Featured News
-

 288Cyber Events
288Cyber EventsTrump, Clinton Would Like To Burn Freedom of Speech on Internet
The U.S. presidential candidates who were once supporters of the freedom of speech seem to have completely changed their ideas. Looking at...
-

 169Hacked
169HackedIndia-based FreeCharge Files Patent For One-Time Password Alternative
Short Bytes: In a step to replace the One-Time Password verification method in online payments, FreeCharge has developed a new verification method...
-

 239How To
239How ToHow to Enable Full Disk Encryption in Windows 10 in Simple Steps
Even though Windows 10 doesn’t offer any integrated solution for data encryption, here are the steps on how to enable full disk...
-

 95Incidents
95IncidentsUS embassy worker hacked for sex images
Ford committed the crimes while working at the US embassy in London A former US official has admitted stalking women and extorting...
-

 176Incidents
176IncidentsWebhost Easily hit by malware attack
UK webhosting company Easily has emailed its customers to inform them that it has fallen victim to a malware attack. COO Edwina...
-

 357Scams
357ScamsTech support scams: 3 steps to conning unsuspecting victims
Tech support scams are “still big business”, ESET’s David Harley has previously said. In this guide we look at how fraudsters dupe...
-
 438Lists
438ListsAirbnb Beats Google To Become The Best Tech Company To Work For In 2016
Short Bytes: Leaving behind the tech giants like Google, Facebook, LinkedIn etc., short-term rental startup Airbnb has made it to the top...
-

 156Data Security
156Data SecurityFBI head: terror fight requires open backdoors to encrypted user data
FBI director James Comey called on tech companies to create backdoor access to their users’ data on Wednesday, arguing it was necessary...
-

 177Vulnerabilities
177VulnerabilitiesKaspersky, McAfee, and AVG all vulnerable to major flaw
Researchers watch the watchmen. Some of the biggest names in the security software business have been compromised by a serious flaw that...
-
 134Incidents
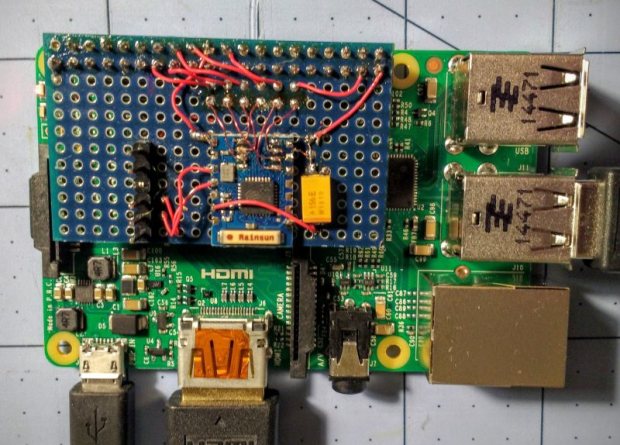
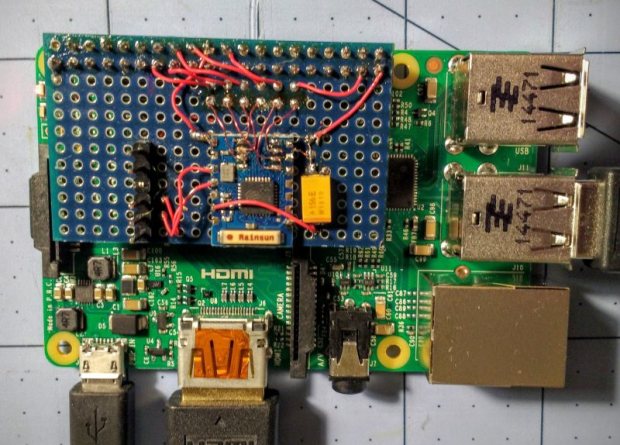
134IncidentsRASPBERRY PI $2 WIFI THROUGH EPIC SDIO HACK
These are the times that we live in: the Raspberry Pi Zero comes out — a full freaking Linux computer on a...
-

 171Data Security
171Data SecurityHacker Lexicon: Malvertising, the Hack That Infects Computers Without a Click
MALVERTISING IS WHEN hackers buy ad space on a legitimate website, and, as the name suggests, upload malicious advertisements designed to hack...
-

 146Cyber Crime
146Cyber CrimeMassive DDoS Attack Leaves UK Universities Without Internet
Some unknown cyber criminals have attacked a publicly funded network “Janet” which was used by many universities throughout the United Kingdom. On...
-

 323Geek
323GeekChrome App for Android To Alert Users on Visiting Malicious Sites
With an aim to secure the browsing, users surfing the Internet via chrome browser on mobile devices will receive a warning in...
-

 160Data Security
160Data SecurityResearchers Found Windows’ Malware Similar To The One Used by NSA
NSA’s one of the known snooping tactics is installing a malware into hard drive’s firmware which makes the deletion of the malware...
-

 111Incidents
111IncidentsDNS Root Servers Hit by DDoS Attack
nternet core infrastructure hit in rare cyber-attack.Unknown parties carried out a large-scale DDoS attack on the Internet’s DNS root servers, causing slight...
-

 206News
206NewsScammers Hack Cricket South Africa Facebook Page with Adult Content
Cricket South Africa page got hacked earlier today where hackers posted racist and sexual content on the page which surprised many of...
-

 256Data Security
256Data SecurityBitcoin’s Creator Satoshi Nakamoto Is Probably This Unknown Australian Genius
EVEN AS HIS face towered 10 feet above the crowd at the Bitcoin Investor’s Conference in Las Vegas, Craig Steven Wright was,...
-

 169Hacked
169HackedKudos! Microsoft Does It Once Again
Short Bytes: Microsoft, long known for harbouring different kinds of malware, this time, “unveils” bootkit, a malware which loads even before the Windows...
-
 179Malware
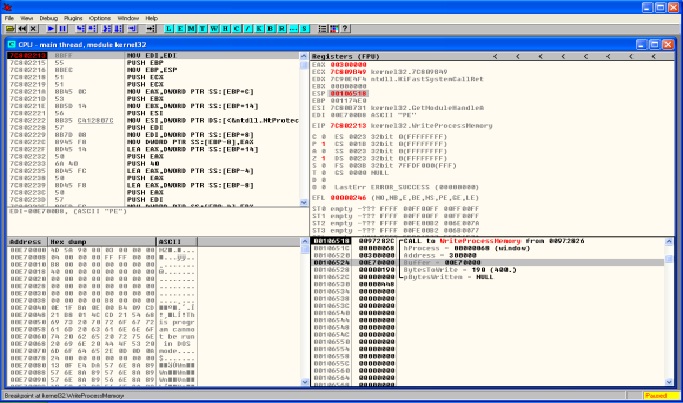
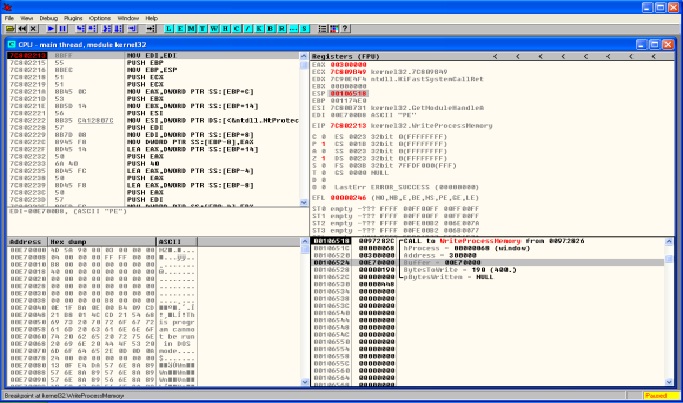
179MalwareMALWARE ANALYSIS – DRIDEX & PROCESS HOLLOWING
Lately the threat actors behind Dridex malware have been very active. Across all the recent Dridex phishing campaigns the technique is the same....
-

 162Vulnerabilities
162VulnerabilitiesApple Patches 50 Vulnerabilities Across iOS, OS X, Safari
Apple has piled on the patches already released by Adobe and Microsoft today, and pushed out updates for iOS, OS X, Apple...
The Latest
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment
-
 Data Security
Data SecurityHow Safe is Your TinyProxy? Step-by-Step Guide to Exploiting Tinyproxy’s Zero Day Vulnerability
-
 Malware
MalwareChina-Linked Hackers Suspected in ArcaneDoor Cyberattacks Targeting Network Devices
-
 Malware
MalwareNew ‘Cuckoo’ Persistent macOS Spyware Targeting Intel and Arm Macs
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Malware
MalwareHackers Increasingly Abusing Microsoft Graph API for Stealthy Malware Communications




