Featured News
-

 489Privacy
489PrivacyResearchers unveil super‑fast anonymity network
A group of six academics have published a paper describing a new high speed anonymity network that could increase the privacy of...
-
 170Geek
170Geek$9 Computer CHIP Reveals Its Open Source Details, Runs on Linux Kernel
If you are interested in the latest technologies and advancements in computing, you must have read about the $9 computer CHIP. This...
-

 215How To
215How ToHow to Create Your Own Google Deep Dream Nightmares in Seconds
Google’s Deep Dream robot has been creating one hell of a stir in recent weeks and fossBytes isn’t untouched by the same....
-
 335Hacked
335HackedHORNET: Tor-like Anonymity Network With Superfast Speeds
The Deep Web is a place that is hidden from the ordinary world because the browsers used to access the Deep Web, continuously encrypt...
-
 335Operating Systems
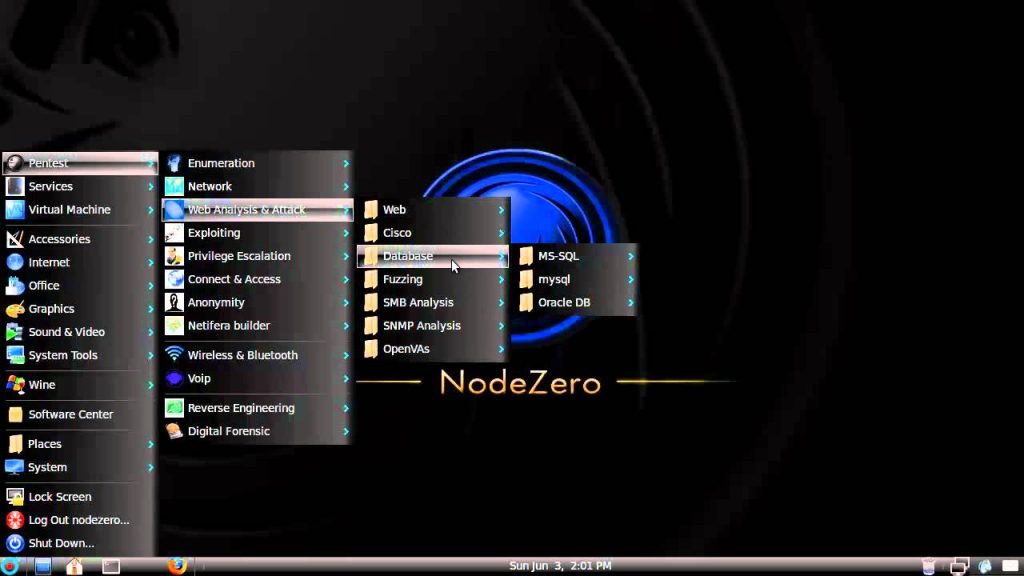
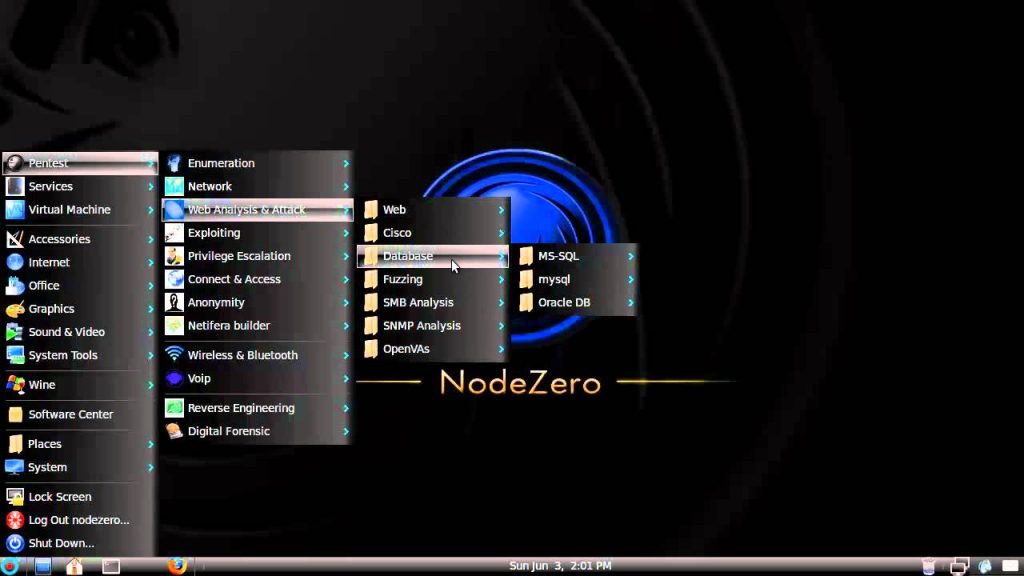
335Operating SystemsNodeZero – Lurking in the shadows of Pentesting
Us penetration testers have of course all heard of BackTrack it’s the most popular penetration testing distro out there but Node Zero...
-
 324Hacked
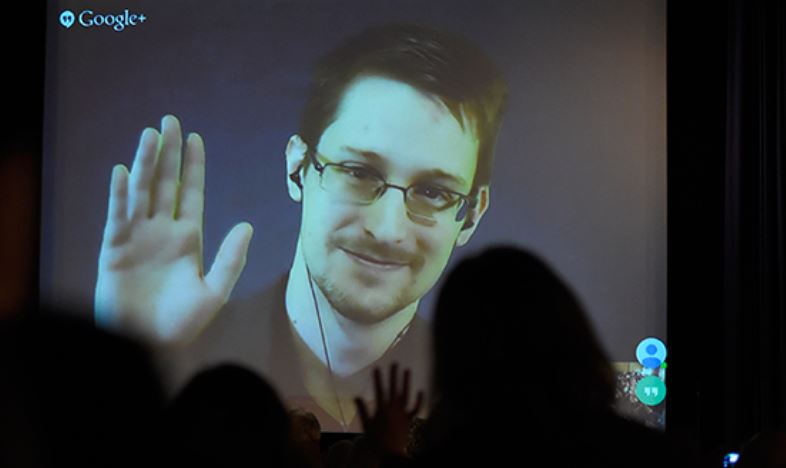
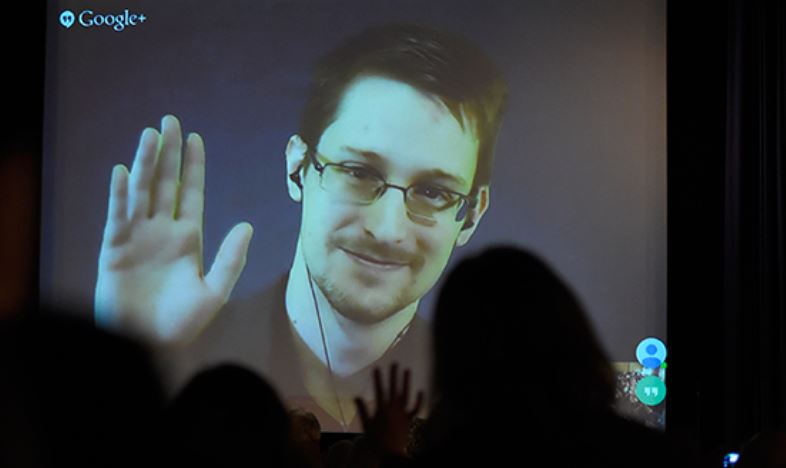
324HackedEdward Snowden Tells How to Build an Internet Focused on Privacy
When someone like Edward Snowden, tells you how to make an internet focused on privacy and user welfare, you listen, and you...
-

 199Cyber Events
199Cyber EventsAnonymous Hacks U.S. Census Bureau, Leaks Officials’ Personal Data Against TPP/TTIP
Remember the Anonymous hackers behind the massive World Trade Center (WTC) leak? Well, he’s back with another breach and this time their...
-

 84Malware
84MalwarePorn clicker keeps infecting apps on Google Play
A recently identified trojan porn clicker is still infecting apps on Google Play.
-
 281Hacked
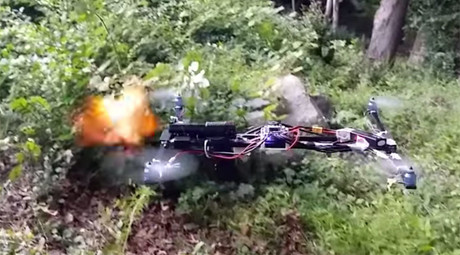
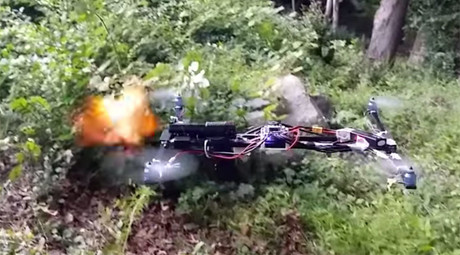
281HackedGun Firing Drone Appears Legal, FAA Still Investigating
Remember the Drone Gun? The quadcopter hovering in the woods of Clinton, Connecticut and firing rounds of shots and completely legal...
-
 448Scams
448ScamsSupport Scammers and Self‑Justification
Support scammers: old twisters, new twists, and scammer psychology.
-

 313Data Security
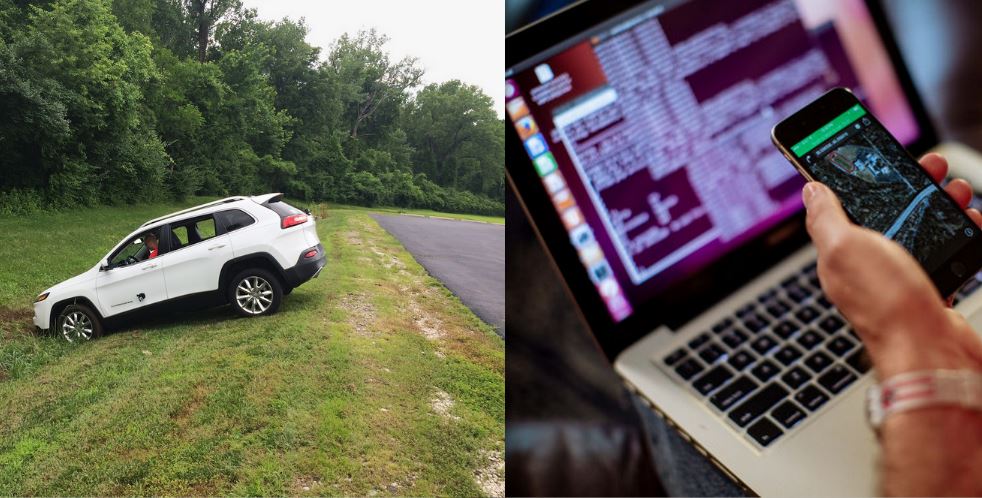
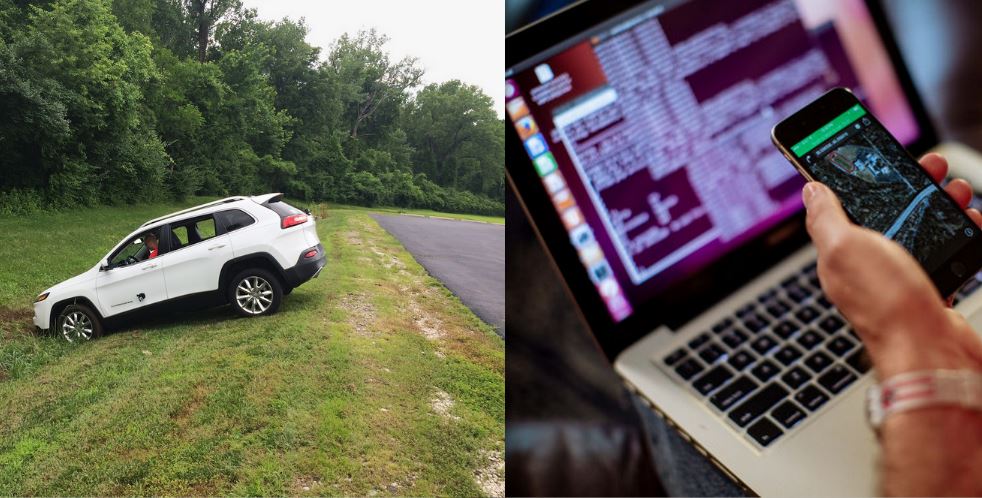
313Data SecurityJeep Cherokee On-Board System Hacked, More Than 470,000 Vehicles at Risk
We have heard about hacking websites, computers, planes, and other devices, but hacking a moving car? Well, it happened and it happened live....
-

 87Cyber Crime
87Cyber CrimeTech giants take action on ad click fraud
Some of the biggest digital companies have banded together to take action on the rising tide of ad click fraud.
-
 189Hacked
189HackedHackers Remotely Hacked This Car Running at 70mph on Highway
As our vehicles become smarter and more dependent on computers, the risk of a car hack automatically increases. Articles titled how to...
-

 110Privacy
110PrivacySmartwatch security ‘lacking’ says HP study
Smartwatch security is noticeably absent in most devices, leaving users at risk of cyberattacks.
-
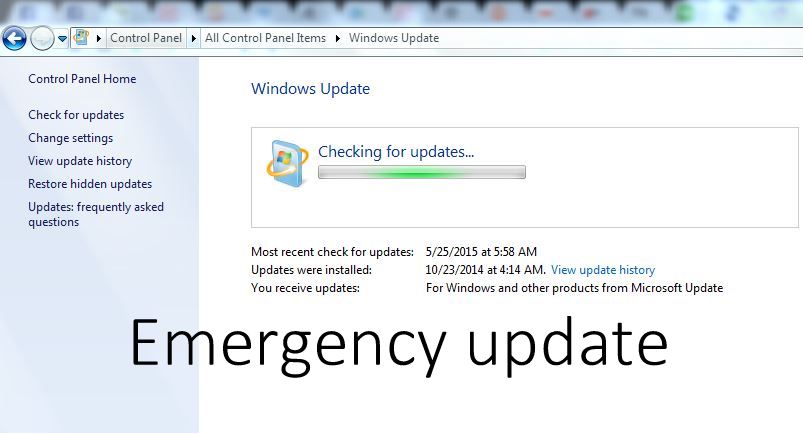
 195Hacked
195HackedDownload this Critical Windows Update Now, Flaw Allows Hackers to Control Entire System
A newly discovered vulnerability can allow hackers to remotely execute codes and take over your entire system. A user could be tricked...
-

 222Cyber Events
222Cyber EventsAnonymous Targets Canadian Police, Crashes RCMP’s Website
This week, on July 17th, there was a police-involved shooting in Dawson Creek, British Columbia Canada, where one of the members of...
-
 141How To
141How ToHow to turn night mode ON in Google Chrome
Google Chrome is the most used browser on the Internet as it is fast and secure. Google Chrome has many extensions in...
-
 222Geek
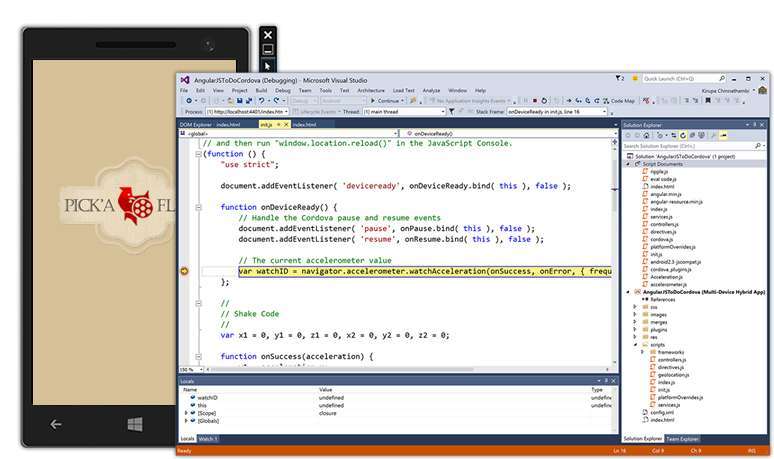
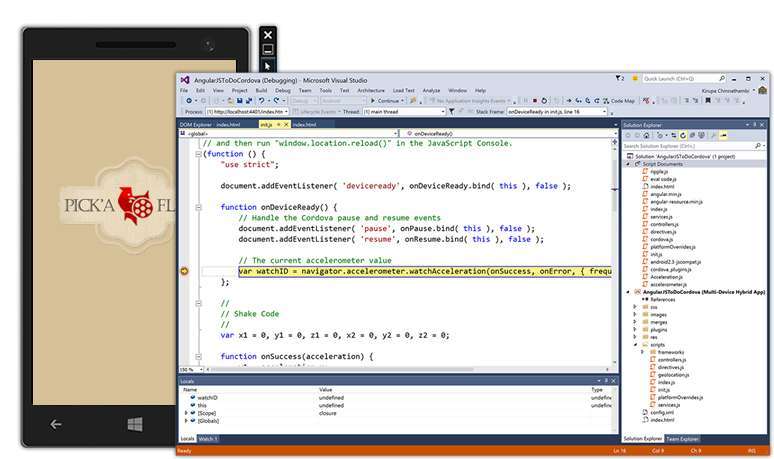
222GeekVisual Studio 2015 and .NET 4.6 Released, Download Now
Today is the Visual Studio 2015 and .NET 4.6 release day. These software from the house of Microsoft have finally graduated exiting...
-

 224News
224NewsHacknet , a real Hacking game.
Developed by Team Fractal Alligator, an Australian one-man studio, Hacknet is “an immersive, terminal-based hacking simulator for PC.” Here’s the official...
-

 135Scams
135ScamsMicrosoft advises ‘spoofed’ Skype users to change passwords
Skype users have been advised by Microsoft to change their passwords following reports that 'spoofed' messages are being sent without user permission.
The Latest
-
 Vulnerabilities
VulnerabilitiesFoxit PDF Reader Flaw Exploited by Hackers to Deliver Diverse Malware Arsenal
-
 Vulnerabilities
VulnerabilitiesDefending Your Commits From Known CVEs With GitGuardian SCA And Git Hooks
-
 Malware
MalwareCyber Criminals Exploit GitHub and FileZilla to Deliver Malware Cocktail
-
 Malware
MalwareLatrodectus Malware Loader Emerges as IcedID’s Successor in Phishing Campaigns
-
 Malware
MalwareGrandoreiro Banking Trojan Resurfaces, Targeting Over 1,500 Banks Worldwide
-
 Malware
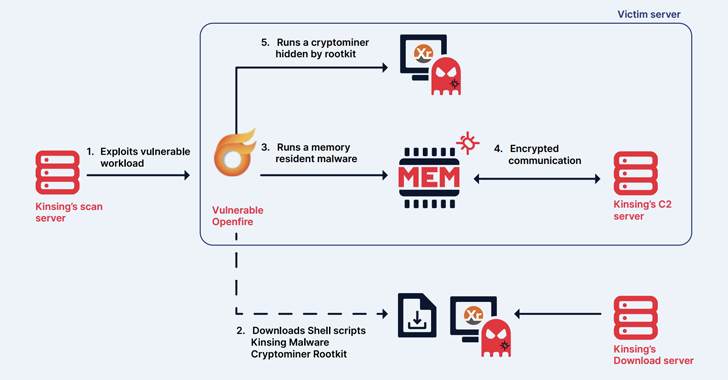
MalwareKinsing Hacker Group Exploits More Flaws to Expand Botnet for Cryptojacking
-
 Malware
MalwareChina-Linked Hackers Adopt Two-Stage Infection Tactic to Deploy Deuterbear RAT
-
 Malware
MalwareKimsuky APT Deploying Linux Backdoor Gomir in South Korean Cyber Attacks
-
 Vulnerabilities
VulnerabilitiesNew Wi-Fi Vulnerability Enables Network Eavesdropping via Downgrade Attacks
-
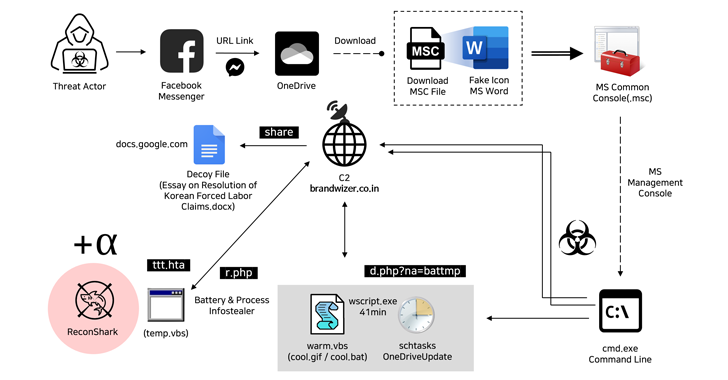 Malware
MalwareNorth Korean Hackers Exploit Facebook Messenger in Targeted Malware Campaign
-
 Malware
MalwareCybercriminals Exploiting Microsoft’s Quick Assist Feature in Ransomware Attacks
-
 Vulnerabilities
VulnerabilitiesGoogle Patches Yet Another Actively Exploited Chrome Zero-Day Vulnerability
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
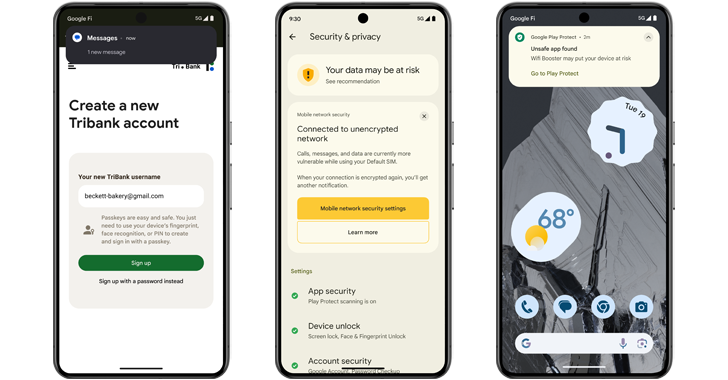 Malware
MalwareAndroid 15 Rolls Out Advanced Features to Protect Users from Scams and Malicious Apps
-
 Malware
MalwareTurla Group Deploys LunarWeb and LunarMail Backdoors in Diplomatic Missions
-
 Vulnerabilities
Vulnerabilities(Cyber) Risk = Probability of Occurrence x Damage
-
 Malware
MalwareEbury Botnet Malware Compromises 400,000 Linux Servers Over Past 14 Years
-
 Cyber Attack
Cyber AttackMicrosoft Patches 61 Flaws, Including Two Actively Exploited Zero-Days
-
 Vulnerabilities
VulnerabilitiesVMware Patches Severe Security Flaws in Workstation and Fusion Products
-
 Vulnerabilities
VulnerabilitiesNew Chrome Zero-Day Vulnerability CVE-2024-4761 Under Active Exploitation




