Featured News
-

 318Vulnerabilities
318VulnerabilitiesUncooperative Russian ISP Prevents Cisco from Shutting Down Cybercriminal Gang
Russian ISP Eurobyte fails to answer Cisco’s emails, allows malvertising campaign to go on undisturbed. Cisco’s Talos research team has managed to identify...
-

 141Data Security
141Data SecurityExperts revealed that security camera vendors lack of security by design
When it comes to securing homes and businesses, a security camera is a privileged solution but it paradoxical is exposing users to...
-
 92Incidents
92IncidentsTime Warner Cable security breach may have exposed 320K customers
The TV cable and Internet service provider Time Warner Cable is warning customers their emails and passwords may have been exposed. Nearly 320,000...
-
 148Vulnerabilities
148VulnerabilitiesGM embraces white-hat hackers with public vulnerability disclosure program
First major automaker (aside from Tesla) to issue guidelines promising not to sue researchers. On January 5, General Motors quietly flipped the...
-

 89Data Security
89Data SecurityApple, Google, Microsoft attack government hacking plans
Tech industry hits back at plans to create legal framework for hacking by spies, military and police. Tech companies including Apple, Microsoft,...
-
 274Lists
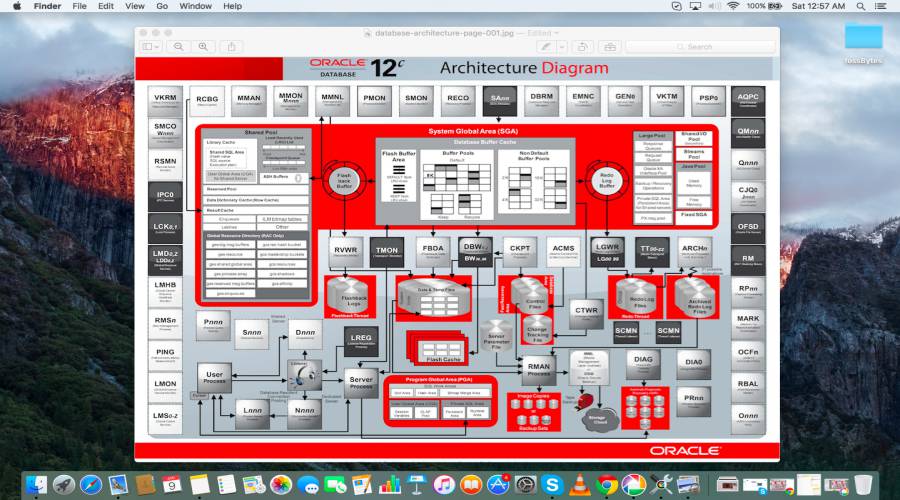
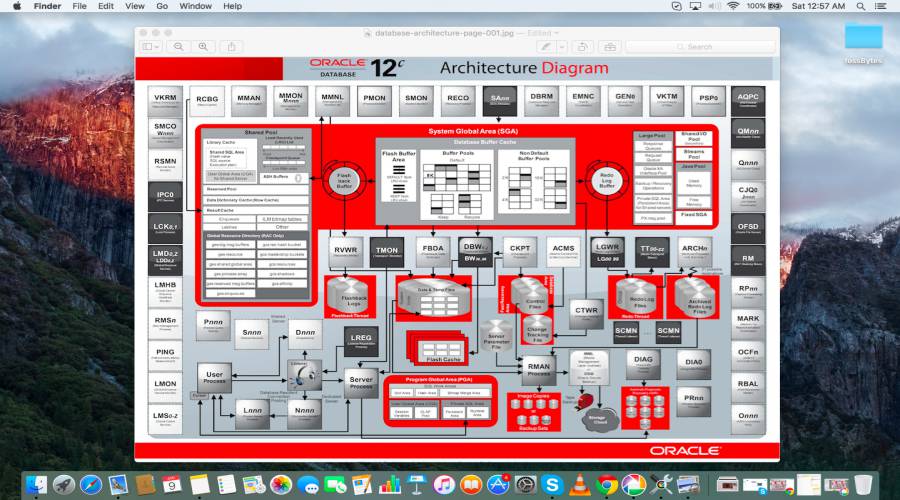
274ListsOracle Named The Best DBMS Of The Year, Followed By MangoDB And Cassandra
Short Bytes: DB-Engines is one of the most respected sources of database rankings. Over the past years, the website has listed the...
-

 334Geek
334GeekPentagon To Give Official Honors To Military Hackers and Drone Pilots
Pentagon has agreed that it will be extending official military honours to remote military personnel like military hackers or drone pilots after...
-

 284Opinion
284OpinionCES 2016: Day 2 – making smarter cars
Car security is rising to the fore here at CES 2016, which is not altogether surprising as 2015 was the year when...
-
 181Cyber Events
181Cyber EventsHacked: 320,000 Time Warner Accounts’ Info Compromised
User data of over 320,000 accounts with Time Warner Cable were stolen when a hack led to details like email ids and...
-

 102Data Security
102Data SecurityProPublica Launches the Dark Web’s First Major News Site
THE SO-CALLED DARK web, for all its notoriety as a haven for criminals and drug dealers, is slowly starting to look more...
-

 173Incidents
173IncidentsATM malware: Gang behind Euro attacks targeted in police swoops
Romanian police have acted to end a series of malware ATM attacks carried out in Germany, France, Norway, Sweden, Poland, and Romania....
-

 339Cyber Crime
339Cyber CrimeChinese Bank Customers Targeted with SMS Phishing Campaign
You have heard about phishing but now you will learn about Smishing. Hackers use phishing messages and compromised websites to steal credentials of...
-
 331Incidents
331IncidentsFBI Hacked 1000+ Dark Web Computers To Shut Down Largest Child-pornography Site
Short Bytes: Last year, the FBI engaged in the largest ever law enforcement hacking campaign to shut down “the largest remaining known...
-

 205Tricks & How To's
205Tricks & How To'sUnlock Netflix’s hidden categories with these secret codes
Here’s a trick that’s been around for a while but may have passed you by: secret category codes added by Netflix engineers...
-

 83Data Security
83Data SecurityAuthors digitally signed Spymel Trojan to evade detection
Zscaler ThreatLabZ detected a new infostealer malware family dubbed Spymel that uses stolen certificates to evade detection. In late December, security experts...
-

 274Incidents
274IncidentsGhost Squad Hackers Hack Ethiopian Websites In Response To Killing Of Protesting Students
Short Bytes: Ghost Squad Hackers group has taken down multiple .gov websites in Ethiopia. The collective has blamed the government for killing...
-

 180News
180NewsISIS Terrorists Kill Female Journalist, Hack Facebook Account
The terrorists first murdered the female journalist Ruqia Hassan and then hacked her Facebook account to spy on her contacts. The terrorist from...
-

 255Data Security
255Data SecurityAnti-NSA Blackphone Not So Secure After all
A security flaw in Blackphone 1 smartphone allowed anyone to take control of the device Blackphone 1 smartphones, one of many privacy-focused...
-
 236Lists
236Lists11 Top Technology Predictions For 2016 | fossBytes
Short Bytes: Technologies like IOT, 3D printing, VR camera and Tesla skimmed through entire 2015. But which technology in 2016 is going...
-

 338News
338NewsFBI Hacked Tor To Hunt Down Paedophiles On The Deep Web
FBI has taken down a site involved in Child pornography through some hacking techniques that have never been used in the history...
The Latest
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Cyber Attack
Cyber AttackMicrosoft Patches 61 Flaws, Including Two Actively Exploited Zero-Days
-
 Cyber Attack
Cyber AttackThe 2024 Browser Security Report Uncovers How Every Web Session Could be a Security Minefield
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Data Breach
Data BreachBlack Basta Ransomware Strikes 500+ Entities Across North America, Europe, and Australia
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Data Breach
Data BreachA SaaS Security Challenge: Getting Permissions All in One Place
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment




