Featured News
-
 301Geek
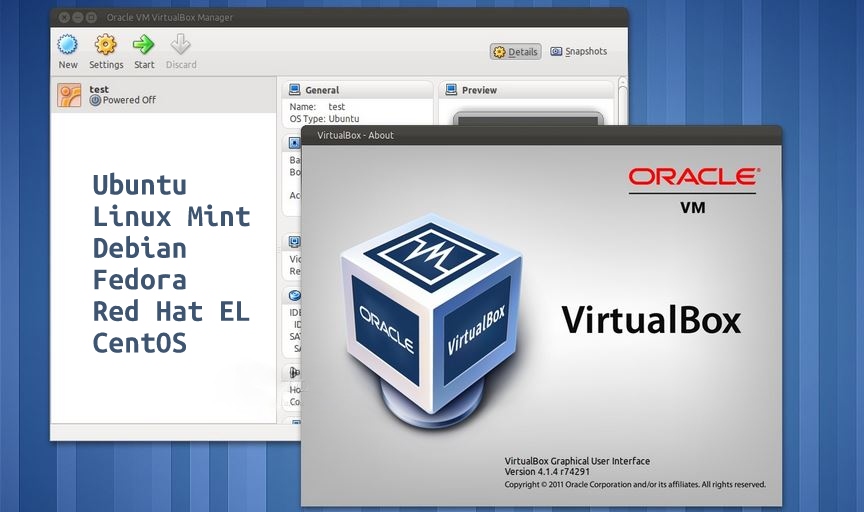
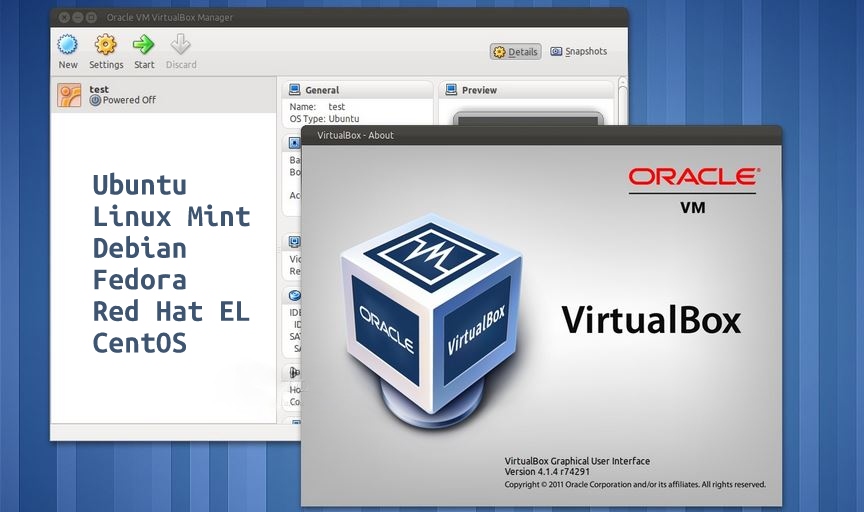
301GeekHow to Install VirtualBox 5.0 In Ubuntu, Debian, Linux Mint, RHEL, CentOS and Fedora
Virtual Machines are software that are used to run other operating systems within a pre-installed operating system. This self-contained OS runs as...
-

 934Cyber Crime
934Cyber CrimeBarclays compensates customers after personal data trove uncovered
Barclays bank is to pay out around £500,000 in compensation to 2,000 customers whose personal data was found on a USB stick...
-

 213Geek
213GeekAmazon Launches AWS Device Farm, Now Test Your Apps on Real Devices
To benefit the hard-working app developers and programmers, Amazon is starting a cloud-based service named AWS Device Farm. AWS Device Farm will...
-

 176Lists
176Lists10 Reasons Why You Should NOT Work for Facebook
Today, Facebook is one of the biggest company to work for. The name itself creates an aura around you (if you are...
-
 351Hacked
351HackedWebsite of ISRO’s Commercial Arm Antrix Hacked by Chinese Hackers
The website of Indian Space Agency ISRO’s commercial wing Antrix Corporation was hacked on Sunday. This attack comes two days after ISRO...
-

 177Hacked
177HackedPopular Game Malware Affecting More than 1 Million Android Users
Do you love playing games on your Android tablet and smartphone? Well, the innocent games you play, could be a route to...
-

 227Cyber Events
227Cyber EventsDDoS Ransom Notes, to Honor or Not to Honor?
In the wake of cyber crimes, a DDoS (Distributed Denial of Service) attack is something to be on the look-out for. Lately,...
-
 189Surveillance
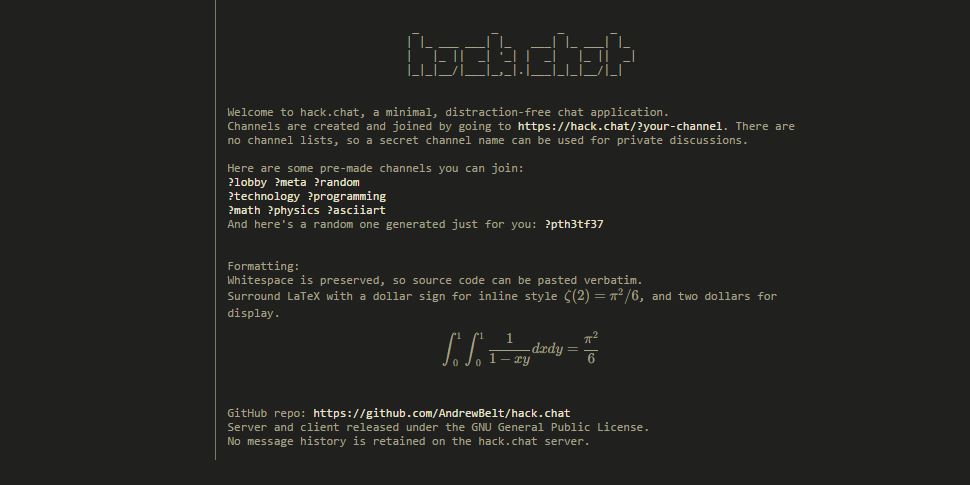
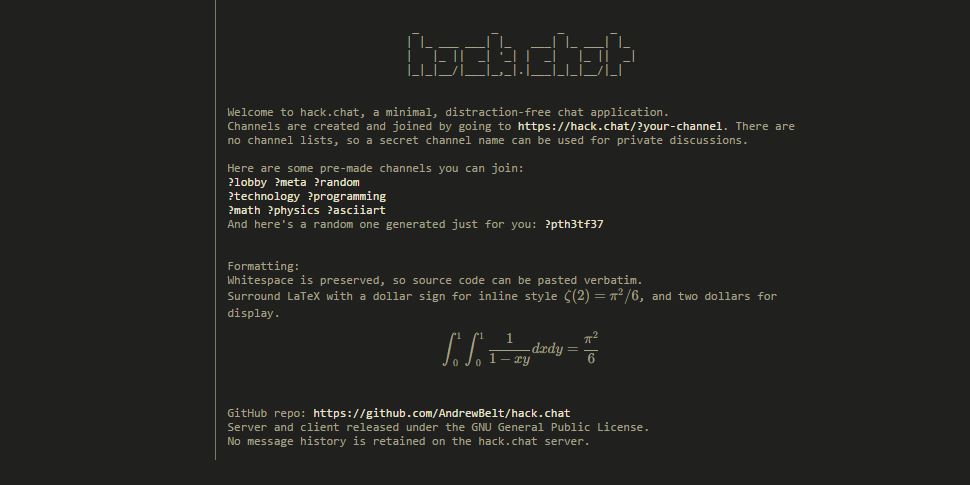
189SurveillanceHack.Chat – Instantly Create A Disappearing Chat Room and Chat Anonymously
From instant messaging to apps like WhatsApp and SnapChat, there are plenty of possibilities to chat on the Web, and many social...
-

 297Surveillance
297SurveillanceYou Can Now Delete Your Google Voice Search History
You know it’s easy to download and delete your searches from Google Search, but did you know you can also delete or manage...
-
 265How To
265How ToHow Hack.chat Makes Private and Disappearing Chatrooms in 5 Seconds
There is no dearth of instant messaging applications these days and people are addicted to Facebook Messenger, WhatsApp, SnapChat, IM on Twitter,...
-
 186How To
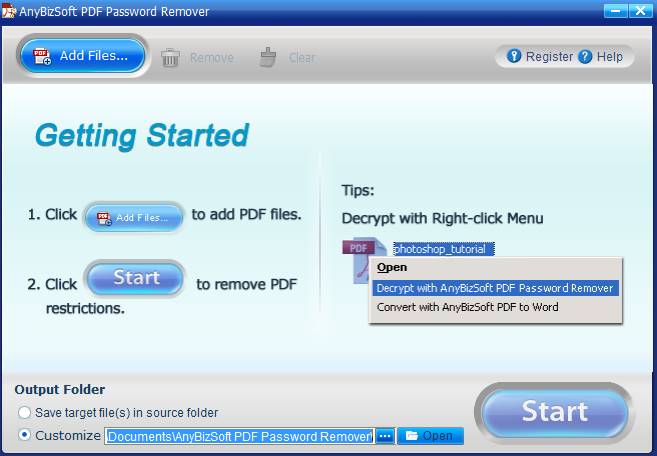
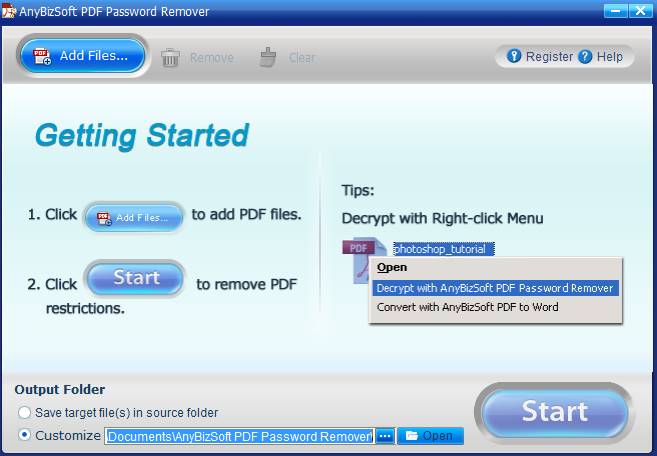
186How ToHow to remove password protection from PDF files
Now a days, we all save our data in a Word file or a PDF file. Some have basic information and some...
-
 145How To
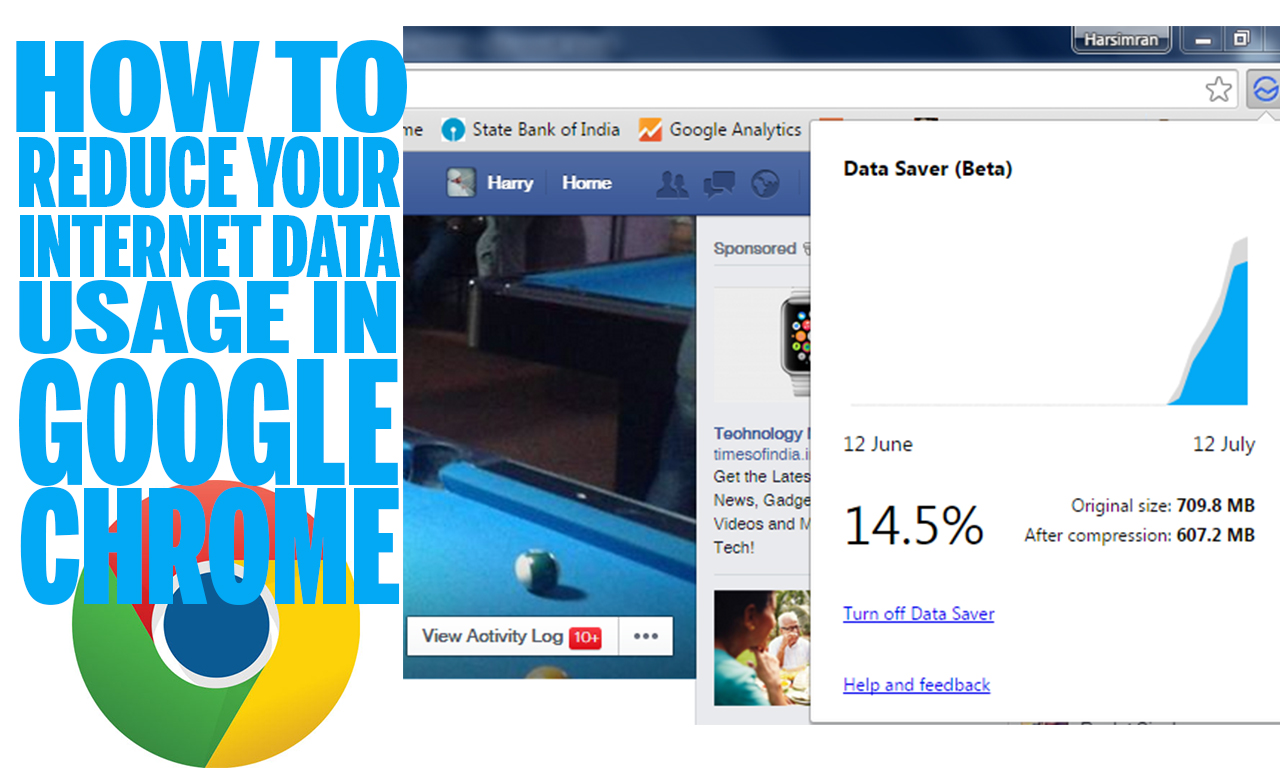
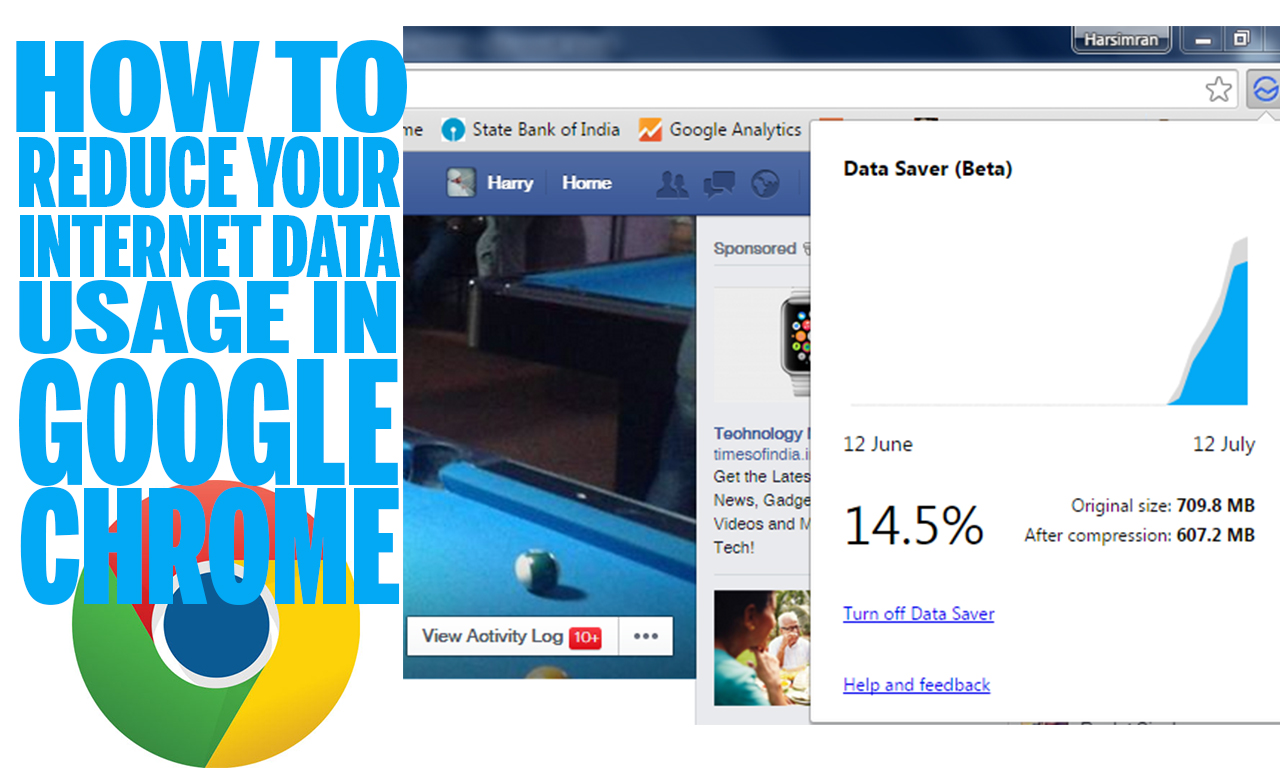
145How ToHow to reduce your Internet data usage in Google Chrome
Almost everyone uses the Internet now a days. Some people use mobiles and tablets where we all have to pay data usage...
-
 130Cyber Events
130Cyber EventsAnonymous Fights Animal Cruelty by Exposing Email Orders to Kill Bear Cubs
This weekend, Bryce Casavant who is a Canadian conservation officer was suspended from duty when he denied the orders to kill two...
-

 198News
198NewsOne Million Android Users Infected With Facebook Hacking Malware Apps
Ever wondered about the number of users an Android-based malware app can infect after getting approved and published on the Google Play...
-
 301Geek
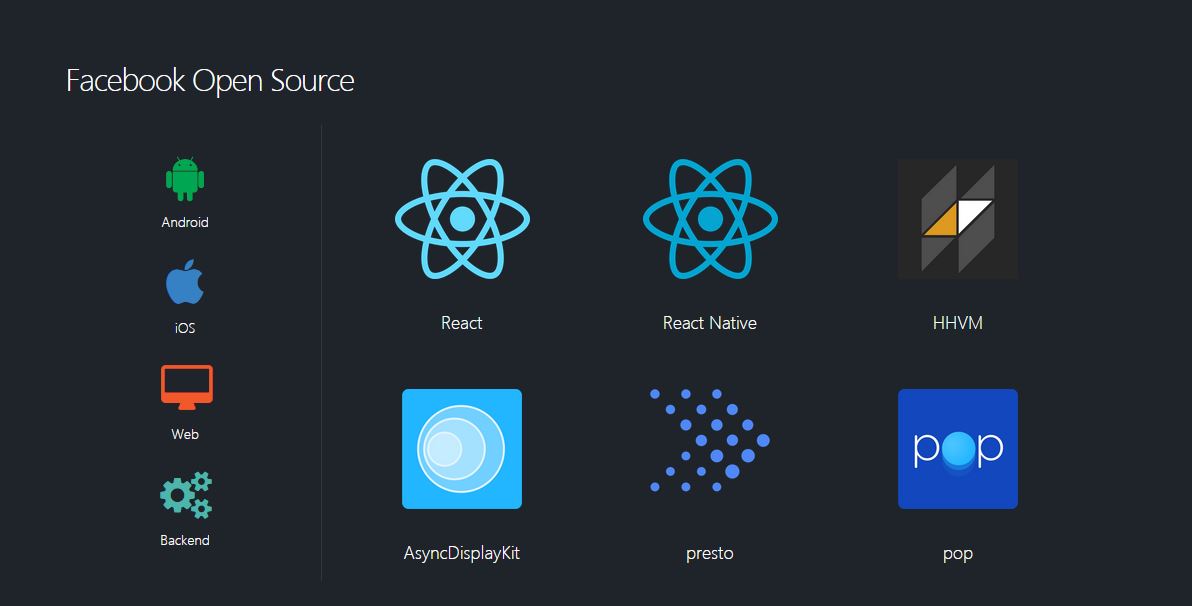
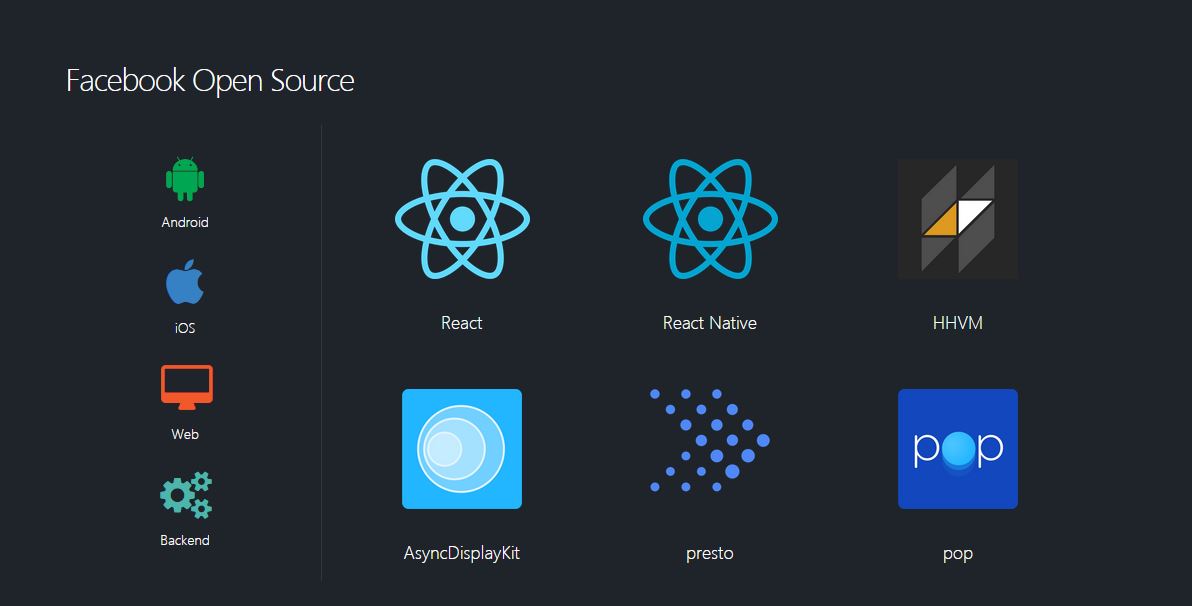
301GeekTop 15 Facebook Open Source Projects You Must Know
This is the first article of the series where we will be publishing about top open source projects made by big blue...
-
 130Cyber Crime
130Cyber CrimeBeware: Hackers Target Users with Adobe Phishing Scam
Taking Advantage of Hacking Team Leak, Hackers Target Users with Adobe Phishing Email. As you know Adobe flash is a software used...
-
 209Hacked
209HackedPirate Bay Founders Not Guilty in Criminal Copyright Case, Court Rules
The Pirate Bay is one of the most popular torrenting sites of the world, and it has constantly been into the limelight...
-

 317Data Security
317Data SecurityBeware of Fake Apps: Google Deletes Fake BatteryBot Pro Malware App
Last week we reported hackers are developing Android malware every 17 seconds, making it one of the most vulnerable OS ever. Now...
-
 188News
188NewsObama’s Election Campaign Social Network Domain Hacked by Yemeni Hacker
A Yemeni hacker going with the handle of “Lov3rDns” has hacked and defaced the official social network domain of U.S president Barack...
-

 232Cyber Crime
232Cyber CrimeSextortionist jailed for life, FBI searching for 350 online victims
31-year old Lucas Chansler is set to serve 105 years, perhaps the remaining days of his life, in prison after admitting to...
The Latest
-
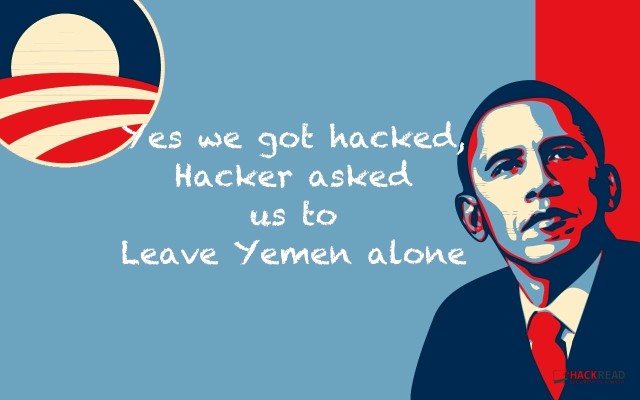
 Vulnerabilities
VulnerabilitiesExperts Find Flaw in Replicate AI Service Exposing Customers’ Models and Data
-
 Malware
MalwareBeware: These Fake Antivirus Sites Spreading Android and Windows Malware
-
 Vulnerabilities
VulnerabilitiesUpdate Chrome Browser Now: 4th Zero-Day Exploit Discovered in May 2024
-
 Malware
MalwareJAVS Courtroom Recording Software Backdoored – Deploys RustDoor Malware
-
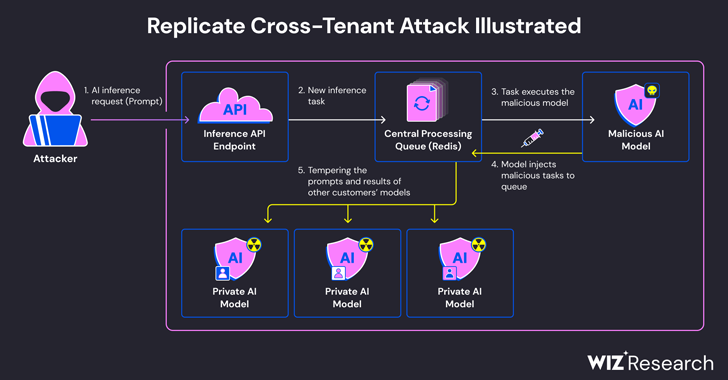
 Malware
MalwareStealthy BLOODALCHEMY Malware Targeting ASEAN Government Networks
-
 Vulnerabilities
VulnerabilitiesCISA Warns of Actively Exploited Apache Flink Security Vulnerability
-
 Malware
MalwareNew Frontiers, Old Tactics: Chinese Espionage Group Targets Africa & Caribbean Govts
-
 Malware
MalwareInside Operation Diplomatic Specter: Chinese APT Group’s Stealthy Tactics Exposed
-
 Data Breach
Data BreachAre Your SaaS Backups as Secure as Your Production Data?
-
 Vulnerabilities
VulnerabilitiesIvanti Patches Critical Remote Code Execution Flaws in Endpoint Manager
-
 Malware
MalwareResearchers Warn of Chinese-Aligned Hackers Targeting South China Sea Countries
-
 Vulnerabilities
VulnerabilitiesRockwell Advises Disconnecting Internet-Facing ICS Devices Amid Cyber Threats
-
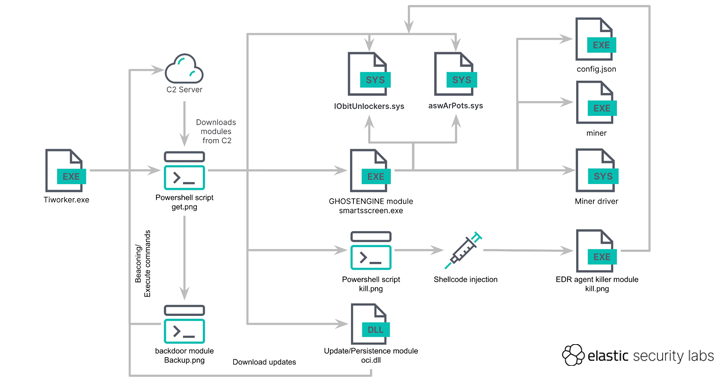 Malware
MalwareGHOSTENGINE Exploits Vulnerable Drivers to Disable EDRs in Cryptojacking Attack
-
 Data Breach
Data BreachMS Exchange Server Flaws Exploited to Deploy Keylogger in Targeted Attacks
-
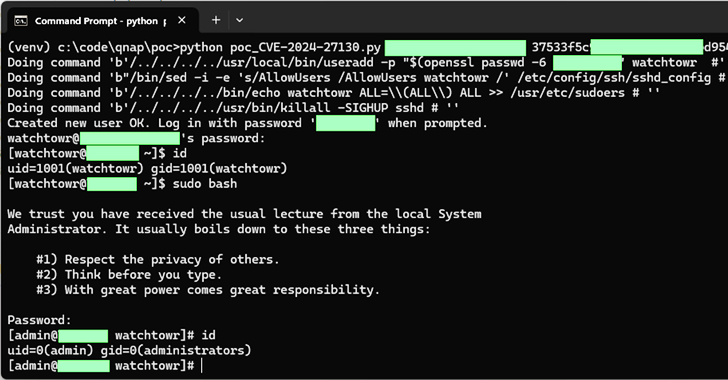 Vulnerabilities
VulnerabilitiesQNAP Patches New Flaws in QTS and QuTS hero Impacting NAS Appliances
-
 Vulnerabilities
VulnerabilitiesCritical Veeam Backup Enterprise Manager Flaw Allows Authentication Bypass
-
 Vulnerabilities
VulnerabilitiesCritical GitHub Enterprise Server Flaw Allows Authentication Bypass
-
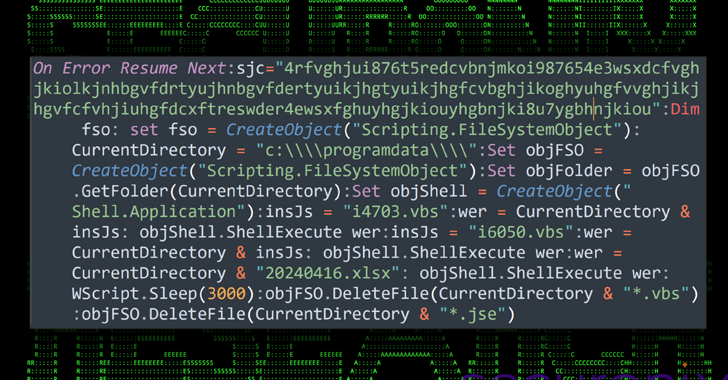 Malware
MalwareMalware Delivery via Cloud Services Exploits Unicode Trick to Deceive Users
-
 Data Breach
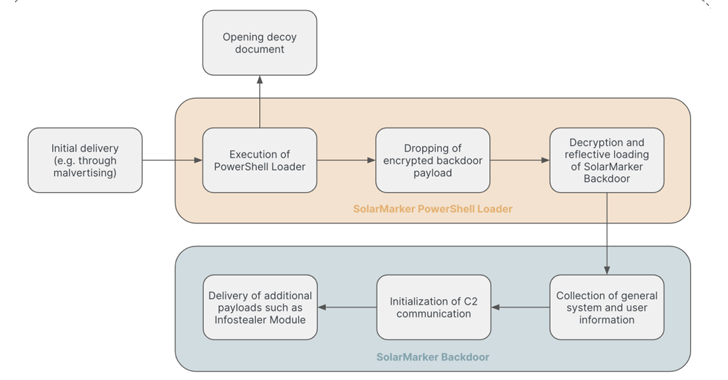
Data BreachSolarMarker Malware Evolves to Resist Takedown Attempts with Multi-Tiered Infrastructure
-
 Vulnerabilities
VulnerabilitiesNextGen Healthcare Mirth Connect Under Attack – CISA Issues Urgent Warning




