Featured News
-

 515How To
515How ToHow To Get Windows 10 Upgrade Icon If Missing – Official Method by Microsoft
Microsoft is trying desperately to convince the users to upgrade their Windows 7 and Windows 8.1 PCs to the next iteration to...
-
 201How To
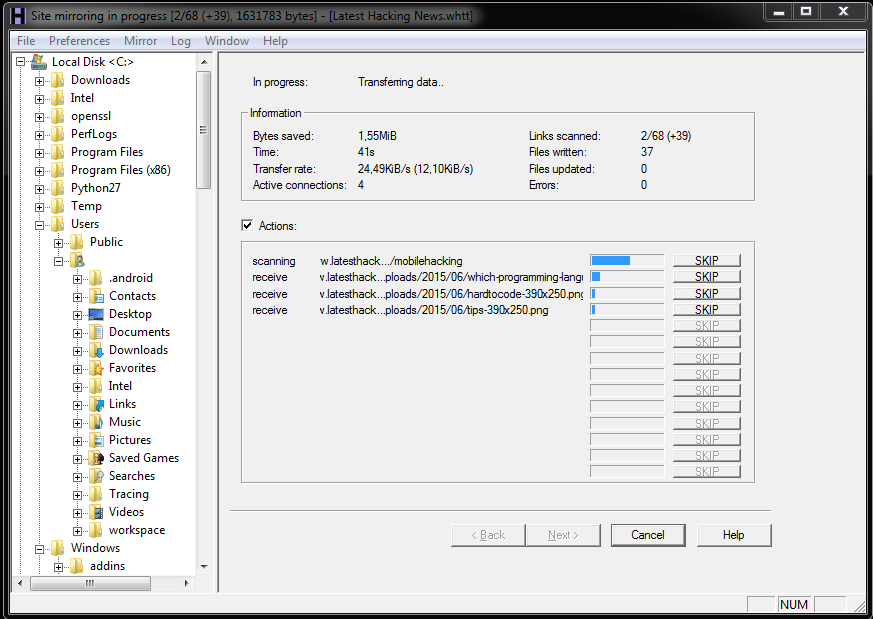
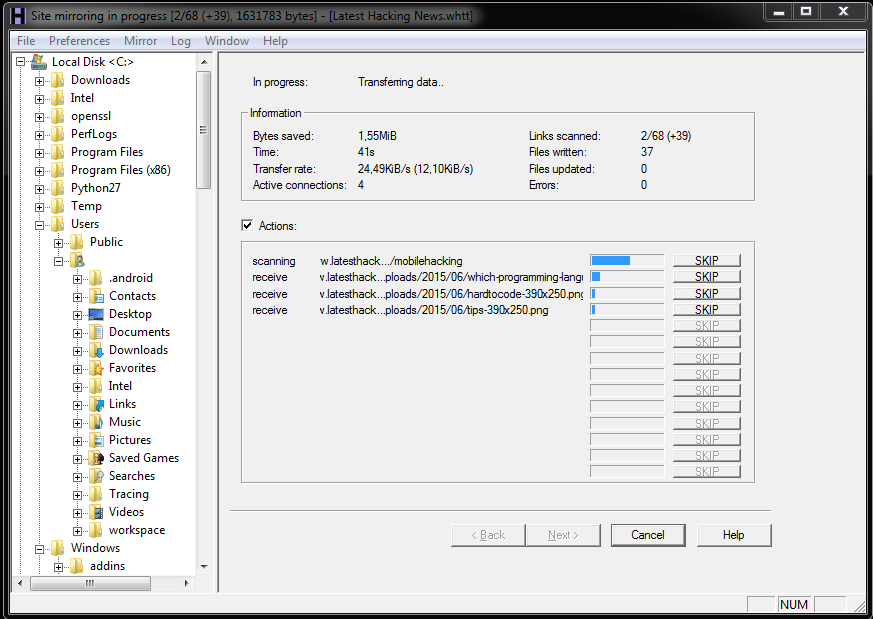
201How ToHow To Download And View Website Offline
Few times you have to give up on loading multiple website with slow internet connection or having problem with internet, or when...
-

 195Privacy
195PrivacyWikipedia switches to HTTPS by default
Wikimedia has announced that all of its web properties – including the enormously popular crowd-sourced dictionary Wikipedia – will now use HTTPS...
-
 222Hacked
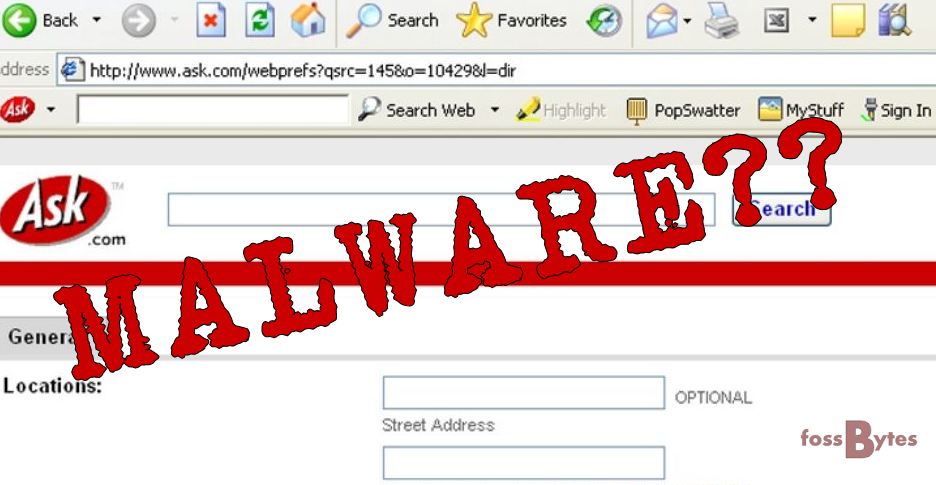
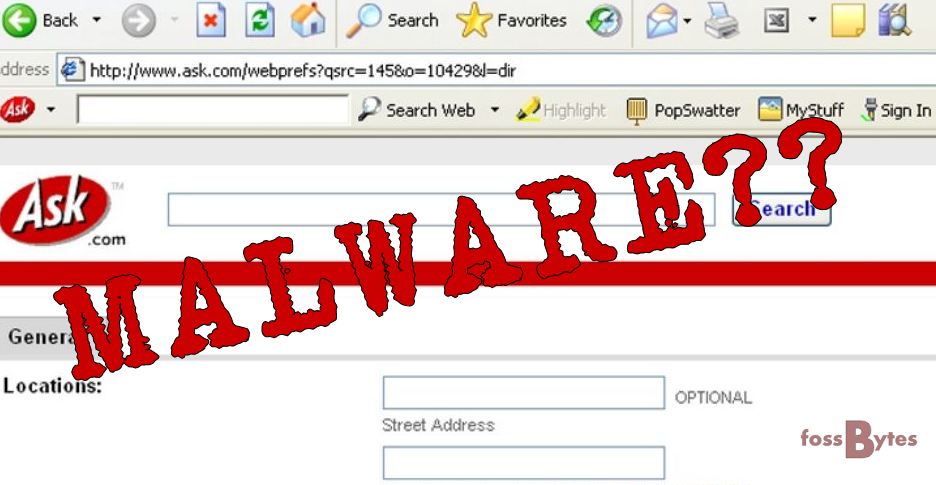
222HackedAsk Toolbar in Your Browser is a Malware: Microsoft
The vintage Ask toolbar that you can spot in your computer’s web browser has now been termed as threat to your PC...
-
 160Tricks & How To's
160Tricks & How To'sHow to check whether your ISP is Throttling your Internet speeds.
You, the usual and the average consumer, doesn’t know the boundaries that define the exploitation when it comes to the net neutrality...
-

 306How To
306How ToA Complete Guide On Facebook Tips And Tricks
Who would have thought something that started as a mischief could go on to become the heart of a billion people’s social...
-

 285Data Security
285Data SecurityHacker Targets Pedophiles with TOX Ransomware
Tox is yet another example of cyber justice that has been meted out by cyber criminals. In this case, Tox sends a...
-

 186Geek
186GeekNew Computer Algorithm Learns Rap Lyrics and Writes Its Own Rap Song
Have you ever wondered how musicians write music? Do you think it’s possible to technically generate a composition and write lyrics to...
-

 284News
284NewsSecond Hack Rattles US Federal and Military Personnel
Another hack has just exposed the personal details of more than 14 million people. According to intelligence reports, the hack was linked...
-

 232Geek
232GeekNew Headsets will Merge Night Vision and Thermal Imaging Features
A new headset is being developed by the BAE Systems Plc, which will merge thermal imaging and night vision to make night...
-
 243Hacked
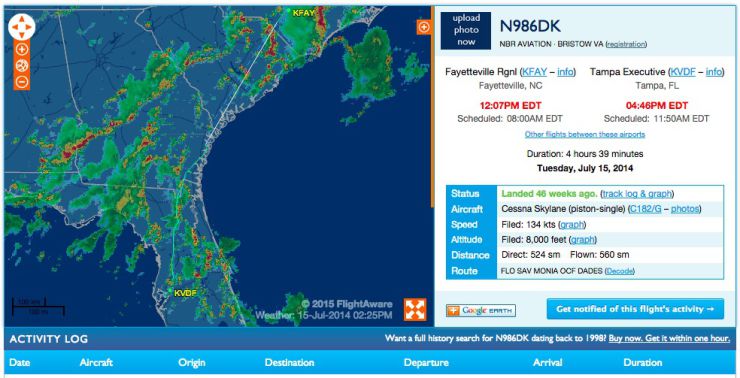
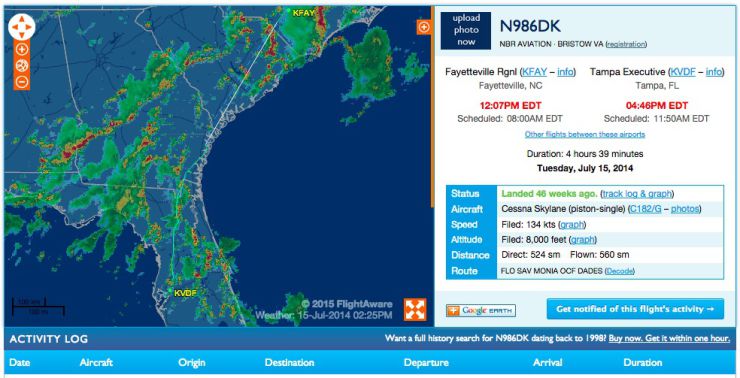
243HackedHere’s How You Can Track the FBI Spy Planes
In a report earlier his month, it was reported that the Federal Bureau of Investigation (FBI) is flying spy planes over the...
-

 238Data Security
238Data SecurityApps will Automatically Detect Malware in Windows 10
Software developers will have the opportunity to integrate their application to any antimalrware program (available on their computer) in windows 10. Microsoft...
-

 128Cyber Crime
128Cyber CrimeCanadian Hacker Jailed in U.S. for Hacking Military and Xbox
A hacker from Mississauga, Canada got imprisoned for leading a worldwide computer hacking group that managed to penetrate the U.S military network...
-

 524Privacy
524PrivacySnapchat bolsters security with optional Two‑factor authentication
Snapchat has added an option for two-factor authentication in its latest update, followed in the footsteps of Apple, Twitter and Facebook.
-

 108Data Security
108Data SecuritySecurity Bug Makes Millions Of iOS 8.3 iCloud Passwords Vulnerable
You may need to change the password of your iOS device as a security researcher reported that a flaw in Apple’s systems can...
-

 134Data Security
134Data SecurityFacebook Users Left Red-Faced After Porn Malware Attack
Hackers spammed Facebook timelines and newsfeeds with malicious malware that spread pornographic videos and images. The attack left hundreds of social media...
-

 334Data Security
334Data SecurityFrance Believes Russia Hacked TV5Monde Posing as ISIS Hackers
The involvement of a Russian hacking group posing as ISIS/ISIL militants in the April cyberattack that crippled a French-language broadcaster has been...
-

 78Cyber Crime
78Cyber CrimeFBI trace celebrity iCloud hacks to Chicago home
The FBI has seized a computer, cellphones and storage devices belonging to a Chicago man thought to be responsible for last year's...
-

 316News
316NewsHackers Hiding Vawtrak Banking Malware Command Servers in Tor
Some versions of Vawtrak banking Malware or Neverquest have been discovered to be having hidden command and control servers at Tor anonymity...
-

 247Cyber Crime
247Cyber CrimeEuropol shuts down cybercrime ring with 49 arrests
Europol's European Cybercrime Centre has arrested 49 suspects in a joint international operation targeting the takedown of a major cybercrime ring.
The Latest
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Malware
MalwareEternal Malware: CVE-2024-3400 Rootkits Persist Through Palo Alto Firewalls Updates and Resets
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Data Breach
Data BreachNavigating the Threat Landscape: Understanding Exposure Management, Pentesting, Red Teaming and RBVM
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage




