Featured News
-
 210Data Security
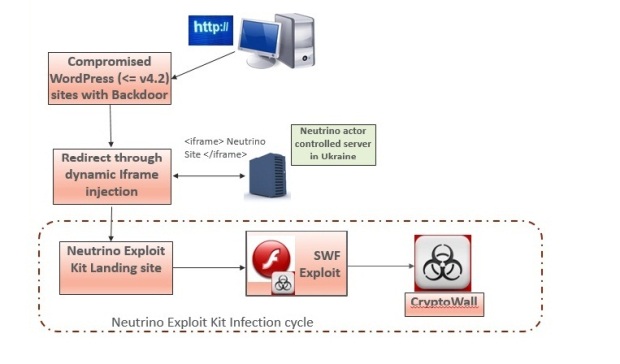
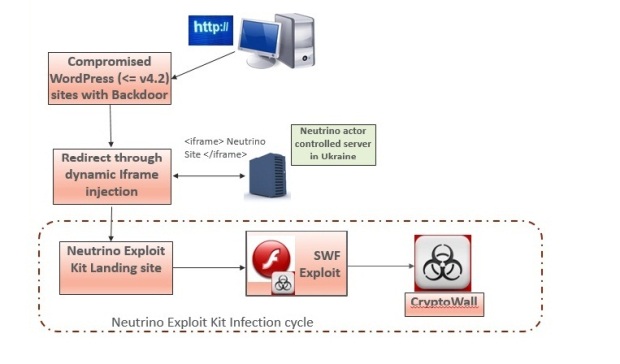
210Data SecurityExperts warn Neutrino and RIG exploit kit activity spike
Security experts at Heimdal Security are warning a spike in cyber attacks leveraging the popular Neutrino and RIG exploit kit. Cyber criminals...
-

 232Vulnerabilities
232VulnerabilitiesA Flaw on eBay’s Site Allowed Hackers To Steal User’s Passwords
A critical bug on eBay’s website opened the door for malicious hackers to create fake login pages to steal passwords and harvest...
-

 95Data Security
95Data SecurityTrochilus RAT Evades Antivirus Detection, Used for Cyber-Espionage in South-East Asia
A new type of RAT (Remote Access Trojan) has been discovered in use against governments and civil society organizations in South-East Asia,...
-

 197Data Security
197Data SecuritySay “Cyber” again—Ars cringes through CSI: Cyber
CBS endangered cyber-procedural: Plane hacking! Software defined radio! White noise! OMG!. There are lots of cringeworthy technology moments on television, especially when the...
-

 99Data Security
99Data SecuritySmartwatches Can Be Used to Spy on Your Card’s PIN Code
Wearable devices can be used as motion-based keyloggers. French student and software engineer, Tony Beltramelli, has published his master thesis called Deep-Spying: Spying...
-

 351Hacked
351Hacked26-year-old Hacker Sent To Jail For 334 Years, Highest Ever For A Cybercriminal
Short Bytes: A young Turkish hacker namedOnur Kopçak was sentenced to 334 years in prison. The cyber criminal was convicted for credit...
-

 275Opinion
275OpinionCES 2016: Day 3 – the drones are back (but with augmented reality)
The final instalment in Cameron Camp's security-focused coverage of CES 2016, looks at the future of drones. It's all about augmented reality.
-
 118Vulnerabilities
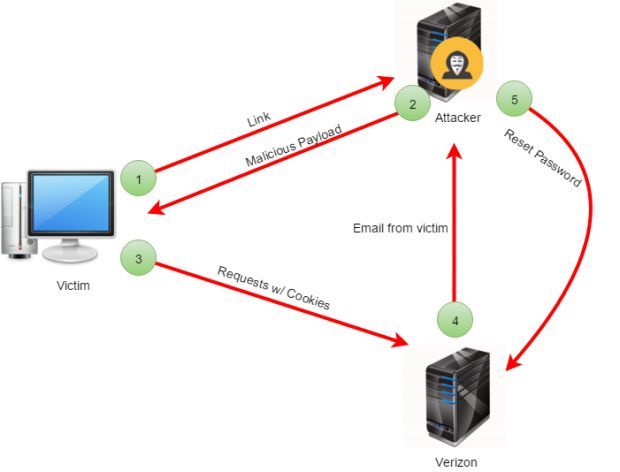
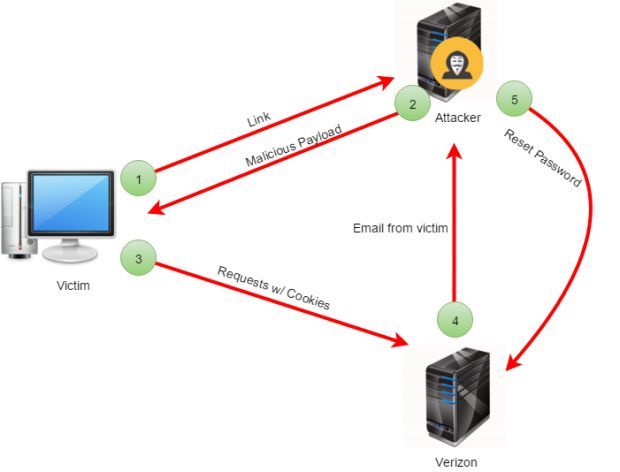
118VulnerabilitiesCSRF Bug in Verizon’s API Left My FiOS Accounts Open to Attacks
API used a simple authentication scheme, exposing users to CSRF attacks that allowed third-parties to hijack accounts. Verizon fixed an issue in...
-

 77Cyber Crime
77Cyber CrimeBlackEnergy and the Ukrainian power outage: What we really know
Robert Lipovsky, a senior malware researcher at ESET, offers his expert insight into the recent discovery of BlackEnergy malware in Ukrainian energy...
-

 166Incidents
166IncidentsThis Netflix Hack Reveals The Secret Movie Genres You’re Missing
Netflix Hack : Here Is How To Open Up Movie Portals You Didn’t Know Existed. You probably know that Netflix is a online...
-

 303Hacked
303HackedTop 10 Best Free Antivirus Software Of 2016 — Computer Virus Protection
Short Bytes: fossBytes brings you a list of 10 best free antivirus software of 2016 for different kinds of platforms such as best antivirus...
-

 235Data Security
235Data SecurityJuniper drops NSA-developed code following new backdoor revelations
Researchers contradict Juniper claim that Dual_EC_DRBG weakness couldn’t be exploited. Juniper Networks, which last month made the startling announcement its NetScreen line...
-

 210Incidents
210IncidentsDDoS attack on BBC may have reached 602Gbps, never so powerful
The hacking group New World Hacking that claimed the responsibility for the BBC attack revealed that the DDoS attack reached the 602...
-
 327Geek
327GeekHow PING Could Save and Prevent Deadly Accidents
Ian Trump of LOGICnow wonders whether the humble PING could be our savior This Government of Canada press release caught my eye...
-

 176Hacked
176HackedKingston’s ‘Unhackable’ DataTraveler USB Drive Self-destructs With Incorrect PIN Entry
Image | Kingston Short Bytes: Kingston Digital, one of the world leaders in memory products, has released DataTraveler 2000 encrypted USB Flash...
-

 336News
336NewsTech Giants in Battle Against UK Government Over Surveillance Program
Privacy protection or criminal activity prevention? UK Government faces battle against tech companies on a hot matter UK Government drafted a plan...
-
 251Geek
251GeekYour Location on Windows 10 Phone is Traceable, Here’s How to Disable it
Random Hardware Address Prevents Windows 10 Mobile Phone’s location from being tracked — Here’s how to do it Tracking users’ location through...
-

 148News
148NewsAnonymous Targets Nigerian Government Sites, Wages War Against Corruption
Appalled by Corruption, Theft & Poverty- Anonymous Declares Cyberwar against Nigerian Government Anonymous, the infamous hacktivist group having footprints around the world,...
-

 218Geek
218GeekGoogle Play Store, Receptacle Of Germs: Malware-Infected Apps Had To Be Removed
Brain Test malware is back. Its developers compromised 13 apps on the Google Play Store, Lookout cyber security firm discovered last December....
-

 315Vulnerabilities
315VulnerabilitiesUncooperative Russian ISP Prevents Cisco from Shutting Down Cybercriminal Gang
Russian ISP Eurobyte fails to answer Cisco’s emails, allows malvertising campaign to go on undisturbed. Cisco’s Talos research team has managed to identify...
The Latest
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Malware
MalwareChina-Linked Hackers Suspected in ArcaneDoor Cyberattacks Targeting Network Devices
-
 Malware
MalwareNew ‘Cuckoo’ Persistent macOS Spyware Targeting Intel and Arm Macs
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Malware
MalwareHackers Increasingly Abusing Microsoft Graph API for Stealthy Malware Communications
-
 Malware
MalwareNSA, FBI Alert on N. Korean Hackers Spoofing Emails from Trusted Sources
-
 Vulnerabilities
VulnerabilitiesFour Critical Vulnerabilities Expose HPE Aruba Devices to RCE Attacks
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Vulnerabilities
VulnerabilitiesWhen is One Vulnerability Scanner Not Enough?
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Vulnerabilities
VulnerabilitiesNew “Goldoon” Botnet Targets D-Link Routers With Decade-Old Flaw
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Malware
MalwareZLoader Malware Evolves with Anti-Analysis Trick from Zeus Banking Trojan
-
 Malware
MalwareEternal Malware: CVE-2024-3400 Rootkits Persist Through Palo Alto Firewalls Updates and Resets
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024




