Featured News
-

 162Malware
162MalwareThe Vawtrak Trojan reemerges tougher and sneakier
The Vawtrak bug back and meaner than ever, say Proofpoint researchers. A once-dormant banking trojan has reared its ugly head once again,...
-

 291Banking
291BankingUK’s NCA warns online bankers to be wary of Dridex malware
The virulent Dridex malware poses a serious threat to online bankers in the UK, according to the National Crime Agency. Internet users...
-
 171Data Security
171Data SecurityResearcher messes up Wi-Fi with an rPi and bargain buy radio stick
Putrid Piper picked apart a packet for just $15. KU Leuven Phd student Mathy Vanhoef has smashed conventional wireless security thought by...
-

 218Incidents
218IncidentsJackpot: New hacking group steals 150,000 credit cards from casino
Flat, firewall-free network was a walk in the park, boffins say. Cyber Defence Summit An un-named Casino with next-to-no security has lost...
-

 160Vulnerabilities
160VulnerabilitiesNew zero-day exploit hits fully patched Adobe Flash
Attacks used to hijack end users’ computers when they visit booby-trapped sites. Attackers are exploiting a previously unknown vulnerability in fully patched...
-

 207Cyber Events
207Cyber EventsAnonymous Targets Belgian Government, Knocks Prime Minister’s Website Off
The online hacktivist group Anonymous Belgian conducted a series of DDoS attacks on the official website of Belgian Prime Minister Charles Michel,...
-
 111Hacked
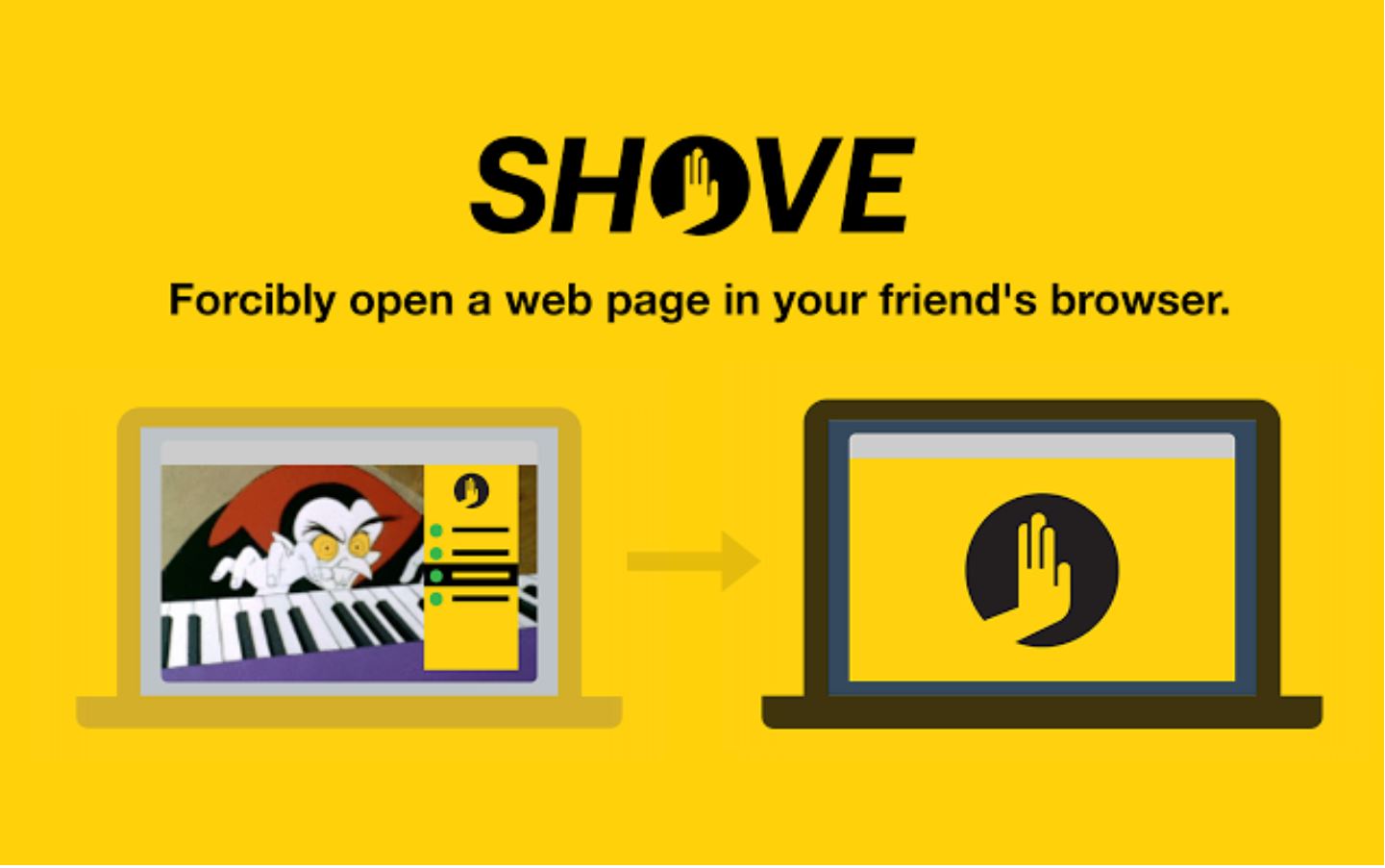
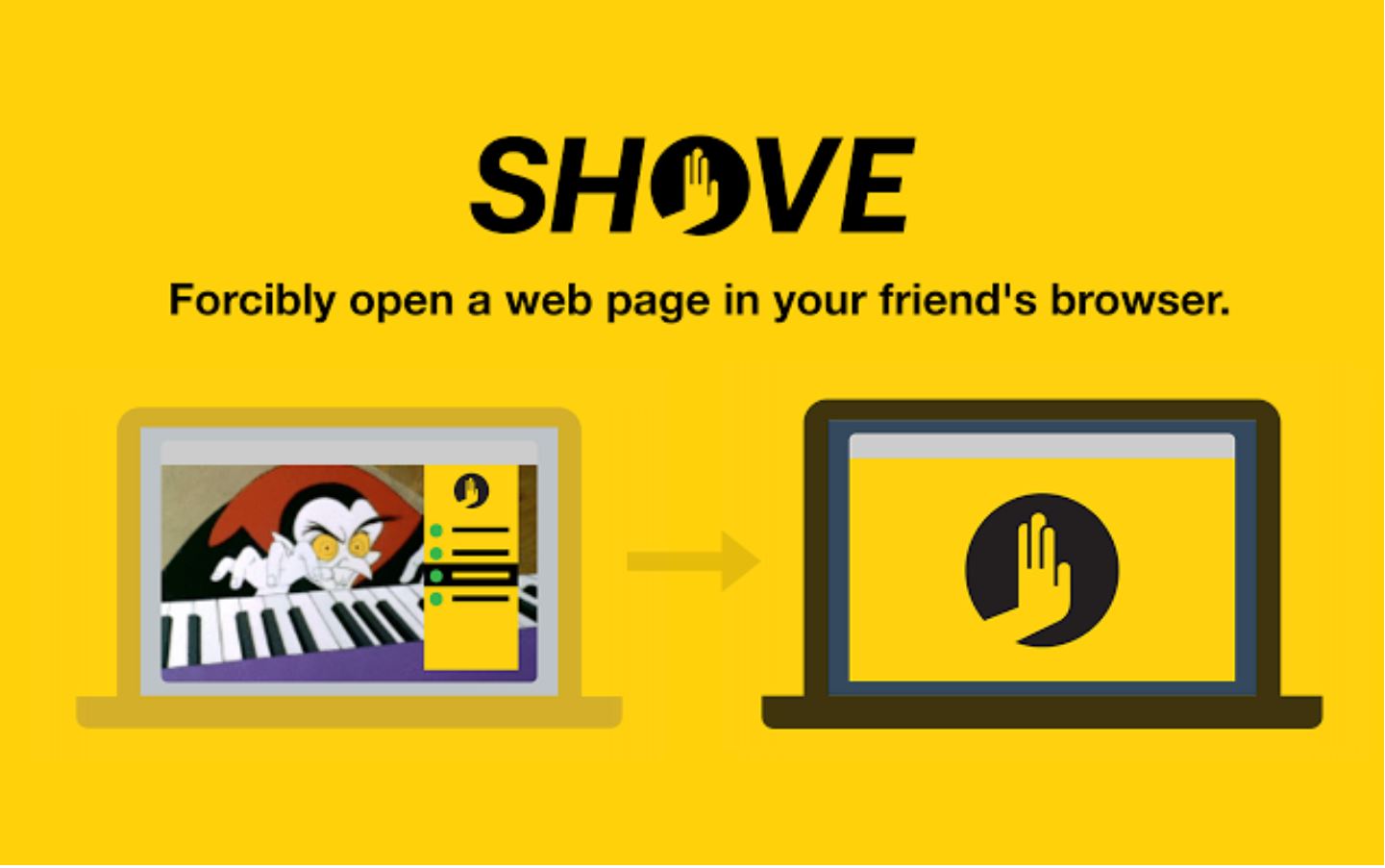
111HackedHow to Hijack Your Friend’s Browser With This Simple Chrome Extension
Short Bytes: Shove extension for Chrome is made with a good intention of sharing the links with your friends instantly. But, you...
-

 358Data Security
358Data SecurityWatch Out – This Killer USB Drive Will Fry Your Laptop
Do you know the USB devices we carry each day can be converted into a bomb? You must be thinking like “yeah whatever.”...
-

 98Malware
98MalwareBeware banking trojans and their nasty helpers
Banking trojans are ubiquitous and growing in number and sophistication, largely through trojan downloaders and webinjects. Here are four severe cases.
-

 257Data Security
257Data SecurityUSB Killer Version 2.0 is Here to Burn and Destroy Your Computer
The maker of USB Killer is here with the USB Killer version 2.0 – a more advanced version of the computer frying...
-

 181Hacked
181HackedUSB Killer Version 2.0 Burns and Destroys Your Computer
Short Bytes: The maker of USB Killer is here with the USB Killer version 2.0 – a more advanced version of the...
-

 302How To
302How ToHow to Find Your Lost or Stolen Laptop?
Having your laptop stolen is the biggest nightmare anyone can face in the era of our gadget-centric lives. Here are some ways...
-
 248Hacked
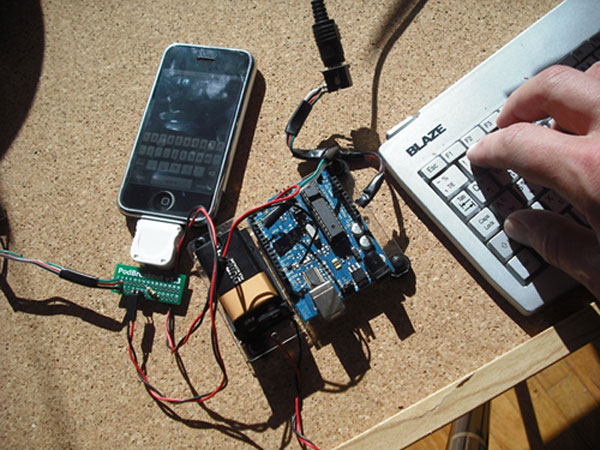
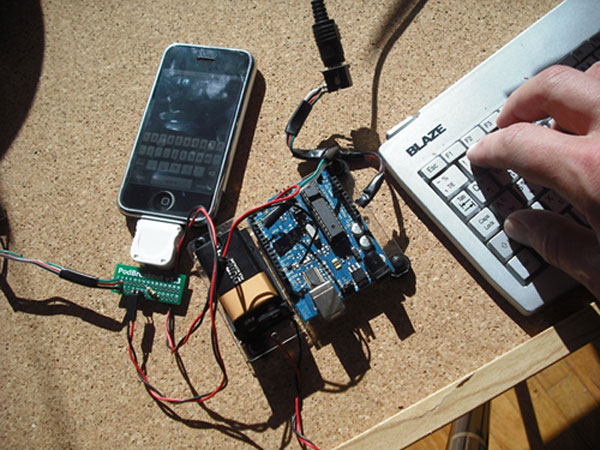
248HackedCrypto Backdoor Isn’t The Only Way To Hack Into Your iPhone
Short Bytes: Crypto backdoor entry isn’t the only way for the cops to access your data. You think your iPhone is the...
-

 82Data Security
82Data SecurityHackers can steal your BRAIN WAVES
Depressingly familiar and stupid mistakes in EEG kit, health org’s storage of recorded brains. BruCon: Behold the future: attackers can already get...
-

 93Malware
93MalwareMalware attack targets America’s Thrift Stores
America’s Thrift Stores said this week that it has been the victim of a malware-driven cyberattack by Eastern European criminals who stole...
-

 172Data Security
172Data SecurityCops Don’t Need a Crypto Backdoor to Get Into Your iPhone
The privacy community scored a victory in a year-long battle over the future of encryption: In internal discussions, the White House quietly...
-

 297News
297NewsSomeone Hacked Uniformed Services University and Leaked Their Credentials Online
A hacker going with the online handle of Kuroi SH hacked and defaced several domains of the United States based Uniformed Services...
-

 370Cyber Events
370Cyber EventsGreat Firewall of China at Work, Apple News May Have Been Blocked
Apple news (Currently in testing mode) has been taken down in China by the company itself. The reason behind this seems obvious:...
-
 306Hacked
306Hacked10 Steps To Defeat Hacking Attacks (And What To Do After You’ve Been Hacked)
Short Bytes: In the third article of the “Steps to Effective Security” series, I’ll tell you 10 steps to defeat hacking attacks and...
-

 277Data Security
277Data SecurityHackers Can Steal Corporate Passwords Through Cisco’s WebVPN Service Backdoor
Researchers identified a flaw in Cisco’s WebVPN — Hackers managed to install backdoors via two methods on the service — This weakness...
The Latest
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft




