Featured News
-

 265Geek
265GeekKickass Torrents The Latest Victim of DDoS Attacks
The Internet’s largest torrents platform Kickass faced major outage due to a series of powerful DDoS attacks by unknown hackers Kickass Torrents...
-

 277Cyber Crime
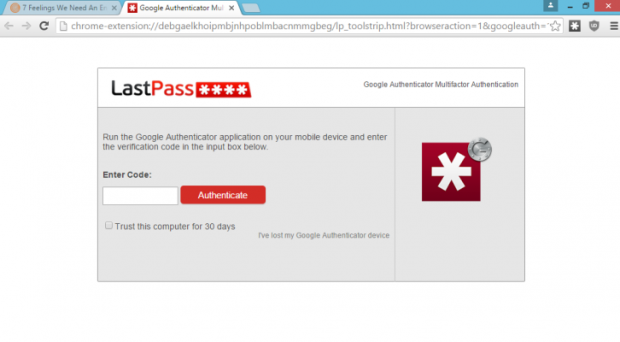
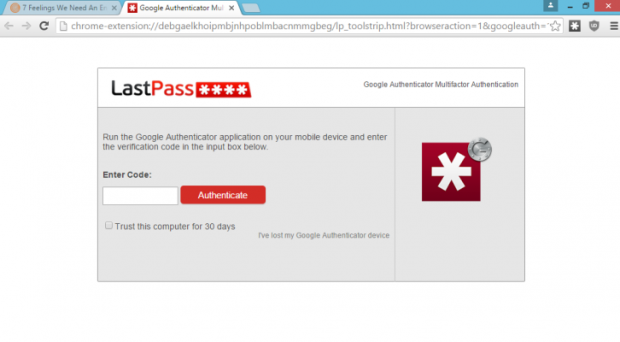
277Cyber CrimeBypassing LastPass’s Security? A phishing Attack Would Serve Just Right
LastPass Password Manager – renowned for being a secure vault for user’s passwords, has recently demonstrated vulnerabilities that could expose many users’...
-
 108News
108NewsCryptsy Hacked: Bitcoin Worth $USD 6 Million Stolen
The hacker inserted a Trojan malware into Cryptsy’s code so that he could access precious information and transfer cyber currencies. Paul Vernon, also...
-

 296News
296NewsAngler Exploit Kit’s Successful Run Continues- More Than 90,000 Websites Infected So Far
Angler Exploit Kit is not going anywhere, it’s here to stay and already compromised 90,000 websites. The Angler Exploit Kit (AEK) is increasing its...
-

 107Data Security
107Data SecurityFeds Raided Another Chicago Home in Nude Celeb Hack Investigation, Still No Charges Pressed
In the summer of 2014, anonymous hackers flooded the internet with private nude photos of major (and minor) celebrities. Two years later,...
-

 186Data Security
186Data SecurityNew Interesting revelation on the Stuxnet cyber weapon
New interesting revelation about the Stuxnet attack published by The New York Times, a must read for experts. The popular cyber security...
-

 321Cyber Events
321Cyber Events5 most dangerous cyber security vulnerabilities that are exploited by hackers
Here are 5 of the most dangerous cyber security vulnerabilities that are exploited by hackers All the major government organizations and financial firms...
-

 158Incidents
158IncidentsUkraine blames Russia of cyber attacks against the Boryspil airport
Ukrainian Government is accusing Russia of organizing hacker attacks against the Boryspil airport’s networks. Cyber security experts of the State Service of...
-

 223Geek
223GeekKnow The Best Programming Language For You By Taking This 1-Minute Quiz
Short Bytes: Your inspiration behind learning how to code could be anything. It could be a desire to become a professional developer...
-
 213Data Security
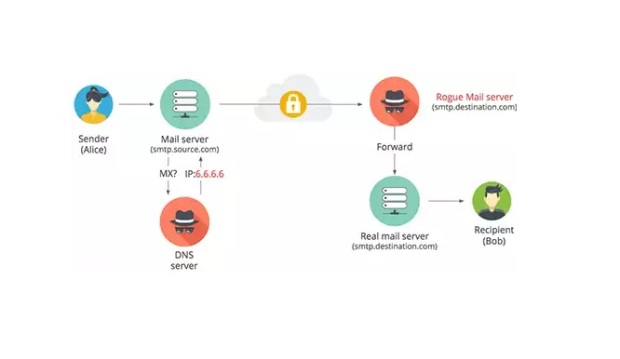
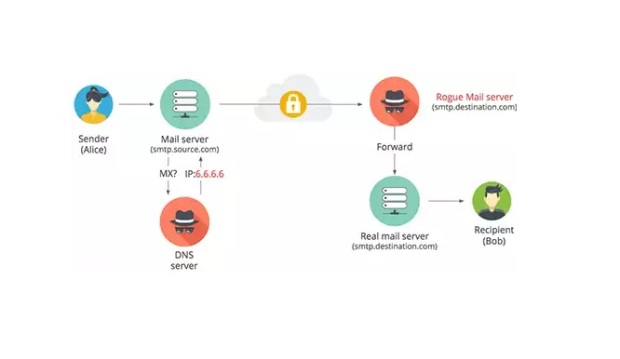
213Data SecurityHow email in transit can be intercepted using DNS hijacking
This article looks at how an attacker can intercept and read emails sent from one email provider to another by performing a...
-
 123Hacked
123HackedA Hacker’s Paradise: Top 20 Cities With Most Malware Infections
Short Bytes: In Enigma Software’s yearly top 20 cities list, Tampa maintains its top spot with 506% higher infections than the national average....
-

 167Hacked
167HackedWhat Is A Web App Attack, How Does It Work — 5 Stages Of A Web App Attack
Short Bytes: A Web App Attack is one of the biggest threats faced by websites and online businesses. In this article, we...
-

