Featured News
-

 194News
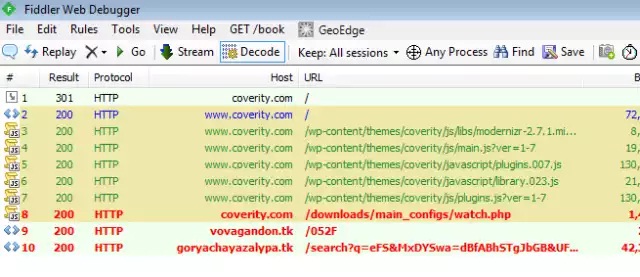
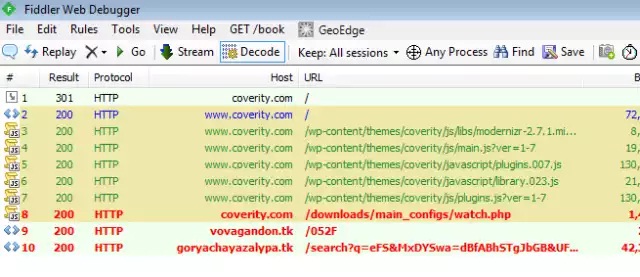
194NewsScreenshot Malware Spying On Online Poker Players
A unique malware has been found by security experts which spies on the players of online poker gaming sites, specifically Full Tilt...
-
 282Hacked
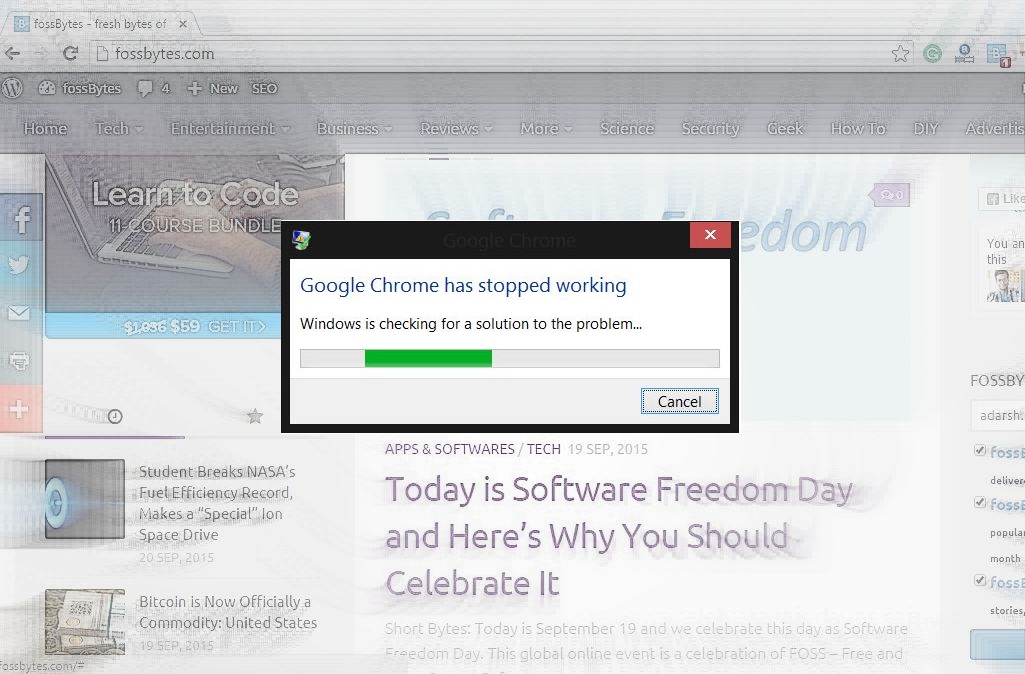
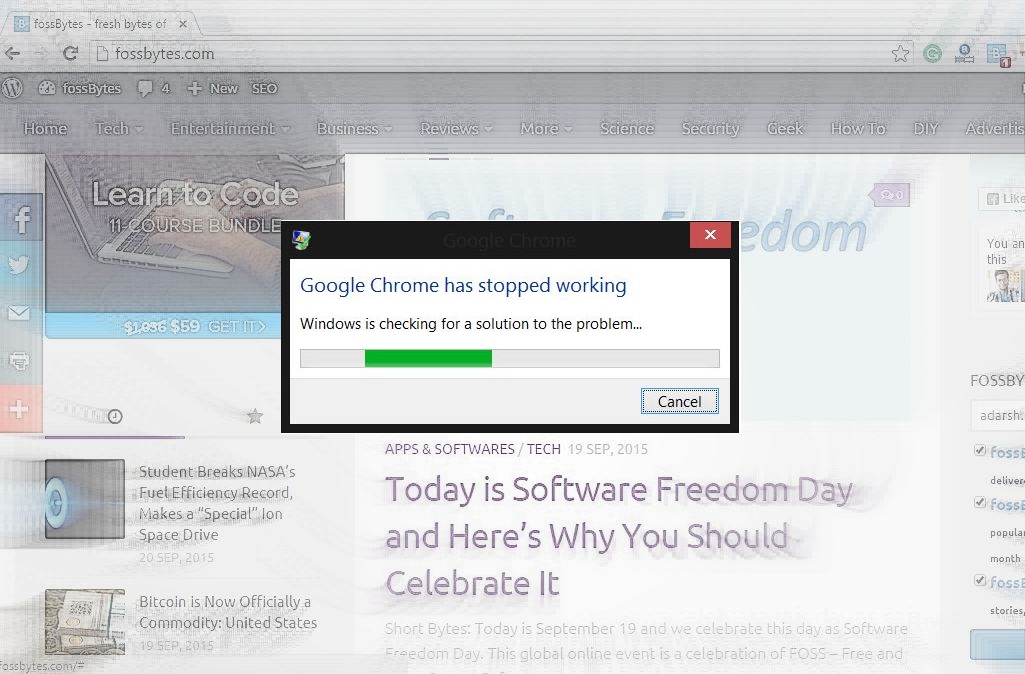
282HackedHow and Why Crash Google Chrome With These 16 Characters in 2 Seconds
Short Bytes: Do you want to crash someone’s Google Chrome just for the heck of it? Here’s how to do it with...
-

 309Geek
309GeekMicrosoft Windows Devices Responsible For 80% of Malware Infections
Microsoft Windows, in spite of having an insignificant share in the mobile market, is the leading operating system that is responsible for...
-
 324News
324NewsPhishing Attack Causes Bitcoin Payment Processor BitPay to Lose $1.8M
BitPay the Atlanta-based Bitcoin payment processor had been hit by a massive phishing attack costing the company $1.8 million. Verified by the...
-
 168Data Security
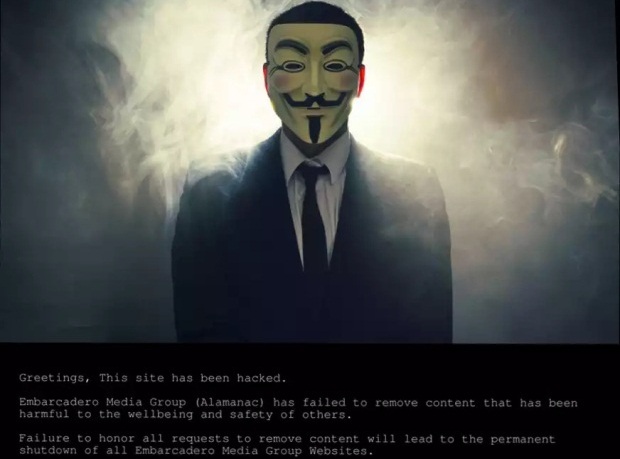
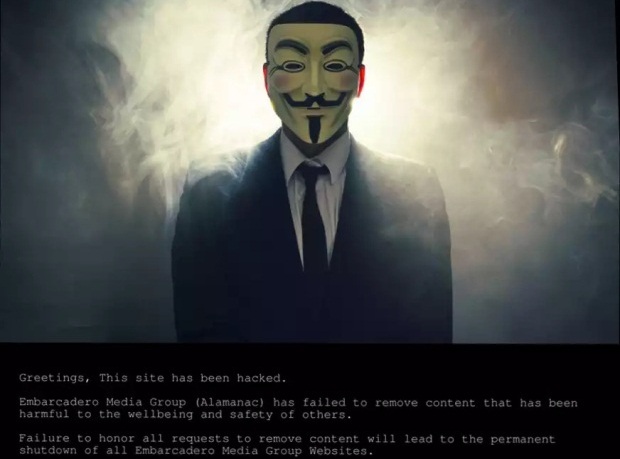
168Data SecurityHackers Hold Silicon Valley’s Hometown Newspapers Hostage
Sometime yesterday, 17 September, hackers took over the websites of Silicon Valley’s Embarcadero Media Group, publisher of the Palo Alto Weekly, theAlmanac,...
-
 150Malware
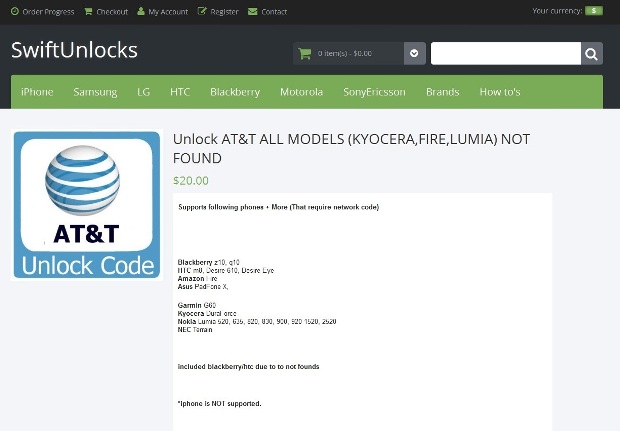
150MalwareAT&T Employees Installed Malware on Their PCs to Aid Phone Unlocking Service
AT&T has filed a lawsuit against 3 former call center employees, accusing them of installing malware on their servers with the purpose...
-

 102Data Security
102Data SecurityHack Brief: Malware Sneaks Into the Chinese iOS App Store
THE APPLE ECOSYSTEM is well known for very rarely letting any dodgy apps enter it because of the company’s stringent security checks....
-

 127Malware
127MalwareNew PoS Trojan Can Download Other Malware, Launch DDOS Attacks
The world of computer viruses and antivirus solutions is in a constant change, with cyber-crooks evolving their code and cyber-security firms trying...
-

 198Vulnerabilities
198VulnerabilitiesD-Link Accidentally Leaks Private Code-Signing Keys
A simple mistake by networking gear manufacturer D-Link could have opened the door for costly damage. Private keys used to sign software...
-
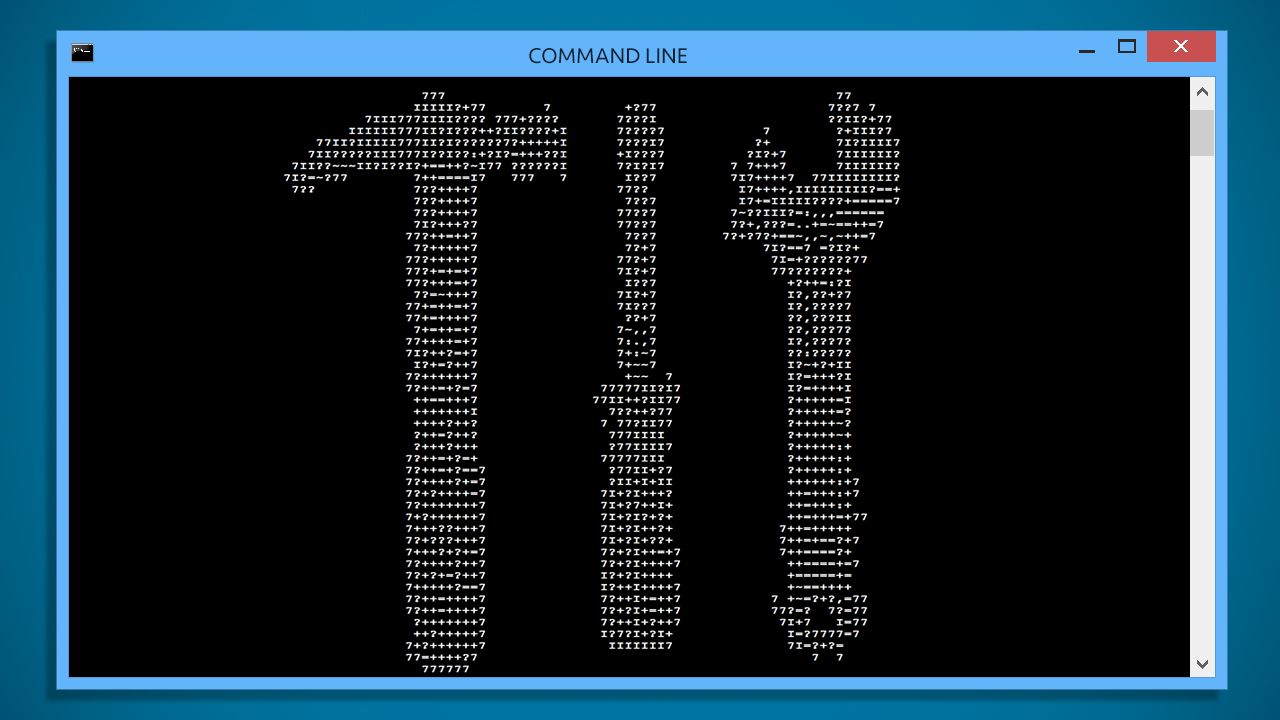
 227Tricks & How To's
227Tricks & How To's10 Windows Commands you need to know for Troubleshooting
The command line is an interface for typing commands directly to a computer’s operating system. It is usually used to resolve Microsoft...
-

 288Hacked
288Hacked“seL4” is an Unhackable Kernel for Keeping All Computers Safe From Cyberattack
Short Bytes: The Australian national research agency Data61 has developed an unhackable kernel named seL4 and proved its unhackable property mathematically. The kernel...
-
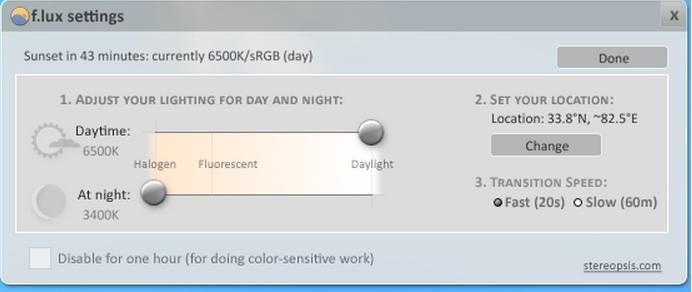
 176Tricks & How To's
176Tricks & How To'sSave your eyes from Computer Strain
No more watery eyes, when you wake up from sleep in the middle of the night to work on your bright computer...
-

 312Data Security
312Data SecurityRussian Hacker who stole 160 million credit card details gets sentenced for 30 years in prison
Russian national pleads guilty in global hacking scheme. Russian Hacker Vladimir Drinkman faces 30 years sentence after pleading guilty to hacking NASDAQ,...
-
 78Malware
78MalwareThe evolution of ransomware: From PC Cyborg to a service for sale
A look back at how ransomware – a type of malware used mostly for hijacking user data – has evolved from the...
-
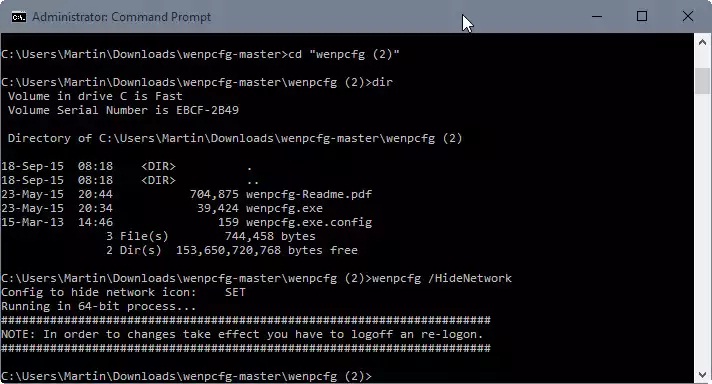
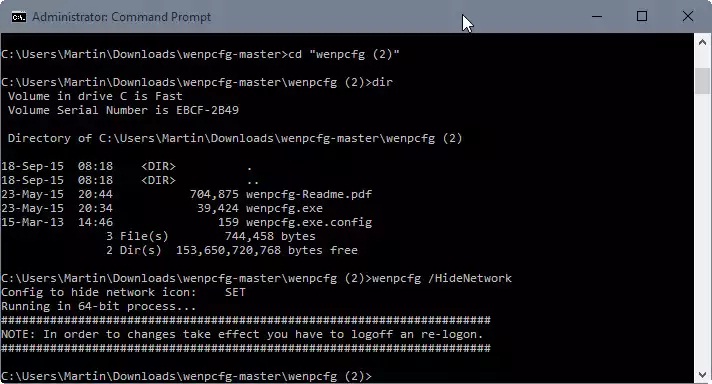 102Data Security
102Data SecurityRemove Libraries, Network, Homegroup and other links from File Explorer
When you open File Explorer in Windows 10, the system’s default file browsing and management tool, you will notice immediately that it...
-
 78Data Security
78Data Security3D printed TSA Travel Sentry keys really do open TSA locks
Last year, the Washington Post published a story on airport luggage handling that contained unobscured images of the “backdoor” keys of the Transportation...
-

 153Malware
153MalwareDutch Police Arrest Alleged CoinVault Ransomware Authors
Ransomware has emerged as major threat to consumers and businesses in recent years, and law enforcement agencies and security researchers have taken...
-
 109Malware
109MalwareActive malware campaign uses thousands of WordPress sites to infect visitors
15-day-old campaign has spiked in past 48 hours, with >5,000 new infections daily. Attackers have hijacked thousands of websites running the WordPress...
-

 176Geek
176GeekAVG Sells Your Data To Third Parties To Make Money
Antivirus and Security vendor AVG, based in Czech Republic and creator of one of the world’s leading antivirus software collections, is excited...
-
 109Cyber Crime
109Cyber CrimeHackers Using Amazon As A Bait For Phishing Attacks
A new phishing campaign has been doing the rounds on the Internet in which hackers are using Amazon UK’s fake email message...
The Latest
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Malware
MalwareChina-Linked Hackers Suspected in ArcaneDoor Cyberattacks Targeting Network Devices
-
 Malware
MalwareNew ‘Cuckoo’ Persistent macOS Spyware Targeting Intel and Arm Macs
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Malware
MalwareHackers Increasingly Abusing Microsoft Graph API for Stealthy Malware Communications
-
 Malware
MalwareNSA, FBI Alert on N. Korean Hackers Spoofing Emails from Trusted Sources
-
 Vulnerabilities
VulnerabilitiesFour Critical Vulnerabilities Expose HPE Aruba Devices to RCE Attacks
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Vulnerabilities
VulnerabilitiesWhen is One Vulnerability Scanner Not Enough?
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Vulnerabilities
VulnerabilitiesNew “Goldoon” Botnet Targets D-Link Routers With Decade-Old Flaw
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Malware
MalwareZLoader Malware Evolves with Anti-Analysis Trick from Zeus Banking Trojan
-
 Malware
MalwareEternal Malware: CVE-2024-3400 Rootkits Persist Through Palo Alto Firewalls Updates and Resets
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024




