Featured News
-
 215Cyber Events
215Cyber EventsUS Blames China for Stealing Data of 4 Millions Government Workers
Hackers working for the Chinese military unit allegedly carried out a “massive breach” in December targeting records of the Office of Personnel...
-
 216How To
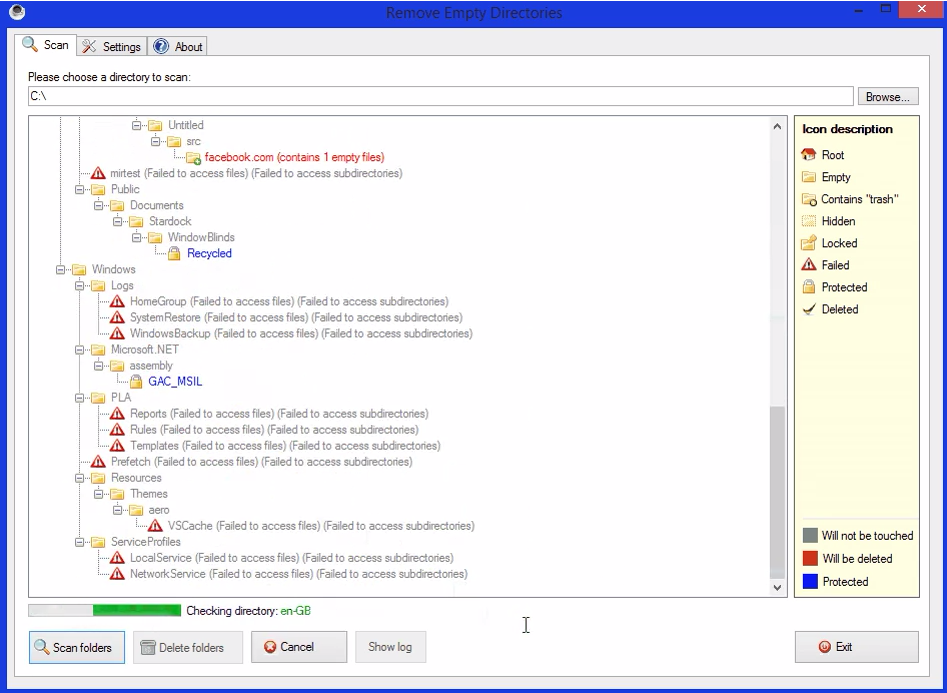
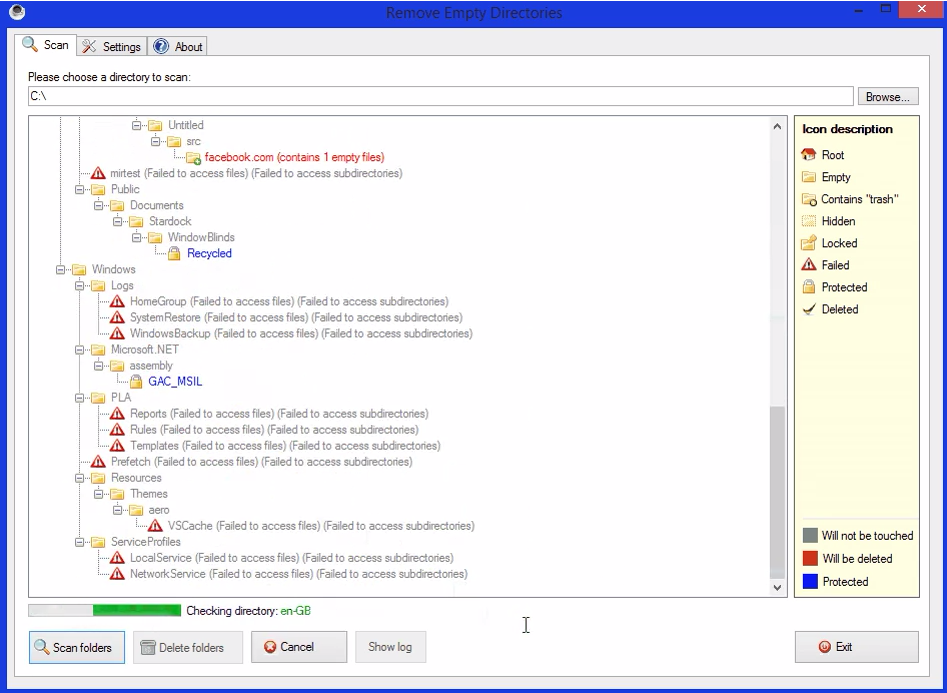
216How ToHow To Delete Empty Folder With One Click
Why do you wanna have empty folders for no use? You can download software when your tired to search and delete. This program...
-

 91Malware
91MalwareOpenSesame: Hacked kids’ toy could open garage doors
Garage doors may be vulnerable to being opened remotely by hackers using little more than a children's toy, a security researcher has...
-

 289Hacking Tutorials
289Hacking TutorialsHow to detect SQL Injection attacks
SQL Injection (SQLi) attacks have been around for over a decade. You might wonder why they are still so prevalent. The main...
-

 79Cyber Crime
79Cyber Crime4 million government employees’ personal data stolen in OPM hack
Four million federal employees have had their personal data stolen from the Office of Personnel Management, according to a statement on its...
-

 135Cyber Crime
135Cyber CrimeBatman v Superman: Dawn of Cybercrime Justice?
The fight against cybercrime could use some superheroes, but who would do a better job: Batman or Superman?
-
 254Cyber Events
254Cyber EventsAmnesty Launches “Don’t Punish Edward Snowden” Campaign
The Amnesty International (United Kingdom) launched an online petition in support of ex-NSA spy and now a whistleblower Mr. Edward Snowden, urging...
-

 209Data Security
209Data SecurityBeware: This Simple Trick Lets Hackers to Hack Your WhatsApp Account
A YouTube Video explains that Facebook’s popular social messaging service WhatsApp can potentially and easily be hijacked by anyone if the user...
-

 104Surveillance
104SurveillanceFBI’s Mysterious Surveillance Planes Hovering Over US Cities
The Federal Bureau of Investigation (FBI) is using aircrafts for its surveillance operations on the ground in the US. The Associated Press exposed startling...
-
 211Surveillance
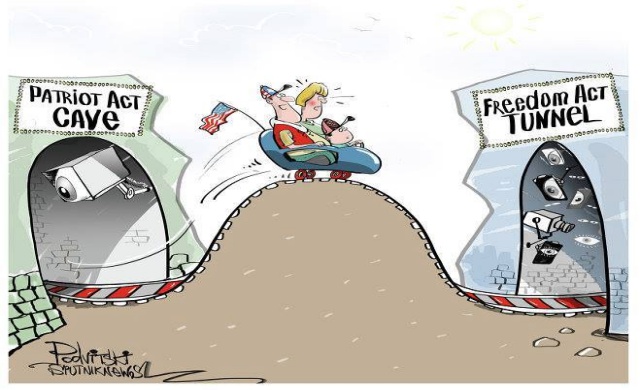
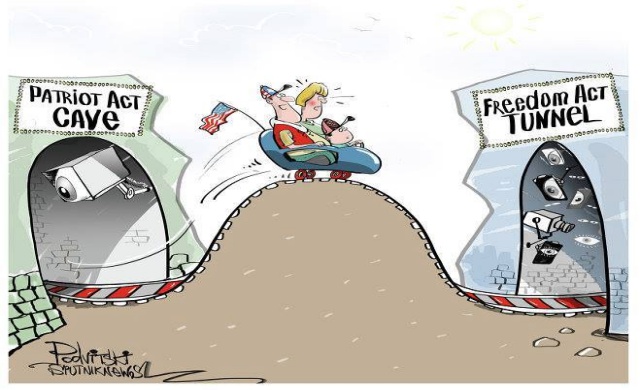
211SurveillanceThanks to Freedom Act: NSA Bulk Data Collection Coming Back to Haunt you
The Obama administration is seeking a temporary restart in its call records bulk collection program using the same law that banned it...
-

 326Social Engineering
326Social EngineeringJust 6% of UK workers trained for phishing attacks, reveals study
Just six percent of British employees have received training in dealing with phishing attacks, a survey has revealed.
-

 220Geek
220GeekNew Technology from Microsoft will provide Wi-Fi to users worldwide
World has changed, same goes for trends how nations progress. To make things productive you need to provide Internet access to users...
-

 340Geek
340GeekIndian PM Modi is in the list of ‘Top 10 Criminals’ on Google Image Search
If you search for ‘Top 10 Criminals’ on Google Image Search, you will find Indian Prime Minister Narendra Modi’ topping the list and Indians...
-

 212News
212NewsPro-Palestinian Group Hacks Piatt County’s Sheriff Office Website
Summary: In a successful cyber attack the online pro-Palestinian hackivist AnonGhost hacked the official website of Piatt County, Illinois along with the...
-
 167Surveillance
167SurveillanceGoogle Patents for contact lens that can scan your Iris
Google’s love for contact lenses is never ending. The search engine giant has already done considerable work on contact lenses and their...
-

 299News
299NewsSomeone hacked this traffic sign, replaced with Drake’s Steph Curry Lyric
Someone hacked into this electronic traffic signboard and left Drake’s Steph Curry song Lyrics. It is unclear who did it but they seem...
-
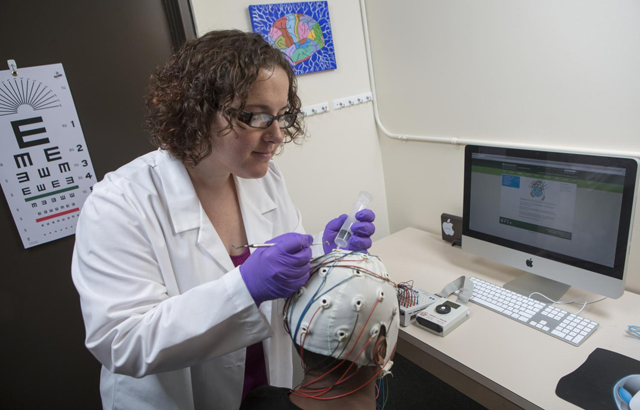
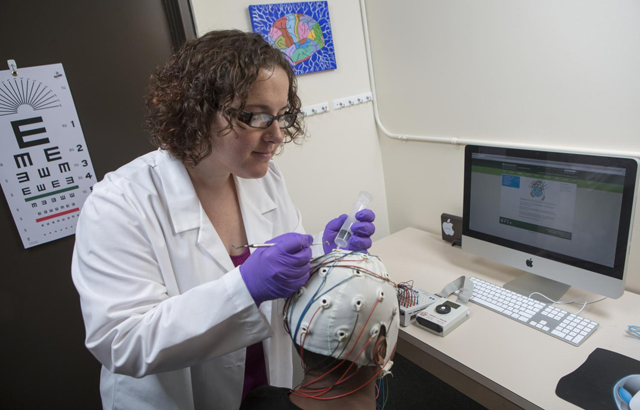 117Password
117PasswordCould brainwaves replace the password?
As biometrics become more popular, the password is increasingly losing ground to new alternatives. So, are Brainwaves the next big thing biometrics?
-

 121Scams
121Scams(More) Confessions of a Support Scammer
David Harley examines the latest confessions of a support scammer to appear on the web, this time from a Reddit Q&A.
-

 187Surveillance
187SurveillanceEdward Snowden is a hero, I like what he did: Actor Vince Vaughn
The 45-year old entertainer Vince Vaughn says that Snowden is a “hero” and guns should be allowed in public places and schools....
-

 163How To
163How ToHow To Check Storage Space On Your MAC OS X
Do you own a MacBook and don’t know how to check storage space of you MAC OS X, then let me tell...
The Latest
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Cyber Attack
Cyber AttackMicrosoft Patches 61 Flaws, Including Two Actively Exploited Zero-Days
-
 Cyber Attack
Cyber AttackThe 2024 Browser Security Report Uncovers How Every Web Session Could be a Security Minefield
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Data Breach
Data BreachBlack Basta Ransomware Strikes 500+ Entities Across North America, Europe, and Australia
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Data Breach
Data BreachA SaaS Security Challenge: Getting Permissions All in One Place
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment




