Featured News
-

 279Hacked
279HackedIntel Makes Automotive Security Review Board to Save Your Cars From Getting Hacked
Short Bytes: In the wake of recent car hacks and security breaches, Intel has planned to establish an Automotive Security Review Board (ASRB)...
-
 91Data Security
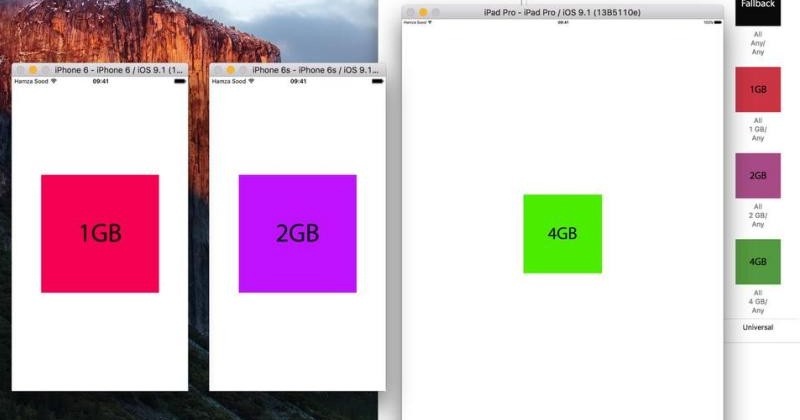
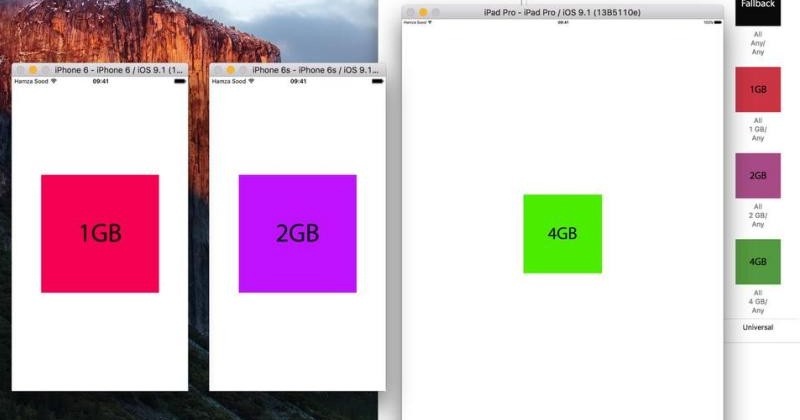
91Data SecurityXcode hack confirms 2GB RAM on iPhone 6s, 4GB on iPad Pro
Apple is traditionally mum on some details of its devices’ hardware, preferring to talk about how “B is X times faster than...
-

 77Data Security
77Data SecurityHow did jihadists hack into top UK ministerial emails if no security breach took place?
Answers on a postcard from Syria, please. GCHQ has declined to comment on a report in the Daily Telegraph this weekend, which...
-

 170Vulnerabilities
170VulnerabilitiesYokogawa patches widespread SCADA vulnerability
Networking process crashed by crafted packets. One of the world’s major suppliers of industrial networking kit, Japanese company Yokogawa, has alerted the...
-
 205Malware
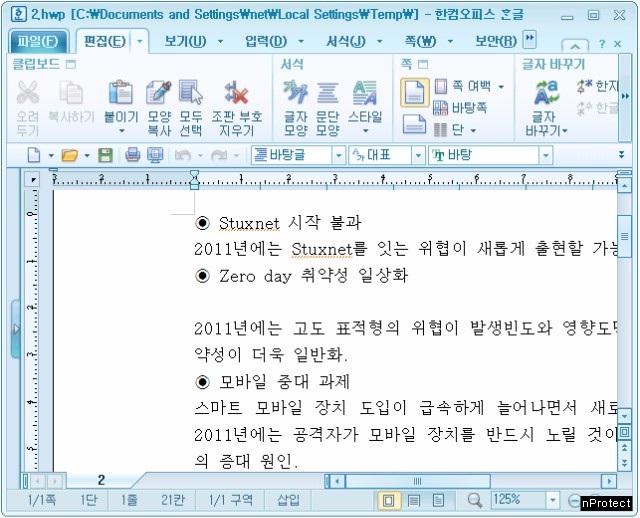
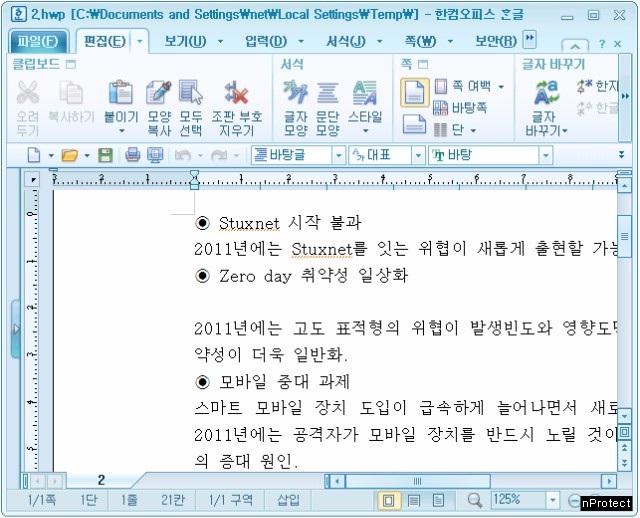
205MalwareNorth Korea Installs Backdoor in South Korea’s Favorite Word Processor
Hackers linked to known North Korean attack points and methods exploited a zero-day vulnerability in the Hangul Word Processor (HWP), widely deployed...
-
Firewall
GlassWire – Best Firewall Software
GlassWire is a lot more than just a great firewall. The free firewall software monitors your network in an easy to understand...
-

 340How To
340How ToGetting Started With Raspberry Pi – Knowing Your Pi (Part – 1)
Short Bytes: The credit-card-sized Raspberry Pi was released long back in 2012 and it has grown to become one of the most...
-

 215Geek
215GeekWhat’s New in iOS 9 SDK?
Short Bytes: iOS 9 SDK includes new APIs and services that are enabling new categories of apps and features. Multitasking and gaming APIs...
-

 206News
206NewsSmartwatch Users Beware – Report Identifies Vulnerabilities in Wearable Devices
In the past, we reported how your wearable fitness trackers can be hacked. Now, The university of Illinois at Urbana-Champaign’s associate professor Romit Roy Choudhry...
-
 127Data Security
127Data SecuritySurvey Shows Most Americans are Fine with Backdoor in Their Devices
A recent survey from Vormetric revealed that people in the United States are OK with the addition of backdoors in their devices/software....
-

 212News
212NewsTop British Ministers Hacked by ISIS in Sophisticated Espionage Operation
Crucial information held by some of the most senior ministers of David Cameron (including Home Secretary Theresa May) has possibly landed in...
-

 301Cyber Crime
301Cyber CrimeSearching For Hacking Software Leads to Vulnerable Spammy Sites
Thousands of legit websites’ security has been compromised to secretly redirect the visitors, coming through specific search terms, to prospective fraudulent websites...
-
 122Geek
122GeekWordPress High CPU Load Bug After 4.3 “Billie” Upgrade and How to Fix it
Short Bytes: WordPress high CPU load bug – We faced it and I am guessing thousands of other blogs hosted on WordPress faced it too, when...
-
 324Geek
324GeekMicrosoft is Force-Downloading Windows 10 on Windows 7 and 8 Machines
As reported previously how Microsoft released updates to spy on Windows 7, 8 and 8.1 Users just like it does on Windows 10. Now...
-
 224How To
224How ToCrack WPA & WPA2 with Aircrack-ng on Kali Linux
Aircrack-ng best WiFi penetration testing tool used by hackers. In this tutorial we are going to teach you How to Crack WPA &...
-
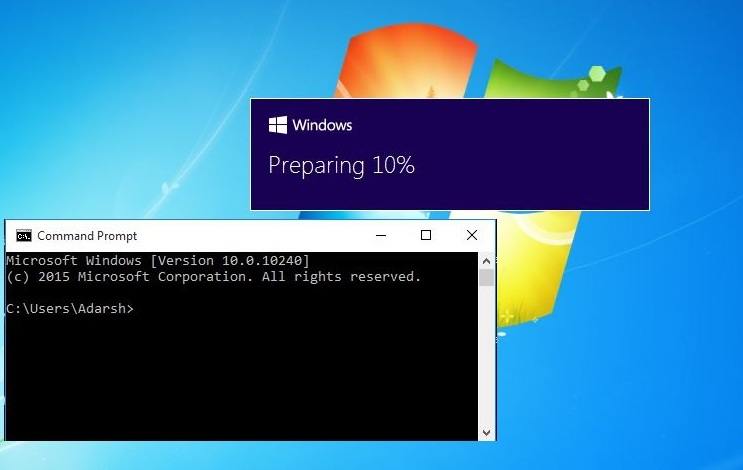
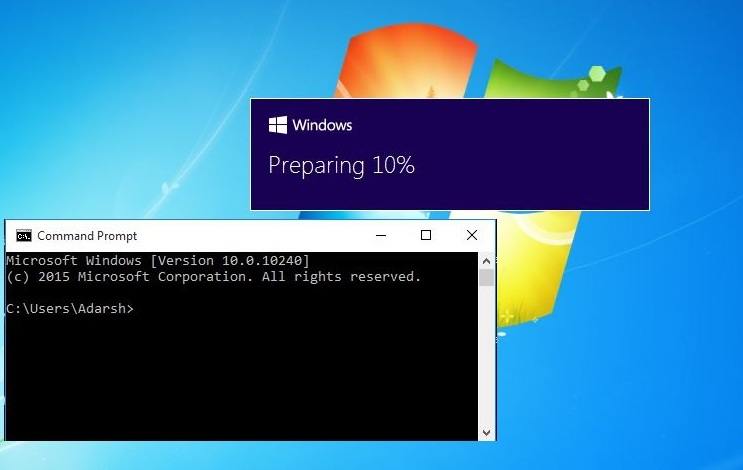 380How To
380How ToHow to Stop Windows 10 Automatic Downloading on Your Windows 7 and 8.1 PC
Short Bytes: It’s reported that some Windows 7 and 8.1 PCs are downloading Windows 10 automatically- even if the users haven’t reserved the...
-
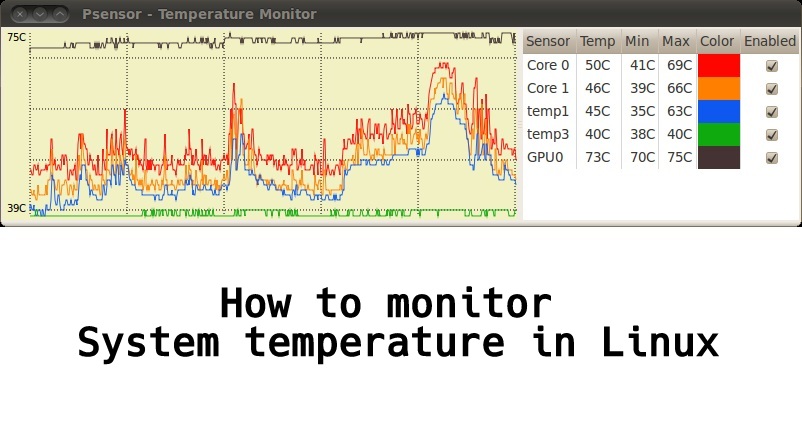
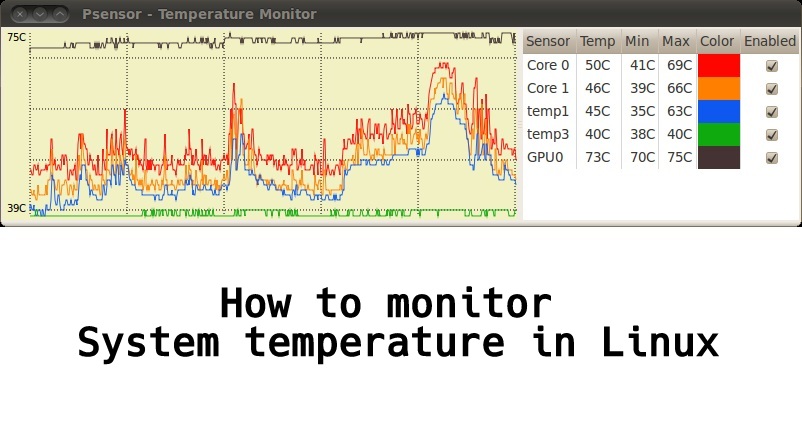 288Geek
288GeekHow to Monitor System Temperature in Linux – GUI Based Temperature Monitoring Tool
Short Bytes: Psensor is a graphical hardware temperature monitor for Linux. It is a GTK+ application for monitoring hardware sensors, including temperatures and fan...
-

 175Vulnerabilities
175VulnerabilitiesiOS 9 Jailbreak: Yes, Apple’s latest version of iOS has already been cracked
Apple will release iOS 9 next week, and some iOS 8 users who rely on unofficial apps installed on their iPhones and...
-
 228Hacked
228HackedMIT is the Most Insecure University in the US
Short Bytes: MIT may boast of having one of the smartest bunch of people under one roof, but when it comes to...
-
 154Data Security
154Data SecurityFirst library to support anonymous Internet browsing effort stops after DHS e-mail
Since Edward Snowden exposed the extent of online surveillance by the US government, there has been a surge of initiatives to protect...
The Latest
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Cyber Attack
Cyber AttackMicrosoft Patches 61 Flaws, Including Two Actively Exploited Zero-Days
-
 Cyber Attack
Cyber AttackThe 2024 Browser Security Report Uncovers How Every Web Session Could be a Security Minefield
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Data Breach
Data BreachBlack Basta Ransomware Strikes 500+ Entities Across North America, Europe, and Australia
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Data Breach
Data BreachA SaaS Security Challenge: Getting Permissions All in One Place
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment




