Featured News
-

 314Banking
314BankingSophisticated webinjects ‘tailored’ to beat bank security
From its relatively simplistic and niche origins, webinjects have advanced significantly in recent years to become a more sophisticated beast.
-

 165Malware
165MalwareMatch.com suspends UK advertising after malware warning
Online daters risk being held to ransom in possible cyber attack on Match.com Match.com has suspended advertising on its UK site whilst...
-

 135Malware
135MalwareMore Adult Themed Android Ransomware
During the course of our daily malware hunt, we came across a new mobile ransomware variant that leverages pornography to lure victims...
-

 161Data Security
161Data SecurityChrysler Catches Flak for Patching Hack Via Mailed USB
Six weeks after hackers revealed vulnerabilities in a 2014 Jeep Cherokee that they could use to take over its transmission and brakes,...
-

 105Data Security
105Data SecurityNew Android Ransomware Communicates over XMPP
A new strain of Android ransomware disguised as a video player app uses a means of communication unseen in other similar malware....
-

 117Malware
117MalwareNew Versions of Carbanak Banking Malware Seen Hitting Targets in U.S. and Europe
New variants of the notorious Carbanak Trojan have surfaced in Europe and the United States, and researchers say that the malware now has...
-

 347News
347NewsWatch out for Paedophiles, 9 Internet Connected Baby Cams Can Be Hacked
If you are using baby monitors, you need to be careful as the security researchers have discovered critical security flaws which can...
-

 183How To
183How ToHow To Find Wi-Fi Password From Windows, Linux and Mac OS Using Wifresti
Features: Recover Wifi password on Windows Recover Wifi password on Unix Windows Linux (tested on ubuntu) Mac OS Python 2.7 sudo su...
-
 224Geek
224GeekNew Option in Google Docs Allows You to Type with Your Voice
Move over boring typing, now Google docs have an NEW VOICE and it is AWESOME! We need typing no more: delete, space...
-
 230How To
230How ToSentry – Prevents Brute Force Attacks Against SSH, FTP, SMTP and More
Supporting OS (operating system) FreeBSD Mac OS X Linux (CentOS, Debain, Ubuntu) Download Command: bash || sh export SENTRY_URL=https://raw.githubusercontent.com/msimerson/sentry/master/sentry.pl curl -O $SENTRY_URL...
-
 343Geek
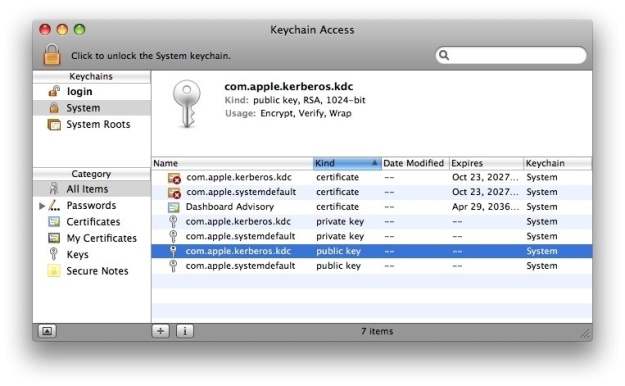
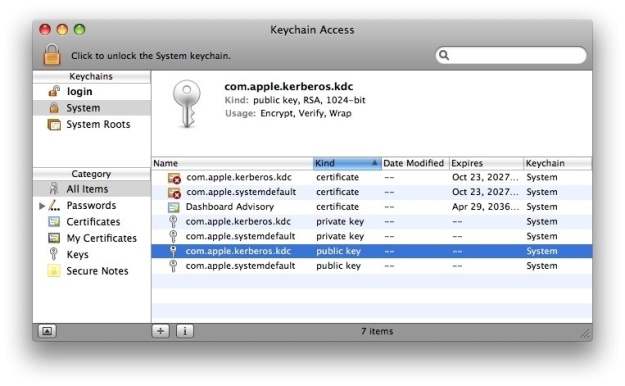
343GeekGenieo Adware Installer Left Mac OS X Keychain Vulnerable
Security researchers have found out that the latest version of the ever-popular Genieo installer adware has fetched a new system to access...
-

 306News
306NewsHacker Puts Crude Poem on Hacked Electronic Signpost in France
If you see a crude poem on an electronic signpost, it is not the handy work of the municipal authorities rather, it...
-
 236Social Engineering
236Social EngineeringOverview of Social Engineering
“In the context of information security, refers to psychological manipulation of people into performing actions or divulging confidential information.” A type of...
-
 236Geek
236GeekLinux Kernel 4.2 Released With Improved Cryptography
Short Bytes: Earlier this week, Linux Kernel 4.2 was released. The new kernel improves cryptographic features with new random number generator and...
-

 177Hacked
177Hacked26 Top Smartphone Models Come With Pre-installed Spyware
Short Bytes: According to a new and surprising report by the security firm G Data, 26 top Android smartphone models come with...
-
 195Geek
195GeekGoogle, Netflix, Microsoft, Mozilla, Amazon Join Forces To Kill Flash
Seven of the most prominent Internet and tech firms unite to build a next generation of royalty-free video codec in an attempt...
-

 84Malware
84MalwareVMworld: When IT grows up
Virtualization aims to totally change how we think of IT altogether. Against the backdrop of VMworld, we take a closer look at...
-

 182Data Security
182Data SecuritySony Pictures reaches settlement with ex-employees over hacking
The hack revealed the inner workings of the studio, as well as the personal information of more than 47,000 celebrities, freelancers, and...
-
 208Vulnerabilities
208VulnerabilitiesAttackers Can Steal Passwords from the Mac Keychain via Email or SMS
It didn’t even take a day for security researchers to find a serious way of exploiting the mechanism through which user clicks...
-
 288Malware
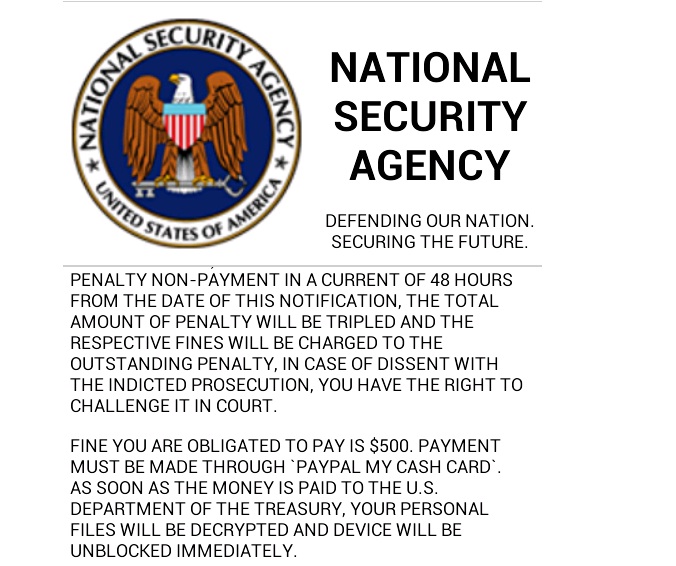
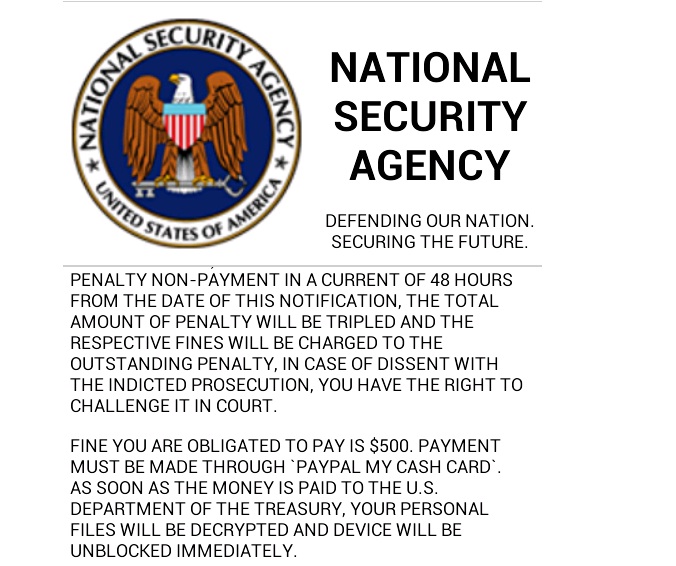
288MalwareRISK ASSESSMENT / SECURITY & HACKTIVISM Android ransomware uses XMPP chat to call home, claims it’s from NSA
A new variant of mobile ransomware that encrypts the content of Android smartphones is putting a new spin on both how it...
The Latest
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Cyber Attack
Cyber AttackMicrosoft Patches 61 Flaws, Including Two Actively Exploited Zero-Days
-
 Cyber Attack
Cyber AttackThe 2024 Browser Security Report Uncovers How Every Web Session Could be a Security Minefield
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Data Breach
Data BreachBlack Basta Ransomware Strikes 500+ Entities Across North America, Europe, and Australia
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Data Breach
Data BreachA SaaS Security Challenge: Getting Permissions All in One Place
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment




