Featured News
-

 176Data Security
176Data SecurityTablets with Pre-installed Trojan Being Sold on Amazon
Recently, researchers from the Cheetah Mobile Security Lab have found a dangerous Trojan, dubbed Cloudsota, pre-installed on certain Android tablets. Tablets infected...
-

 102Incidents
102IncidentsOfficial Premier League Fantasy Website infected with malware
Soccer, or rather football aficionados in the UK may have had their computers infected whilst browsing the Premier League’s official fantasy website...
-
 287Incidents
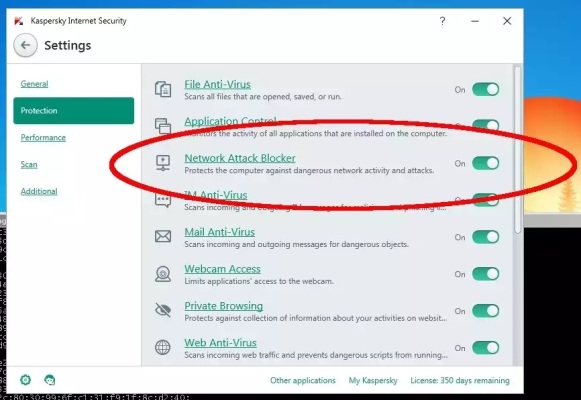
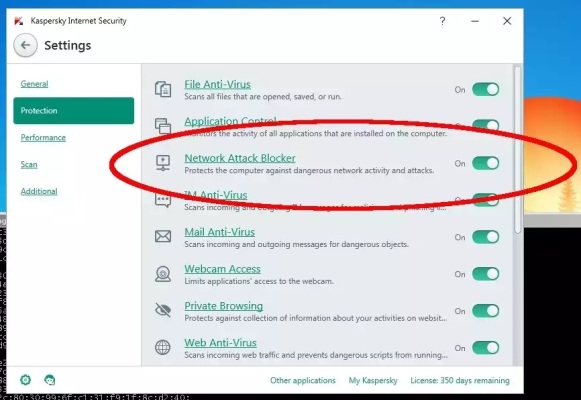
287IncidentsHackers Exploit Kaspersky, Microsoft Security Products to Install Snooping Trojan
Recently, while researching attacks on targets in Thailand, Unit 42 discovered a tool that initially appeared to be a variant of the...
-

 76Data Security
76Data SecuritySAP Security Patch for November 2015 Released
This post by SAP Product Security Response Team shares information on Patch Day Security Notes* that are released on second Tuesday of...
-

 107Incidents
107IncidentsRansomware infected the UK Parliament’s computer networks
A ransomware infected several PC at the UK Parliament, for the first time a threat hit the internal computer network, the Parliamentary...
-

 268Cyber Events
268Cyber EventsAnonymous Exposes Identity of Alleged Halifax Rapist, Police Reopens The Case
Halifax police forced to re-open investigation in a sexual assault case after Anonymous exposes the identity of the alleged culprit. The online...
-

 250Geek
250GeekHuman biology merges with technology as Biohackers implant LED’s under the skin
Biohackers have unveiled something that could be termed as “Technology for future”. The technology is a silicone implant that is LED equipped...
-

 235Tricks & How To's
235Tricks & How To's8 Firefox Add-ons used by Hackers
Ethical hacking could be great fun if you know about these add-ons. The creation of penetration testing labs in Kali Linux or...
-

 94Data Security
94Data SecurityFacebook told by Belgian court to stop tracking non-users
A court has given Facebook 48 hours to stop tracking people in Belgium who are not members of its social network. Facebook...
-
 223Malware
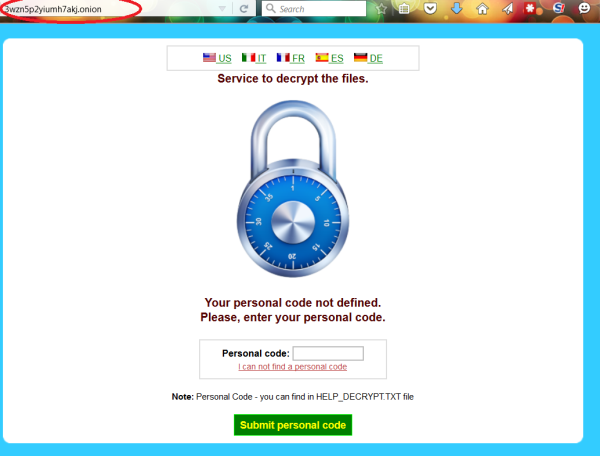
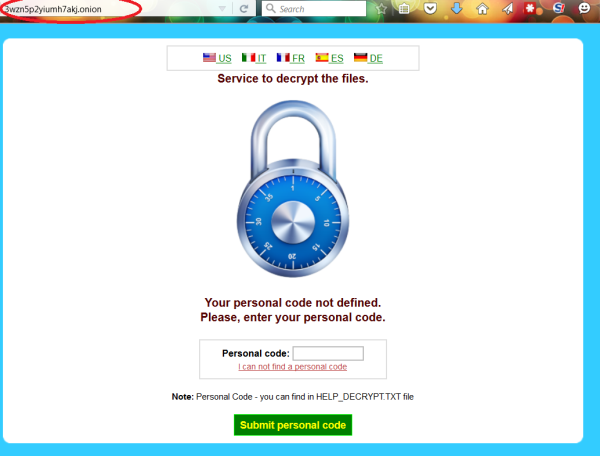
223MalwareCryptoWall 4.0 released with new Features such as Encrypted File Names
CryptoWall 4.0 has been released that displays a redesigned ransom note, new filenames, and now encrypts a file’s name along with its data. We...
-

 102Data Security
102Data SecurityFlaw in Linux.Encoder1 ransomware reveals the decryption key
Experts at Bitdefender have discovered a flaw in Linux Encryption Ransomware Linux.Encoder1 that exposes the decryption Key used to lock the files....
-

 166Data Security
166Data SecurityBadly coded ransomware locks away data forever
Coding mistakes in a malicious program that encrypts data mean anyone hit by the Power Worm virus will not be able to...
-

 89Data Security
89Data SecurityUS banks attacked, manipulated and left (heart)bleeding
In April 2014 the cybersecurity world was rocked by the discovery of Heartbleed, the name given to a vulnerability found in one...
-

 322Geek
322GeekCourt Orders Facebook to Stop Tacking Non-Users or Pay €250K Fine Daily
A Belgian court has ordered Facebook to stop tracking internet users within next 48 hours or they will impose fines of up...
-

 115Cyber Crime
115Cyber CrimeResearchers Expose Iranian Phishing Servers Targeting Opposition
A group of researchers from Checkpoint Security firm claimed that they have breached phishing servers that were used by the Rocket Kitten....
-

 268Cyber Crime
268Cyber CrimeHackers Infect British Parliament Computers with Ransomware
Cyber cooks breached the security of British parliament’s secure network and hacked into many of its computer systems. The hack allowed the...
-

 260Kids Online
260Kids Online5 things you can monitor with your parental control tool
One of the biggest concerns parents have about the internet is the sites their children are browsing. Parental control tools can help...
-

 97Cyber Crime
97Cyber CrimeSocial media savvy students ‘better at avoiding cybercrime’
A new study finds that current university students have a mature approach to social media that helps keep them safe from cybercrime.
-

 172Incidents
172IncidentsComcast resets nearly 200,000 passwords after customer list goes on sale
Over the weekend, a reader (@flanvel) directed Salted Hashto a post on a Dark Web marketplace selling a number of questionable, if...
-

 159Hacked
159HackedThis 9-Year-Old Boy Is An Accomplished Hacker And CEO Of A Company
Short Bytes: Reuben Paul is a cybersecurity expert who lives in Austin, Texas, and attends third grade. He is the CEO of...
The Latest
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft




