Featured News
-
 255How To
255How ToHow to Build Weather Satellite Images Receiver With $20 Dongle
This “how-to build weather satellite images reciever” is based upon Matt Gray’s project on receiving weather satellite image with £8 dongle. Matt Gray is...
-

 276Hacked
276HackedGoogle Tells You How To Stay Safe Online
When most of your Facebook timeline is flooded with news like cyber threats and security, how cyber criminals steal your money, and...
-

 276Surveillance
276SurveillanceHORNET – Faster and Secure Anonymity Network Than Tor
Most of you must have heard about Tor, which is one of the renowned network based on onion router, delivers a good...
-

 182Hacked
182Hacked500 Million Devices at Risk Due to Leaked “Easy to Use” RCSAndroid Malware
The massive data breach at the Hacking Team has resulted in tons of revelations regarding different kinds of spyware and the potential security...
-

 285Surveillance
285SurveillancePakistan’s ISI Plans to Tap International Undersea Cables, Rivals the NSA, GCHQ
The most powerful intelligence and spy agency of Pakistan, specifically Inter-Services Intelligence (ISI), has now planned to tap all the Internet traffic...
-
 314Hacked
314HackedMovie Studios Repeatedly Report Their Own 127.0.0.1 Localhost for Piracy
The torrent pirates that keep hurting the million-dollar movie studios by uploading the data using their torrent clients are their biggest enemies...
-

 265News
265NewsGoogle, Microsoft, Kaspersky Labs, NIC For Morocco Domains Hacked
Who says high-profile websites are unhackable? We just witnessed Moroccan hackers taking over websites of tech giants and those claiming to protect...
-
 220Hacked
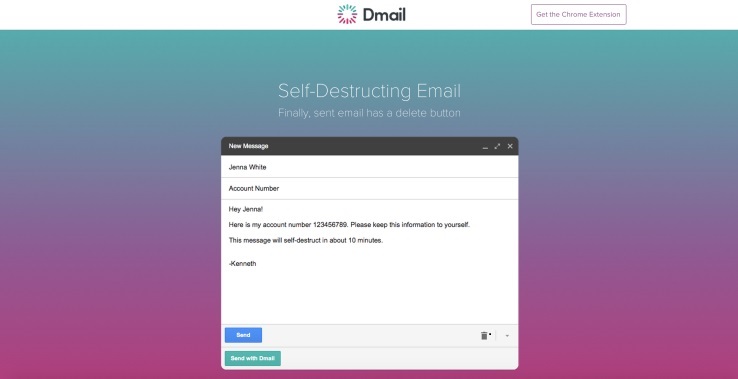
220HackedHow To Self Destruct Email With Dmail
Admit it, you have wanted this for a long time. There must have been instances when you regretted sending an email with...
-

 269Geek
269GeekAnonymous Attacks ISIS Supporters, Spams Twitter Accounts with Anime Pics
The online hacktivist Anonymous has been fighting an online battle against the Islamic State (IS, previously ISIS/ISIL). And now they have just extended their...
-

 483Privacy
483PrivacyResearchers unveil super‑fast anonymity network
A group of six academics have published a paper describing a new high speed anonymity network that could increase the privacy of...
-
 166Geek
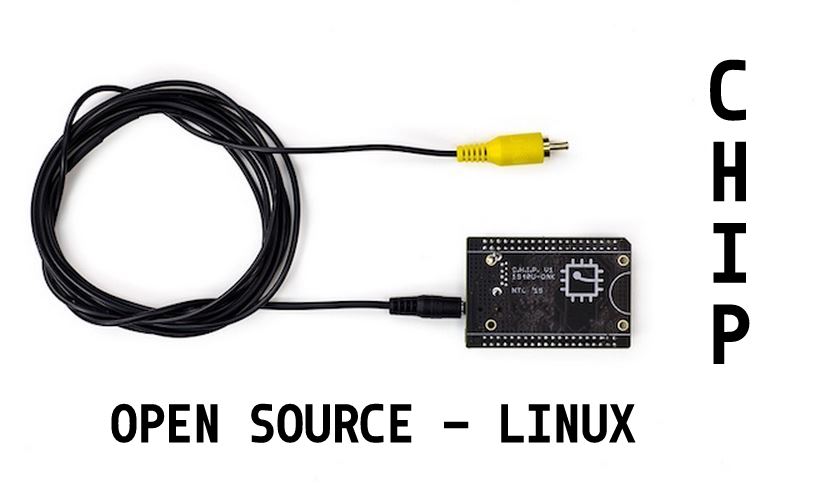
166Geek$9 Computer CHIP Reveals Its Open Source Details, Runs on Linux Kernel
If you are interested in the latest technologies and advancements in computing, you must have read about the $9 computer CHIP. This...
-

 212How To
212How ToHow to Create Your Own Google Deep Dream Nightmares in Seconds
Google’s Deep Dream robot has been creating one hell of a stir in recent weeks and fossBytes isn’t untouched by the same....
-
 329Hacked
329HackedHORNET: Tor-like Anonymity Network With Superfast Speeds
The Deep Web is a place that is hidden from the ordinary world because the browsers used to access the Deep Web, continuously encrypt...
-
 328Operating Systems
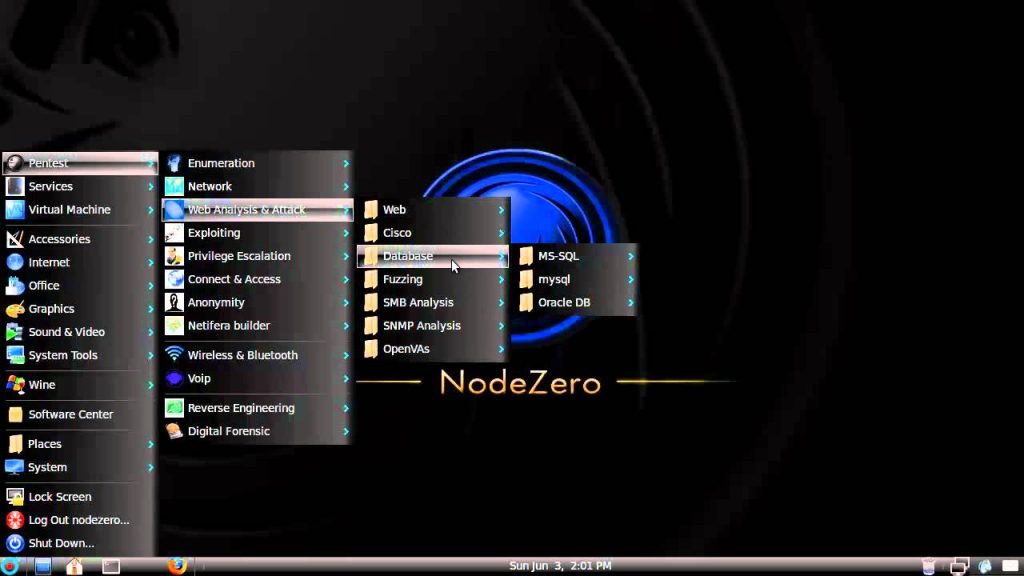
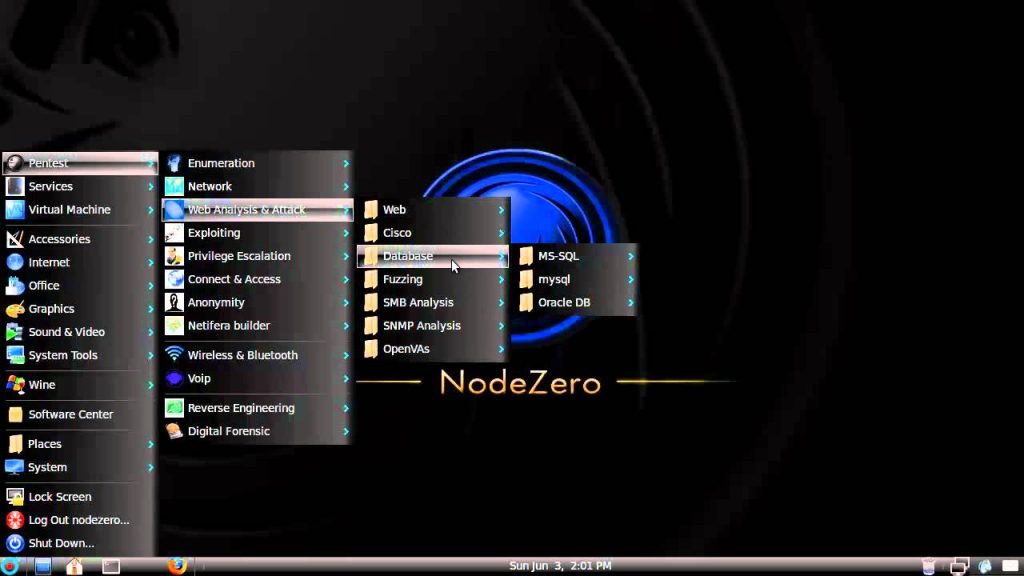
328Operating SystemsNodeZero – Lurking in the shadows of Pentesting
Us penetration testers have of course all heard of BackTrack it’s the most popular penetration testing distro out there but Node Zero...
-
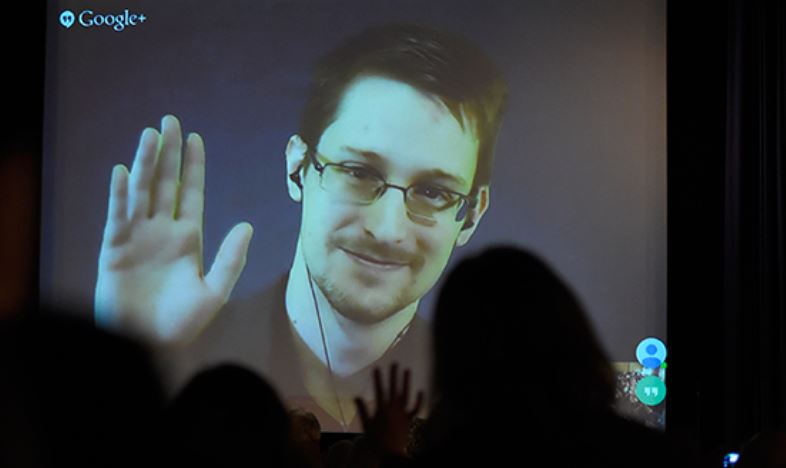
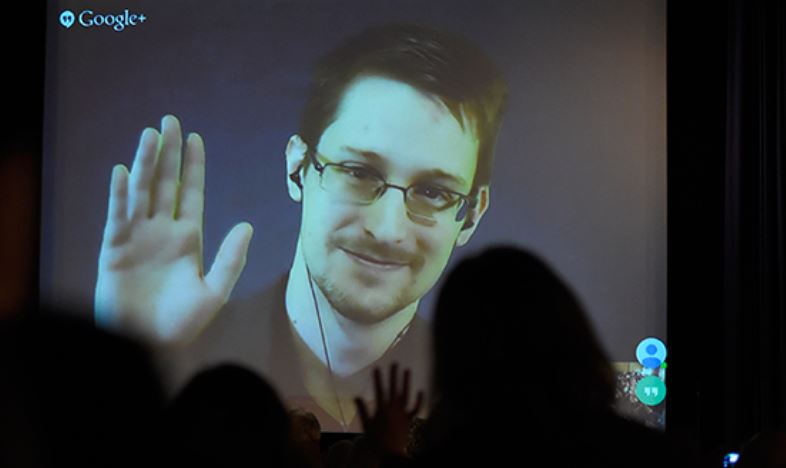 321Hacked
321HackedEdward Snowden Tells How to Build an Internet Focused on Privacy
When someone like Edward Snowden, tells you how to make an internet focused on privacy and user welfare, you listen, and you...
-

 196Cyber Events
196Cyber EventsAnonymous Hacks U.S. Census Bureau, Leaks Officials’ Personal Data Against TPP/TTIP
Remember the Anonymous hackers behind the massive World Trade Center (WTC) leak? Well, he’s back with another breach and this time their...
-

 78Malware
78MalwarePorn clicker keeps infecting apps on Google Play
A recently identified trojan porn clicker is still infecting apps on Google Play.
-
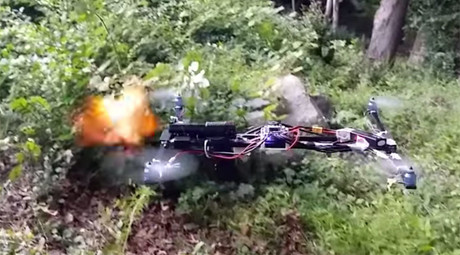
 279Hacked
279HackedGun Firing Drone Appears Legal, FAA Still Investigating
Remember the Drone Gun? The quadcopter hovering in the woods of Clinton, Connecticut and firing rounds of shots and completely legal...
-
 441Scams
441ScamsSupport Scammers and Self‑Justification
Support scammers: old twisters, new twists, and scammer psychology.
-

 308Data Security
308Data SecurityJeep Cherokee On-Board System Hacked, More Than 470,000 Vehicles at Risk
We have heard about hacking websites, computers, planes, and other devices, but hacking a moving car? Well, it happened and it happened live....
The Latest
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Malware
MalwareEternal Malware: CVE-2024-3400 Rootkits Persist Through Palo Alto Firewalls Updates and Resets
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Data Breach
Data BreachNavigating the Threat Landscape: Understanding Exposure Management, Pentesting, Red Teaming and RBVM
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage




