Featured News
-
 121Opinion
121OpinionAn Ashley Madison response plan: does your company have one?
The Ashley Madison data breach has created fresh cybersecurity threats for all organizations. A company response plan is needed. Here's what you...
-

 401News
401NewsPolice Captain Suicides After His Email Was Leaked in Ashley Madison Hack
A former police captain of the City of San Antonio police department committed suicide after his official email address was found amid...
-

 3.4KCyber Crime
3.4KCyber CrimeA big day for consumers: Companies answerable for poor cybersecurity
FTC has the authority to hold organisations to account for failing to deliver tough cybersecurity measures.
-

 111Cyber Crime
111Cyber CrimeChina Caught Spying on Tibetan Activists and Neighbouring Countries
China has been a usual suspect behind the cyber attacks carried out worldwide — From U.S. to India, everyone blames the red...
-
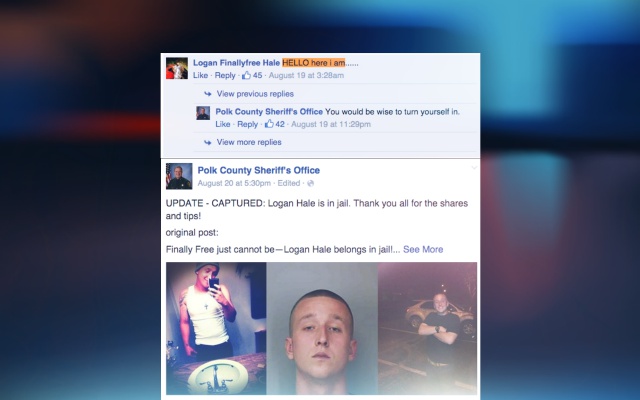
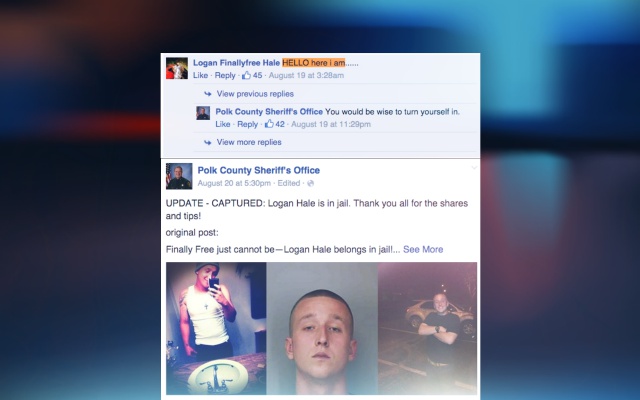 188Geek
188GeekWanted Florida Man Taunts Police on their Facebook Page, Gets Arrested
Florida man who is on the top of the wanted list was found making fun of the cops that also on their...
-

 356Cyber Crime
356Cyber CrimeBBB CEO Falls for Dropbox Phishing Scam, Sends Out Malware Emails
In May 2015, we reported an alert to be careful of a Dropbox phishing scam, but it seems not everyone takes such scams...
-
 367Geek
367GeekMicrosoft Releases Updates To Spy On Windows 7, 8 and 8.1 Users
Back at the beginning of this month, we reported that how Microsoft has planned to spy on its users by releasing their...
-

 241Kids Online
241Kids OnlineMake password into a story and more parental hacks
It’s important to ensure your child's data and devices are secure at school and at home. Check out our to back to...
-
 323Privacy
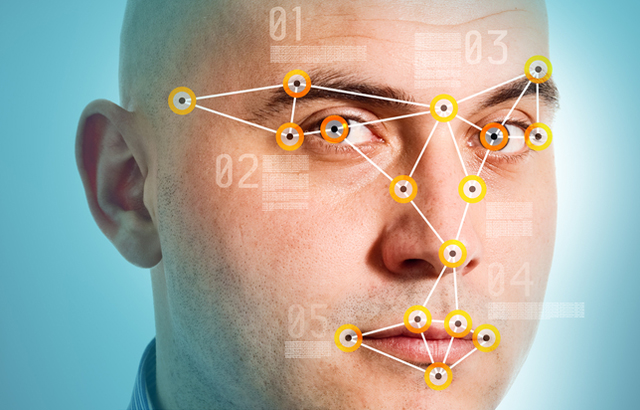
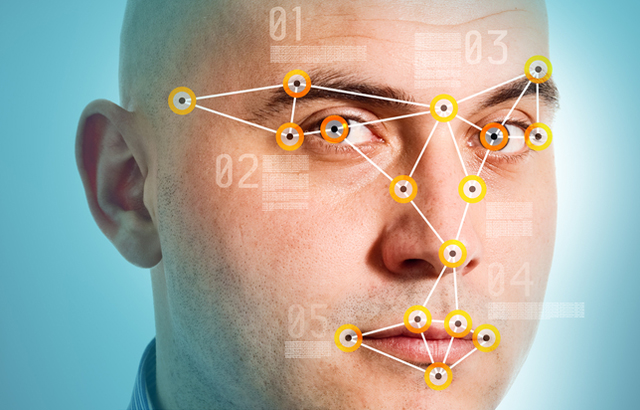
323PrivacyHow does facial recognition technology work?
In this hi-tech age, your face is increasingly becoming a digital ID for authenticating who you are online. We look at how...
-
 266Hacking Tutorials
266Hacking TutorialsReset Windows Password with Kali
Sometimes we forget our password, or even we want to reset the password of the windows OS of our friends, officemate or...
-

 322News
322NewsRoyal Saudi Air Force Website Hacked By Iranian Hackers
An Iranian hacker from Iran Hack Security Team hacked and defaced the official website of Royal Saudi Air Force this Friday morning. Though the...
-
 315Cyber Crime
315Cyber CrimeUniversity of Michigan Employees Trapped by Google Phishing Email
Around 150 University of Michigan employees lost sensitive information thanks to scammed emails, informs the university’s Division of Public Safety and Security....
-

 196Cyber Crime
196Cyber CrimeNew Amazon Phishing Scam Steals Credit Card Details
An email is being sent to users having the subject line ‘New Security feature’ and its sender appears to be Amazon. In...
-
 386How To
386How ToHere’s How to Use Microsoft Edge Without Installing Windows 10
Short Bytes: If you want to test Microsoft Edge without installing Windows 10 on your computer, here’s a good news for you....
-

 154Geek
154GeekWindows 10 Should be banned for Spying on Users – Demands Russia
After the release of Windows 10, we reported how the operating system spies on its users and how to disable selected features...
-

 425Geek
425GeekProtonMail is Now Open Source, iOS, Android Apps Unveiled
The world’s securest Switzerland based emailing service provider ProtonMail goes open source with the public release of their webmail interface version 2.0....
-

 418Hacked
418HackedRussians Demand Windows 10 Ban Because it “Spies on Users”
Short Bytes: Russian lawyers, lawmakers and state agencies have filed complaints seeking Windows 10 ban. They have claimed that Windows 10 OS...
-

 297Geek
297Geek4GB, 8GB Or 16GB; How Much RAM Do You Need?
Short Bytes: How much you should RAM: 4 GB, 8 GB or 16 GB? It’s one tricky choice that every computer buyer,...
-

 376Google Dorks
376Google DorksGoogle Dorks – Google Hacking
Google search engine find answer to our question which is helpful in our daily lives, search about our school assignments, reports, presentation and...
-

 350News
350NewsUK Based Recruitment Portal Suffers Massive Data Breach
A Saudi hacker going with the online handle of JM511 has breached into the server of a UK-based international network of independent...
The Latest
-
 Cyber Attack
Cyber AttackCheck Point Warns of Zero-Day Attacks on its VPN Gateway Products
-
 Data Breach
Data BreachNew Research Warns About Weak Offboarding Management and Insider Risks
-
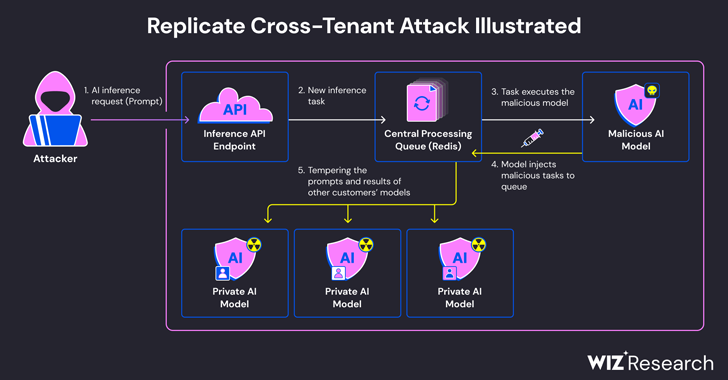 Vulnerabilities
VulnerabilitiesExperts Find Flaw in Replicate AI Service Exposing Customers’ Models and Data
-
 Cyber Attack
Cyber AttackHackers Created Rogue VMs to Evade Detection in Recent MITRE Cyber Attack
-
 Malware
MalwareBeware: These Fake Antivirus Sites Spreading Android and Windows Malware
-
 Vulnerabilities
VulnerabilitiesUpdate Chrome Browser Now: 4th Zero-Day Exploit Discovered in May 2024
-
 Malware
MalwareJAVS Courtroom Recording Software Backdoored – Deploys RustDoor Malware
-
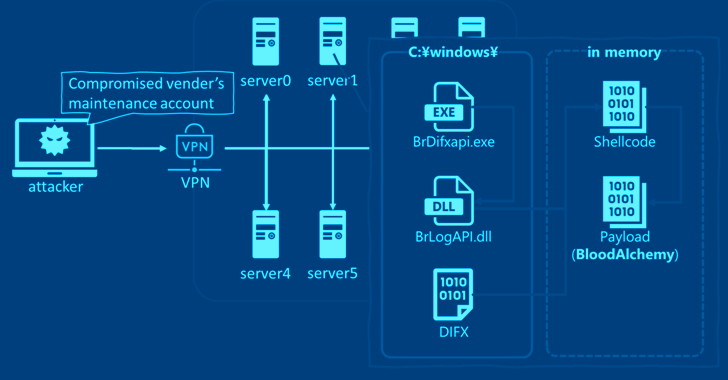 Malware
MalwareStealthy BLOODALCHEMY Malware Targeting ASEAN Government Networks
-
 Vulnerabilities
VulnerabilitiesCISA Warns of Actively Exploited Apache Flink Security Vulnerability
-
 Malware
MalwareNew Frontiers, Old Tactics: Chinese Espionage Group Targets Africa & Caribbean Govts
-
 Malware
MalwareInside Operation Diplomatic Specter: Chinese APT Group’s Stealthy Tactics Exposed
-
 Data Breach
Data BreachAre Your SaaS Backups as Secure as Your Production Data?
-
 Vulnerabilities
VulnerabilitiesIvanti Patches Critical Remote Code Execution Flaws in Endpoint Manager
-
 Malware
MalwareResearchers Warn of Chinese-Aligned Hackers Targeting South China Sea Countries
-
 Vulnerabilities
VulnerabilitiesRockwell Advises Disconnecting Internet-Facing ICS Devices Amid Cyber Threats
-
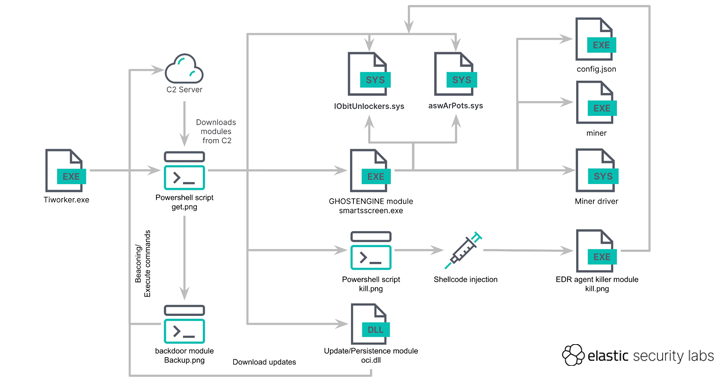 Malware
MalwareGHOSTENGINE Exploits Vulnerable Drivers to Disable EDRs in Cryptojacking Attack
-
 Data Breach
Data BreachMS Exchange Server Flaws Exploited to Deploy Keylogger in Targeted Attacks
-
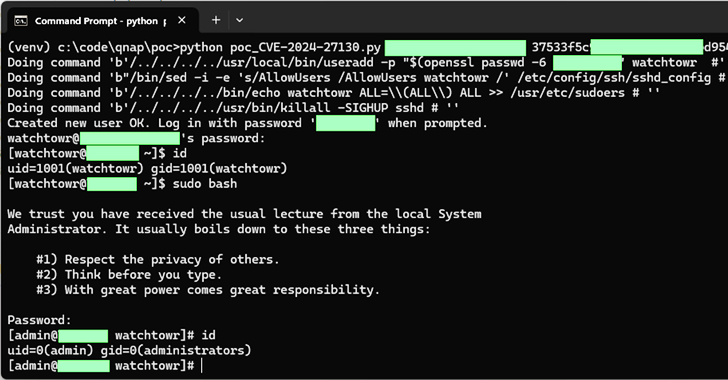 Vulnerabilities
VulnerabilitiesQNAP Patches New Flaws in QTS and QuTS hero Impacting NAS Appliances
-
 Vulnerabilities
VulnerabilitiesCritical Veeam Backup Enterprise Manager Flaw Allows Authentication Bypass
-
 Vulnerabilities
VulnerabilitiesCritical GitHub Enterprise Server Flaw Allows Authentication Bypass




