Featured News
-

 217Cyber Events
217Cyber EventsRussian MP Sick of LGBT Rainbow Flag Wants Facebook Blocked
The sitting MP of the regional parliament of Saint Petersburg, Vitaly Milonov, has introduced a new law to shut down the social...
-
 227Operating Systems
227Operating SystemsReview of Parrot OS
Parrot Security OS is a security oriented operating system designed for Pentesting, Computer Forensic, Reverse engineering, Hacking, Cloud pentesting, privacy/anonymity and cryptography....
-
 128News
128NewsHacker Series – Enough to motivate you?
With the amount of hackers expanding in the modern world, so does TV shows start to react. Time to get your ‘mode’...
-

 243Hacked
243HackedOne of the Best Anti-Virus Malwarebytes Offers Free 1-Year Premium Keys
“The Internet is full of pioneers and cowboys. It’s also got its fair share of pirates and trolls.” Piracy is the biggest...
-

 112Privacy
112PrivacyICANN policy changes trigger privacy concerns
Internet name authority ICANN has unsettled privacy advocates after a new working group document flagged changes to the way domain proxy services...
-

 195Surveillance
195SurveillanceUsing Drone for Abortion: Here Comes The Abortion Drone
Dutch based campaigners are focusing on women’s access to “easy and safe” method to bring an end to pregnancy with the help of...
-

 177Lists
177ListsTop 5 Supercomputers Of The World
Courtesy: Prof. Jack Dongarra Supercomputers of today are the retrogressive image of the one’s in 1960s i.e. a gigantic machine racking up an...
-

 176Surveillance
176SurveillanceHackers Posting Nude Pictures of Women without Their Knowledge
Nude pictures of more than 700 Aussie females leaked online without their permission or knowledge. An individual hosting the cache in a cloud...
-

 235News
235NewsHackers Target Gospel News Portal, Leave LGBT Flag Behind
The U.S supreme court yesterday ruled in favor of same-sex marriages nationwide. Some are celebrating and some are unhappy with the ruling, but...
-
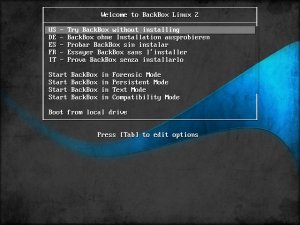
 203Operating Systems
203Operating SystemsBackbox – Turning heads in the pentesting scene
A relative newcomer to the forensic and penetration testing live CD scene, Italian project BackBox is already turning heads as it hits...
-

 216Android Hacking
216Android HackingTurning your Android into a hacking device
Now days, smartphones and tablets are the most popular gadgets. The reason behind this is that people utilize tablets for most of...
-
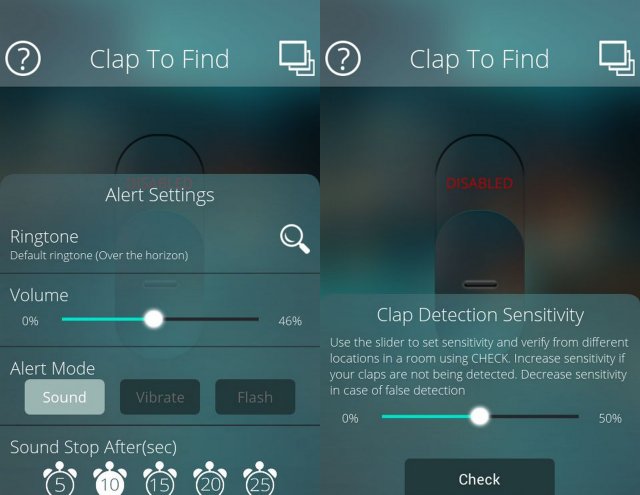
 329How To
329How ToHow to find your Silent Phone in a room without Internet
When busy with an important task, people like to put the mobile phone on Silent Mode. But what if you misplaced your...
-

 231Lists
231ListsMIT Lists 50 Smartest Companies That Owned the Year 2015
Short Bytes: This is an era of technological amelioration and every tech giant is striving to be the best. This article presents...
-
 114Hacked
114HackedHow To Remove Your Embarrassing Photos From All Social Media Websites
Work Hard and Party Even Harder. That’s the byword of today’s generation. Most of us have the same motto, myself being its hardcore...
-
 434Hacked
434HackedWatching Porn In Incognito Mode In Your Browser Isn’t As Safe As You Think
Short Bytes: The web browsers we use are shipped with settings that promise private browsing to the users. In Google Chrome, this...
-
 127Geek
127GeekRacket-lang: A Programmable Programming Language
You must have read our coverage on programming language and its development. If not, I would recommend you to go through it once....
-
 278Geek
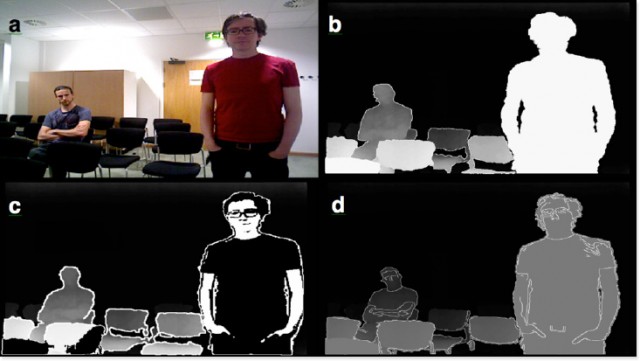
278GeekThese Wearable Glasses Lets Legally Blind People See Again
SmartSpecs are wearable glasses developed by Startup VA-ST using augmented reality so that visually impaired could see clearly once again. A University...
-

 198Geek
198GeekFacebook Algorithm Recognise You in Images Even if You’re Not Looking
Facebook’s new Algorithm powerful enough to identify you even if you aren’t looking at the camera. Facebook’s AI/artificial intelligence lab introduced an...
-

 118News
118NewsCredentials of over 47 U.S Government Agencies Leaked on the Internet
Reportedly, login credentials of around 47 U.S government institutions across 89 different domains have been leaked. Apparently, in the earlier part of...
-
 209Surveillance
209SurveillanceSecret Audio Recording Exposes Doctors Making Fun of Patient’s Penis
Patient Records Audio While being Operated- Hears doctors Making Fun of His Penis. You surely wouldn’t expect doctors to laugh at your...
The Latest
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft




