Featured News
-
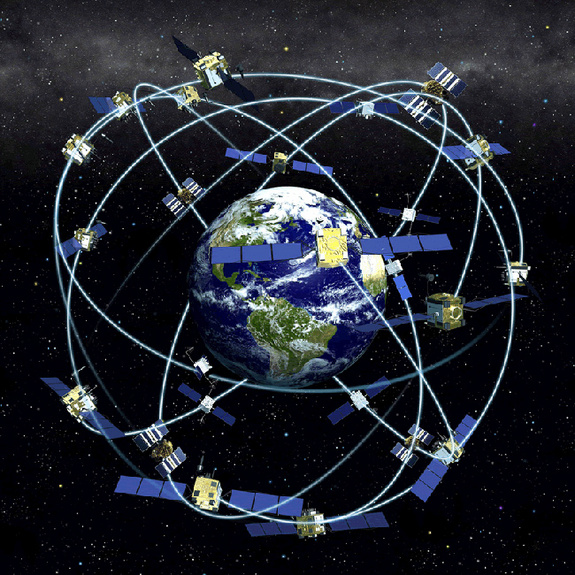
 316GPS & Radio
316GPS & RadioSatellite & GPS Hacking
A satellite is a moon, planet or machine that orbits a planet or a star. Earth is a satellite because it orbits...
-

 240Cyber Crime
240Cyber CrimeIT security budgets will continue to rise, finds Dell report
Around half of IT security leaders said that budgets will significantly increase (19%) or increase (31%) over the next two years, finds...
-
 241Data Security
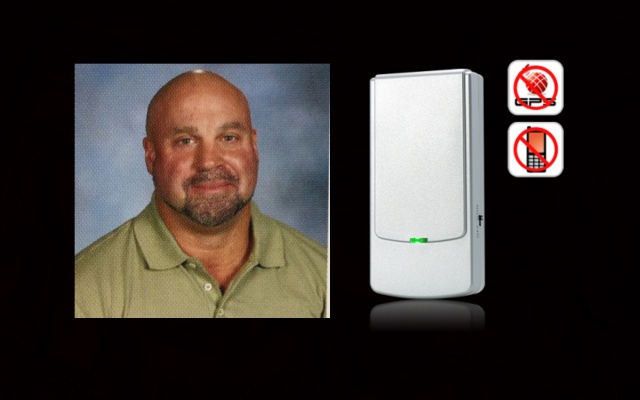
241Data SecurityTeacher Suspended for using jammer in class to stop students’ cell phones
Summary: Five days suspension without pay awaited the Hudson teacher who took a class experiment a bit too far and used jammer...
-

 217Cyber Crime
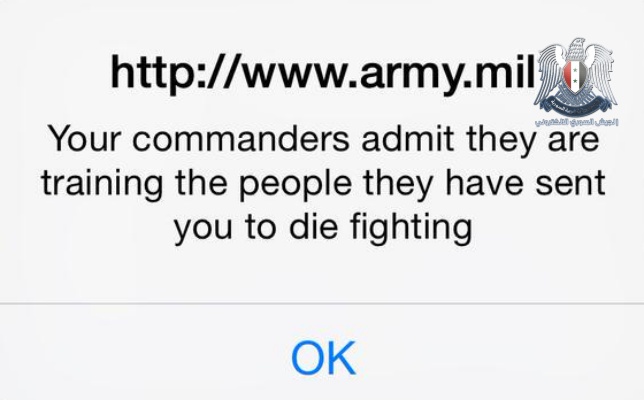
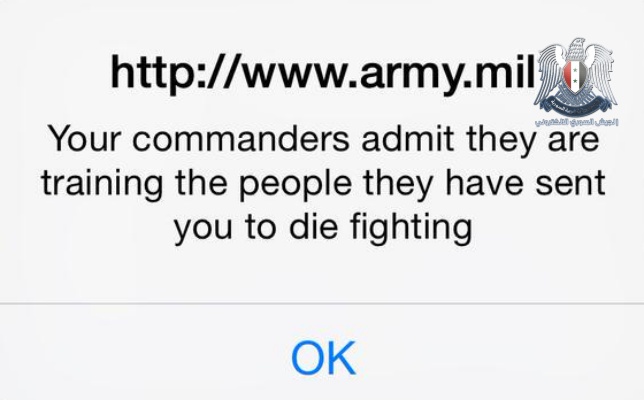
217Cyber CrimeUS Army website defaced by Syrian Electronic Army hackers
Hackers, supportive of the Assad regime in Syria, have successfully compromised content displayed on the US Army's website, popping up messages to...
-

 223News
223NewsWebsite of Serbian Embassy in the United States Hacked
The official website of Embassy of Serbia in the United States has been hacked and defaced by a group of Moroccan hackers. The...
-
 421News
421NewsSyrian Electronic Army Hacks Official US Army Website
The world renowned Syrian hacktivists form Syrian Electronic Army (SEA) hacked and defaced the official website of United States Army earlier today...
-
 313News
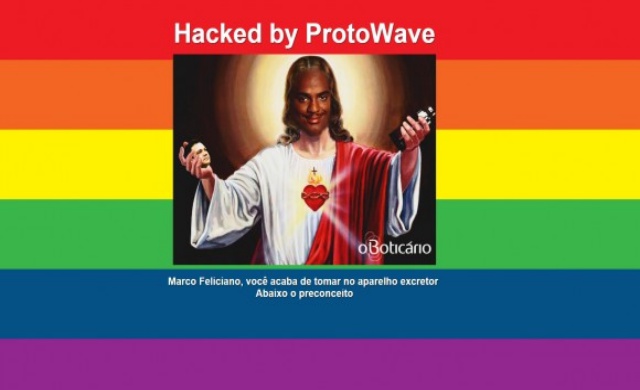
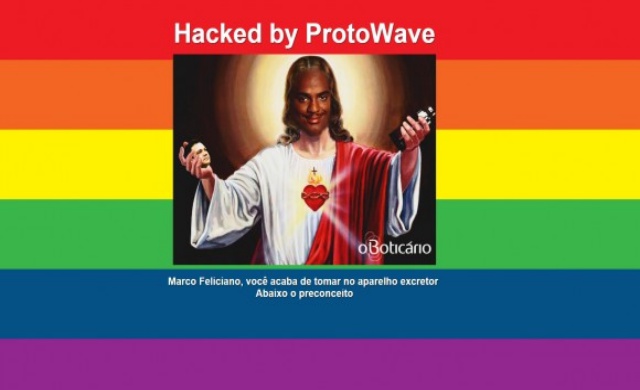
313NewsHomophobic Pastor’s Website Hacked During Gay Pride Parade
A Brazilian hacker going with the handle of ProtoWave, broke into the official website of Brazilian pastor Marco Feliciano, on Sunday afternoon (7th June),...
-

 358Hacked
358HackedProject Shield: Google Wants to Protect News and Human Rights Websites from DDOS Attack
DDOS aka Distributed Denial of Service (DDoS) attack is an attempt to make an online service unavailable by overwhelming it with traffic from...
-

 163Hacked
163Hacked“Dark Jedi” Security Flaw Found, Lets Hackers Attack Apple Computers
It was just the last week when people found out that iPhone could be crashed just by sending a particular text message....
-

 266Surveillance
266SurveillanceChina Using Surveillance Drones to Prevent Cheating in College Exam
We have always heard about negative use of drones or most of the times drones for surveillance purposes. But now two testing centers in...
-

 337Geek
337GeekInjured Girl Gets 1st-ever 3D Printed Titanium Skull Implant
Summary: Jessica Cussioli suffered a horrible motorcycle accident and was left without a major portion of her skull. Neurosurgeons rescued her by...
-

 293Cyber Crime
293Cyber CrimeStudents Hack High School Computers to Modify Their Grades
Some students of San Dimas High School, California, allegedly hacked the computer system of the school’s network and modified the grades of...
-

 315How To
315How ToHow to Use New Google Photos App from Your Computer
Google has recently launched the brand-new and charming Google Photos. This is available both on the web and mobile devices and is...
-

 391Lists
391ListsA Complete Guide On YouTube Tips and Tricks
It wouldn’t come across as a surprise to anyone if I say that today the word Video has become synonymous with YouTube....
-

 389Geek
389GeekNow Access YouTube and Google Maps Offline on Your Android Phone
Google, at its I/O conference that concluded recently, launched a range of initiatives aimed at making applications lighter and more user-friendly in...
-

 199News
199NewsOrganizer of “Freedom of Speech Rally” in Arizona Has Been Hacked
Summary: Jon Eric Ritzheimer, the man behind organizing an anti-Islamic protest in Phoenix, Arizona is now claiming that he has been hacked by...
-

 217Surveillance
217SurveillanceUS Air Force Bombs ISIS HQ after Tracking Location Through Social Media Post
The US Air Force claims it destroyed ISIS HQ Building within 22 hours following a social media post from an ISIS member. ISIS...
-

 231Data Security
231Data SecurityFacebook Users Hit with Malware Disguised as Google Chrome Video Installer
Trend Micro researchers have identified a new scheme in which scammers have used Facebook again to distribute malware. This malware has been...
-
 279News
279NewsHacker uses Toy to Hack and Open Garage Doors in Seconds
An electronic Mattel toy was transformed into a tool by Samy Kamkar to unlock all kinds of fixed-code garage doors within seconds....
-

 367Data Security
367Data SecurityApple, Google’s Encryption helping ISIS, Encouraging Terrorism- FBI
The Federal Bureau of Investigation believes that Apple and Google are actually helping ISIS and encouraging terrorism by offering users encrypted communications....
The Latest
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Cyber Attack
Cyber AttackMicrosoft Patches 61 Flaws, Including Two Actively Exploited Zero-Days
-
 Cyber Attack
Cyber AttackThe 2024 Browser Security Report Uncovers How Every Web Session Could be a Security Minefield
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Data Breach
Data BreachBlack Basta Ransomware Strikes 500+ Entities Across North America, Europe, and Australia
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Data Breach
Data BreachA SaaS Security Challenge: Getting Permissions All in One Place
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment