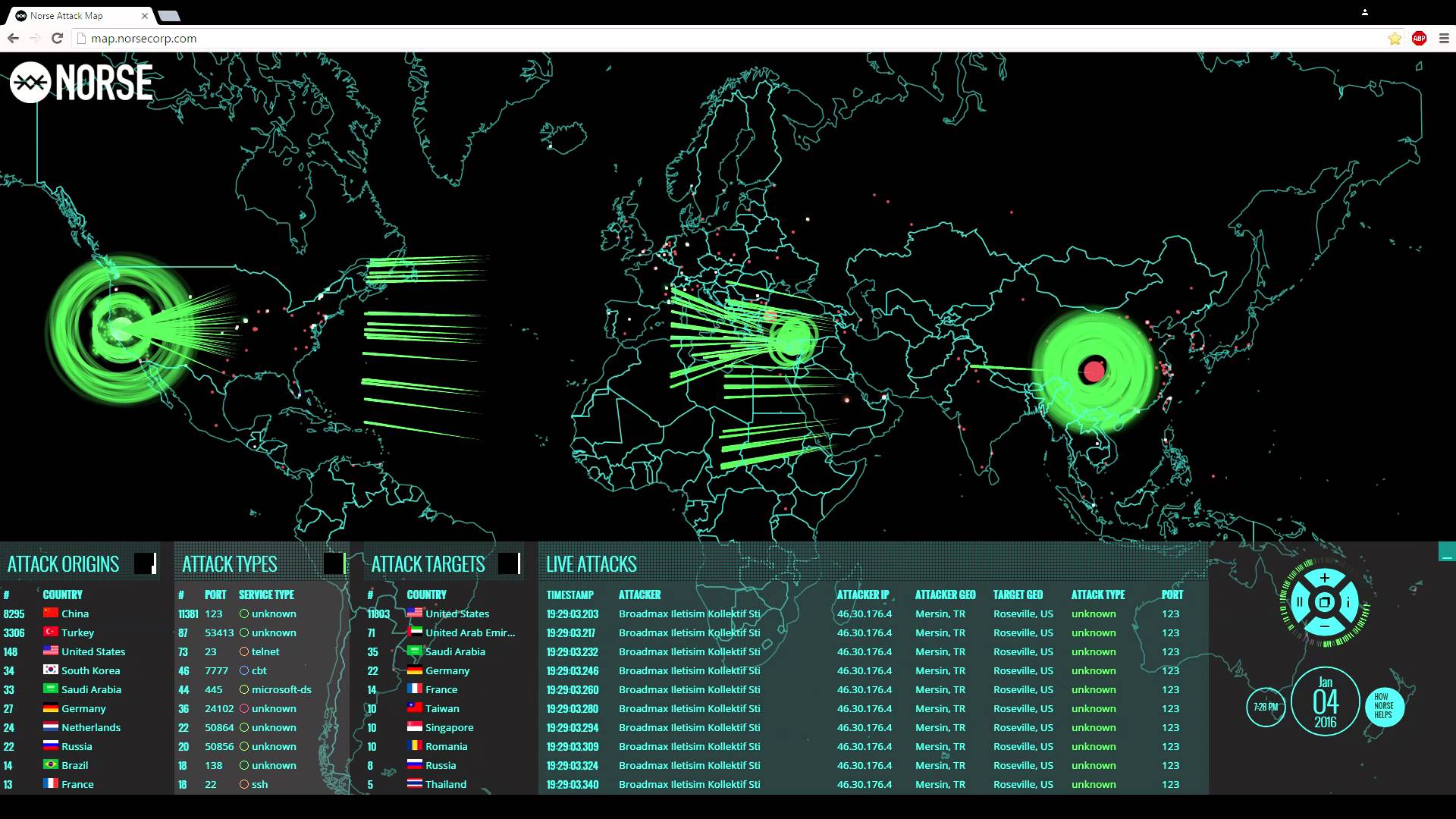
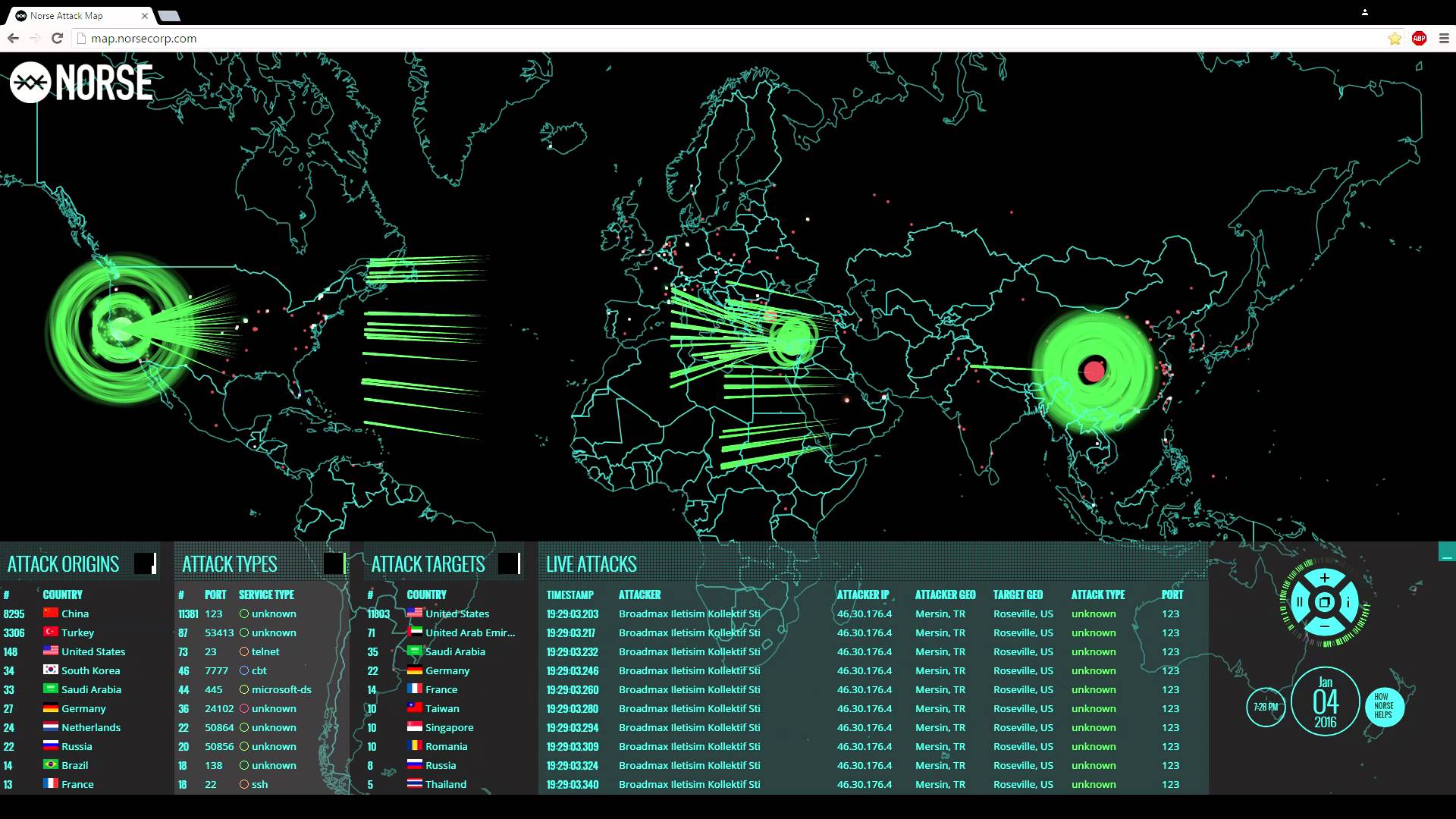
 158Data Security
158Data SecurityHack Like a Pro: How to Hack Like the NSA
Over the years, I have written many articles here on Null Byte chronicling the many the hacks of the NSA, including the...
-
 199Incidents
199IncidentsLastPass phishing attack could allow attackers to steal your passwords
At the recent ShmooCon conference a researcher presented a LastPass phishing attack that could allow hackers to steal your password. We discussed...
-

 371Cyber Events
371Cyber EventsProgram Languages That Generate Most Software Security Bugs
You maybe a top notch developer or programmer but do you know which program languages generate most software security bugs? Recently, a lot...
-
 255Lists
255Lists10 Facts About Wikipedia That You Didn’t Know
Short Bytes: Wikipedia is the world’s seventh most popular website. This free online encyclopedia has been providing us information from the past...
-
 323Denial of service
323Denial of serviceHow to kick players Offline on PS4 / Xbox One
Using a few windows tools we are able to kick players offline and automatically win by default. Whether you are a...
-
 341Hacked
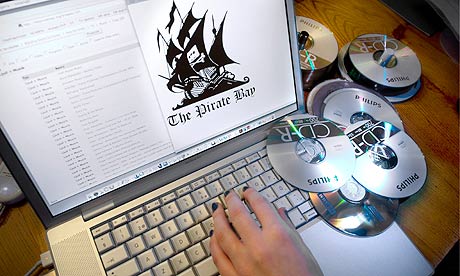
341HackedThe Anatomy of Copyright Lawsuits – Number Of People Sued Drops By 84% Since 2010
Image: Wtamu.edu Short Bytes: A report published by Mathew Sag claims that the number of people sued for illegal file sharing in...
-

 277Social Media Hacking
277Social Media HackingBypass Facebook Photo Tag Verification
Facebook notices when a security feature has been abused by placing a photo tag verification to reduce the amount of fake accounts....
-

 282Cyber Events
282Cyber EventsCyber Attacks Threatening Oil and Gas Sector Severely Now Than Ever Before
It is being reported that the oil and gas sectors have suddenly become more vulnerable to cyber threats. In 2013, we at...
The Latest
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Malware
MalwareChina-Linked Hackers Suspected in ArcaneDoor Cyberattacks Targeting Network Devices
-
 Malware
MalwareNew ‘Cuckoo’ Persistent macOS Spyware Targeting Intel and Arm Macs
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Malware
MalwareHackers Increasingly Abusing Microsoft Graph API for Stealthy Malware Communications
-
 Malware
MalwareNSA, FBI Alert on N. Korean Hackers Spoofing Emails from Trusted Sources
-
 Vulnerabilities
VulnerabilitiesFour Critical Vulnerabilities Expose HPE Aruba Devices to RCE Attacks
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Vulnerabilities
VulnerabilitiesWhen is One Vulnerability Scanner Not Enough?
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Vulnerabilities
VulnerabilitiesNew “Goldoon” Botnet Targets D-Link Routers With Decade-Old Flaw
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Malware
MalwareZLoader Malware Evolves with Anti-Analysis Trick from Zeus Banking Trojan
-
 Malware
MalwareEternal Malware: CVE-2024-3400 Rootkits Persist Through Palo Alto Firewalls Updates and Resets
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024




