Featured News
-
 301How To
301How ToiOS 9 Release: How to Prepare Your iPhone for iOS 9 Upgrade
Short Bytes: The latest iOS iteration is slated to arrive on September 16. iOS 9 will bring new features and you need to...
-

 297Geek
297GeekNATO Will Check for Backdoors in Microsoft’s Products
Microsoft has taken NATO onboard in its program which presents information about vulnerabilities and provides access to source code. A Security Agreement...
-

 318Data Security
318Data SecurityCisco Routers Vulnerable To Malware Attacks Via Backdoor Firmware Installation
It has always been believed that Cisco routers being used in the enterprise environment could be hacked via installation of backdoor firmware,...
-

 197Android Hacking
197Android HackingAdding a Recycle bin to your Android device
Adding a Recycle Bin to your Android phone and tablet provides a safeguard in case you erase some valuable photos, videos, text...
-

 252Data Security
252Data SecurityGCHQ Encouraging Users To Use Simple Passwords
The common perception is that a strong password is always a good password, but GCHQ thinks otherwise; urging people to use “simple passwords” to keep...
-

 243Geek
243GeekKnow Everything About World’s First Programmer, Ada Lovelace
Short Bytes: Ada Lovelace is known as the first programmer in the history and pioneer of the modern computing. Her name is...
-

 214Geek
214GeekDad of Minor Daughter Exposed to Predators on Facebook Gets Paid
Father of Vulnerable Minor Daughter exposed to Sexual Predators on Facebook gets paid an Undisclosed Amount. Facebook was forced to enforce its...
-

 379Banking
379BankingTop tips on safe online banking from the comfort of your home
Online banking from the comfort of your own home makes life much easier, but you may still be at risk of cybercrime....
-
 155Data Security
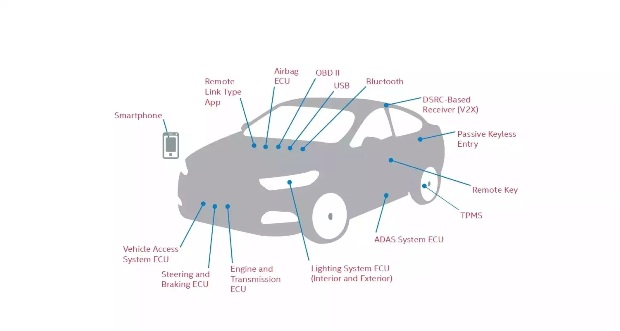
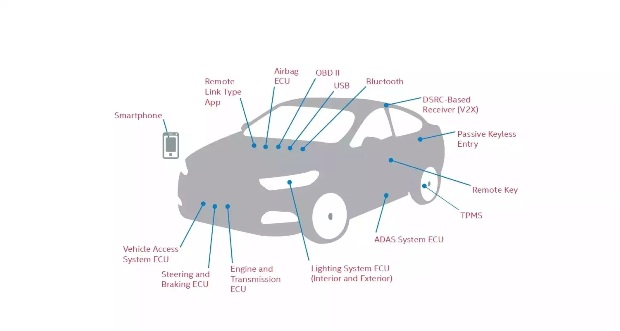
155Data SecurityIntel Announces the Automotive Security Review Board (ASRB) to Take On Car Hackers
This Sunday, Intel announced the creation of the Automotive Security Review Board (ASRB) to help automakers secure cars and drivers in the...
-
 113Data Security
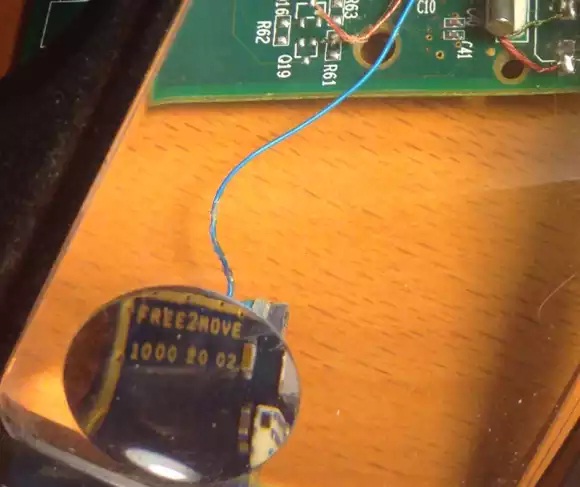
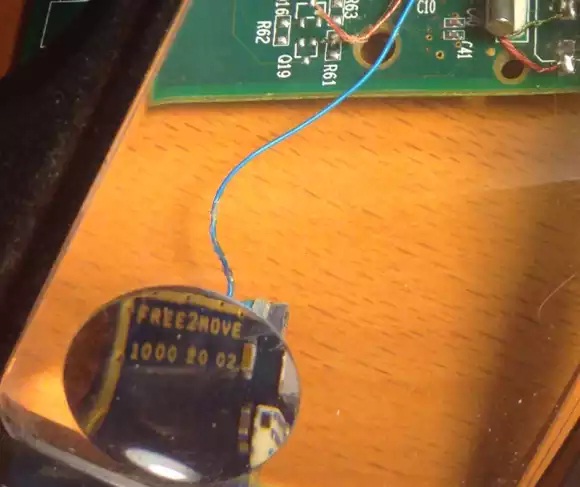
113Data SecurityTracking a Bluetooth Skimmer Gang in Mexico
Halfway down the southbound four-lane highway from Cancun to the ancient ruins in Tulum, traffic inexplicably slowed to a halt. There was some...
-
 159Vulnerabilities
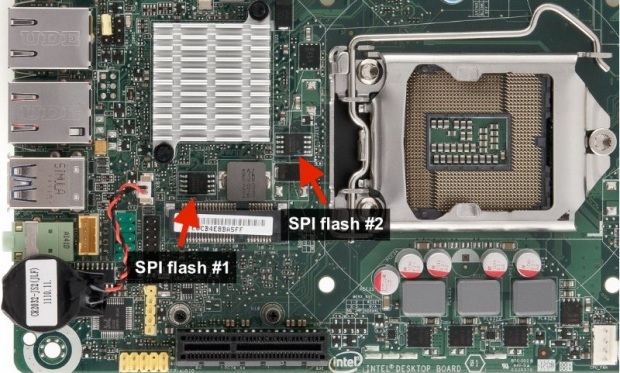
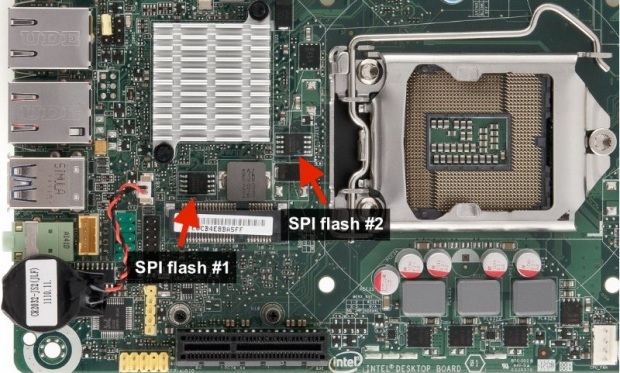
159VulnerabilitiesCHIPSEC Module That Exploits UEFI Boot Script Table Vulnerability
This vulnerability was discovered by Rafal Wojtczuk and Corey Kallenberg, check original white paper. Around one month ago, at 31-st Chaos Communication...
-
 172Geek
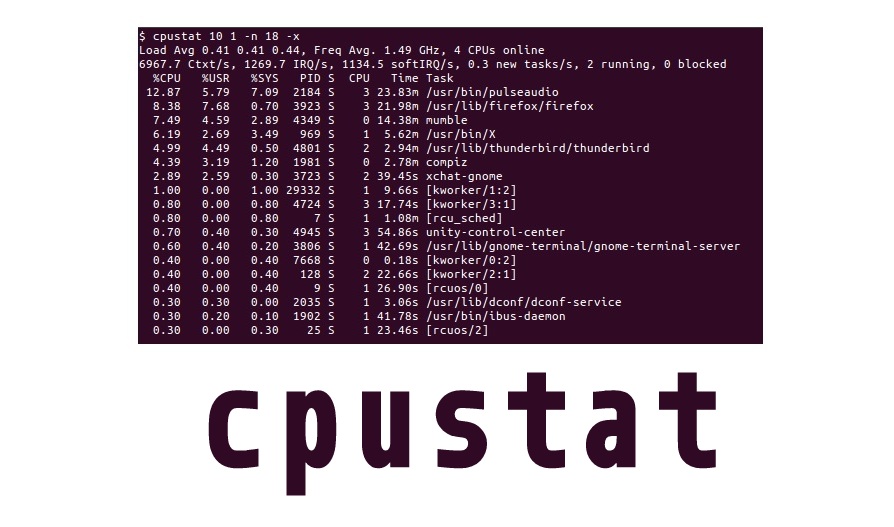
172Geekcpustat – A Lightweight Process Stats Tool For Small Ubuntu Devices
Short Bytes: cpustat is a lightweight tool for monitoring per-process cpu utilization (from /proc/$pid/stat) in a fast and efficient way with minimal overhead. It is...
-

 209Malware
209MalwareHackers Could Use ATM Malware To Steal Debit & Credit Cards
A new ATM malware has hit the streets and it’s called Suceful. This new malware seems to have been created in August 2015, and...
-
 290Hacked
290HackedThe Top 5 Most Hackable Cars You Shouldn’t Buy (And the Safest Ones)
Short Bytes: A forensic consultancy PT&C}|LWG Forensic Consulting Services has made a list of top 5 most hackable cars by performing a...
-

 159Cyber Crime
159Cyber CrimeHackers Can Infect ATM With Malware To Hold Your Card
Security researchers over at FireEye have discovered a serious security flaw within the ATM (Automated Teller Machine) that could be exploited by...
-

 304Geek
304GeekPosting @[4:0] in Facebook Comment Shows ‘Mark Zuckerberg’, it Won’t Get You Hacked
Get Mark Zuckerberg Displayed simply by typing @[4:0] as a Facebook Comment — This isn’t a hacking related issue so no need to be on high...
-

 231Geek
231GeekWindows 10 Lets Users Log into Their PC with a Picture Password
Since its release, Windows 10 is surrounded by controversies, but at the same time the operating system offers some mind-blowing features such as...
-

 196Geek
196GeekNew Android Malware Changes PIN Code and Demand Ransom
Android users need to be highly careful while using your smartphone as ESET researchers have identified simplocker, a new screen-locking malware that...
-
 198Hacked
198HackedNorth Korea Hacks Into Word Processor Used by South Korean Government
Short Bytes: According to the security firm FireEye, Hangul Word Processor program used by the South Korean government was recently hacked by North...
-
 227How To
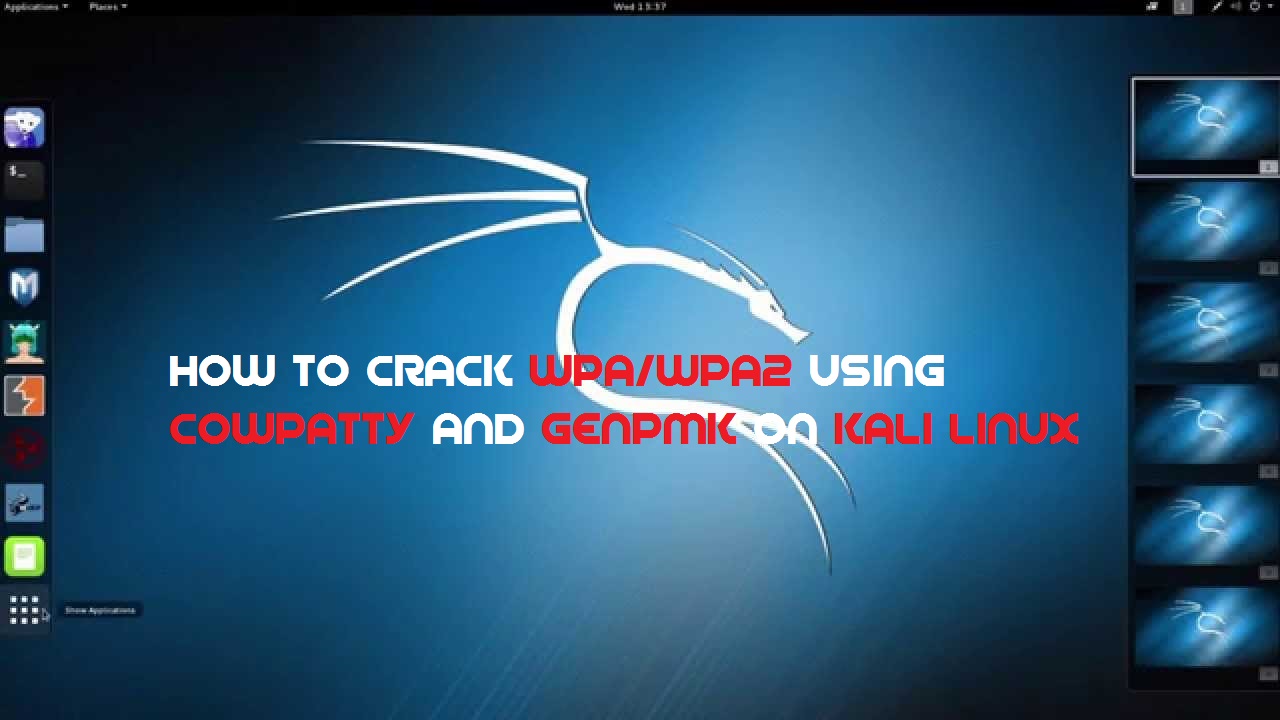
227How ToCrack WPA & WPA2 with Cowpatty and Negpmk on Kali Linux
In this tutorial we are going to teach you How to crack WPA & WPA 2 with cowpatty and negpmk on Kali Linux. We...
The Latest
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Cyber Attack
Cyber AttackMicrosoft Patches 61 Flaws, Including Two Actively Exploited Zero-Days
-
 Cyber Attack
Cyber AttackThe 2024 Browser Security Report Uncovers How Every Web Session Could be a Security Minefield
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Data Breach
Data BreachBlack Basta Ransomware Strikes 500+ Entities Across North America, Europe, and Australia
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Data Breach
Data BreachA SaaS Security Challenge: Getting Permissions All in One Place
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment




