Featured News
-

 283News
283NewsEven the Best isn’t Safe: World’s Leading Cybersecurity Firm Kaspersky Hacked
An expensive and highly sophisticated hack attack was carried out on the Moscow-based Kaspersky Lab by state-backed hackers. On Wednesday the world’s...
-

 154Cyber Crime
154Cyber CrimeCredit Unions and the Data Security Act of 2015
Credit Unions lost a lot of money due to recent breaches, so financial institutions are eager to see merchants held to higher...
-

 112Cyber Crime
112Cyber Crime“Attempts to Export Opengraph File” Phishing Scam Targeting Facebook Users
A new phishing scam has surfaced on the web via Facebook in the form of a message titled “Attempts to Export Opengraph...
-

 253Surveillance
253SurveillanceCanada’s New Anti-Terror Bill C-51 will Ruin Internet Privacy
Canada approves anti-terror law C-51 that weakens Internet privacy – NDP-Liberal coalition may get triggered as a result warn conservative critics. At...
-

 269News
269NewsPro-Palestine Group Hacks Subdomains of US Air Force Website
Summary: Yesterday, it was the pro-Assad hackers from Syrian Electronic Army who took over the US Army website, today the pro-Palestinian hackers...
-

 95Cyber Crime
95Cyber CrimeBritish businesses spend £34bn a year defending cyberattacks, limiting growth
A new survey has estimated that British businesses spend around £34bn a year ($52.5bn) protecting the country from cyberattacks,
-
 195Cyber Events
195Cyber EventsGeneration Y is More Vulnerable to Cyber Attacks than Generation X, says study
A survey conducted by the Gartner-affiliated research firm Software Advice shows that Generation Y – those born after the 80s – is more vulnerable...
-

 223Cyber Events
223Cyber EventsUN Watchdog Warns of Increase in Cyberattacks on Nuclear Facilities
Computer systems at nuclear facilities all over the world face cyberattacks on a daily basis, says a UN nuclear watchdog group while addressing...
-
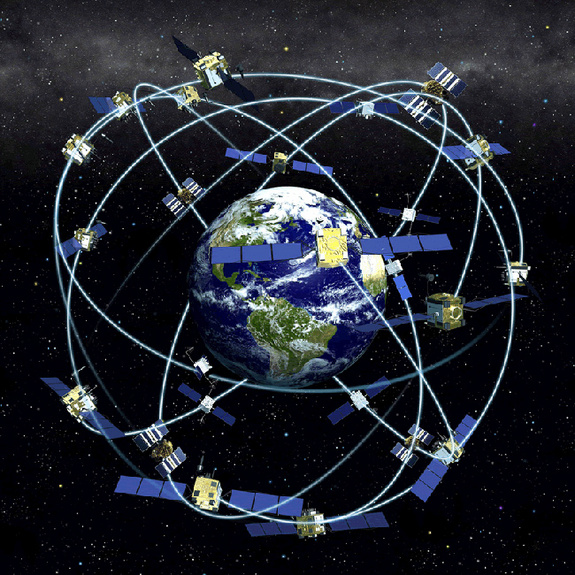
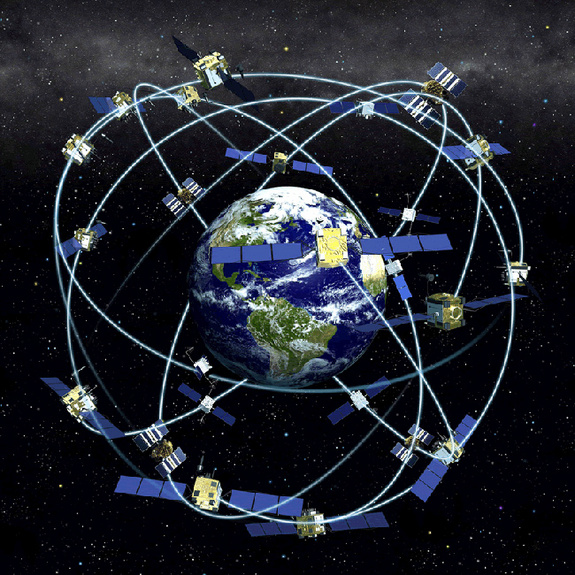 314GPS & Radio
314GPS & RadioSatellite & GPS Hacking
A satellite is a moon, planet or machine that orbits a planet or a star. Earth is a satellite because it orbits...
-

 237Cyber Crime
237Cyber CrimeIT security budgets will continue to rise, finds Dell report
Around half of IT security leaders said that budgets will significantly increase (19%) or increase (31%) over the next two years, finds...
-
 240Data Security
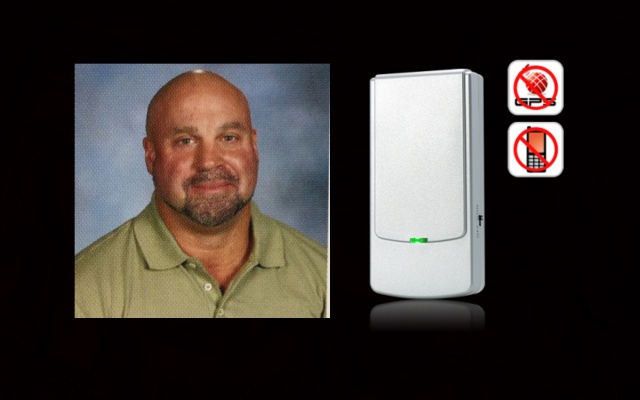
240Data SecurityTeacher Suspended for using jammer in class to stop students’ cell phones
Summary: Five days suspension without pay awaited the Hudson teacher who took a class experiment a bit too far and used jammer...
-

 215Cyber Crime
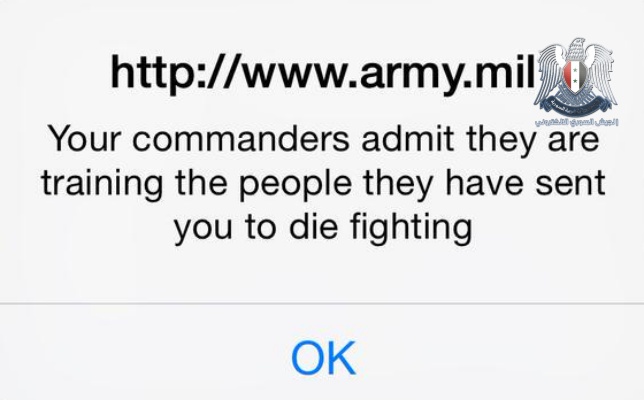
215Cyber CrimeUS Army website defaced by Syrian Electronic Army hackers
Hackers, supportive of the Assad regime in Syria, have successfully compromised content displayed on the US Army's website, popping up messages to...
-

 220News
220NewsWebsite of Serbian Embassy in the United States Hacked
The official website of Embassy of Serbia in the United States has been hacked and defaced by a group of Moroccan hackers. The...
-
 416News
416NewsSyrian Electronic Army Hacks Official US Army Website
The world renowned Syrian hacktivists form Syrian Electronic Army (SEA) hacked and defaced the official website of United States Army earlier today...
-
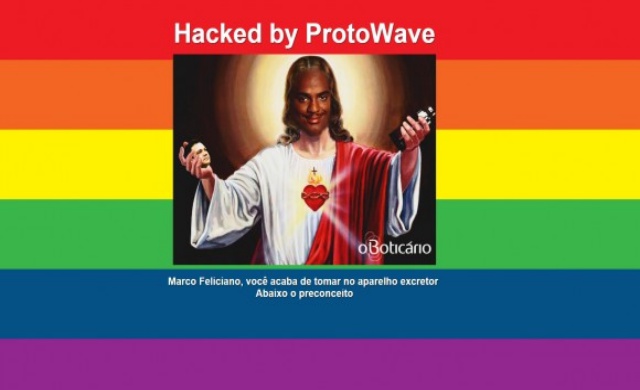
 311News
311NewsHomophobic Pastor’s Website Hacked During Gay Pride Parade
A Brazilian hacker going with the handle of ProtoWave, broke into the official website of Brazilian pastor Marco Feliciano, on Sunday afternoon (7th June),...
-

 352Hacked
352HackedProject Shield: Google Wants to Protect News and Human Rights Websites from DDOS Attack
DDOS aka Distributed Denial of Service (DDoS) attack is an attempt to make an online service unavailable by overwhelming it with traffic from...
-

 160Hacked
160Hacked“Dark Jedi” Security Flaw Found, Lets Hackers Attack Apple Computers
It was just the last week when people found out that iPhone could be crashed just by sending a particular text message....
-

 263Surveillance
263SurveillanceChina Using Surveillance Drones to Prevent Cheating in College Exam
We have always heard about negative use of drones or most of the times drones for surveillance purposes. But now two testing centers in...
-

 335Geek
335GeekInjured Girl Gets 1st-ever 3D Printed Titanium Skull Implant
Summary: Jessica Cussioli suffered a horrible motorcycle accident and was left without a major portion of her skull. Neurosurgeons rescued her by...
-

 290Cyber Crime
290Cyber CrimeStudents Hack High School Computers to Modify Their Grades
Some students of San Dimas High School, California, allegedly hacked the computer system of the school’s network and modified the grades of...
The Latest
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Malware
MalwareEternal Malware: CVE-2024-3400 Rootkits Persist Through Palo Alto Firewalls Updates and Resets
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Data Breach
Data BreachNavigating the Threat Landscape: Understanding Exposure Management, Pentesting, Red Teaming and RBVM
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage




