Featured News
-
 167Vulnerabilities
167VulnerabilitiesAndroid and Linux Zero-Day Gives Attackers Root Access
A new zero-day vulnerability allows Android or Linux applications to escalate privileges. Security researchers have discovered a new zero-day vulnerability in Linux kernel that...
-

 95Data Security
95Data SecurityA new archive of US voting records appeared on the Dark Web
A new archive containing alleged voting records of millions of US citizens is available on a hidden service on the dark web....
-

 268News
268NewsChina’s Top University Website Hacked by Pro-ISIS Hacker
A hacker who claims to be the ally of the ISIS terrorist group managed to hack the official website of Tsinghua University, China’s...
-
 141Data Security
141Data SecurityLinux Hit with Malware That Saves Activity Screenshots Every 30 Seconds
A new Linux malware has been discovered which aims to help criminals steal data and spy on the PCs of infected users....
-

 305News
305NewsCracka with Attitude Hackers Claim To Hack Email ID of Obama’s Senior Advisor
Government Officials under Attack: Hackers Who targeted CIA Director now reach the White House The hacking group Crackas With Attitude have been...
-

 362Data Security
362Data SecurityUkraine Airport’s Computer Networks Infected with Malware
The computer networks installed at the main airport in Kiev, Ukraine, have been identified as containing malware. The discovery was made public...
-
 105Geek
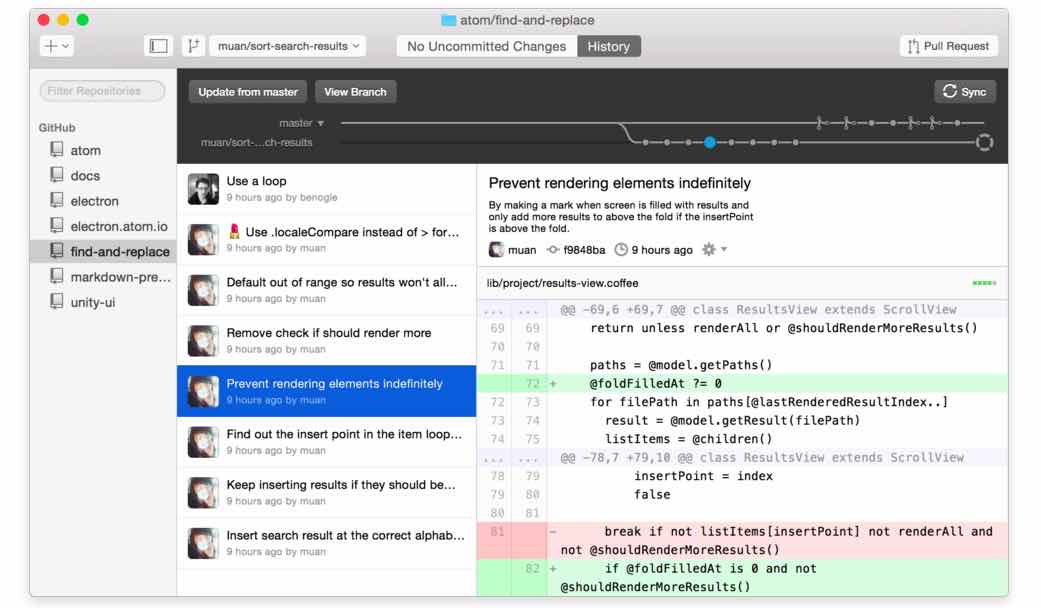
105GeekDear GitHub, More Than 1000 Famous Developers Are Mad At Your Issues Tracker
Short Bytes: Annoyed by GitHub’s outdated Issues Tracker feature, a CloudFlare developer has written an open letter to GitHub, suggesting the website to...
-
 285Geek
285GeekSorry People But Windows 10 is Only For Latest PCs — Confirms Microsoft
Only Latest Technology PCs will run Windows 10 – Confirms Microsoft Now this can be termed as nothing else but a bombshell...
-

 235Hacked
235HackedThese White Hat Hackers Tell You All The Different Ways Your Phone Can Be Hacked
Short Bytes: As new mobile threats continue to emerge, the white hat hackers are busy busting the ways your phone can be...
-

 143Android Hacking
143Android HackingDendroid – Android RAT
Dendroid is a HTTP RAT that is marketed as being transparent to the user and firmware interface, having a sophisticated PHP panel,...
-

 102Android Hacking
102Android HackingStealing Windows Passwords with your Android Device
A hacking tool discovered by analysts at F-Secure, which is capable of stealing information from a connected Windows machine. USB Cleaver seems...
-

 430News
430NewsTurkish Hackers Deface Russian Bank Website
Turkish hackers target Russian banking website, mock the Russian SU-24 jet incident. A group of Turkish hackers going by the online handle WKPF...
-
 210Malware
210MalwareNew Trojan Spies on Linux Users by Taking Screenshots and Recording Audio
Dr.Web, a Russian antivirus maker, has detected a new threat against Linux users, the Linux.Ekocms.1 trojan, which includes special features that allow...
-
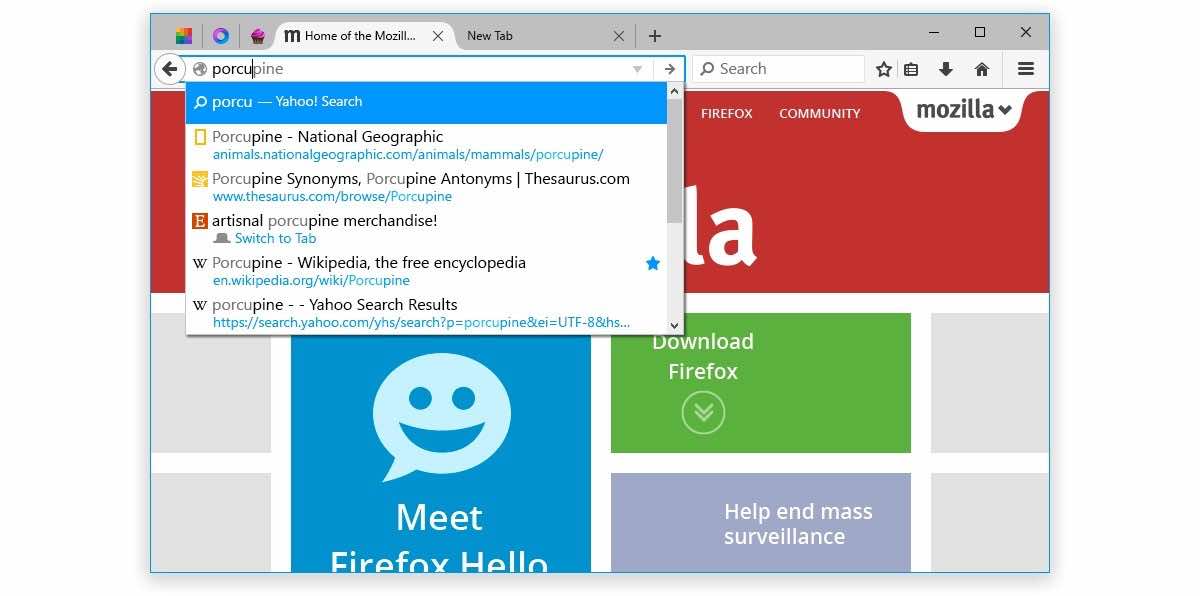
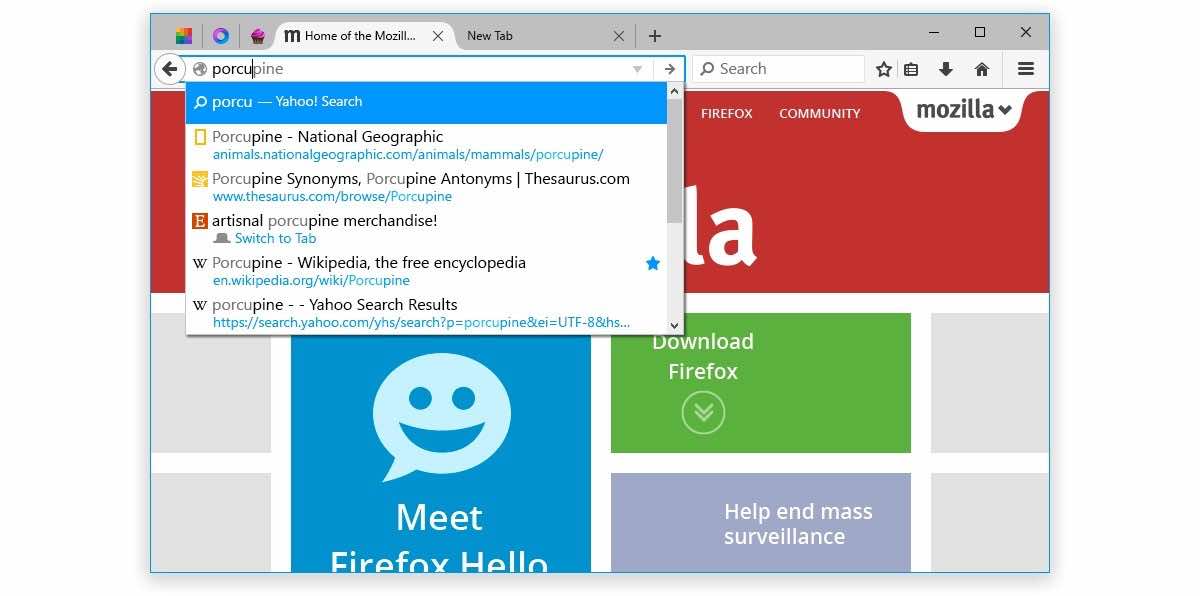 189Lists
189ListsWhat Is The Best Windows 10 Web Browser – According To Benchmark Tests
Short Bytes: When we talk about the best Windows 10 web browsers, our list narrows down to Chrome, Firefox, Edge etc. Microsoft...
-

 66Data Security
66Data SecurityShop online at Asda? Website vuln created account hijack risk
Walmart-owned store patches hole, but it was open for nearly 2 years. Retailer Asda dragged its heels for nearly two years before...
-

 190Data Security
190Data SecurityTinba, a 20KB trojan that scares banks in Singapore and Indonesia
A new variant of the infamous Tinba banking trojan has emerged in the wild and is targeting financial institutions in the Asia...
-
 93Geek
93GeekTwitter is down worldwide (Update)
Twitter is down. Yes, the social media giant’s website and mobile apps are inaccessible at the moment. Visitors to the website were greeted...
-

 156Vulnerabilities
156VulnerabilitiesYahoo! Mail! Had! Nasty! XSS! Bug!
Finnish fellow scores $10k bug bounty for reporting malformed HTML mess. Video A stored XSS vuln in Yahoo! Mail has netted Finnish...
-

 111Incidents
111IncidentsBelinda Carlisle’s Official Website Hacked, Sports Viagra Banner
At some point over the weekend, the official website of Belinda Carlisle was compromised, displaying banner ads for a Canadian Pharmacy page....
-

 226Data Security
226Data SecurityHere’s how a cheap webcam can be converted into network backdoor
This is how a $30 D-Link webcam can be converted into a backdoor. Researchers at US security firm Vectra Networks have hacked a ‘tiny’...
The Latest
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Cyber Attack
Cyber AttackMicrosoft Patches 61 Flaws, Including Two Actively Exploited Zero-Days
-
 Cyber Attack
Cyber AttackThe 2024 Browser Security Report Uncovers How Every Web Session Could be a Security Minefield
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Data Breach
Data BreachBlack Basta Ransomware Strikes 500+ Entities Across North America, Europe, and Australia
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Data Breach
Data BreachA SaaS Security Challenge: Getting Permissions All in One Place
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment




