Featured News
-

 318Malware
318MalwareYiSpectre, the First iOS Malware That Attacks Non-Jailbroken Devices
The malware spreads with the help of an adult movie player. Security researchers at Palo Alto Networks have discovered and analyzed malware that...
-

 87Data Security
87Data SecurityVW’s ‘neat hack’ exposes danger of corporate software
It was only old-fashioned detective work that forced Volkswagen to admit to the existence of its ‘defeat device’. And that should worry...
-

 317Data Security
317Data SecurityHow to do hacking attacks over satellite communications?
Hack Satellite comunication In this article we will cover satellite based hacking attack which has been used by hacking groups since...
-

 386Data Security
386Data SecurityHOW TO INTERCEPT SATELLITE COMMUNICATIONS EASILY?
In today world we use satellite communication in many respects and industries and we all know how important they are in our...
-
 323How To
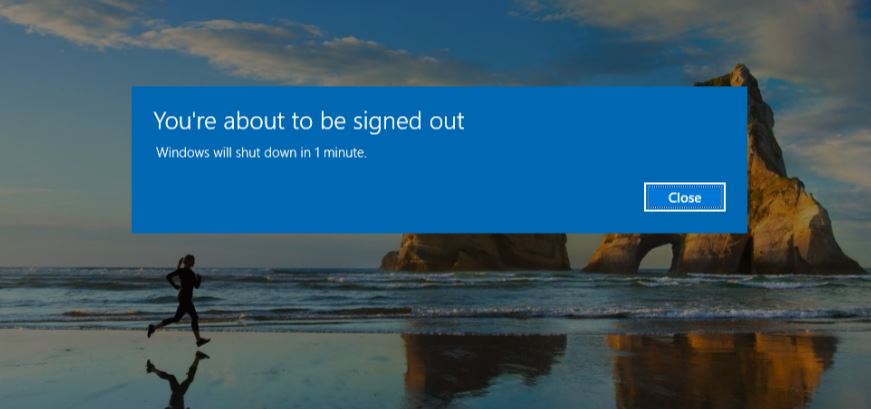
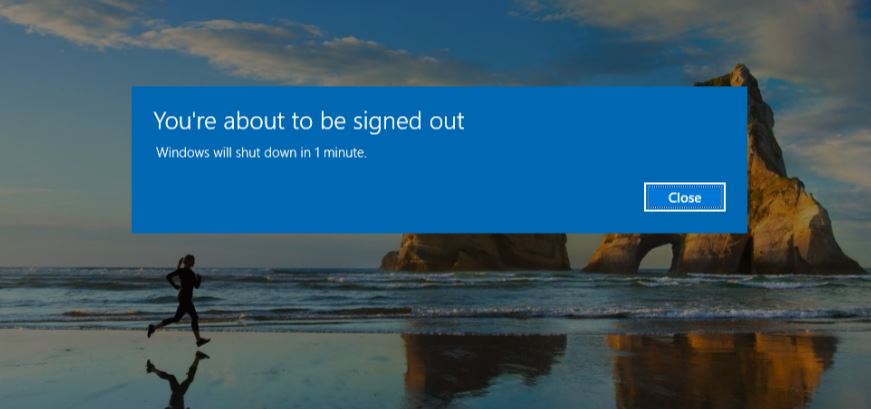
323How ToHow To Schedule A Shutdown For Windows OS?
Short Bytes: This article describes the steps to schedule a Shutdown command for Windows OS. Take a look. The very first task...
-
 97How To
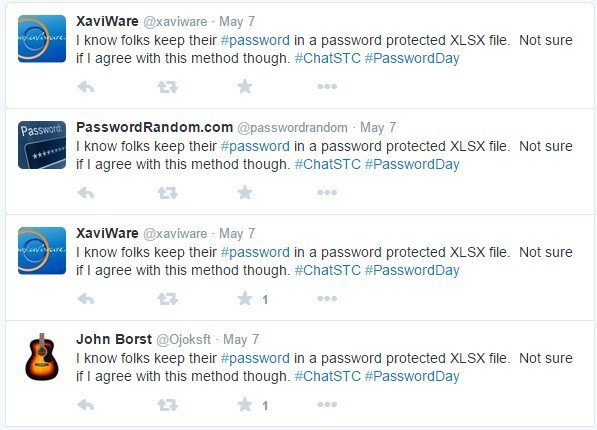
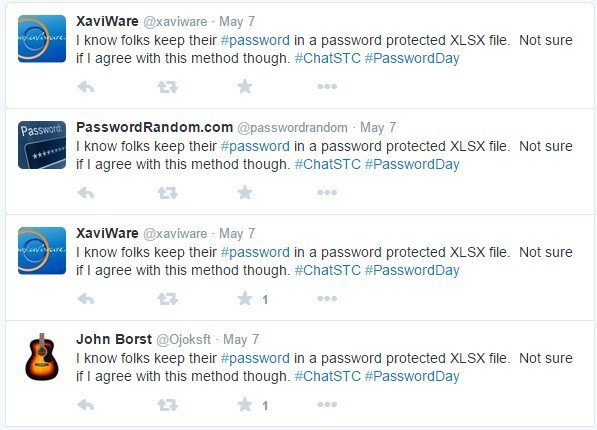
97How ToHow To Find The People Stealing Your Tweets On Twitter
This small piece of python code will find the people stealing your tweets and copy-pasting them on their twitter timeline. This python...
-
 266Geek
266GeekMS Word Vulnerability Exploited in Operation Pony Express to Spread Malware
Operation Pony Express was a spear-phishing campaign that was detected by Sophos researchers between April and May 2015. The research team identified...
-

 298Hacked
298HackedFirst Step to Effective Security – How to Know if You’ve Been Hacked
Short Bytes: Was your data compromised in the latest data breaches? How to know if you’ve been hacked? Here are the answers. The...
-
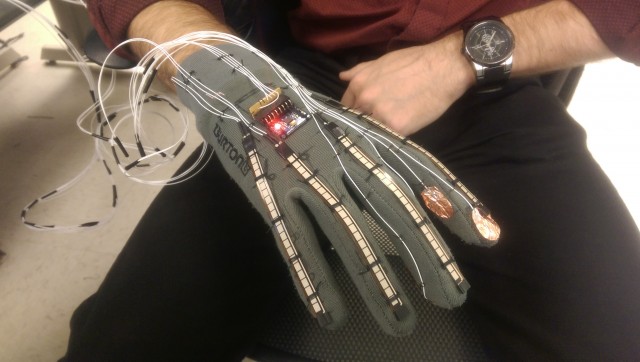
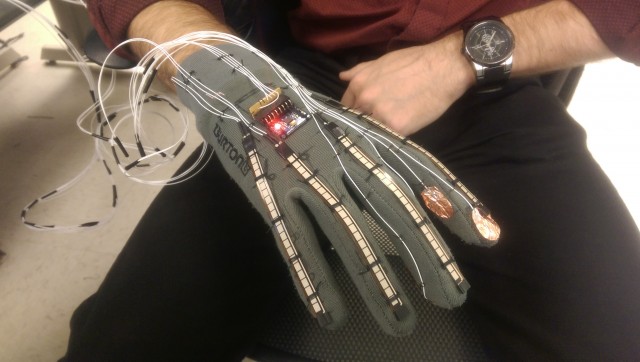 290Geek
290GeekFuturistic Smart-Glove Can Translate Sign Language Into Text and Speech
Scientists are constantly working on user-friendly products for those with physical disabilities. In the past, these wearable glasses came out to help...
-

 118Geek
118GeekStagefright 2.0: Security Flaw in Android Puts 1 Billion Devices at Risk
The risk of remote hacking is triggered through the faults in the media processing components that may be misused by malicious websites....
-
 298Geek
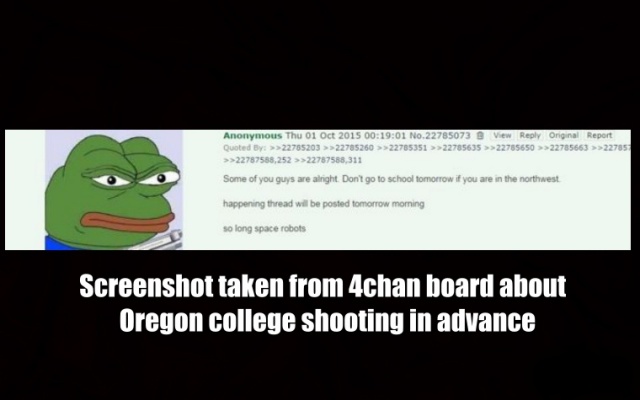
298GeekWas Oregon Shooting Predicted on 4chan?
Someone used 4chan to post about Oregon college shooting in the US before it actually took place. The sudden increase of Internet users...
-
 482Geek
482GeekWhat is Free and Open Source Software (FOSS) and Why You Should Use it?
Short Bytes: FOSS (Free And Open Software) is the modern day result of the free software movement that draws its philosophies from...
-

 111Malware
111MalwareDangerous resurgent banking malware hits UK
Bank trojan twin pivots to smash supply chain biz. The formidable Dyreza and Dridex banking malware are back in renewed and rejigged...
-

 131Malware
131MalwareAndroid Malware Disguises as PayPal App
A recent spam campaign is leading users to a fake PayPal app which steals their real credentials, but also comes hard-coded to...
-

 322Cyber Crime
322Cyber CrimeFBI Caught Paedophile By Infecting Tor Web Browser
Do you think that using anonymity software like Tor will protect your online presence from spies? A new spyware has been developed...
-

 167Incidents
167IncidentsPatreon was warned of serious website flaw 5 days before it was hacked
Even worse: Thousands of other sites are making the same facepalm-worthy mistake. Five days before Patreon.com officials said their donations website was...
-

 114Vulnerabilities
114VulnerabilitiesSamsung Decides Not to Patch Kernel Vulnerabilities in Some S4 Smartphones
Two kernel vulnerabilities were left unpatched on older devices running Android Jelly Bean and KitKat. QuarksLAB, a security research company based in Paris,...
-

 195Vulnerabilities
195VulnerabilitiesWordPress Jetpack Plugin Patched Against Stored XSS Vulnerability
After a few critical bugs were recently discovered and patched in the core WordPress engine—a rarity with WordPress-related security issues—order has apparently...
-
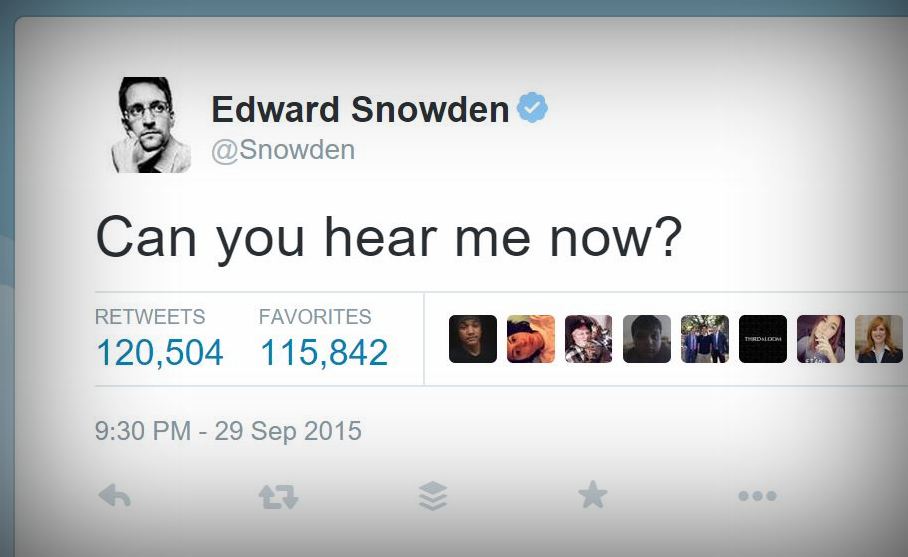
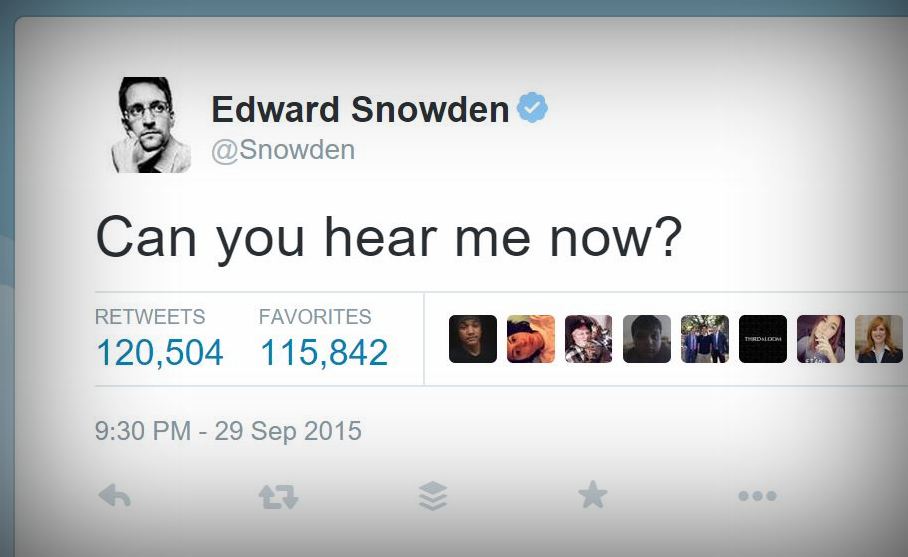 203Hacked
203HackedEdward Snowden Gets Bombarded With 47GB of Twitter Notifications
Short Bytes: Former NSA contractor and a newbie to Twitter, Edward Snowden, forgot to turn off the email notifications on Twitter and...
-

 316Data Security
316Data SecurityHackers Can Exploit Security Flaws In Drones To Hijack Flight Controller
Security flaws have been found in drones that could allow hackers to target and attack the flight controller which includes numerous sensors...
The Latest
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Malware
MalwareChina-Linked Hackers Suspected in ArcaneDoor Cyberattacks Targeting Network Devices
-
 Malware
MalwareNew ‘Cuckoo’ Persistent macOS Spyware Targeting Intel and Arm Macs
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Malware
MalwareHackers Increasingly Abusing Microsoft Graph API for Stealthy Malware Communications
-
 Malware
MalwareNSA, FBI Alert on N. Korean Hackers Spoofing Emails from Trusted Sources
-
 Vulnerabilities
VulnerabilitiesFour Critical Vulnerabilities Expose HPE Aruba Devices to RCE Attacks
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Vulnerabilities
VulnerabilitiesWhen is One Vulnerability Scanner Not Enough?
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Vulnerabilities
VulnerabilitiesNew “Goldoon” Botnet Targets D-Link Routers With Decade-Old Flaw
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Malware
MalwareZLoader Malware Evolves with Anti-Analysis Trick from Zeus Banking Trojan
-
 Malware
MalwareEternal Malware: CVE-2024-3400 Rootkits Persist Through Palo Alto Firewalls Updates and Resets
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024




