Featured News
-
 191Data Security
191Data SecurityExploit broker offers $1 million for reliable iOS 9 exploit
Here’s a treat for hackers and security researchers who don’t mind selling information about zero-day vulnerabilities to the highest bidder: Zerodium, the...
-
 390Hacked
390HackedWorld’s Biggest 0-day Bug Bounty Program: Hack Apple iOS 9 to Win $1,000,000
Short Bytes: Security firm Zerodium has launched “The Million Dollar iOS 9 Bug Bounty”, that offers $1 million for finding vulnerabilities and...
-

 248Data Security
248Data SecuritySoon, you may not be able to delete WhatsApp messages for 90 days
Govt mulls a policy that requires users to save messages, and hand them over to law enforcement agencies, if asked. Deleting WhatsApp...
-

 177Vulnerabilities
177VulnerabilitiesAdobe Patches 23 Critical Vulnerabilities in Flash Player
Adobe has released a Flash Player update that addresses 23 critical vulnerabilities in the software, many which can lead to code execution....
-

 192Malware
192MalwareTop QLD sex shop cops Cryptowall lock; cops flop as state biz popped
Cryptowall attackers are smashing businesses in the Australian state of Queensland, according to the owner of a Townsville sex shop which has...
-

 158Geek
158GeekGhost Push Android Malware Responsible for Infecting 600k New Users Daily
The Ghost Push malware comes with those Android apps that are available at non-Google app stores. The newly discovered Android malware dubbed as Ghost Push Malware has...
-

 210Vulnerabilities
210VulnerabilitiesAndroid Malware Steals Money from Your Bank Account, Hides SMS Transaction Alerts
New Android malware was discovered, able to steal money from online banking accounts, and hide SMS notifications coming to confirm financial transactions....
-
 379Hacked
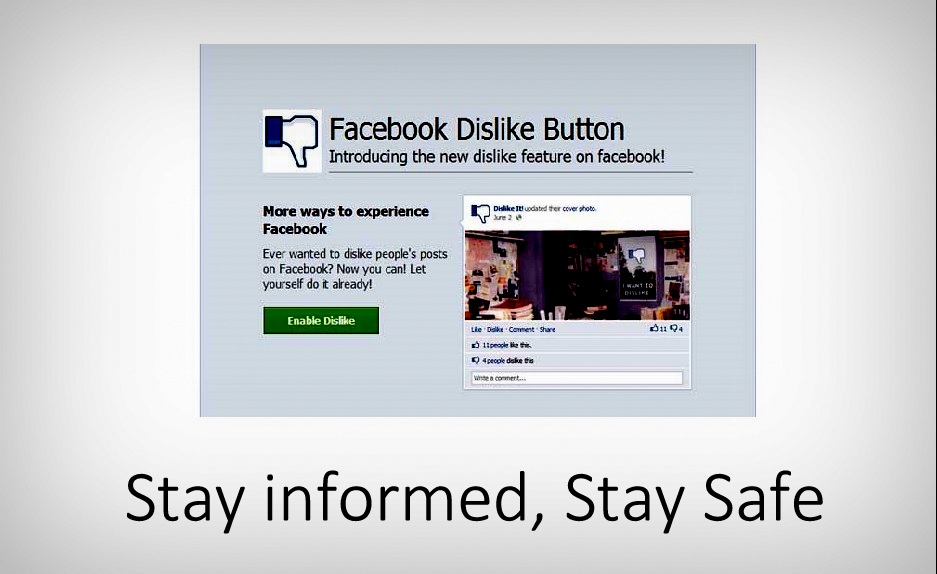
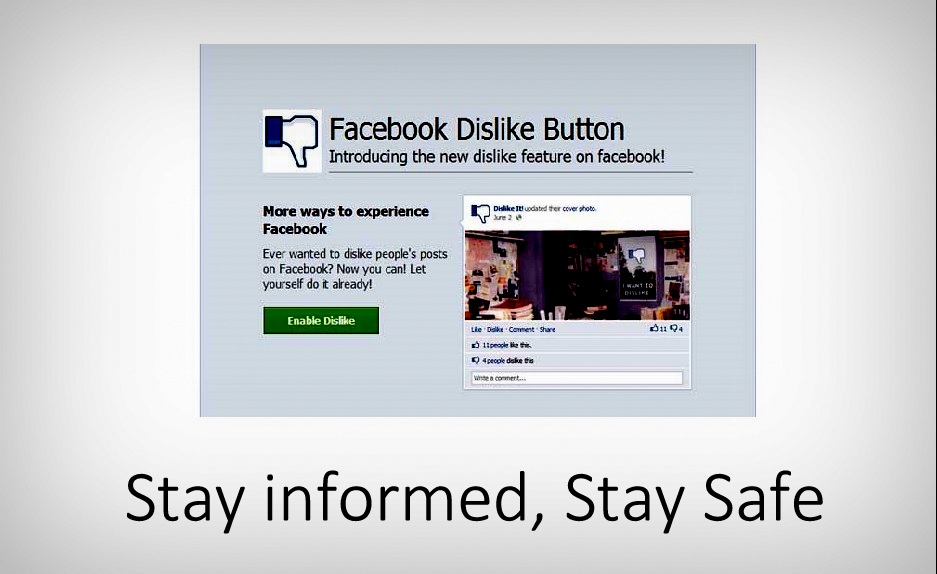
379HackedStay Informed, Stay Away from Facebook Dislike Button Scams
Short Bytes: It’s reported that scammers are taking advantage of Facebook Dislike button anticipation and they’re using the Facebook users. These scams trick...
-

 90Data Security
90Data SecurityBitcoinist Weekly News Re-Hash: BitPay Hack, California Bitcoin Bill Dies
After two weeks of sharp, last minute changes in the Bitcoin price, the markets caught a break this week, with the price...
-

 102Hacked
102HackedIndia’s New Encryption Policy is Ridiculous, Deleting Your Chats Could Soon Become Illegal
Short Bytes: The government of India doesn’t understand the concept of online privacy and the importance of encryption. A new government body...
-

 75Malware
75MalwareApple removes hundreds of malicious apps after major malware attack
Apple has removed more than 300 malicious apps after confirming the first major breach to its iOS app store.
-
 75Data Security
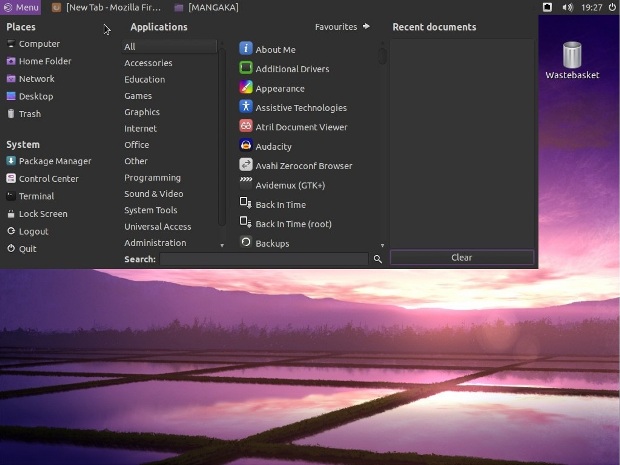
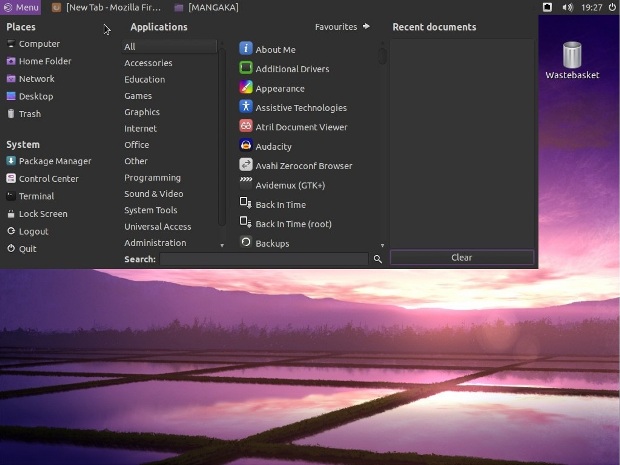
75Data SecurityLinux Mangaka Mou Arrives for Anime and Manga Fans, Based on Ubuntu 14.04 LTS
Just a few minutes ago, September 20, Animesoft International had the great pleasure of informing Softpedia about the immediate availability for download...
-

 178Incidents
178IncidentsUS Air Force Creates an Airplane for Hacking Enemy Military Networks
At the Air Force Association Air & Space conference in National Harbor, Maryland (near Washington), Major General Burke Wilson revealed a new...
-

 218Data Security
218Data SecurityHow malware finally infected Apple iOS apps: XCodeGhost
Hackers can’t easily get malware directly in iOS apps so they’re taking a different approach: Modifying the programming environment that Apple provides...
-

 216Incidents
216IncidentsAnonymous Philippines Hacks Telecom Commission Site Against Slow Internet Speed
Anonymous Philippines, an affiliate of the online hacktivist group Anonymous, hacked and defaced the official website of the country’s National Telecommunications Commission (NTC) Sunday...
-

 239Geek
239GeekScammers Targeting Facebook Users with Dislike Button Scam
New Dislike button scam has started to make rounds on the Facebook, one of the most popular and widely used social media...
-
 372How To
372How ToGetting Started With Docker – Intro to Containers World (Part -1)
Short Bytes: Linux containers (LXC) are very popular these days among developers and companies (perhaps due to Docker, which leverages LXC on the...
-

 270News
270NewsHow Your ATM Card Data Could Get Hacked
Security experts have warned ATM (Automated Teller Machine) users to stay clear from suspicious ATMs for past several years because of numerous...
-
 240Geek
240Geek“My First Line of Code”: Linux Creator Linus Torvalds
Short Bytes: Linus Torvalds is the creator of Linux and he still decides what will happen in the world of Linux. Read...
-

 239News
239NewsAnonymous Hacks Vietnam Govt websites Against Human Rights Abuse
The online hacktivists affiliated to Anonymous, AntiSec and HagashTeam conducted a cyber attack on Vietnamese government websites against online censorship and human...
The Latest
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Malware
MalwareChina-Linked Hackers Suspected in ArcaneDoor Cyberattacks Targeting Network Devices
-
 Malware
MalwareNew ‘Cuckoo’ Persistent macOS Spyware Targeting Intel and Arm Macs
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Malware
MalwareHackers Increasingly Abusing Microsoft Graph API for Stealthy Malware Communications
-
 Malware
MalwareNSA, FBI Alert on N. Korean Hackers Spoofing Emails from Trusted Sources
-
 Vulnerabilities
VulnerabilitiesFour Critical Vulnerabilities Expose HPE Aruba Devices to RCE Attacks
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Vulnerabilities
VulnerabilitiesWhen is One Vulnerability Scanner Not Enough?
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Vulnerabilities
VulnerabilitiesNew “Goldoon” Botnet Targets D-Link Routers With Decade-Old Flaw
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Malware
MalwareZLoader Malware Evolves with Anti-Analysis Trick from Zeus Banking Trojan
-
 Malware
MalwareEternal Malware: CVE-2024-3400 Rootkits Persist Through Palo Alto Firewalls Updates and Resets
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024




