Geek News
Popular Posts
-
 5.2KCyber Attack
5.2KCyber AttackU.S. Sanctions 6 Iranian Officials for Critical Infrastructure Cyber Attacks
The U.S. Treasury Department’s Office of Foreign Assets Control (OFAC) announced sanctions against six...
-
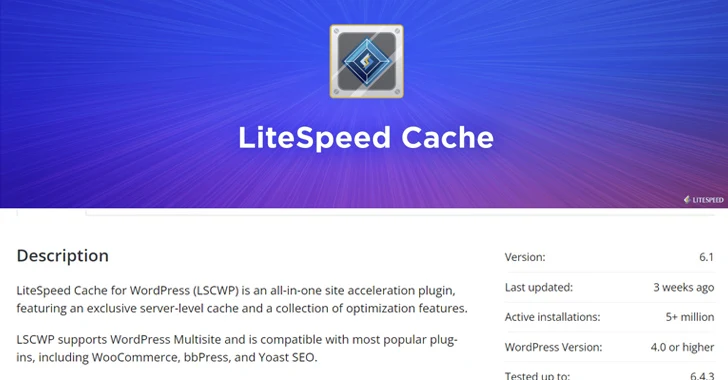
 5.1KVulnerabilities
5.1KVulnerabilitiesWordPress LiteSpeed Plugin Vulnerability Puts 5 Million Sites at Risk
A security vulnerability has been disclosed in the LiteSpeed Cache plugin for WordPress that...
-

 5.1KCyber Attack
5.1KCyber AttackAfter FBI Takedown, KV-Botnet Operators Shift Tactics in Attempt to Bounce Back
The threat actors behind the KV-botnet made “behavioral changes” to the malicious network as...
-

 5.1KVulnerabilities
5.1KVulnerabilitiesMalicious Code in XZ Utils for Linux Systems Enables Remote Code Execution
The malicious code inserted into the open-source library XZ Utils, a widely used package...
-

 5.0KVulnerabilities
5.0KVulnerabilitiesIntel and Lenovo BMCs Contain Unpatched Lighttpd Server Flaw
A security flaw impacting the Lighttpd web server used in baseboard management controllers (BMCs)...
-

 3.4KCyber Attack
3.4KCyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
Polish government institutions have been targeted as part of a large-scale malware campaign orchestrated by a Russia-linked nation-state actor called APT28. “The...
-

 3.6KMalware
3.6KMalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
The U.K. National Crime Agency (NCA) has unmasked the administrator and developer of the LockBit ransomware operation, revealing it to be a...
-

 4.3KMalware
4.3KMalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
The Iranian state-backed hacking outfit called APT42 is making use of enhanced social engineering schemes to infiltrate target networks and cloud environments....
-

 3.0KVulnerabilities
3.0KVulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
The MITRE Corporation has offered more details into the recently disclosed cyber attack, stating that the first evidence of the intrusion now...
-

 4.1KData Breach
4.1KData BreachNew Case Study: The Malicious Comment
How safe is your comments section? Discover how a seemingly innocent ‘thank you’ comment on a product page concealed a malicious vulnerability,...
-

 1.5KMalware
1.5KMalwareChina-Linked Hackers Suspected in ArcaneDoor Cyberattacks Targeting Network Devices
The recently uncovered cyber espionage campaign targeting perimeter network devices from several vendors, including Cisco, may have been the work of China-linked...
-

 4.6KMalware
4.6KMalwareNew ‘Cuckoo’ Persistent macOS Spyware Targeting Intel and Arm Macs
Cybersecurity researchers have discovered a new information stealer targeting Apple macOS systems that’s designed to set up persistence on the infected hosts...
-

 2.5KCyber Attack
2.5KCyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
Czechia and Germany on Friday revealed that they were the target of a long-term cyber espionage campaign conducted by the Russia-linked nation-state...
-

 3.5KMalware
3.5KMalwareHackers Increasingly Abusing Microsoft Graph API for Stealthy Malware Communications
Threat actors have been increasingly weaponizing Microsoft Graph API for malicious purposes with the aim of evading detection. This is done to...
-

 4.8KMalware
4.8KMalwareNSA, FBI Alert on N. Korean Hackers Spoofing Emails from Trusted Sources
The U.S. government on Thursday published a new cybersecurity advisory warning of North Korean threat actors’ attempts to send emails in a...
-

 3.0KVulnerabilities
3.0KVulnerabilitiesFour Critical Vulnerabilities Expose HPE Aruba Devices to RCE Attacks
HPE Aruba Networking (formerly Aruba Networks) has released security updates to address critical flaws impacting ArubaOS that could result in remote code...
-

 770Data Breach
770Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
Several popular Android applications available in Google Play Store are susceptible to a path traversal-affiliated vulnerability codenamed the Dirty Stream attack that...
-

 615Vulnerabilities
615VulnerabilitiesWhen is One Vulnerability Scanner Not Enough?
Like antivirus software, vulnerability scans rely on a database of known weaknesses. That’s why websites like VirusTotal exist, to give cyber practitioners...
-

 3.6KData Breach
3.6KData BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
Cloud storage services provider Dropbox on Wednesday disclosed that Dropbox Sign (formerly HelloSign) was breached by unidentified threat actors, who accessed emails,...
-

 3.3KVulnerabilities
3.3KVulnerabilitiesNew “Goldoon” Botnet Targets D-Link Routers With Decade-Old Flaw
A never-before-seen botnet called Goldoon has been observed targeting D-Link routers with a nearly decade-old critical security flaw with the goal of...
-

 797Data Breach
797Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has added a critical flaw impacting GitLab to its Known Exploited Vulnerabilities (KEV) catalog,...
-

 2.4KData Breach
2.4KData BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
A new malware called Cuttlefish is targeting small office and home office (SOHO) routers with the goal of stealthily monitoring all traffic...
-

 4.9KCyber Attack
4.9KCyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
Cybersecurity researchers have discovered a previously undocumented malware targeting Android devices that uses compromised WordPress sites as relays for its actual command-and-control...
-

 2.8KData Breach
2.8KData BreachHow to Make Your Employees Your First Line of Cyber Defense
There’s a natural human desire to avoid threatening scenarios. The irony, of course, is if you hope to attain any semblance of...
-

 2.5KMalware
2.5KMalwareZLoader Malware Evolves with Anti-Analysis Trick from Zeus Banking Trojan
The authors behind the resurfaced ZLoader malware have added a feature that was originally present in the Zeus banking trojan that it’s...
The Latest
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment
-
 Malware
MalwareChina-Linked Hackers Suspected in ArcaneDoor Cyberattacks Targeting Network Devices
-
 Malware
MalwareNew ‘Cuckoo’ Persistent macOS Spyware Targeting Intel and Arm Macs
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Malware
MalwareHackers Increasingly Abusing Microsoft Graph API for Stealthy Malware Communications
-
 Malware
MalwareNSA, FBI Alert on N. Korean Hackers Spoofing Emails from Trusted Sources
-
 Vulnerabilities
VulnerabilitiesFour Critical Vulnerabilities Expose HPE Aruba Devices to RCE Attacks
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Vulnerabilities
VulnerabilitiesWhen is One Vulnerability Scanner Not Enough?
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Vulnerabilities
VulnerabilitiesNew “Goldoon” Botnet Targets D-Link Routers With Decade-Old Flaw
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Data Breach
Data BreachHow to Make Your Employees Your First Line of Cyber Defense
-
 Malware
MalwareZLoader Malware Evolves with Anti-Analysis Trick from Zeus Banking Trojan