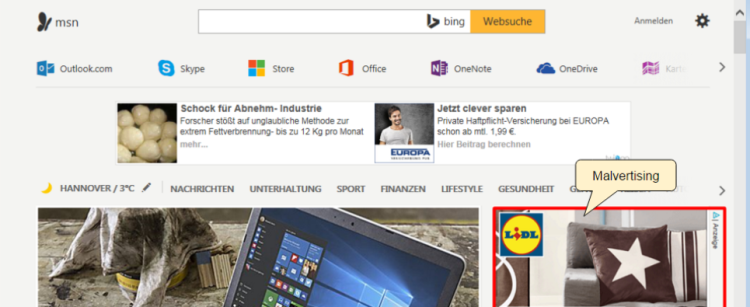 86Malware
86MalwareMSN Home Page Drops More Malware Via Malvertising
Malvertisers are once again abusing ad technology platform AdSpirit and exposing visitors of the MSN homepage to malware. These attacks appeared to...
-

 181Geek
181GeekWhy Is Linux Foundation’s Latest Change A Bad News For Linux And Open Source?
Short Bytes: Up until recently, the Linux Foundation allowed the individual members to elect two board members and ensure that the voice...
-

 201Data Security
201Data SecurityTeslaCrypt Decrypted: Flaw in TeslaCrypt allows Victim’s to Recover their Files
For a little over a month, researchers and previous victims have been quietly helping TeslaCrypt victims get their files back using a flaw in...
-

 191Vulnerabilities
191VulnerabilitiesIntel Fixes Security Bug to Prevent Attackers From Hijacking the Driver Update Process
Intel-powered laptops are safe again. So are desktops. Intel has released version 2.4 of the Intel Driver Update Utility, fixing a critical...
-

 256News
256NewsTurk Hack Team Conducting DDoS Attacks on Iran and Russian Websites
Turk Hack Team conducted several cyber attacks on top Iranian and Russian Ministry websites since the beginning of the conflict at the...
-

 305News
305News10 Most Notorious Hacking Groups
Here are top 10 hacking and hacktivist groups that changed the world like no one else. Hacking has grown massively in the...
-

 256Geek
256GeekFugitive Tells Police To Use Better Photo of Him on Facebook, Gets Arrested
Ohio man Sends Selfie To Police Saying It is a “better photo” than the “terrible” mug shot and Gets Arrested It has...
-
 99Cyber Crime
99Cyber CrimeNew wave of cyberattacks against Ukrainian power industry
ESET has discovered a new wave of cyberattacks attacks against Ukraine's electric power industry. Interesting, the malware that was used is not...
-

 230Geek
230GeekFacebook Integrates TOR into its Android App For Better Privacy
Privacy seekers and admirers have every reason to rejoice since Facebook is bringing TOR, the free anonymizing software to support its android...
-
 89Cyber Crime
89Cyber CrimeESET Trends for 2016: Threats keep evolving as security becomes part of our lives
ESET's Trends for 2016: (In)Security Everywhere report includes a review of the most important events of last year and outlines trends in...
-

 103Malware
103MalwareAsacub Evolves from Simple Spyware to Full-On Android Banking Trojan
Cyber-crooks secretly develop new Asacub Android malware, deploy it for the first time this Christmas. Over the past six months, security experts from...
-

 459Lists
459ListsThese Are The 10 Best Jobs In Tech Field To Apply For In 2016
Short Bytes: Looking for a new job in tech? Here’s an article telling you the 10 bets jobs in the tech field...
-

 173Data Security
173Data SecurityHot Potato exploit mashes old vulns into Windows System ‘sploit
Exploit takes a long time to cook Windows, but gives hackers a menu of evil options. Shmoocon Foxglove Security bod Stephen Breen...
-
 187Incidents
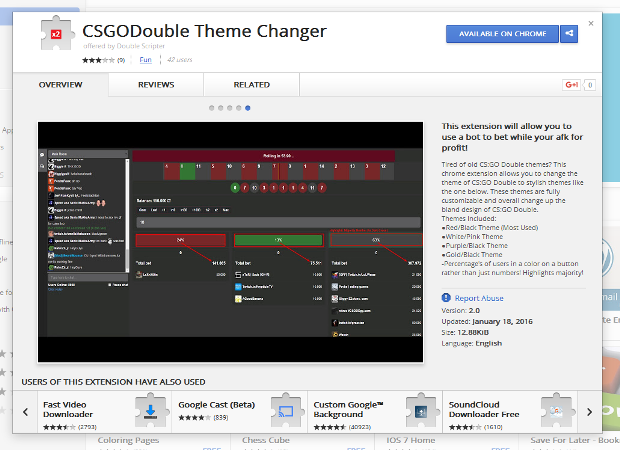
187IncidentsChrome Extensions Steal Your Steam Inventory
Steam scammer caught red-handed by Panda Security researcher. A crafty Steam user created four Chrome extensions that would empty out his victim’s Steam...
-

 232Lists
232Lists10 Best Emulators For Android 2016 — Run Android Apps On PC, PSP, N64
Short Bytes: fossBytes brings you the top 10 best emulators for Android 2016. This list also includes Android emulators for PC, best N64 emulator...
-
 171Hacked
171HackedWindows XP Computers Cause Havoc In Hospital After Getting Virus Infection
Short Bytes: Royal Melbourne Hospital in Australia was still running Windows XP and little did they know about the upcoming havoc that...
-
 109Data Security
109Data SecurityFacebook Android App Gets Built-in TOR Support But Still Needs Your Real Name
Short Bytes: If you are interested in increasing the security and privacy of your network traffic, here’s a great news for you....
The Latest
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Cyber Attack
Cyber AttackMicrosoft Patches 61 Flaws, Including Two Actively Exploited Zero-Days
-
 Cyber Attack
Cyber AttackThe 2024 Browser Security Report Uncovers How Every Web Session Could be a Security Minefield
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Data Breach
Data BreachBlack Basta Ransomware Strikes 500+ Entities Across North America, Europe, and Australia
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Data Breach
Data BreachA SaaS Security Challenge: Getting Permissions All in One Place
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment




