Featured News
-

 357Geek
357GeekHow to Protect Your Wi-Fi Router From Hacking Using Simple Tricks
Short Bytes: The humble wireless router in your home, as you might not think, could be the biggest loophole in your personal...
-

 121Geek
121GeekDon’t Fall for Stupid Scam, Facebook Won’t Charge You any Privacy Fee
Last week, news spread across the web (appearing in newsfeeds of many users) that Facebook is about to assign a fee for...
-
 171Hacked
171HackedWinRAR Exposed to Dangerous Vulnerability: Attack Just by Unzipping Files
Short Bytes: The latest WinRAR SFX v5.21 update has a serious vulnerability that allows remote attackers to execute any malicious code on your...
-

 180Vulnerabilities
180VulnerabilitiesMicrosoft Exchange Server Fixed Against Information Disclosure Bug
Vulnerability allowed hackers to hijack active user sessions.Microsoft Exchange Server has been recently patched to fix an important security vulnerability which would...
-

 206Data Security
206Data SecurityXOR DDoS Attack Tool Being Used to Launch Over 20 Daily Attacks
Threat actors are using a previously discovered distributed denial-of-service (DDoS) attack tool dubbed XOR DDoS to launch upwards of 20 DoS attacks...
-

 292Hacked
292HackedThis New Linux Trojan Launches Deadly DDoS Attacks at 150+ Gpbs
Short Bytes: As more and more Linux systems are going online, the threat to the once-secure Linux systems is increasing. In a...
-

 312Geek
312GeekEdward Snowden Joins Twitter, Stays Classy, Follows the NSA
The NSA whistleblower Edward Snowden has finally joined Twitter and within a few hours he has earned a verified badge along with...
-

 163Vulnerabilities
163VulnerabilitiesSAP Patches 12 SQL Injection, XSS Vulnerabilities in HANA
SAP patched a dozen holes in its in-memory management system, HANA, that could have led to SQL injection attacks, cross-site scripting (XSS)...
-

 100Kids Online
100Kids OnlineUK parents ‘want minimum age for smartphone ownership’
A survey has found that most parents in the UK are keen to see a minimum age introduced for smartphone ownership.
-

 227News
227NewsIntended crucifixion of Ali Mohammed al-Nimr Compels Anonymous to Target Saudi Websites
Saudi Arabia’s Government’s decision to crucify Mohammed al-Nimr has prompted a strong response from the Hacktivist group Anonymous when various significant Saudi government websites were hacked...
-

 218Hacked
218HackedBlackphone 2 Could Be the Most Secure Android Phone Ever, And It’s Now On Sale
Short Bytes: To address your privacy concerns, Silent Circle has tried to create the super-secure Android phone and its newest model Blackphone...
-
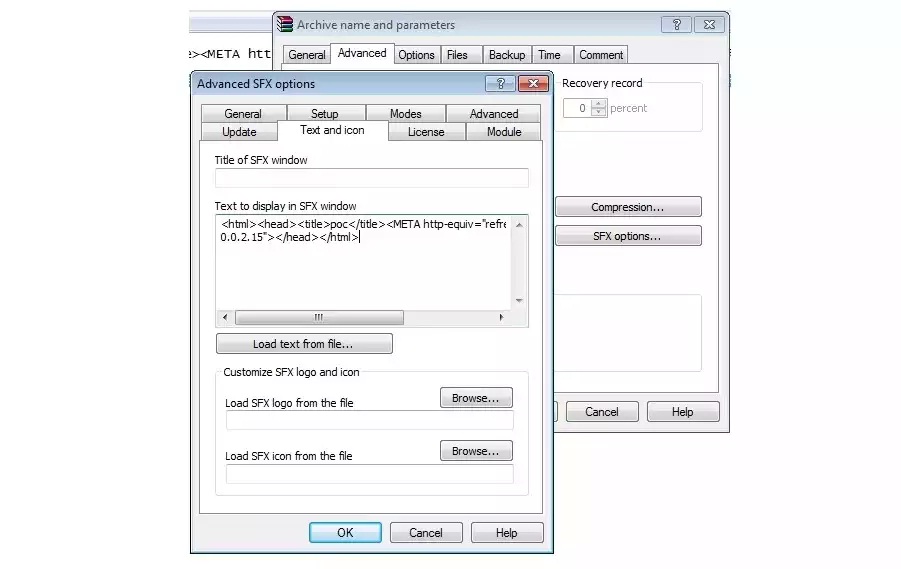
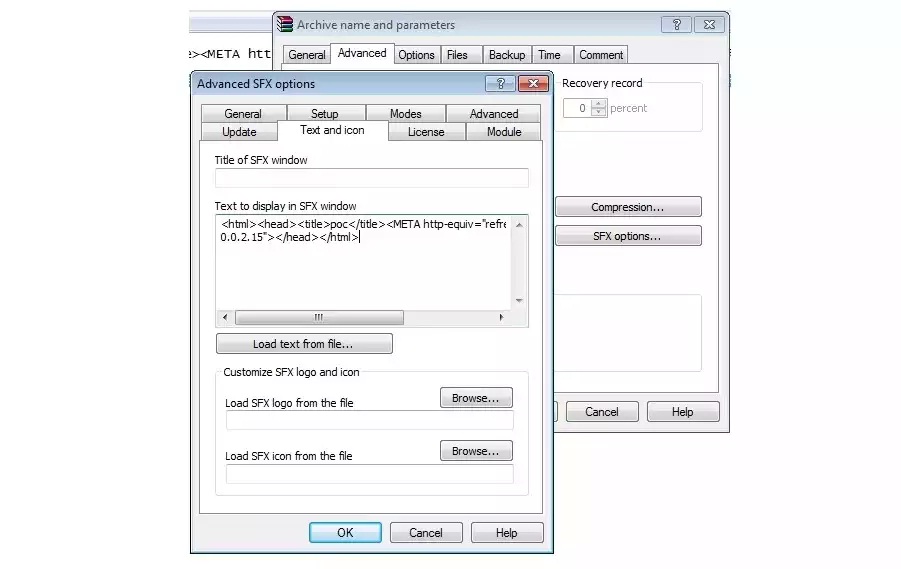 258Vulnerabilities
258VulnerabilitiesLatest Version of WinRAR Plagued by Dangerous Security Bug
WinRAR, the popular file compression and decompression utility, has a security vulnerability that allows attackers to remotely execute code on the user’s...
-

 294Geek
294GeekWindows Registry now Providing Shelter to Destructive Kovter Malware
Kovter Trojan can hide in Windows registry and does not need to be stored on the computer’s hard drive- claims Symantec —...
-

 100Malware
100MalwareDyreza Trojan Targeting IT Supply Chain Credentials
The Dyreza Trojan long ago ceased its exclusive focus on stealing banking credentials, and has been blamed for its part in attacks...
-

 270Data Security
270Data SecurityEdward Snowden joins Twitter and follows NSA
Fugitive US intelligence contractor Edward Snowden has opened an account on the social network website Twitter. His opening tweet was: “Can you...
-
 308Hacked
308HackedWelcome to the Darknet: The Underground for the “Underground”
Short Bytes: Do you know about the Darknet and TOR? Here’s an interesting piece of information if you are interested in the...
-

 409How To
409How ToGetting Started With Raspberry Pi – Get Everything You’ll Need (Part – 2)
Short Bytes: In the second article of Getting Started With Raspberry Pi series on fossBytes, I’ll be telling you about all the...
-

 182Data Security
182Data SecurityPirate Bay co-founder Gottfrid Svartholm Warg—aka Anakata—exits prison
Pirate Bay is online and playing a game of cat and mouse with IP regulators. Pirate Bay co-founder Gottfrid Svartholm Warg was released...
-
 309Hacked
309HackedMicrosoft Explains: “We Are Not Spying On You With Windows 10”
Short Bytes: Finally, Microsoft takes some time to address the widespread Windows 10 privacy concerns. In a blog post on Windows.com, a...
-
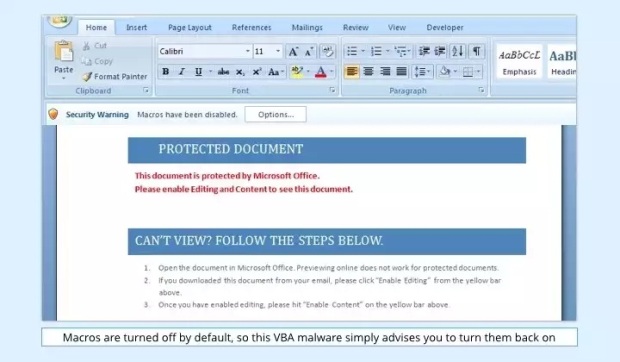
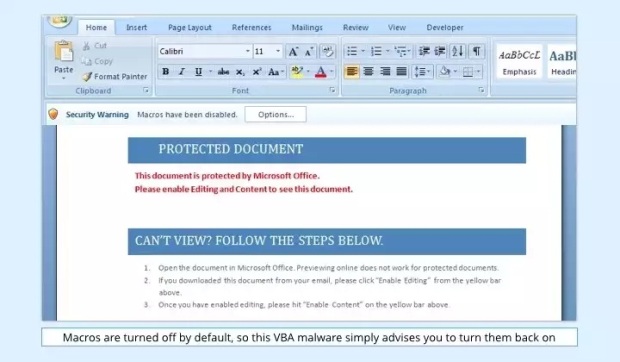 165Malware
165MalwareVBA Malware Makes a Comeback Inside Booby-Trapped Word Documents
VBA stands for Visual Basic for Applications and is a programming language developed by Microsoft to help programmers create Windows applications using...
The Latest
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Malware
MalwareChina-Linked Hackers Suspected in ArcaneDoor Cyberattacks Targeting Network Devices
-
 Malware
MalwareNew ‘Cuckoo’ Persistent macOS Spyware Targeting Intel and Arm Macs
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Malware
MalwareHackers Increasingly Abusing Microsoft Graph API for Stealthy Malware Communications
-
 Malware
MalwareNSA, FBI Alert on N. Korean Hackers Spoofing Emails from Trusted Sources
-
 Vulnerabilities
VulnerabilitiesFour Critical Vulnerabilities Expose HPE Aruba Devices to RCE Attacks
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Vulnerabilities
VulnerabilitiesWhen is One Vulnerability Scanner Not Enough?
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Vulnerabilities
VulnerabilitiesNew “Goldoon” Botnet Targets D-Link Routers With Decade-Old Flaw
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Malware
MalwareZLoader Malware Evolves with Anti-Analysis Trick from Zeus Banking Trojan
-
 Malware
MalwareEternal Malware: CVE-2024-3400 Rootkits Persist Through Palo Alto Firewalls Updates and Resets
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024




