Featured News
-
 126Malware
126MalwareDyreza Banking Trojan Adds Support for Microsoft Edge and Windows 10
Hide your Windows 10 & Edge browser, Dyreza is coming!. A new variant of the Dyreza banking trojan comes with support for Microsoft’s...
-

 361How To
361How ToHow To Save Google Maps for Offline Use
Google Maps are no doubt very helpful to most of the people. We can navigate through places and streets easily using Google...
-
 313Geek
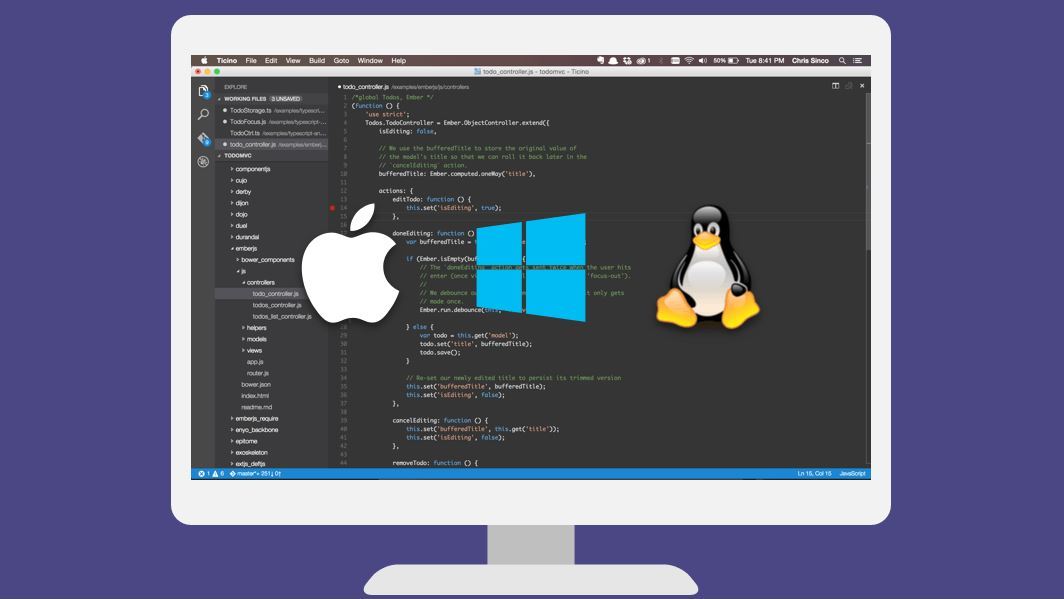
313GeekMicrosoft Open Sources Visual Studio Code, Supports Linux App Debugging
Short Bytes: Microsoft has made tons of announcements and launches at its Connect(); Developers Conference 2015. The company has open sourced its Visual Studio...
-
 337Hacking Tutorials
337Hacking TutorialsHow to Hack ISIS
Encouraging the people to join the cyber-war against ISIS, hacktivist group Anonymous has published three hacking guides. These guides have instructions regarding...
-

 134Opinion
134OpinionBirds of a feather code together
Lysa Myers, a security researcher at ESET, looks at the diversity challenges and opportunities in information security - while there is much...
-

 298News
298NewsCloudFlare CEO Denies Anonymous’ allegation of protecting ISIS sites
In a reaction to Paris Attacks last Friday, Anonymous declared a war against the ISIS on Monday and were determined to knock...
-

 182Data Security
182Data SecuritySeized: Fake EFF .org linked to hackers hitting NATO, White House PCs
Digital rights group takes down Pawn Storm base. The (EFF) has been awarded control of its namesake domain, which was being used...
-

 182Incidents
182IncidentsFBI’s website is the easiest to hack says hacker who hacked FBI and Home Office from his bedroom
Reformed hacker says that US government websites especially FBI and Home Office are easiest to hack. You would be surprised to know...
-

 284Lists
284Lists5 Most Useless Yet Awesome Inventions Ever
Short Bytes: Ever came across a creative invention and questioned its use? Well, you are at the right place as we have...
-
 107Data Security
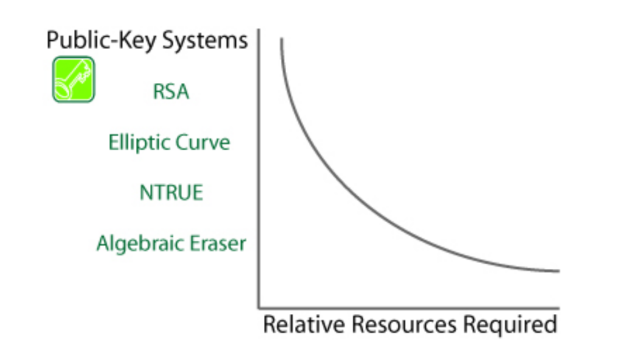
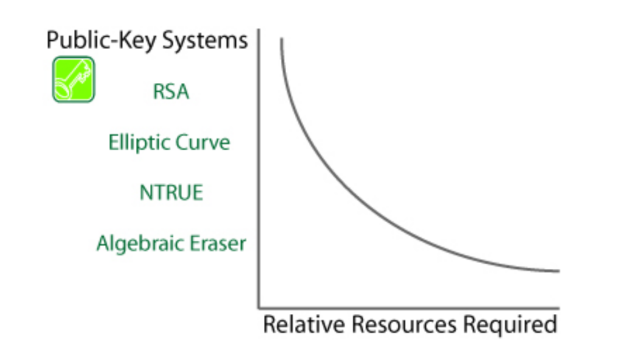
107Data SecurityWhy Algebraic Eraser may be the riskiest cryptosystem you’ve never heard of
A potential standard for securing network-connected pacemakers, automobiles, and other lightweight devices has suffered a potentially game-over setback after researchers developed a...
-
 292Hacked
292HackedAnonymous Publishes Three Guides To Teach You “How To Hack” And Fight ISIS
Short Bytes: Encouraging the people to join the cyber-war against ISIS, hacktivist group Anonymous has published three hacking guides. These guides have...
-

 74Cyber Crime
74Cyber CrimeFighting talk from Great Britain as it says it will hit back against internet attacks
British chancellor George Osborne has warned about the spectre of online terrorists attacking national infrastructure, and made some rather bold pronouncements about...
-

 314News
314NewsFrench Blogger Accuses Anonymous of Impeding Police in Fight Against ISIS
Anonymous has declared full-time war against ISIS and warned the terrorist group to expect the worse. In a recent video, they left...
-
 288Geek
288GeekGmail to Alert Users Upon Receiving Unencrypted Messages
Google has decided to tighten up those loose strings that hinder their efforts to offer comprehensive protection to its users against internet...
-
 271Hacked
271HackedISIS Calls Anonymous Hackers “Idiots” For Declaring War
Short Bytes: ISIS has responded to Anonymous’ declaration of war and threat of hunting them down from all over the world. The...
-

 288Hacked
288HackedWhy Is Edward Snowden Being Blamed For Paris Attacks
Short Bytes: The security agencies have accused the NSA whistle blower Edward Snowden for the terrorist happenings in the city of Paris....
-

 330Cyber Events
330Cyber EventsResearcher Claims Dark Web is the next safe haven for the ISIS
Al-Hayat, an agency that spreads all the content relevant to ISIS on different online platforms has announced the ISIS intentions on moving...
-

 218News
218NewsAnonymous Expose and Shutdown 8824 Pro-ISIS Twitter Accounts
The online hacktivist group Anonymous has declared a “total war” against the terrorist group and so-called Islamic State (IS, previously ISIS/ISIL) group. To keep up...
-

 319Data Security
319Data SecurityISIS May Have Used Sony PS4 to Plan Paris Attacks
French authorities after the Paris attacks are busy trying to find the source using which the whole massacre was planned. Last Friday,...
-
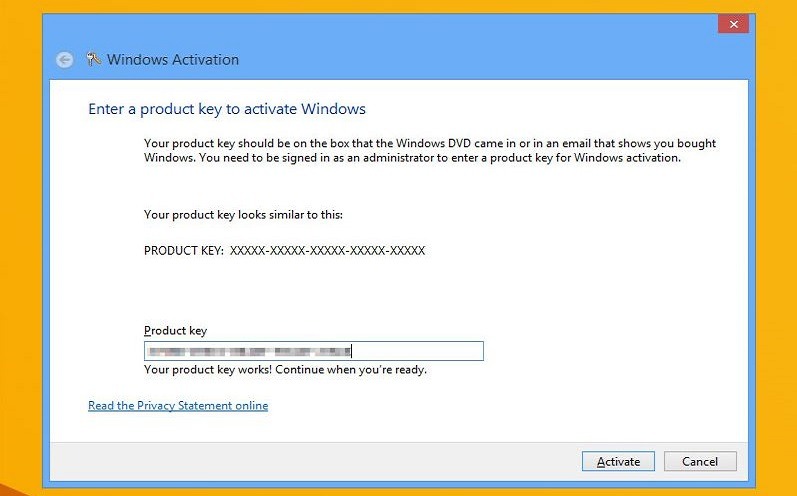
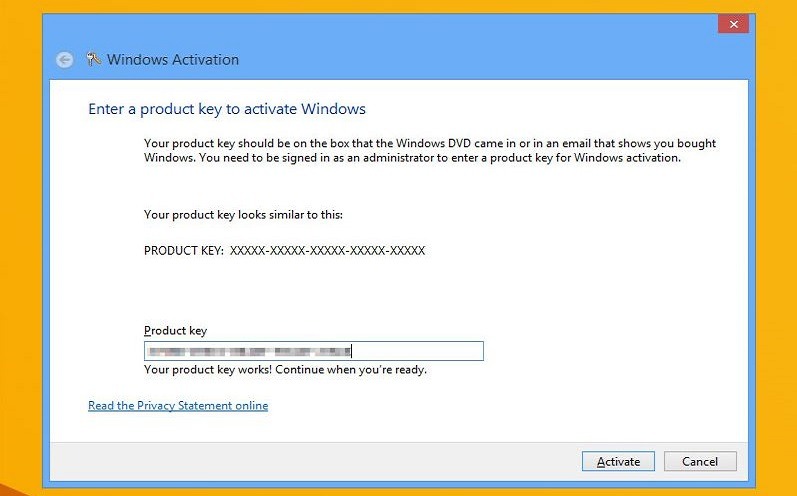 261How To
261How ToHow To Activate Windows 10 Using Windows 7 or 8.1 Product Key
Short Bytes: Microsoft has finally responded to the user feedback in the form of recognizing Windows 7 and 8.1 product keys to...
The Latest
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft




