Featured News
-
 91Data Security
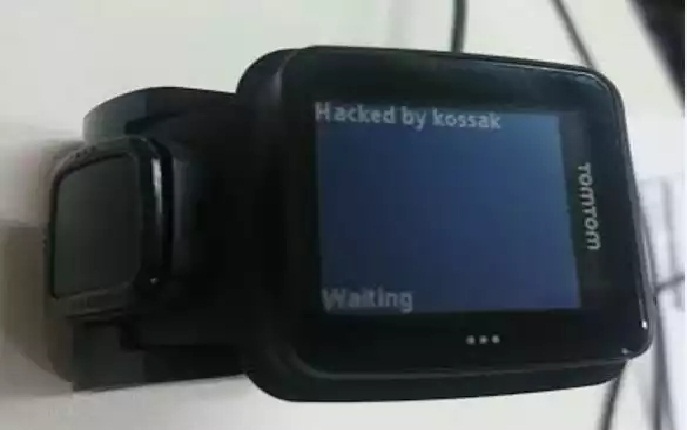
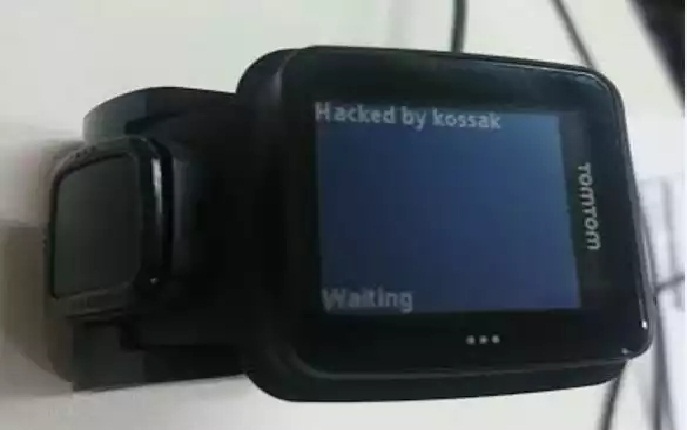
91Data SecurityHacking Smartwatches – the TomTom Runner
I intended originally for this series to contain only three posts, and in order to achieve that, this post is longer than...
-

 241Data Security
241Data SecurityEmbedded Devices Share, Reuse Private SSH Keys, HTTPs Certificates
Researchers have found that thousands of Internet gateways, routers, modems and other embedded devices share cryptographic keys and certificates, exposing millions of...
-

 197News
197NewsAnonymous Hacks UN Climate Change Site Against Police Attack on Cop21 March
The hacktivist group Anonymous breached into the website of United Nations Framework Convention on Climate Change (UNFCCC) and leaked a trove of...
-
 302How To
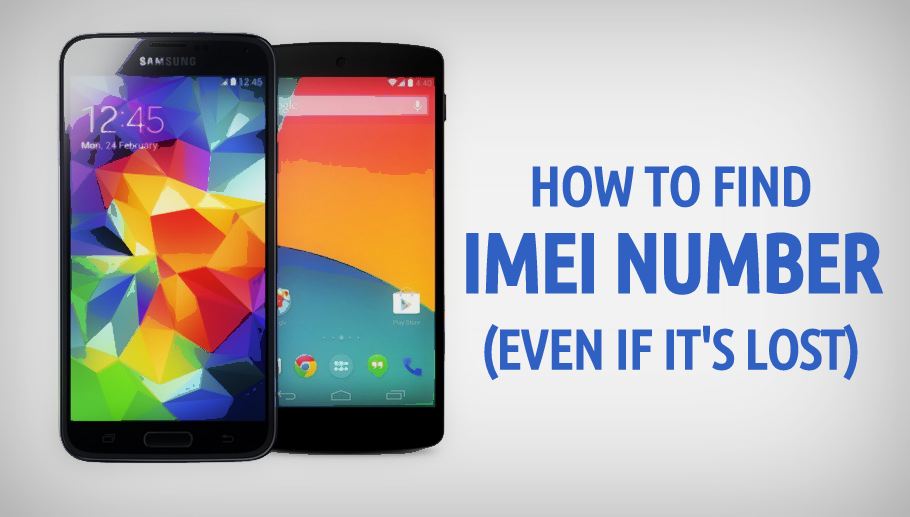
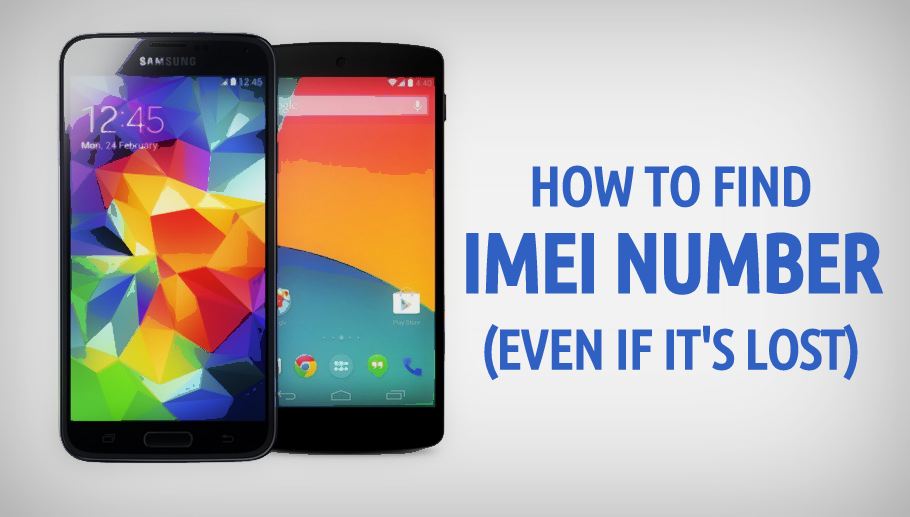
302How ToHow To Find IMEI Number Of Your Phone (Even If It’s Lost)
Short Bytes: The IMEI, or International Mobile Station Equipment Identity, is a unique number which is associated with your phone. The IMEI...
-
 319News
319NewsHackers Steal Parents, Kids Data in a Massive Data Breach on Toy Manufacture
A Chinese company VTech, dealing in electronic toys has faced a massive data breach in which 4.8 million parents and children details...
-

 137Vulnerabilities
137VulnerabilitiesMultiple serious vulnerabilities in RSI Videofied’s alarm protocol
RSI Videofied are a French company that produce a series of alarm panels that are fairly unique in the market. They are...
-

 343Banking
343BankingDifferent nations’ online banking habits: better safe than sorry?
When it comes to online banking, the UK and the US leads the way with security – over 70% of Brits and...
-

 134Hacked
134HackedMedical Devices Ransomware Is The Biggest Hacking Threat of 2016
Short Bytes: As we are making progress on the front of online security, the cybercriminals are competing head-to-head to target every device connected...
-

 534Banking
534BankingOnline banking on‑the‑move? For most it’s a no‑go
What environment do you consider the safest for online banking? Would you make your financial transactions solely in the safety of your...
-

 111Incidents
111IncidentsOn China’s fringes, cyber spies raise their game
By Clare Baldwin, James Pomfret and Jeremy Wagstaff HONG KONG/SINGAPORE (Reuters) – Almost a year after students ended pro-democracy street protests in...
-

 108Incidents
108IncidentsAnonymous Takes Down Five Government Websites in Iceland to Protest Whale Hunting
Group also goes after the website of a whale hunting company Online activists associated with Anonymous took down five websites belonging to...
-
 112Incidents
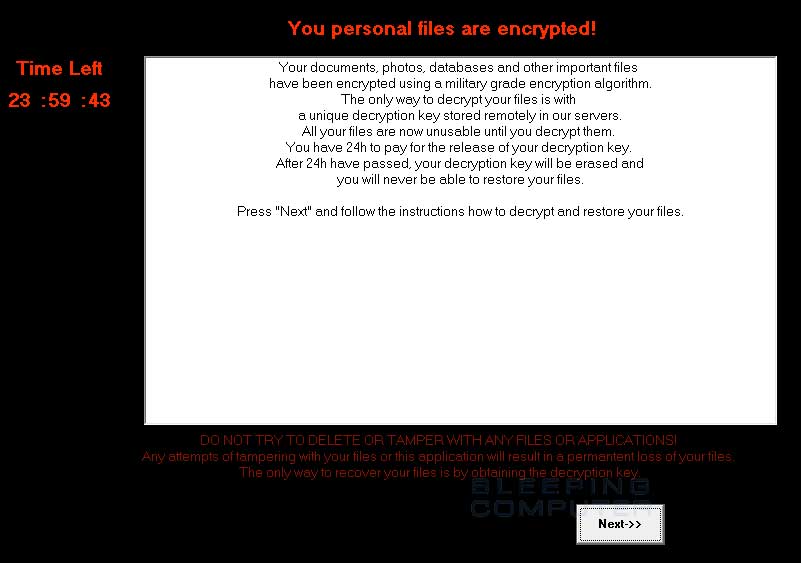
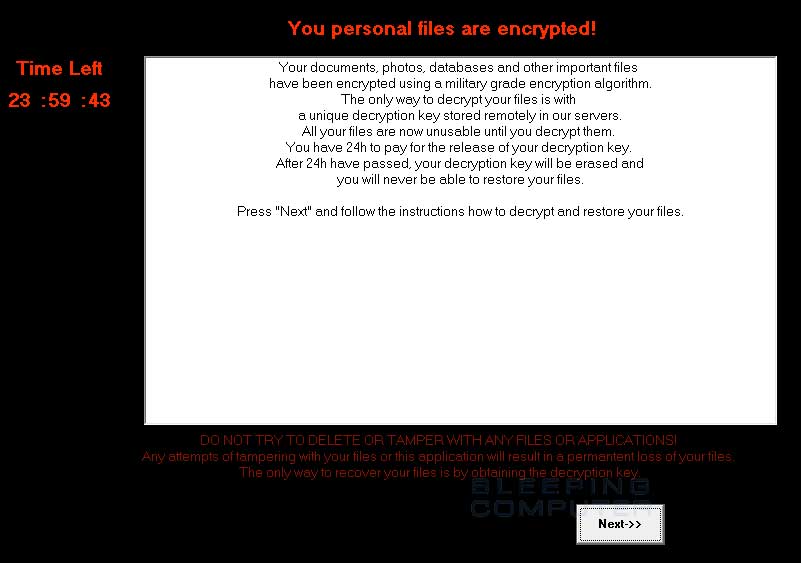
112IncidentsDecryptorMax Ransomware Decrypted, No Need to Pay the Ransom
Emsisoft researchers creates decryption tool.Fabian Wosar of Emisoft has created a tool capable of decoding files encrypted by the DecryptorMax ransomware, also...
-

 173Hacked
173HackedOne of the Only Publicly Known Anonymous Hacker Tells How Anonymous Fights ISIS
Short Bytes: Only very few members of the hacktivist collective Anonymous have been publicly identified. One such person is Gregg Housh, who recently...
-

 271News
271NewsAnonymous Crushes Almost Every Iceland Govt Site Against Whale Slaughter
Anonymous kicked started the operation #OpWhales and shut down almost all the Iceland government websites for about 13 hours as a protest against...
-

 271Hacked
271HackedThe “Secret ISIS Cybersecurity Guide” Was Just A Simple Security Guide In Arabic
Short Bytes: After the unfortunate Paris attacks, online media outlets like Wired, Yahoo News, and The Telegraph uncovered a ‘secret ISIS OPSEC...
-

 357Cyber Crime
357Cyber CrimeCouple Arrested For Providing Malware Encryption Service To Cyber Criminals
A couple (22-year-old man and a 22-year-old woman from Colchester, Essex) offering malware encryption services has been arrested by British police — The...
-

 195Data Security
195Data SecurityCritical Vulnerability in VPN Exposes User’s Real IP Address to Attacker
Researchers have found a vulnerability in VPN networks that could allow hackers or scammers to access real IPs of the users. Though,...
-

 219How To
219How ToHow To Capture Your Screen In Mac OS X In Simple Steps
Short Bytes: Mac OS X has a very nice way to capture full or partial screen without any software, but many users are...
-

 214Data Security
214Data SecurityRussians embrace Bitcoins, the West sticks with PayPal
One day, as you’re busy surfing on one of your favorite online stores, you stumble upon a pair of chic shades …...
-

 186Hacked
186HackedNSA Is Finally Ending Its Bulk Phone Syping Program From Tomorrow
Short Bytes: The NSA will end its bulk phone spying program by 11:59 p.m. EST Saturday (4:59 a.m. GMT Sunday). This step is...
The Latest
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Malware
MalwareEternal Malware: CVE-2024-3400 Rootkits Persist Through Palo Alto Firewalls Updates and Resets
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Data Breach
Data BreachNavigating the Threat Landscape: Understanding Exposure Management, Pentesting, Red Teaming and RBVM
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage




