Featured News
-

 237Vulnerabilities
237VulnerabilitiesIntel Skylake Processors Affected By Bug That Can Freeze PCs During Complex Work
Intel acknowledges that Skylake processors freeze in the middle of work. A bug has been found in the Intel processors that can freeze...
-
 213Data Security
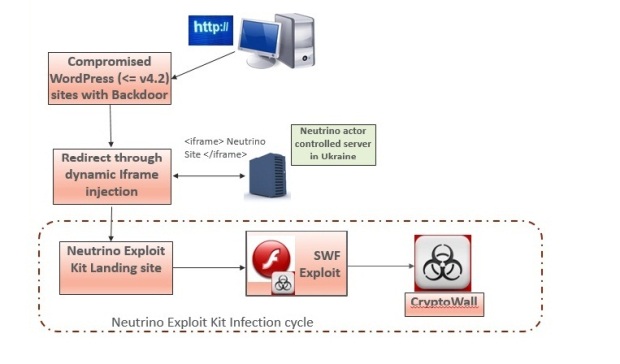
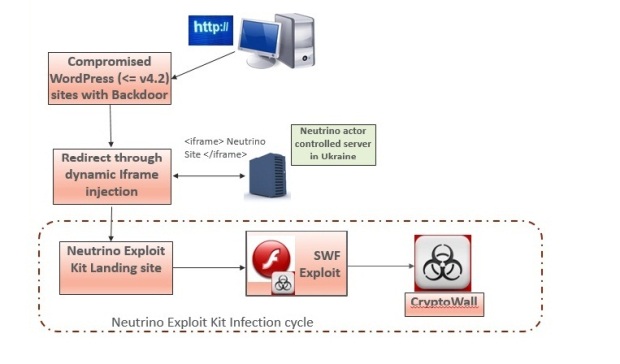
213Data SecurityExperts warn Neutrino and RIG exploit kit activity spike
Security experts at Heimdal Security are warning a spike in cyber attacks leveraging the popular Neutrino and RIG exploit kit. Cyber criminals...
-

 234Vulnerabilities
234VulnerabilitiesA Flaw on eBay’s Site Allowed Hackers To Steal User’s Passwords
A critical bug on eBay’s website opened the door for malicious hackers to create fake login pages to steal passwords and harvest...
-

 96Data Security
96Data SecurityTrochilus RAT Evades Antivirus Detection, Used for Cyber-Espionage in South-East Asia
A new type of RAT (Remote Access Trojan) has been discovered in use against governments and civil society organizations in South-East Asia,...
-

 198Data Security
198Data SecuritySay “Cyber” again—Ars cringes through CSI: Cyber
CBS endangered cyber-procedural: Plane hacking! Software defined radio! White noise! OMG!. There are lots of cringeworthy technology moments on television, especially when the...
-

 102Data Security
102Data SecuritySmartwatches Can Be Used to Spy on Your Card’s PIN Code
Wearable devices can be used as motion-based keyloggers. French student and software engineer, Tony Beltramelli, has published his master thesis called Deep-Spying: Spying...
-

 354Hacked
354Hacked26-year-old Hacker Sent To Jail For 334 Years, Highest Ever For A Cybercriminal
Short Bytes: A young Turkish hacker namedOnur Kopçak was sentenced to 334 years in prison. The cyber criminal was convicted for credit...
-

 278Opinion
278OpinionCES 2016: Day 3 – the drones are back (but with augmented reality)
The final instalment in Cameron Camp's security-focused coverage of CES 2016, looks at the future of drones. It's all about augmented reality.
-
 122Vulnerabilities
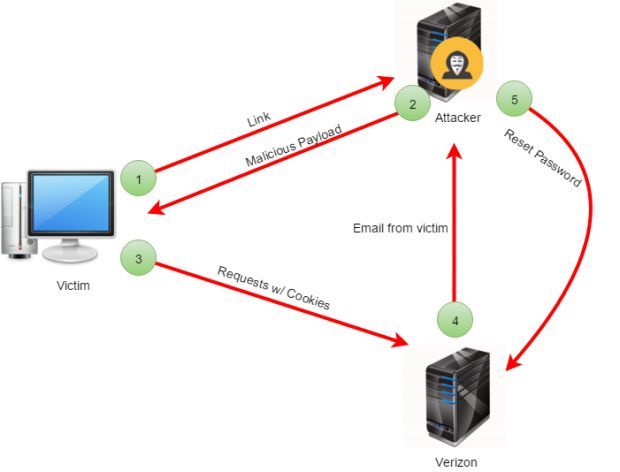
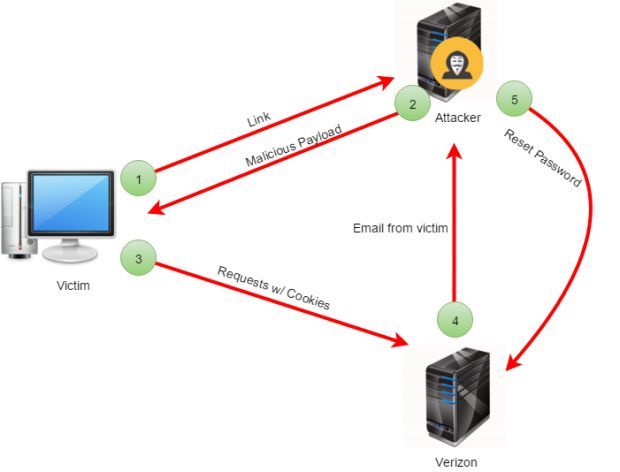
122VulnerabilitiesCSRF Bug in Verizon’s API Left My FiOS Accounts Open to Attacks
API used a simple authentication scheme, exposing users to CSRF attacks that allowed third-parties to hijack accounts. Verizon fixed an issue in...
-

 81Cyber Crime
81Cyber CrimeBlackEnergy and the Ukrainian power outage: What we really know
Robert Lipovsky, a senior malware researcher at ESET, offers his expert insight into the recent discovery of BlackEnergy malware in Ukrainian energy...
-

 168Incidents
168IncidentsThis Netflix Hack Reveals The Secret Movie Genres You’re Missing
Netflix Hack : Here Is How To Open Up Movie Portals You Didn’t Know Existed. You probably know that Netflix is a online...
-

 308Hacked
308HackedTop 10 Best Free Antivirus Software Of 2016 — Computer Virus Protection
Short Bytes: fossBytes brings you a list of 10 best free antivirus software of 2016 for different kinds of platforms such as best antivirus...
-

 237Data Security
237Data SecurityJuniper drops NSA-developed code following new backdoor revelations
Researchers contradict Juniper claim that Dual_EC_DRBG weakness couldn’t be exploited. Juniper Networks, which last month made the startling announcement its NetScreen line...
-

 213Incidents
213IncidentsDDoS attack on BBC may have reached 602Gbps, never so powerful
The hacking group New World Hacking that claimed the responsibility for the BBC attack revealed that the DDoS attack reached the 602...
-
 329Geek
329GeekHow PING Could Save and Prevent Deadly Accidents
Ian Trump of LOGICnow wonders whether the humble PING could be our savior This Government of Canada press release caught my eye...
-

 178Hacked
178HackedKingston’s ‘Unhackable’ DataTraveler USB Drive Self-destructs With Incorrect PIN Entry
Image | Kingston Short Bytes: Kingston Digital, one of the world leaders in memory products, has released DataTraveler 2000 encrypted USB Flash...
-

 337News
337NewsTech Giants in Battle Against UK Government Over Surveillance Program
Privacy protection or criminal activity prevention? UK Government faces battle against tech companies on a hot matter UK Government drafted a plan...
-
 253Geek
253GeekYour Location on Windows 10 Phone is Traceable, Here’s How to Disable it
Random Hardware Address Prevents Windows 10 Mobile Phone’s location from being tracked — Here’s how to do it Tracking users’ location through...
-

 155News
155NewsAnonymous Targets Nigerian Government Sites, Wages War Against Corruption
Appalled by Corruption, Theft & Poverty- Anonymous Declares Cyberwar against Nigerian Government Anonymous, the infamous hacktivist group having footprints around the world,...
-

 221Geek
221GeekGoogle Play Store, Receptacle Of Germs: Malware-Infected Apps Had To Be Removed
Brain Test malware is back. Its developers compromised 13 apps on the Google Play Store, Lookout cyber security firm discovered last December....
The Latest
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Cyber Attack
Cyber AttackMicrosoft Patches 61 Flaws, Including Two Actively Exploited Zero-Days
-
 Cyber Attack
Cyber AttackThe 2024 Browser Security Report Uncovers How Every Web Session Could be a Security Minefield
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Data Breach
Data BreachBlack Basta Ransomware Strikes 500+ Entities Across North America, Europe, and Australia
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Data Breach
Data BreachA SaaS Security Challenge: Getting Permissions All in One Place
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment




