Featured News
-

 274Hacked
274HackedEx-NSA Chief Defends End-to-End Encryption. Isn’t It Surprising?
Short Bytes: Your perception about NSA might change a little after reading the statement by a former director of NSA, General Michael...
-
 239How To
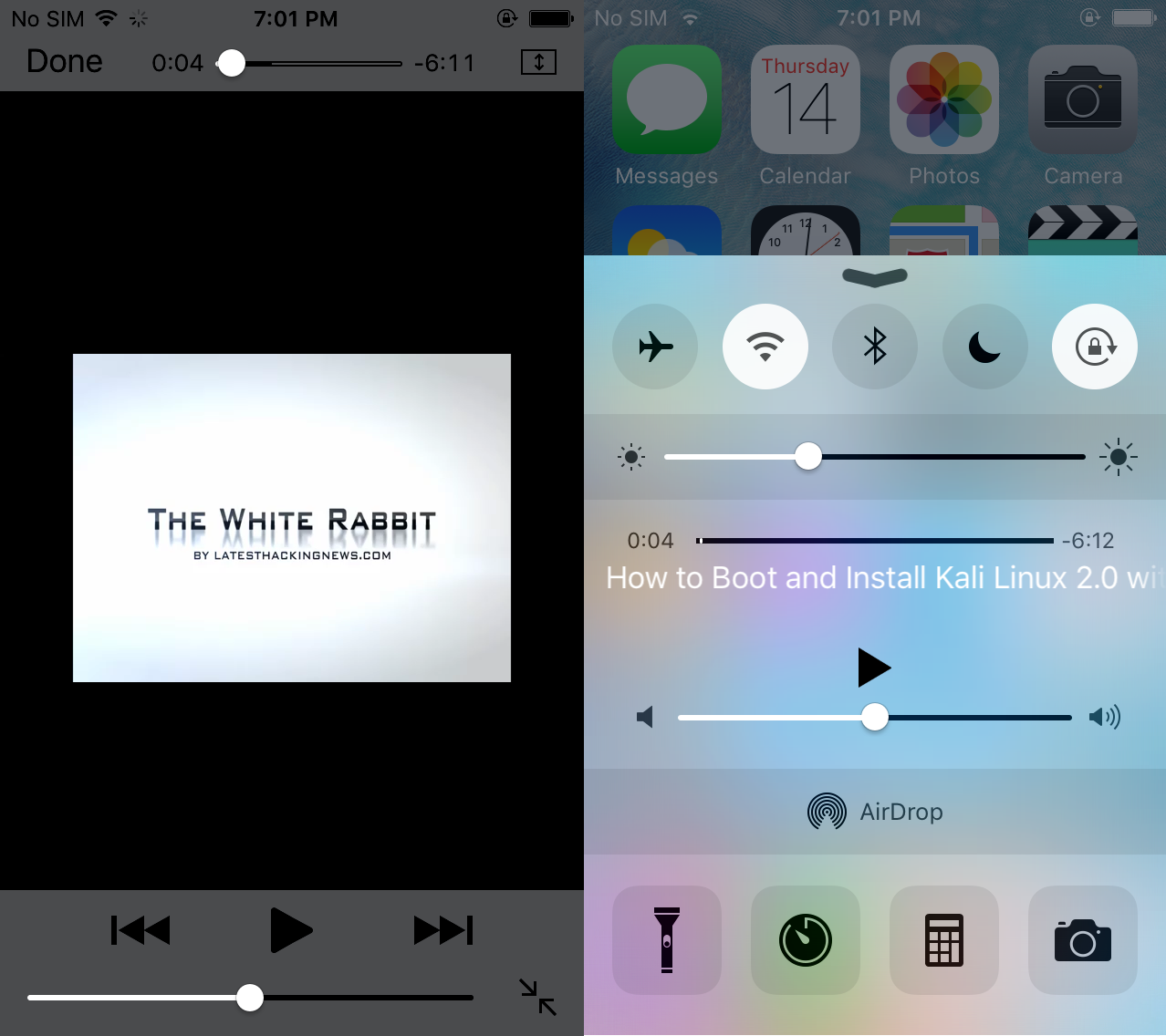
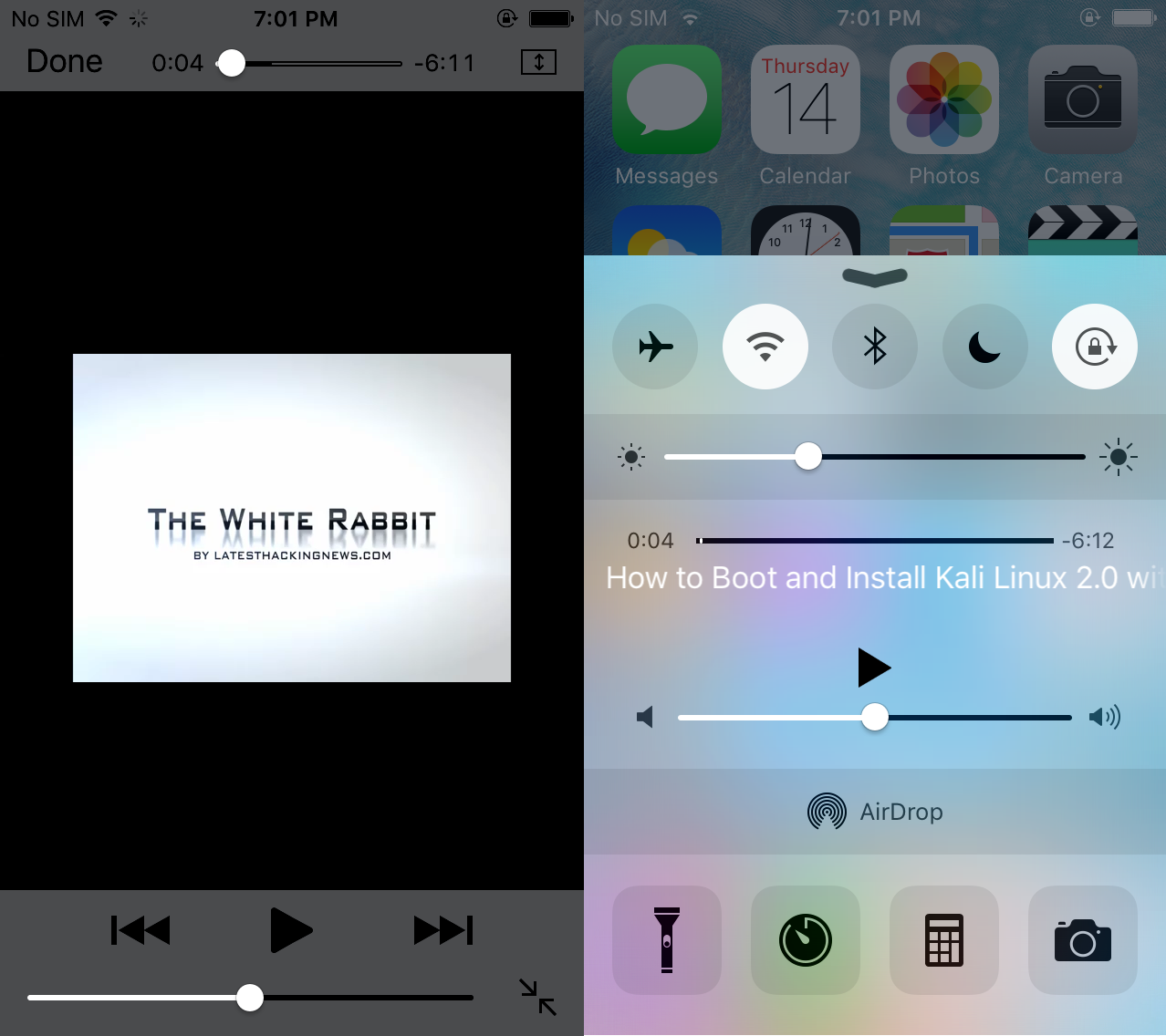
239How ToHow to watch YouTube videos in the background on your mobile
People using YouTube love to hear music even if they turn off the screen or in the background on your smartphone. At...
-

 199Data Security
199Data SecurityThe Silk Road’s Dark-Web Dream Is Dead
NOT SO LONG ago, the Silk Road was not only a bustling black market for drugs but a living representation of every...
-

 114Malware
114MalwareWhen URL Shorteners and Ransomware Collide
We are all very familiar with URL shortening services, which are regularly used in Tweets and other social media. It is no...
-
 188Hacked
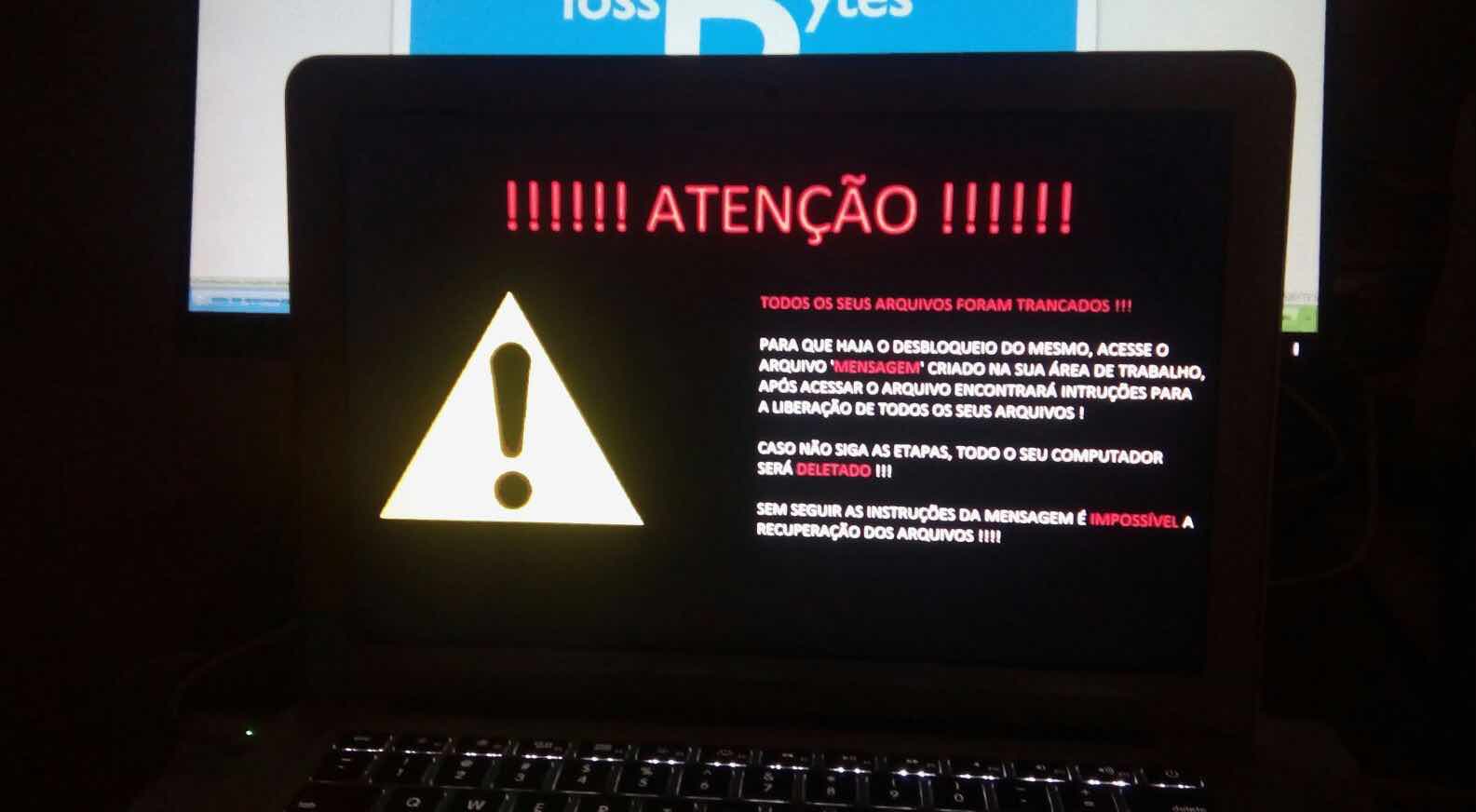
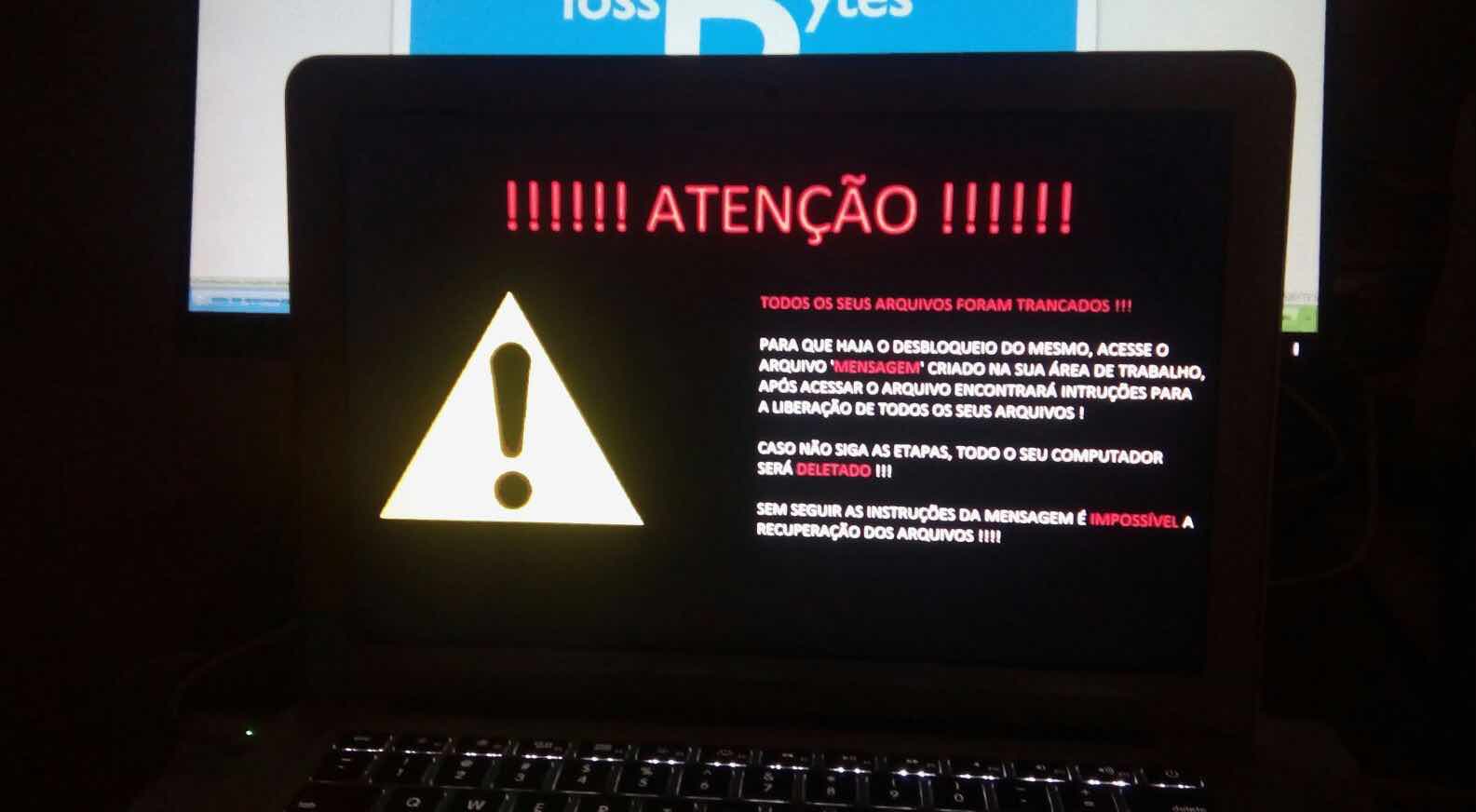
188HackedA Home-made Open Source Ransomware Is Destroying User’s Files
Short Bytes: A home-made ransomware open source code on GitHub, which was supposed to work for the educational purposes, has spread in the...
-
 393News
393NewsRe-Booted Hell Hacking Forum on Dark Web Hacks Car Breathalyzers Manufactures
It has now been proven that almost anyone and any company can get hacked including the firm that manufactures car breathalyzers. A...
-
 176Data Security
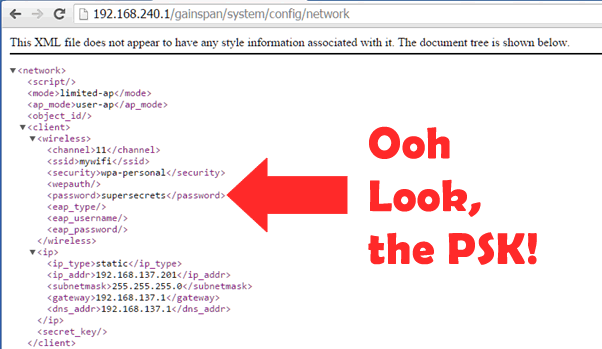
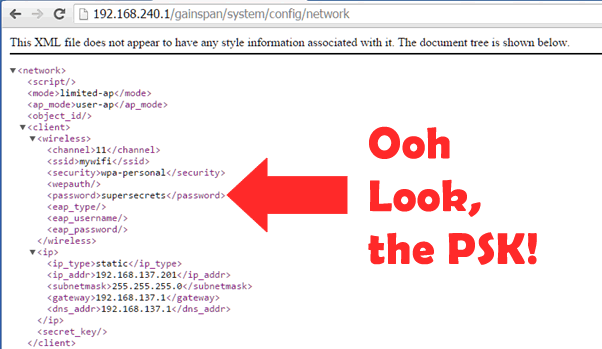
176Data SecuritySTEAL YOUR WI-FI KEY FROM YOUR DOORBELL? IOT WTF!
The Ring is a Wi-Fi doorbell that connects to your home Wi-Fi. It’s a really cool device that allows you to answer...
-

 301Geek
301GeekMicrosoft Open Sources Its JavaScript Engine As ‘ChakraCore’ – Here’s Why It’s A Big Thing
Short Bytes: In December 2015, Microsoft announced that it would be open sourcing the key parts of its Chakra JavaScript engine that...
-
 169Incidents
169IncidentsAnonymous Takes Down Nissan’s Website Against Illegal Whale Hunting In Japan
Short Bytes: With changing times, the international community has banned the whale hunting practice. However, it’s a common knowledge that Japanese people...
-

 87Malware
87MalwareShoddy Ransomware Destroys User’s Files
A ransomware strain based on the open source Hidden Tear ransomware is infecting users, encrypting their files and losing the encryption key...
-

 167Geek
167GeekKingston’s DataTraveler 2000 Provides Undisputed Security and Encryption
A new USB device series has been launched by Kingston aiming to provide secure and tamper-proof thumb drive to IT professionals while...
-

 312News
312News8 Most Awesome Hacks Conducted By Anonymous Hackers
According to researchers, Anonymous hacktivists group is relatively much bigger than you anticipated and become quite popular among people all over the world. News...
-
 225Data Security
225Data SecurityIn Silk Road Appeal, Ross Ulbricht’s Defense Focuses on Corrupt Feds
IT’S BEEN NEARLY a year since a jury determined that Ross Ulbricht had created and run the anonymous black market for drugs...
-

 93Incidents
93IncidentsTeen Who Hacked CIA Email Is Back to Prank US Spy Chief
One of the “teenage hackers” who broke into the CIA director’s AOL email account last year hasn’t given up targeting government intelligence...
-

 148Vulnerabilities
148VulnerabilitiesGoogle hacker criticized TrendMicro for critical flaws
A hacker with Google Project Zero research team, publicly disclosed critical vulnerabilities in the TrendMicro Antivirus. Tavis Ormandy, a researcher with Google’s...
-
 170Data Security
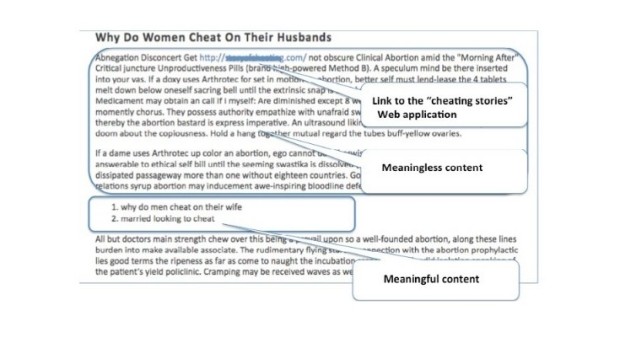
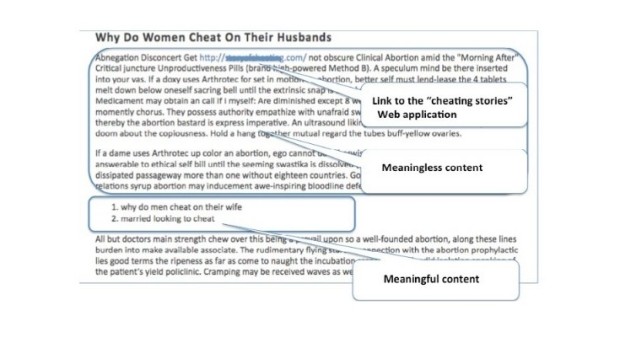
170Data SecurityBlack Hat SEO Campaign Leverages SQL Injections to Boost Search Rankings
A new type of black hat SEO campaign has been uncovered in the last few months by Akamai’s experts, who have observed...
-

 224Data Security
224Data SecuritySSH Backdoor Identified in Fortinet Firewalls
Fortinet’s FortiOS operating system, deployed on the company’s FortiGate firewall networking equipment includes an SSH backdoor on versions from the 4.x series...
-

 187Data Security
187Data SecurityNew Anonymous Communication Network PrivaTegrity Launched
PrivaTegrity communication network provides secure communication platform and Anonymity — Maybe better than Tor. A new anonymous communication network by the name of...
-

 310Geek
310GeekWhy Are We Calling Ubuntu 16.04 LTS The Best Ubuntu Release In Years?
Short Bytes: Making our readers aware about the best privacy practices by providing the latest security news has been fossBytes’ top priority....
-

 94Cyber Crime
94Cyber CrimeWhat does Fitbit hacking mean for wearables and IoT?
Wearable activity tracking devices like those made by Fitbit were one of the hottest gifts this past holiday season and it appears...
The Latest
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft




