Featured News
-

 317News
317NewsDonald Trump’s Website Hacked with Jon Stewart Tribute
Donald Trump organization’s official website Trump.com was attacked by hackers yesterday and a message was posted in which Jon Stewart was praised...
-

 293News
293NewsFirmware Worm Permanently Infects Macs in Seconds
It has been a common understanding that Apple devices are well-protected and less vulnerable. It is also believed that Apple computers are...
-

 140Privacy
140PrivacyHacker sends woman pictures of herself from her own webcam
Hacker sends woman images of herself and her boyfriend, which were captured through their own webcam.
-
 255Lists
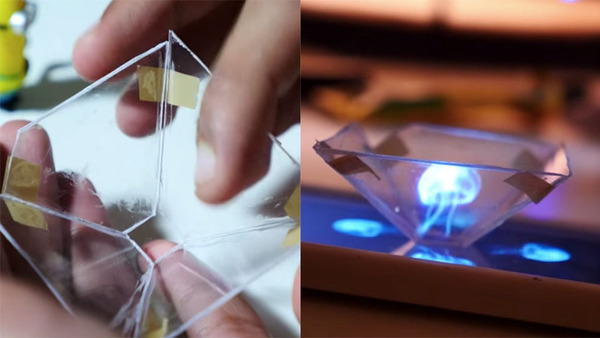
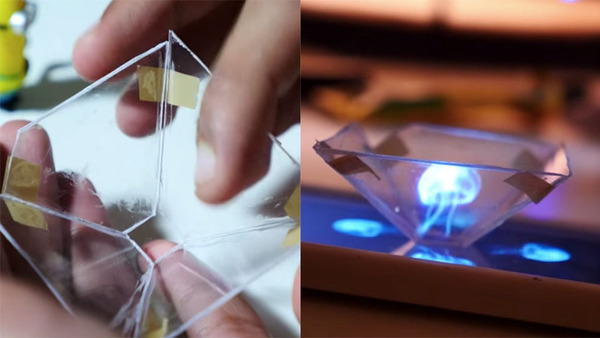
255ListsHow To Make 3D Hologram At Home By the Easiest Method
Short Bytes : Using some stationary items and glass/plastic sheet, you can make 3D hologram at home. Place a pyramidal frustum over...
-

 494Hacked
494HackedExistence of ECHELON Confirmed, Top-Secret NSA Program for Spying on You
A radome at RAF Menwith Hill, a site with satellite uplink capabilities believed to be used by ECHELON (Wikipedia) Short Bytes :...
-
 168Hacked
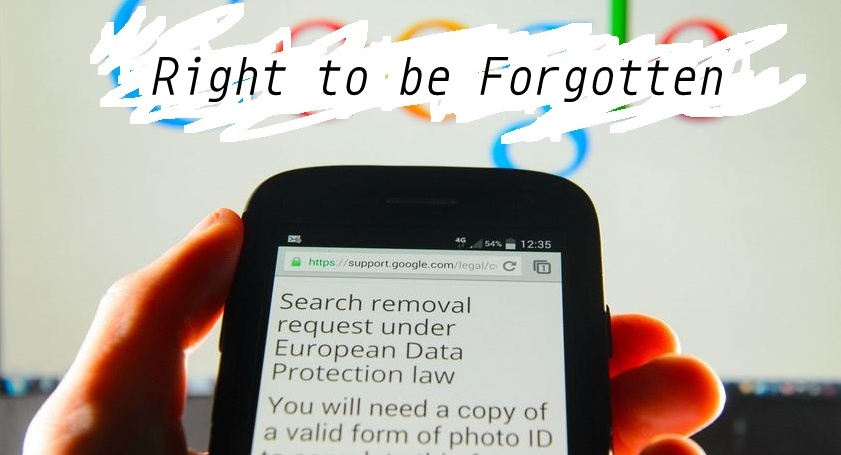
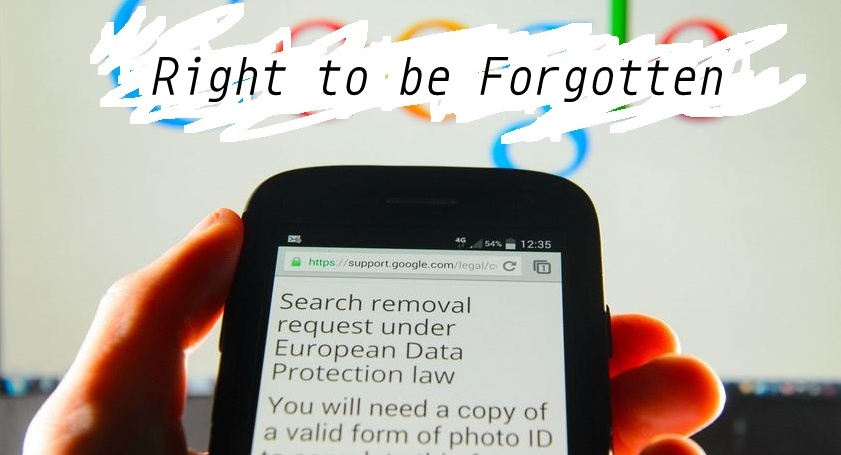
168HackedGoogle: NO Need of Global ‘Right To Be Forgotten’
Short Bytes : Google has written in a new blog post that it won’t be complying with the new French order to...
-

 247Hacked
247HackedThousands of Apps Will Crash When Android M Goes Live, Here’s Why
Short Bytes: A flaw has been reported in thousands of Android apps that will crash them when Android M goes live. The...
-
 307Geek
307GeekHackers Sending Fake Windows 10 Upgrade Ransomware Email, Encrypts Every File
It has not been a week, yet hackers have begun to exploit existing Windows users’ computer by sending them a ransomware, via...
-

 124Data Security
124Data SecurityWindows 10 Uses Your Bandwidth to Send Updates to Other Users
We all are aware that Microsoft has recently released the latest version of Windows i.e. Windows 10 which is available as a...
-

 348News
348NewsAnti-ISIS Kurdish Hacker Targets Etowah County Sheriff’s Office Website
MuhmadEmad, a Kurdish hacker known for his anti-ISIS views is back in news and this time with yet another high-profile hack —...
-
 205Geek
205GeekIBM Open Sources 50 Projects, Launches developerWorks Open
Short Bytes: Technology pioneer IBM has open sourced 50 tools and apps. These tools cover a large interest area varying from Cloud, Analytics, IoT,...
-
 267How To
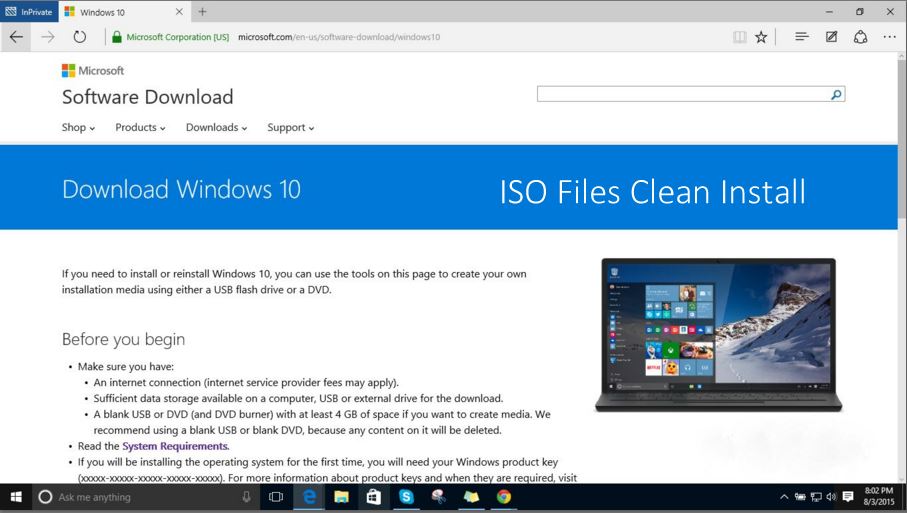
267How ToDon’t Perform Clean Install of Windows 10 WITHOUT Upgrading First
Short Bytes: I’m writing this article to warn the users who are trying to perform clean install of Windows 10 on their...
-
 278Hacked
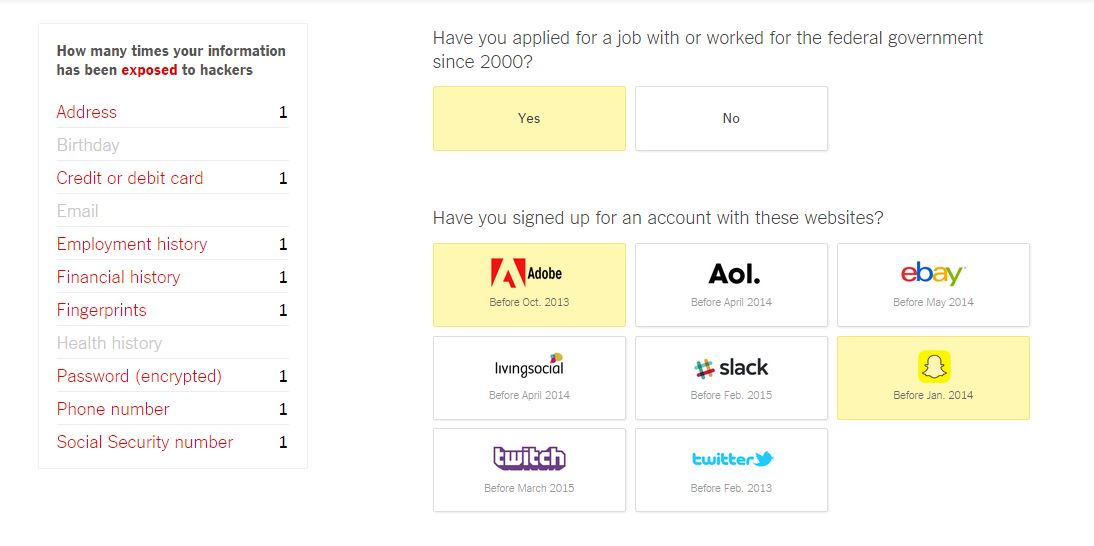
278HackedHow Many Times Has Your Data Been Exposed to Hackers? Take The Quiz And Know
Short Bytes: The New York Times has come up with a quiz that will tell you if your personal information has been...
-
 387How To
387How ToHow to Downgrade Windows 10 to Windows 7 or 8.1 in Simple Steps
Short Bytes: What if you don’t like Windows 10? There are simple ways to downgrade from Windows 10 to Windows 7 or...
-

 203Cyber Events
203Cyber EventsAnonymous Brings Down Taiwan Government Websites
The online hacktivist Anonymous has shut down Taiwan government websites and has termed the act as “just the beginning” of a series...
-

 190Cyber Crime
190Cyber CrimeIndiana’s AG launches investigation into major data breach
Indiana's Attorney General has launched an investigation into a data breach at Medical Informatics Engineering, which has affected up to 4 million...
-
 105Opinion
105OpinionBlack Hat 2015: What to watch out for, besides cars and guns
It's not all about crashing cars and hacking guns: what's hot at Black Hat 2015 USA (#BHUSA) and how to get the...
-

 82Malware
82MalwareThe world’s biggest bug bounty payouts
From finding flaws to suggesting innovative security measures for the future, we look at some of the biggest bug bounty payouts in...
-
 333How To
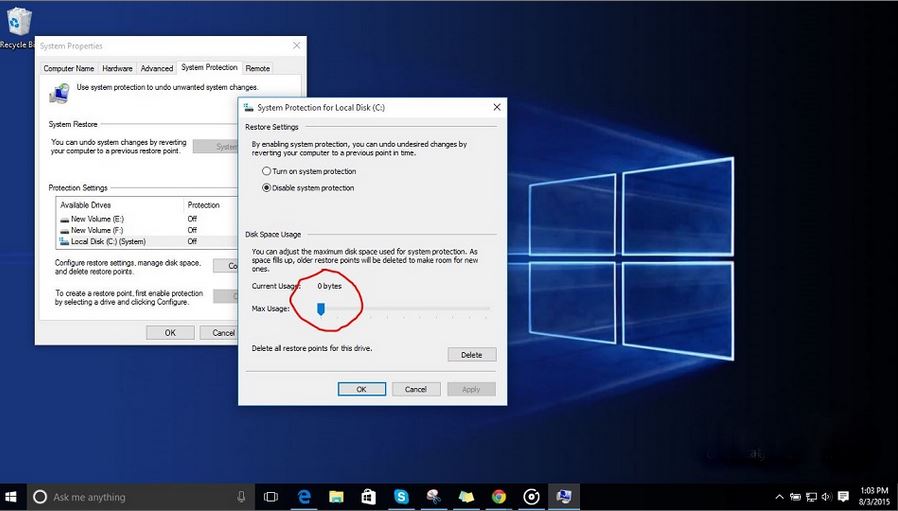
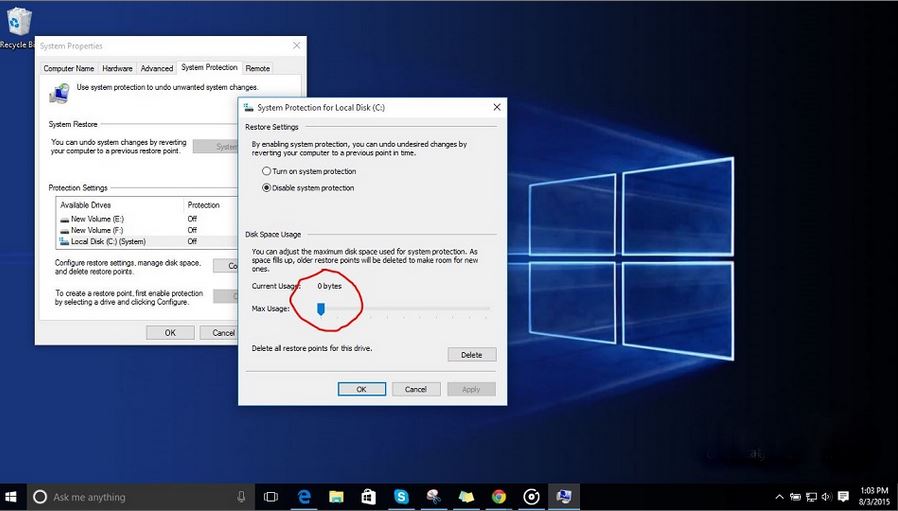
333How ToHow to Turn On System Restore in Windows 10 to Protect Against Bad Windows Updates
Short Bytes : The important feature of System Restore in Windows 10 is disabled by default. This feature protects your PC from the...
-
 259Data Security
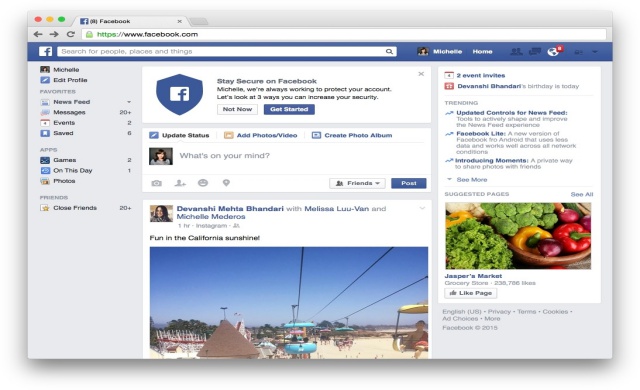
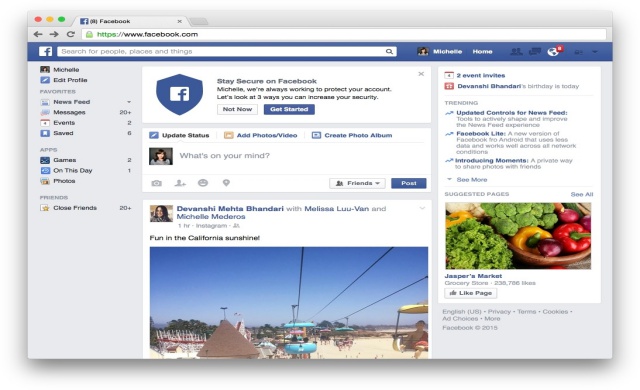
259Data SecurityFacebook’s New Security Checkup Tool To Protect User Accounts
Facebook has officially launched the new Security Checkup feature that was being tested on a narrow user-base for a few months. Facebook...
The Latest
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Cyber Attack
Cyber AttackMicrosoft Patches 61 Flaws, Including Two Actively Exploited Zero-Days
-
 Cyber Attack
Cyber AttackThe 2024 Browser Security Report Uncovers How Every Web Session Could be a Security Minefield
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Data Breach
Data BreachBlack Basta Ransomware Strikes 500+ Entities Across North America, Europe, and Australia
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Data Breach
Data BreachA SaaS Security Challenge: Getting Permissions All in One Place
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment




