Featured News
-

 211Data Security
211Data SecuritySelf-Driving Cars Are Hackable
Jonathan Petit, security researcher at Security Innovation, Inc., has revealed he can easily fool the LiDAR sensors on any self-driving car to...
-
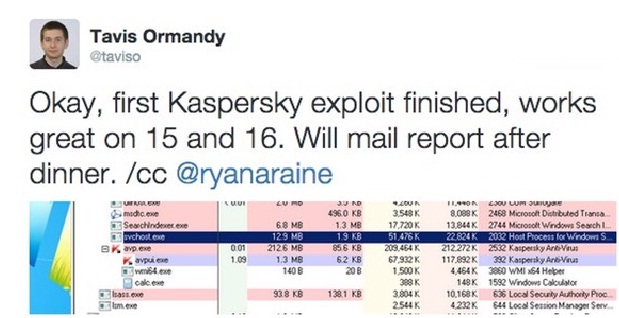
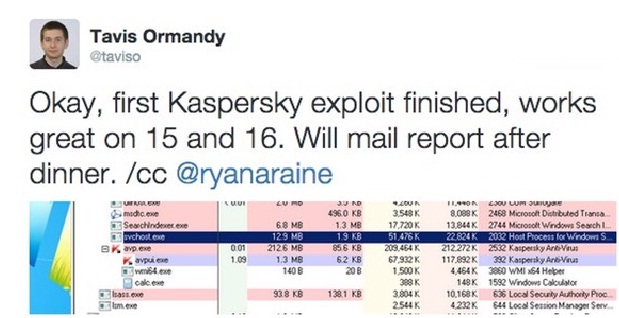 176Vulnerabilities
176VulnerabilitiesZero-day vulnerabilities reportedly found in Kaspersky and FireEye security products
Sounds like it’s going to be a busy few days for R&D and PR departments at least two security companies. This weekend,...
-

 99Data Security
99Data SecurityCoder pleads guilty to writing Gozi banking trojan
A man credited with helping to create the infamous Gozi banking malware has pled guilty in a US court. Deniss Calovskis, 30,...
-

 184Malware
184MalwareOutdated WordPress Sites Used to Deliver Teslacrypt Ransomware
Heimdal Security researchers have observed a new ransomware campaign that utilizes the Neutrino exploit kit to deliver Teslacrypt ransomware to victims via...
-

 298Geek
298GeekiPhone Saves Man’s Life by Stopping a Bullet from Close Range
For those who were complaining about the size of iPhone 5, this guy from the Fresno State owes his life to iPhone 5....
-

 261News
261NewsMozilla’s Bugzilla Hacked, Stolen Data Used For Targeting Firefox users
Mozilla yesterday detailed a security attack on its bug tracker and testing tool Bugzilla, as well as the steps it is taking to mitigate...
-

 312Geek
312GeekMeet Mycroft – World’s 1st Open Source Artificial Intelligence Based on Linux, Raspberry Pi and Arduino
Short Bytes: Using the Internet of Things we will control our future lives by inculcating electronics and internet in each and every small...
-

 315Geek
315GeekHomemade Helicopter Powered By 54 Miniature Drones
Last week, a YouTube user posted a video on his profile in which he recorded a test flight of his homemade personal...
-
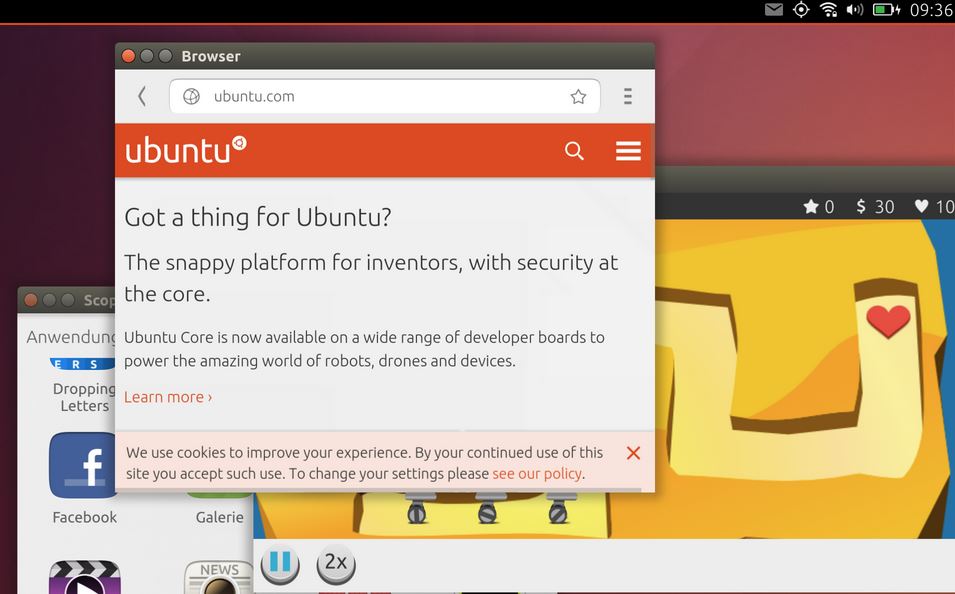
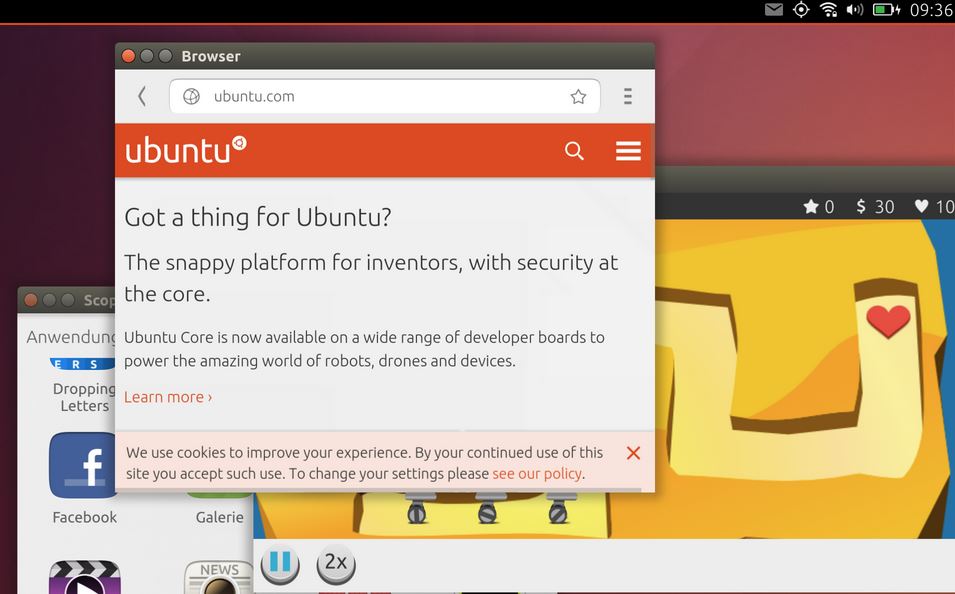 321Geek
321GeekHow to Run Ubuntu Phone in Windowed Mode
Short Bytes: Ubuntu powered phones are gaining popularity each day and we are here with a tweak to run Ubuntu Phone in windowed...
-

 184Reviews
184ReviewsHooks App Review – Get Instant Notifications for Things Important to You
Short Bytes: Hooks is an award winning alert and notification app available for Android and iOS which can send you a notification for anything...
-

 163News
163NewsGenius Teenager Hacked His Parent’s iPhone Text
A genius teenager was planning to throw a party (maybe at his home), but it is usually hard to convince your parents...
-
 333Lists
333ListsSurprising Facebook Facts That You Didn’t Know
Short Bytes: Facebook with its multi-billion user base, is the biggest social media giant today. But there are some things you might not...
-

 78Data Security
78Data Security‘UNSW is drunk’: Facebook page gets hacked on university’s Open Day
UNSW staff had to scramble to contain an embarrassing outbreak of undergraduate humour, after the university’s Facebook page was hacked on its annual...
-
 209Hacked
209HackedMicrosoft: Windows 7 and 8.1 “Spying” Updates Are Completely Optional
Short Bytes: After being criticized due to the introduction of Windows 10-like spying features in Windows 7 and 8.1, Microsoft has tried...
-

 168Vulnerabilities
168VulnerabilitiesAttackers bundle an old version of TeamViewer to exploit vulnerability
We’re used to seeing malware that exploits unpatched vulnerabilities in software. But in a new twist attackers are bundling an old version...
-
 109Data Security
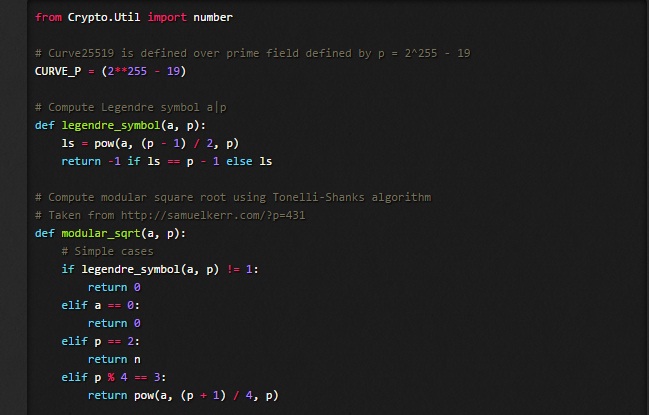
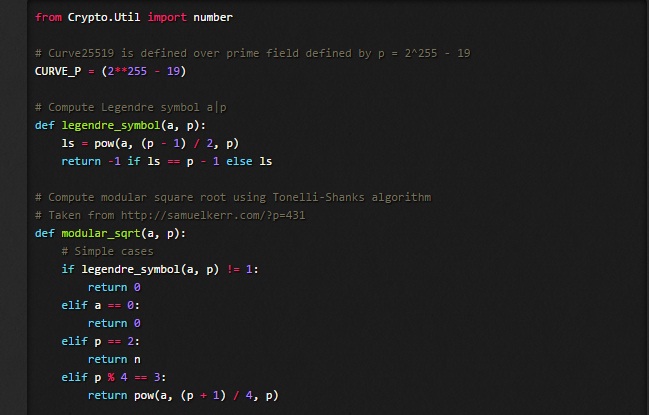
109Data SecurityDetecting an asymmetric Curve25519 backdoor in RSA key generation algorithms
While working on some forthcoming research on cryptographic backdoors i came across an interesting asymmetric backdoor designed to subvert RSA key generation...
-

 103Vulnerabilities
103VulnerabilitiesAttacker Compromised Mozilla Bug System, Stole Private Vulnerability Data
Security experts constantly tell users not to reuse passwords on multiple accounts, but the message often falls on deaf ears. Now, officials at...
-
 199Geek
199GeekPhotos of Drowned Syrian Boy Exploited by Spammers on Facebook
Endangering Humanity: Spammers steep to the lowest level of cruelty — Exploiting the shocking pictures of drowned Syrian boy is plain Inhuman....
-

 123Scams
123ScamsFake vouchers and WhatsApp: Analyzing a new scam trend
Over the last few weeks we’ve seen an increase in fake vouchers being spread via WhatsApp. This scam has all the hallmarks...
-

 270Data Security
270Data Security24 Chinese Android Smartphones Models Come With Pre-Installed Malware
G DATA security experts published their latest research in which they’ve analyzed top Chinese Android smartphone models and found that a large...
The Latest
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Cyber Attack
Cyber AttackMicrosoft Patches 61 Flaws, Including Two Actively Exploited Zero-Days
-
 Cyber Attack
Cyber AttackThe 2024 Browser Security Report Uncovers How Every Web Session Could be a Security Minefield
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Data Breach
Data BreachBlack Basta Ransomware Strikes 500+ Entities Across North America, Europe, and Australia
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Data Breach
Data BreachA SaaS Security Challenge: Getting Permissions All in One Place
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment




