Featured News
-

 159Privacy
159PrivacyMicrosoft issues warning after Xbox Live certificate ‘inadvertently’ leaks
A malicious attacker could in theory use the leaked security certificate to launch a man-in-the-middle attack, intercepting Xbox Live usernames, passwords and...
-

 429Geek
429GeekProject Uses 3D Printing For Visually Impaired “See” Artwork For The First Time
Imagine hearing about the mysterious smile of the Mona Lisa, the surrounding Klimt kiss or Van Gogh’s famous Sunflowers without ever getting...
-

 222How To
222How ToSick of hearing about Donald Trump ? Here’s how you can block him from the web
Many people are sick of hearing about Donald Trump. Trump Trump – Block Trump content an iPhone app that blocks all mentions...
-

 278Cyber Events
278Cyber EventsAnonymous Crushes Japan Prime Minister Website Against Whale Hunt
Earlier this year we reported Anonymous is targeting Japanese airport websites against dolphin slaughter in the country — The cyber attacks were...
-

 177Hacked
177HackedNorth Korea Has Hydrogen Bomb, Claims Kim Jong-Un
Short Bytes: North Korean leader Kim Jong-Un claimed that they’ve been successful in developing a Hydrogen Bomb while he visited a military...
-

 285Cyber Events
285Cyber EventsTrump, Clinton Would Like To Burn Freedom of Speech on Internet
The U.S. presidential candidates who were once supporters of the freedom of speech seem to have completely changed their ideas. Looking at...
-

 166Hacked
166HackedIndia-based FreeCharge Files Patent For One-Time Password Alternative
Short Bytes: In a step to replace the One-Time Password verification method in online payments, FreeCharge has developed a new verification method...
-

 236How To
236How ToHow to Enable Full Disk Encryption in Windows 10 in Simple Steps
Even though Windows 10 doesn’t offer any integrated solution for data encryption, here are the steps on how to enable full disk...
-

 93Incidents
93IncidentsUS embassy worker hacked for sex images
Ford committed the crimes while working at the US embassy in London A former US official has admitted stalking women and extorting...
-

 174Incidents
174IncidentsWebhost Easily hit by malware attack
UK webhosting company Easily has emailed its customers to inform them that it has fallen victim to a malware attack. COO Edwina...
-

 353Scams
353ScamsTech support scams: 3 steps to conning unsuspecting victims
Tech support scams are “still big business”, ESET’s David Harley has previously said. In this guide we look at how fraudsters dupe...
-
 433Lists
433ListsAirbnb Beats Google To Become The Best Tech Company To Work For In 2016
Short Bytes: Leaving behind the tech giants like Google, Facebook, LinkedIn etc., short-term rental startup Airbnb has made it to the top...
-

 154Data Security
154Data SecurityFBI head: terror fight requires open backdoors to encrypted user data
FBI director James Comey called on tech companies to create backdoor access to their users’ data on Wednesday, arguing it was necessary...
-

 174Vulnerabilities
174VulnerabilitiesKaspersky, McAfee, and AVG all vulnerable to major flaw
Researchers watch the watchmen. Some of the biggest names in the security software business have been compromised by a serious flaw that...
-
 131Incidents
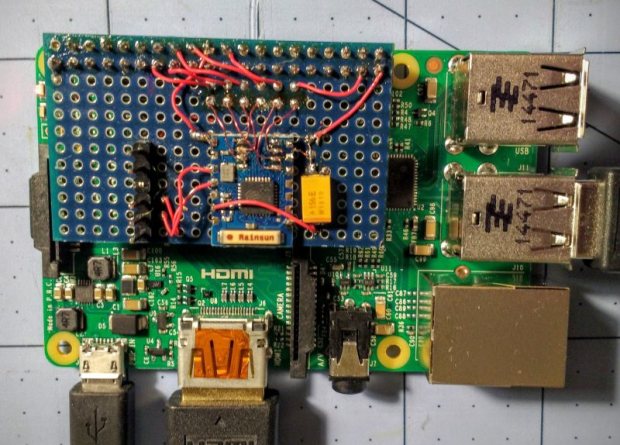
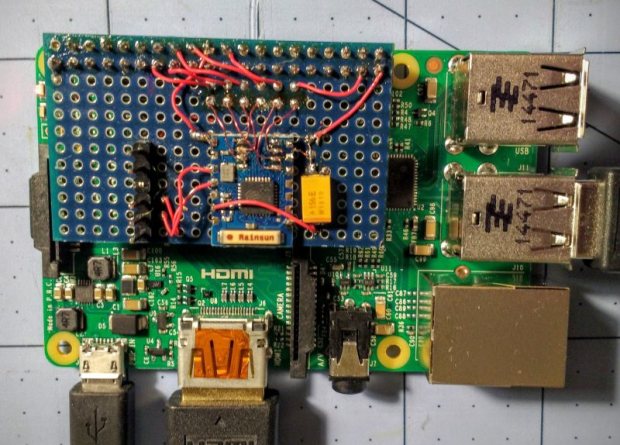
131IncidentsRASPBERRY PI $2 WIFI THROUGH EPIC SDIO HACK
These are the times that we live in: the Raspberry Pi Zero comes out — a full freaking Linux computer on a...
-

 167Data Security
167Data SecurityHacker Lexicon: Malvertising, the Hack That Infects Computers Without a Click
MALVERTISING IS WHEN hackers buy ad space on a legitimate website, and, as the name suggests, upload malicious advertisements designed to hack...
-

 142Cyber Crime
142Cyber CrimeMassive DDoS Attack Leaves UK Universities Without Internet
Some unknown cyber criminals have attacked a publicly funded network “Janet” which was used by many universities throughout the United Kingdom. On...
-

 320Geek
320GeekChrome App for Android To Alert Users on Visiting Malicious Sites
With an aim to secure the browsing, users surfing the Internet via chrome browser on mobile devices will receive a warning in...
-

 157Data Security
157Data SecurityResearchers Found Windows’ Malware Similar To The One Used by NSA
NSA’s one of the known snooping tactics is installing a malware into hard drive’s firmware which makes the deletion of the malware...
-

 107Incidents
107IncidentsDNS Root Servers Hit by DDoS Attack
nternet core infrastructure hit in rare cyber-attack.Unknown parties carried out a large-scale DDoS attack on the Internet’s DNS root servers, causing slight...
The Latest
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft




