Featured News
-

 309Geek
309GeekLinux Foundation Giving Free Chromebooks to Students Enrolling in Their Training Program
Short Bytes: The Linux Foundation is giving away one free Chromebook to those who will enroll in its one-month training courses. This...
-

 177Vulnerabilities
177VulnerabilitiesNetflix Sleepy Puppy Awakens XSS Vulnerabilities in Secondary Applications
Most automated scanning and security tools that ferret out cross-site scripting vulnerabilities don’t do much analysis beyond the target application. Netflix this...
-

 188Incidents
188Incidents9 baby monitors wide open to hacks that expose users’ most private moments
Despite its ubiquity, Internet of Things security still isn’t ready for prime time. The security of Internet-connected baby monitors got a failing...
-
 198Geek
198GeekNew Tool Reveals Your Personality Through Facebook ‘Likes’
This tool has been developed by the University of Cambridge and uses Facebook Likes data to estimate a person’s key psychological traits,...
-

 170Cyber Events
170Cyber EventsAnonymous Offshoot GhostSec Launches Another Phase of Attacks Against ISIS
Another phase of an online battle against the members of the so-called Islamic State (IS, previously ISIS/ISIL) group has been launched throughout the world by...
-
 354How To
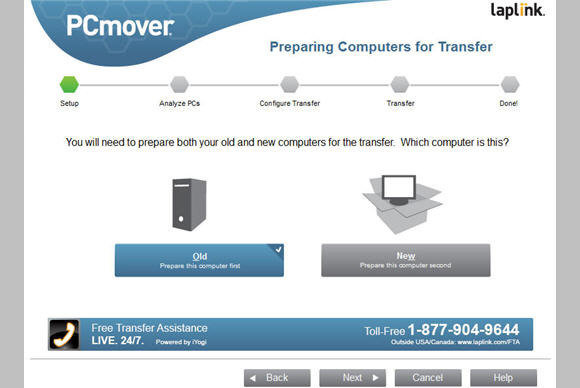
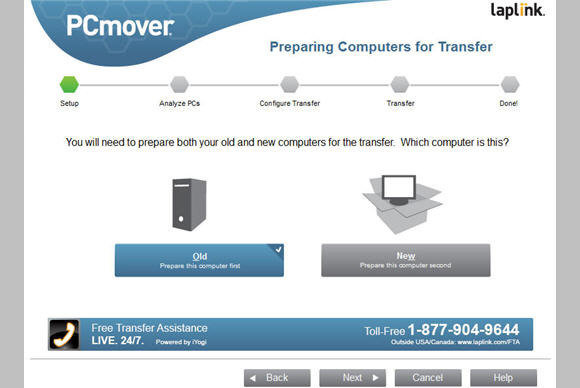
354How ToFree App from Microsoft to Move Your Files from Windows 7 to Windows 10
Microsoft partners with Laplink Software, Inc. to provide free download of Laplink’s file transfer software PCmover. According to Thomas Kool, Laplink’s CEO...
-

 303Cyber Events
303Cyber EventsLizard Squad Shuts Down British National Crime Agency Site
The United Kingdom’s National Crime Agency (NCA) website was taken down by the cyber-attackers using Distributed Denial of Service (DDoS) attack, apparently...
-

 143Geek
143GeekDetails No One Should Keep on Facebook
If you are using Facebook, there is certain information which should never be used whatsoever. The primary reason behind using Facebook is to...
-
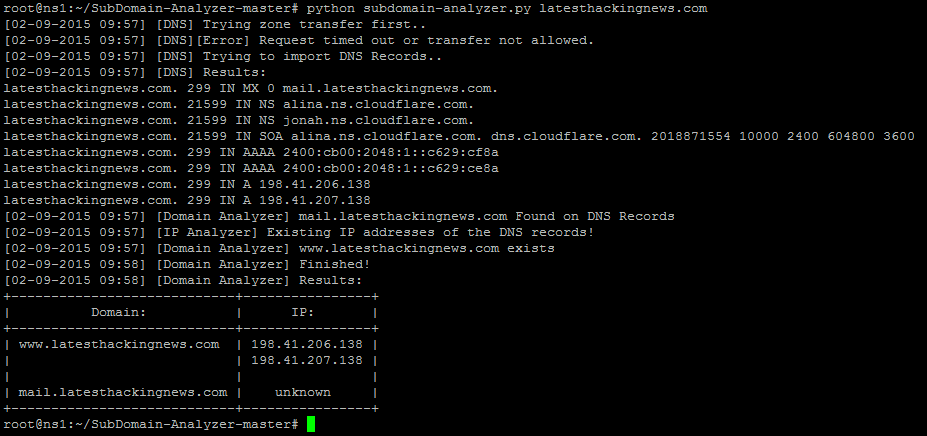
 263How To
263How ToHow To View The Details of A Domain With SubDomain Analyzer
From the following steps SubDomain-Analyzer gets data from a domain: Get the zone transfer file Gathers all the information from DNS records...
-

 527Privacy
527Privacy10 steps to staying secure on public Wi‑Fi
The convenience of public Wi-Fi for many people is invaluable, yet there are risks. With all this in mind, here are 10...
-
 177Malware
177MalwareCreate your own Ransomware – Open source Ransomware malware
Ransomware, the biggest pain that is causing many PC and laptop completely encrypted. If you don’t have money or brains, you cannot...
-

 198Incidents
198IncidentsMillions hit by personal data hack still have not been told
The U.S. government has not yet notified any of the 21.5 million federal employees and contractors whose security clearance data was hacked...
-

 337Cyber Crime
337Cyber CrimeFormer US Federal Agent Pleads Guilty To $820,000 Bitcoin Laundering
Earlier today, a former United States secret service agent pleaded guilty for the theft of over $820,000 worth of digital currency, Bitcoin,...
-

 95Malware
95MalwareVMworld: VM acceleration – how do we get there?
If you have a ton of VMs sprawling the globe, how do you make them all fast? That’s the subject floating around...
-

 159Vulnerabilities
159VulnerabilitiesPayPal XSS Vulnerability Found, Fixed Before Being Exploited
A stored XSS vulnerability was identified and reported by Bitdefender’s staff to PayPal, one that could have been easily used by hackers...
-

 168Vulnerabilities
168VulnerabilitiesUPnP Trouble Puts Devices Behind Firewall at Risk
Security vulnerabilities in UPnP continue to crop up and continue to put millions of home networking devices at risk for compromise. The...
-

 107Malware
107MalwareHidden password-stealing malware lurking in your GPU card? Intel Security thinks not
Fears that malware is hiding in people’s graphics chipsets may be overclocked, according to Intel Security. Earlier this year, researchers from the...
-
 185Data Security
185Data SecurityCoreBot Can Steal Your Credentials, Download and Execute Malware
CoreBot is a new malware that steals user credentials and have the ability to cause a great amount of trouble. This stealer...
-

 364News
364NewsOfficials Claim China, Russia Scanning Hacked Data to Haunt U.S. Spies
The officials are claiming that foreign spy agencies such as those from China and Russia are verifying hacked databases in order to...
-

 346Cyber Crime
346Cyber CrimeHamza Bendelladj, Co-Creator of SpyEye Trojan NOT Sentenced To Death
Update: Creators of SpyEye Trojan Aleksandr Panin, Hamza Bendelladj Sentenced Even though several social media platforms are claiming that Hamza Bendelladj has been...
The Latest
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Cyber Attack
Cyber AttackMicrosoft Patches 61 Flaws, Including Two Actively Exploited Zero-Days
-
 Cyber Attack
Cyber AttackThe 2024 Browser Security Report Uncovers How Every Web Session Could be a Security Minefield
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Data Breach
Data BreachBlack Basta Ransomware Strikes 500+ Entities Across North America, Europe, and Australia
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Data Breach
Data BreachA SaaS Security Challenge: Getting Permissions All in One Place
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment




